The defining 2026 remote-work security number is not a phishing rate. It is an underwriter's number. Coalition's 2025 Cyber Claims Report finds remote access services served as the entry point for 87% of ransomware claims, with VPN compromises alone responsible for 73% of ransomware intrusions where an entry vector was identified, up from 38% in 2023 and 66% in 2024. At-Bay's 2024 InsurSec claims data attribute 80% of all ransomware claims to remote-access tools, with VPNs alone two-thirds of the total. The Verizon 2025 Data Breach Investigations Report, based on 22,052 incidents and 12,195 confirmed breaches, records vulnerability exploitation rising to 20% of breach initial-access vectors (a 34% YoY jump) and zero-day exploits against network edge devices and VPNs at 22% of all vulnerability-exploit breaches, up from 3% the prior year, an almost eight-fold increase. The structural risk in 2026 is not the home Wi-Fi network or the laptop in the airport. It is the corporate-managed VPN concentrator, the SSL VPN headend, the single sign-on portal, the customer-support remote-access tool, and the edge appliance whose firmware patch landed last quarter and was never applied.
Three forces drive 2026 remote-work compromise. Edge-device zero-days are now the default entry technique for both ransomware affiliates and state-sponsored intrusion teams. CitrixBleed (CVE-2023-4966) and CitrixBleed 2 (CVE-2025-5777) bracket the trend; Imperva alone observed 11.5 million exploitation attempts against CVE-2025-5777, with 40% of those attacks targeted at financial services, after CISA added the flaw to the Known Exploited Vulnerabilities catalog on July 10, 2025. Ivanti Connect Secure CVE-2025-0282 was actively exploited at scale before patches landed, with Mandiant tracing exploitation back to mid-December 2024 and CISA later reporting the RESURGE malware variant designed to defeat the official mitigations. Fortinet, Cisco, and F5 followed with their own KEV-listed remote-access RCEs. Operational tempo collapsed: Mandiant's M-Trends 2026, drawing on roughly 450,000 hours of incident-response data, finds the average attacker hands off initial access to a follow-on operator in 22 seconds, down from 8+ hours in 2022, with CrowdStrike's 2026 Global Threat Report clocking an average eCrime breakout time of 29 minutes (fastest 27 seconds) and 82% of detections malware-free. And the social-engineering channel into remote access has industrialized: CrowdStrike measured a 442% jump in vishing between H1 and H2 2024 with at least four campaigns leveraging spam-bombing as a pretext for follow-up help-desk calls.
This post is the Stingrai research team's canonical 2026 reference for remote-work security risks. It assembles 90+ numeric claims from 25 named primary publishers, including Verizon DBIR, IBM Cost of a Data Breach Report 2025, Coalition Cyber Claims, At-Bay, Sophos State of Ransomware 2025, Mandiant M-Trends 2025 and 2026, Microsoft Digital Defense Report 2025, CrowdStrike Global Threat Reports 2025 and 2026, ENISA Threat Landscape 2025, NIST, CISA Known Exploited Vulnerabilities, the National Vulnerability Database, the FIDO Alliance, Gallup, and named corporate-incident records (Change Healthcare / UnitedHealth Group, Snowflake / UNC5537, MGM 2023, PowerSchool). Lead data is full-year 2024 and full-year 2025 telemetry, the freshest available; primary publishers have not yet released full-year 2026 reports as of April 2026. Stingrai is a Toronto-headquartered offensive-security firm founded in 2021; its team has published 18 CVEs, holds OSCE3 / OSCP / OSWE / OSED / OSEP / CREST CRT certifications, and runs PTaaS programs that test the same VPN concentrators, identity providers, and remote-access tooling discussed below. Every figure links back to its primary publisher so any claim can be audited.
TL;DR: 12 labeled key stats
Share of ransomware claims via remote access (2025): 87% (Coalition 2025 Cyber Claims Report).
Share of ransomware intrusions via VPN compromise where vector was identified (2025): 73% (up from 38% in 2023 and 66% in 2024) (Coalition).
Share of ransomware claims attributed to remote-access tools (2024): 80% (At-Bay InsurSec).
Verizon DBIR: vulnerability exploitation share of breach initial-access vectors: 20% (+34% YoY) (Verizon 2025 DBIR).
Verizon DBIR: zero-day exploits in network edge devices and VPNs: 22% of vulnerability-exploit breaches (up from 3% prior period) (Verizon 2025 DBIR).
Mandiant M-Trends 2026: average initial-access handoff time: 22 seconds (down from 8+ hours in 2022) (Mandiant M-Trends 2026).
Mandiant: exploits as initial-infection vector: 32% (sixth consecutive year as #1) (Mandiant M-Trends 2026).
CrowdStrike 2026 GTR: malware-free detections: 82% of intrusions (CrowdStrike 2026 GTR).
CrowdStrike 2026 GTR: average eCrime breakout time: 29 minutes (fastest 27 seconds) (CrowdStrike 2026 GTR).
Microsoft MDDR 2025: identity attacks that were password-spray: 97% (Microsoft Digital Defense Report 2025).
Microsoft MDDR 2025: criminal-marketplace remote-access listings that are RDP: 53% (corporate VPN portals 26%) (Microsoft Digital Defense Report 2025).
Imperva exploitation attempts against CitrixBleed 2 (CVE-2025-5777): 11.5M (40% targeted at financial services) (Arctic Wolf).
Key takeaways
Remote access is the load-bearing entry vector for ransomware in 2026. The two largest cyber-insurance carriers in the US, Coalition and At-Bay, both attribute roughly 80 to 87% of ransomware to remote-access services, with VPNs alone driving the majority. Remote work is no longer a network-edge accessory; it is the network edge, and edge appliances are the most-attacked infrastructure on the public internet.
Edge-device zero-days are now standard tradecraft. The Verizon DBIR's eight-fold YoY rise in zero-day exploits against VPN and edge appliances, Mandiant's documentation of UNC5221 burning two zero-days in the same VPN product over three months, and the steady cadence of CISA KEV additions (Ivanti, Citrix, Fortinet, Cisco ASA, F5 BIG-IP) all point to the same conclusion. Patching SLAs measured in weeks are operationally insufficient. The median between disclosure and mass exploitation is now zero days.
MFA without phishing-resistance is decorative on remote-access portals. Microsoft attributes 80% of MFA-bypass breaches to AiTM session-token theft and reports Tycoon2FA accounted for ~62% of all phishing it blocked by mid-2025. Change Healthcare's Citrix portal had no MFA at all. Snowflake's UNC5537 attackers used valid customer credentials with MFA not enforced. The defender baseline in 2026 is FIDO2 / passkeys / device-bound credentials on every remote-access path, with conditional access blocking unenrolled devices.
Identity is the second front. Microsoft's 97% password-spray share of identity attacks, RDP listings at 53% of criminal-marketplace remote-access offerings, and the Snowflake breach pattern (infostealer-derived credentials some dating to 2020 still working in 2024) underline that compromised credentials remain the cheapest, most reliable way into a remote-work environment. Stingrai covers the credential-theft side in detail in the Compromised Credential Statistics 2026 post.
Help-desk vishing closes the loop. CrowdStrike documented a 442% rise in vishing between H1 and H2 2024 and at least six help-desk-impersonation campaigns. The MGM 2023 attack, which started with a 10-minute call to MGM's help desk and ended with around US$100M in losses, is the canonical example. The defender pattern: out-of-band callback verification, ticket-based identity-proofing for credential resets, and operational segmentation between help-desk privilege and identity-provider privilege. Stingrai's Social Engineering Statistics 2026 covers the human-layer side in greater depth.
Methodology
Date cutoff: April 29 2026. Lead data is full-year 2024 or 2025 telemetry where a primary publisher has released it; 2026 figures are labeled as forecasts or projections. Statistics that could not be reached via a named primary source on at least one verification pass were dropped rather than estimated. Where multiple primary publishers report compatible figures we cite the publisher whose methodology window matches the claim. Secondary news aggregators are cited only where they constitute the public record of a corporate incident.
Sources span: Verizon Data Breach Investigations Report 2025 (22,052 incidents); IBM Cost of a Data Breach Report 2025 (600+ orgs); Coalition Cyber Claims Report 2025 and Cyber Threat Index 2025; At-Bay 2024 InsurSec and 2026 InsurSec Reports; Sophos State of Ransomware 2025 (3,400 IT/security leaders, 17 countries); Mandiant M-Trends 2025 and 2026 (~450,000 IR hours, CY2025); Microsoft Digital Defense Report 2025 plus the Tycoon2FA disruption blog; CrowdStrike 2025 + 2026 Global Threat Reports and 2025 Threat Hunting Report (Falcon and OverWatch telemetry); ENISA Threat Landscape 2025 (4,875 incidents); NIST SP 800-46 Rev 2 (telework guidance), NIST SP 800-207 (Zero Trust Architecture), and NIST SP 800-63-4 (digital identity, July 2025); CISA Known Exploited Vulnerabilities entries and joint advisories AA25-022A; the National Vulnerability Database; the FIDO Alliance passkey adoption surveys; Gallup Workplace surveys; Gartner public commentary on ZTNA replacement; Arctic Wolf and Tenable vulnerability-intelligence write-ups; and named corporate-incident records (Change Healthcare / UnitedHealth Group, Snowflake / UNC5537, MGM 2023, PowerSchool).
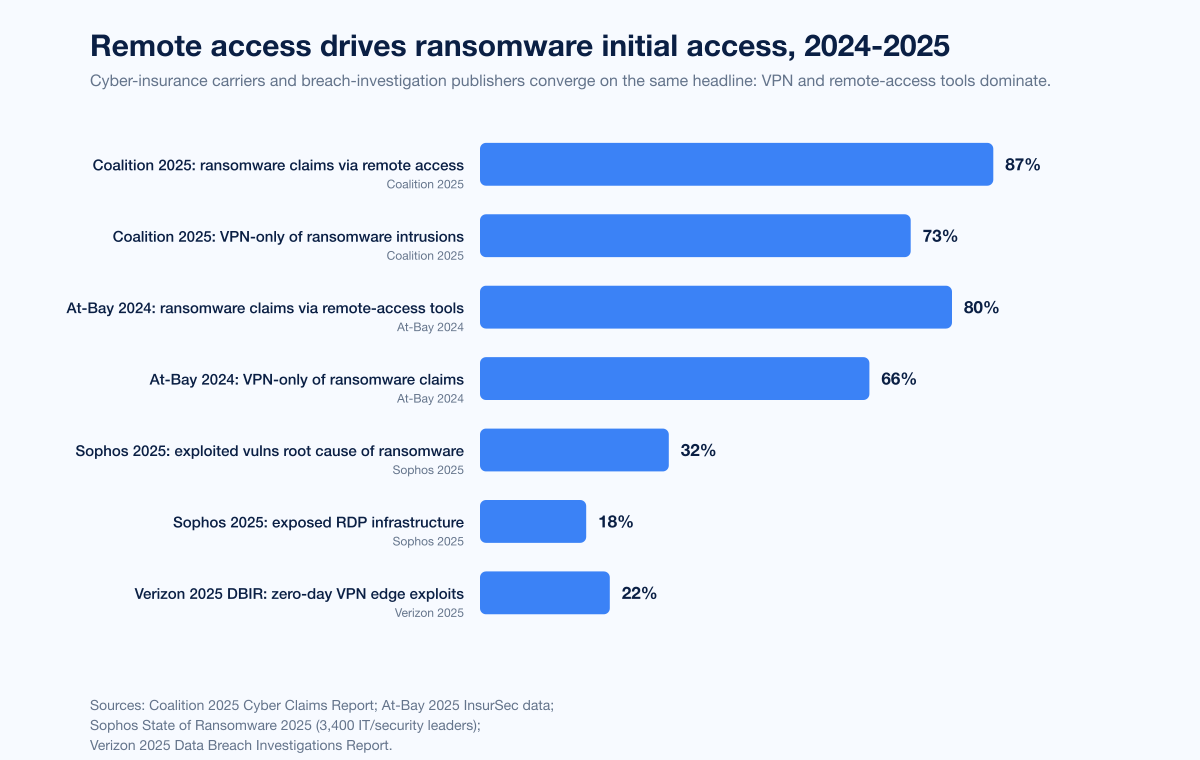
Figure 1: Share of ransomware initial-access vectors driven by remote access across the 2024 to 2025 primary-publisher set. Sources: Coalition 2025 Cyber Claims Report; At-Bay InsurSec 2024 + 2026; Sophos State of Ransomware 2025; Verizon 2025 DBIR.
How big is the remote-work security problem in 2026?
Three datasets anchor the answer. The first is underwriter claims data, because cyber insurers have to pay when remote-access controls fail and therefore have the strongest financial incentive to root-cause attacks honestly. The second is the Verizon DBIR, the longest-running corpus of breach forensics. The third is incident-response data from Mandiant and CrowdStrike, which sees what attackers actually do post-compromise.
Coalition Cyber Claims Report 2025
Coalition's 2025 Cyber Claims Report, drawing on the carrier's full-year 2024 claims plus early 2025 data, found that the most common ransomware initial-access vectors were stolen credentials (47%) and software exploits (29%). Most ransomware attacks started with the compromise of perimeter security appliances (58%) or remote desktop protocol (18%). Coalition's network-scanning telemetry detected over 5 million internet-exposed remote-management solutions and tens of thousands of exposed login panels across the public internet; when applying for cyber insurance, 65%+ of businesses had at least one internet-exposed web login panel. Coalition's later 2025 update reported remote access services served as the entry point for 87% of ransomware claims, up from 80% the prior year, with VPN compromises alone climbing to 73% of ransomware intrusions where an entry vector was identified, from 38% in 2023 and 66% in 2024.
At-Bay 2024 and 2026 InsurSec Reports
At-Bay's 2024 cyber claims data reported remote-access tools as the initial entry vector for 80% of ransomware claims, with VPNs alone responsible for two-thirds (66%) of all ransomware attacks. At-Bay's 2026 InsurSec Report tracked the trajectory through 2025: a 300% surge in SonicWall-related ransomware claims between Q2 and Q3 2025 driven by a single ransomware affiliate, an average ransom demand of US$958K (more than double the prior year), and a dwell time on these attacks averaging 1.5 days from initial intrusion to full encryption, with some cases moving from initial intrusion to full encryption in less than one hour.
Verizon 2025 DBIR
The Verizon 2025 DBIR, based on 22,052 incidents and 12,195 confirmed breaches between November 1 2024 and October 31 2025, found credential abuse the initial access vector in 22% of breaches, vulnerability exploitation second at 20% (a 34% YoY rise), phishing third at 16%. The most notable finding for remote work: zero-day bugs that attackers exploited in network edge devices and VPNs accounted for 22% of vulnerability exploits, up from just 3% in the prior period. VPN-targeted exploits grew almost eight-fold YoY. Twenty-two percent of all vulnerability-exploitation breaches targeted edge infrastructure (firewalls, VPN concentrators, remote-access gateways). Organizations fully remediated only 54% of these edge vulnerabilities, with a 32-day median time-to-remediate against a median time of zero days between disclosure and mass exploitation for new critical vulnerabilities affecting these devices.
Mandiant M-Trends 2025 + 2026
Mandiant's M-Trends 2026, drawing on roughly 450,000 hours of incident-response data through CY2025, reported exploits remain the leading entry point for the sixth consecutive year, at 32% of initial infection vectors. The average attacker hands off initial access to a follow-on operator in 22 seconds, down from 8+ hours in 2022. The report calls out network edge devices, including VPNs, firewalls, and routers, as among the most targeted systems for initial access; the canonical example is UNC5221 exploiting two separate zero-day vulnerabilities in the same VPN product over a three-month period, deploying in-memory malware to minimize disk artifacts and tunneling command-and-control traffic through legitimate third-party services to bypass network filtering. Many of the vulnerabilities used for initial access were exploited as zero-days, weaponized before a patch existed.
CrowdStrike 2025 + 2026 Global Threat Reports
The CrowdStrike 2026 Global Threat Report, based on Falcon telemetry across CY2025, recorded an 89% YoY increase in attacks by AI-enabled adversaries, 82% of detections malware-free (attackers using valid credentials, native administrative utilities, and commercial remote-access tools to blend into normal business activity), an average eCrime breakout time of 29 minutes (a 65% increase in speed from 2024), and a fastest observed breakout time of 27 seconds. CrowdStrike observed a 42% YoY increase in zero-days exploited prior to public disclosure as adversaries weaponized dozens for initial access, RCE, and privilege escalation.
The CrowdStrike 2025 Global Threat Report, covering CY2024, documented an extraordinary 442% rise in voice phishing (vishing) between H1 and H2 2024 with a 40% compounded monthly growth rate. CrowdStrike tracked at least six distinct campaigns in 2024 in which threat actors posed as IT support staff to persuade users into establishing remote-support sessions, with at least four leveraging spam-bombing as a pretext for follow-up vishing calls. CrowdStrike documented a CURLY SPIDER intrusion in which the entire chain, from initial social-engineering contact through backdoor account creation, took under four minutes end-to-end.
The remote-access edge device problem
Network-perimeter remote-access devices are the single most-attacked infrastructure category in 2025 and 2026. They sit at the boundary of the corporate network. They are difficult to monitor with traditional endpoint security tools because they often run vendor-managed firmware that does not accept standard EDR agents. They concentrate trust because a single device can mediate thousands of users into the corporate environment. And the patch cadence on these devices is structurally slower than software endpoints, because rolling a new firmware image typically requires a maintenance window, a backout plan, and (in regulated environments) change-board approval.
The Verizon DBIR's almost eight-fold YoY rise in zero-day exploitation against these devices is the headline. The CISA KEV catalog over the past 18 months tells the story in detail.
CitrixBleed (CVE-2023-4966) and CitrixBleed 2 (CVE-2025-5777)
CVE-2023-4966, known as CitrixBleed, is a sensitive information-disclosure vulnerability in Citrix NetScaler Gateway and NetScaler ADC products with a CVSS score of 9.4. The flaw allows an unauthenticated attacker to send a crafted HTTP GET request and retrieve session tokens directly out of memory, bypassing both password and MFA. CISA added the CVE to KEV on October 18, 2023, and CISA, FBI, MS-ISAC, and the Australian Signals Directorate jointly attributed Lockbit 3.0 affiliate exploitation in subsequent advisories. Sophos's State of Ransomware 2025 named CitrixBleed the single most exploited vulnerability for initial access in 2024 ransomware attacks at 5% of cases.
CVE-2025-5777, nicknamed CitrixBleed 2, is a pre-authentication remote memory-disclosure vulnerability in Citrix NetScaler ADC and Gateway with a CVSS 4.0 score of 9.3. CISA added it to the KEV catalog on July 10, 2025. Imperva publicly reported observing 11.5 million exploitation attempts against the flaw, with 40% of those attacks targeted at financial services. The vulnerability affects NetScaler devices configured as a Gateway (VPN virtual server, ICA Proxy, CVPN, RDP Proxy) or AAA virtual server, and enables session-token hijacking similar to the original CitrixBleed.
Ivanti Connect Secure (CVE-2025-0282 / 0283)
CVE-2025-0282 is a stack-based buffer overflow in Ivanti Connect Secure that allows a remotely delivered, unauthenticated request to overflow a fixed-size stack buffer and lead to arbitrary code execution. The vulnerability affects Ivanti Connect Secure (versions before 22.7R2.5), Ivanti Policy Secure (versions before 22.7R1.2), and Ivanti Neurons for ZTA gateways (versions before 22.7R2.3). Mandiant and Ivanti's joint investigation detected exploitation going back to mid-December 2024, with post-exploitation activity including lateral movement and deployment of SPAWN-family malware. CISA added CVE-2025-0282 to the KEV catalog and later issued updated mitigation guidance after identifying the RESURGE malware variant designed to undermine the official patch and ICT mitigations.
CISA's joint advisory AA25-022A documented threat actors chaining vulnerabilities in Ivanti Cloud Service Applications. The lesson for buyers is that an Ivanti Connect Secure appliance with a 60-day patch backlog is, in 2026 threat conditions, an unauthenticated RCE waiting to happen.
FortiOS SSL VPN and FortiManager
The Fortinet remote-access stack accumulated a year of KEV-listed exploits across 2024 and 2025. CVE-2024-21762 is an out-of-bounds write in FortiOS SSL VPN that allows pre-auth RCE. CVE-2024-23113 is an externally controlled format string in the fgfmd daemon, also pre-auth RCE. CVE-2024-55591, disclosed January 14 2025, was reported as actively exploited at the time of disclosure. CVE-2024-47575 in FortiManager was tracked by Mandiant under cluster UNC5820 with mass exploitation across 50+ potentially compromised FortiManager devices as early as June 27, 2024. CISA's Fortinet post-exploitation advisory in April 2025 added a fresh wrinkle: a technique that allowed attackers to maintain post-exploitation access via symbolic-link manipulation even after the underlying CVEs were patched.
Cisco ASA and IOS XE
Cisco's adaptive-security-appliance and firewall-threat-defense stack had its own zero-day month in late 2025. CVE-2025-20333 is a critical authenticated RCE in Cisco ASA / FTD that requires only valid VPN credentials and a crafted HTTP request. CVE-2025-20362 is a medium-severity unauthenticated flaw allowing access to restricted URL endpoints. CVE-2025-20363 allows unauthenticated remote code execution against Cisco ASA / FTD software. CISA's Emergency Directive ED 25-03 ordered federal civilian agencies to identify and mitigate compromised Cisco devices. The campaign behind these flaws is connected to the ArcaneDoor activity tracked since early 2024.
F5 BIG-IP APM (CVE-2025-53521)
CVE-2025-53521 is a pre-authentication remote-code-execution vulnerability in F5 BIG-IP Access Policy Manager (APM), affecting BIG-IP APM versions 17.x, 16.x, and 15.x. The flaw was originally disclosed in October 2025 as a denial-of-service issue (CVSS 7.5); on March 27, 2026, F5 reclassified it as RCE (CVSS 9.3) after research surfaced exploitable code paths. CISA added CVE-2025-53521 to the KEV catalog the same day and ordered federal civilian agencies to assess exposure and mitigate by March 30, 2026. F5 BIG-IP APM is widely deployed as the SSL VPN, application gateway, and identity-aware-proxy front door for large enterprises and federal agencies; the patch window for organizations that mistakenly believed they had until October 2026 to patch a DoS was four days.
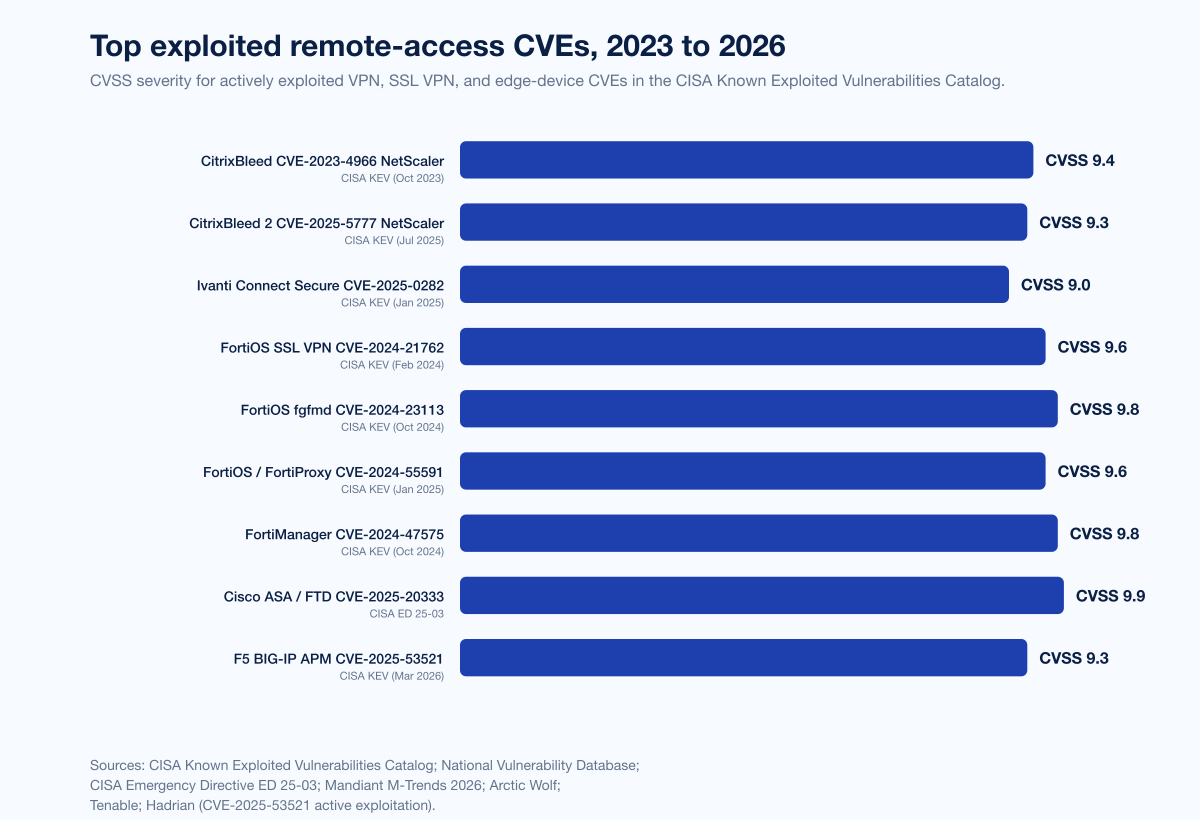
Figure 2: Top exploited remote-access CVEs 2023 to 2026, by CVSS severity. Sources: CISA Known Exploited Vulnerabilities; NVD; Sophos State of Ransomware 2025; Mandiant M-Trends 2026; Tenable; Arctic Wolf.
CVE | Product | CVSS | Type | KEV | Exploitation signal |
|---|---|---|---|---|---|
CVE-2023-4966 | Citrix NetScaler ADC / Gateway (CitrixBleed) | 9.4 | Pre-auth info disclosure / session hijack | Yes (Oct 18 2023) | LockBit 3.0 affiliate exploitation; Sophos: 5% of 2024 ransomware initial access |
CVE-2025-5777 | Citrix NetScaler ADC / Gateway (CitrixBleed 2) | 9.3 | Pre-auth memory disclosure | Yes (Jul 10 2025) | Imperva: 11.5M exploitation attempts; 40% targeting financial services |
CVE-2025-0282 | Ivanti Connect Secure / Policy Secure / ZTA | 9.0 | Pre-auth stack-based buffer overflow / RCE | Yes (Jan 2025) | Mandiant: exploitation since mid-Dec 2024; RESURGE malware to defeat mitigations |
CVE-2025-0283 | Ivanti Connect Secure / Policy Secure / ZTA | 7.0 | Auth stack-based buffer overflow / privilege escalation | Yes | Paired with 0282 in chained exploitation |
CVE-2024-21762 | FortiOS SSL VPN | 9.6 | Pre-auth out-of-bounds write / RCE | Yes (Feb 2024) | Mass scanning / exploitation observed |
CVE-2024-23113 | FortiOS / FortiPAM / FortiSwitchManager (fgfmd) | 9.8 | Format-string pre-auth RCE | Yes (Oct 2024) | CISA-confirmed in-the-wild exploitation |
CVE-2024-55591 | FortiOS / FortiProxy | 9.6 | Auth bypass / super-admin | Yes (Jan 2025) | Active exploitation at disclosure |
CVE-2024-47575 | FortiManager | 9.8 | Auth-bypass / RCE | Yes (Oct 2024) | Mandiant UNC5820: 50+ devices affected |
CVE-2025-20333 | Cisco ASA / FTD | 9.9 | Auth RCE via crafted HTTP | Yes (2025) | ArcaneDoor-linked activity |
CVE-2025-20362 | Cisco ASA / FTD | 6.5 | Restricted-URL access bypass | Yes (2025) | Chained with 20333 |
CVE-2025-53521 | F5 BIG-IP APM | 9.3 | Pre-auth RCE | Yes (Mar 27 2026) | Reclassified from DoS; CISA ED-style mitigation |
Identity is the second front
Compromised credentials remain the cheapest, most reliable way into a remote-work environment. The Microsoft Digital Defense Report 2025 reports 97% of identity attacks were password-spray attacks, exploiting the structural problem of weak and overused passwords across cloud SaaS and identity providers. 28% of breaches were initiated through phishing or social engineering, 18% via unpatched web assets, and 12% leveraged exposed remote services. RDP listings on criminal marketplaces accounted for 53% of remote-access offerings, followed by corporate remote-access portals at 26%.
Three identity patterns dominate 2026 remote-work intrusions.
Infostealer-derived credentials. Mandiant's investigation of UNC5537 found credentials stolen by infostealer malware infections on non-Snowflake-owned systems still working against Snowflake customer accounts in 2024, with some credentials dating back to infostealer infections as early as 2020. The structural failure was that Snowflake customer accounts were not configured with MFA, and infostealer-stolen credentials remained valid years after the original device compromise. The threat actor primarily used Mullvad and Private Internet Access VPN IP addresses to access victim Snowflake instances; Mandiant notified approximately 165 potentially exposed organizations, with public records identifying AT&T, Ticketmaster / Live Nation, Santander Bank, LendingTree, Advance Auto Parts, Neiman Marcus, and Bausch Health among the affected.
AiTM session-token theft. Microsoft attributes 80% of MFA-bypass breaches to AiTM session-token theft. The March 2026 disclosure on Tycoon2FA reports the AiTM phishing-as-a-service kit accounted for ~62% of all phishing blocked by Microsoft by mid-2025, with Microsoft Defender for Office 365 blocking more than 13 million Tycoon2FA emails in October 2025 alone. The AiTM kit is rented for US$120 (10-day access) to US$350 (monthly), lowering the technical bar for credential-plus-session-token theft against Microsoft 365. Microsoft, Europol, and 11 partners disrupted the platform's infrastructure in early March 2026, but the underlying technique (an attacker-controlled reverse proxy intercepting the OAuth dance) is generic and will outlive any specific kit.
Help-desk impersonation. CrowdStrike documented a 442% rise in vishing between H1 and H2 2024 and at least six distinct help-desk-impersonation campaigns through 2024. Scattered Spider's resurgence in 2025 used the same playbook with faster and more aggressive tradecraft. The canonical 2023 example: a 10-minute call by Scattered Spider to MGM Resorts' IT help desk, in which attackers impersonated an employee they had identified via LinkedIn, walked the help-desk operator through a credential reset, and gained administrator privileges in MGM's Okta and Azure tenant environments. Within 24 hours the group had configured a new identity provider via Okta's inbound-federation feature and started sniffing passwords. ALPHV deployed ransomware to more than 100 ESXi hypervisors. The estimated cost to MGM was approximately US$100M in lost revenue, legal fees, and remediation.
For the deeper credential-theft and SIM-swap cuts, see Stingrai's Compromised Credential Statistics 2026 and SIM Swap Statistics 2026.
BYOD, home networks, and the unmanaged endpoint
Bring-your-own-device and unmanaged-endpoint policies were a remote-work necessity in 2020. By 2026 they are the third-largest remote-work risk after edge-device exploitation and credential theft, primarily because the controls organizations apply to corporate-issued laptops do not extend to personal devices. The Verizon DBIR consistently shows that managed-endpoint visibility (EDR coverage, posture compliance, OS patch level) is dramatically higher than on personal devices accessing corporate resources via VPN or web SSO.
Three structural issues dominate the BYOD failure mode.
No EDR on the personal device. When a remote worker connects via VPN from a home laptop running an outdated OS, the corporate SOC has zero visibility into what is running on that endpoint. If the personal device hosts an infostealer, the credentials it harvests are corporate credentials; the Snowflake / UNC5537 pattern is exactly this. Microsoft MDDR 2025 specifically calls out "isolate management interfaces and RMM tools to VPN-only or dedicated admin networks" as a critical control because of this asymmetry.
Home-network IoT compromise. A compromised consumer router or smart-home device on the same Wi-Fi as a remote worker's laptop can host a man-in-the-middle, intercept DNS, or pivot to the laptop. Stingrai's IoT Attack Statistics 2026 covers consumer-router and smart-home compromise rates in detail. Bitdefender + NETGEAR home-network research shows roughly half of US homes carry at least one vulnerable IoT device.
Lost or stolen devices. A laptop left in an airport with corporate session cookies in browser storage, or a phone with refresh tokens bound to corporate Microsoft 365, is a remote-access incident even if no credential is ever phished. Conditional-access policies that bind sessions to known device IDs and revoke on physical-loss reports are the defender pattern.
The defender control set: enforce MDM (Microsoft Intune, Jamf, Workspace ONE) device-posture checks on every remote-access path; require an EDR agent (Defender for Endpoint, CrowdStrike Falcon, SentinelOne) on any device that touches corporate data; block unenrolled devices with conditional access; and use secure browsers (Island, Talon, Chrome Enterprise Premium) for high-sensitivity workloads where a full MDM enrollment is not feasible.
VPN deprecation: the slow-motion phase-out
Gartner has been forecasting Zero Trust Network Access (ZTNA) replacement of always-on VPN for five years. The 2025 numbers say it is finally happening, slowly. Gartner's Market Guide for ZTNA and related public commentary forecast that by 2025 at least 70% of new remote-access deployments will rely on ZTNA rather than VPN services. Industry surveys cited in The State of Zero Trust 2025 show 34% of companies using cloud-delivered ZTNA platforms, 27% using peer-to-peer mesh VPNs (Tailscale, Twingate, Cloudflare Access), and 41% still on legacy always-on VPN.
Three patterns characterize the transition.
Greenfield deployments lead. New offices, new SaaS-first lines of business, and new acquisitions overwhelmingly skip always-on VPN in favor of ZTNA + identity-aware proxy. Cloudflare Access, Zscaler Private Access, Twingate, and Tailscale dominate the new-deployment market. Microsoft Entra Private Access and Cisco Secure Access (formerly Duo + Umbrella + AnyConnect) are the incumbent-vendor offers.
Legacy-stack inertia is real. Large regulated enterprises with a Citrix or F5 BIG-IP estate cannot rip-and-replace inside a fiscal year. The pattern is incremental: migrate user-to-app traffic to ZTNA first, leave legacy admin and partner connectivity on the legacy concentrator, and aggressively segment what is left.
SASE convergence is the destination. Gartner's SASE framing predicts ZTNA will be bundled into both SSE and SASE offerings, replacing always-on VPN as the default remote-access mechanism by the end of the decade. The agent-based ZTNA architecture is converging across vendors.
The remote-access tradeoff matrix in 2026:
Approach | Remote-access topology | Identity model | Best fit | Risk pattern |
|---|---|---|---|---|
Always-on SSL VPN | Network-layer tunnel | User → network → app (broad) | Brownfield, regulated, latency-tolerant | Edge-device CVE exposure; lateral-movement risk inside VPN |
Per-app ZTNA (cloud) | Application-layer tunnel via cloud broker | User → app (narrow), conditional | SaaS-first orgs, hybrid workforce | Trust in ZTNA broker; broker outage blast radius |
Mesh VPN (peer-to-peer) | WireGuard mesh | User → app (segmented) | Engineering-heavy orgs, infra access | Endpoint compromise → mesh-wide reach if not segmented |
Browser-based isolation | HTTPS through secure browser | User → app (browser-bound) | High-sensitivity workloads, contractors | Browser CVE exposure; non-browser apps unsupported |
Bastion / IAP for admin | Identity-aware proxy + jump host | Admin → resource (just-in-time) | Cloud-infrastructure access | Bastion CVE exposure; misconfigured policies |
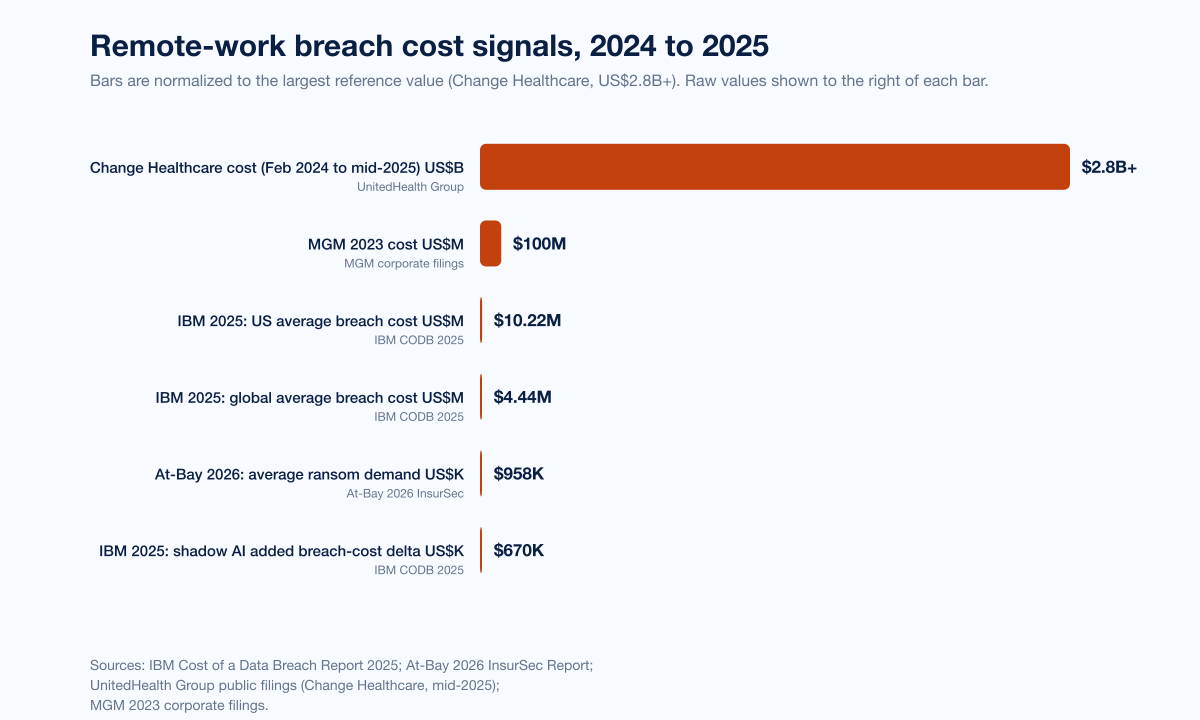
Figure 3: Remote-work breach-cost signals across 2024 and 2025 primary publishers. Sources: IBM Cost of a Data Breach Report 2025; At-Bay 2026 InsurSec; Change Healthcare / UnitedHealth Group public filings; MGM 2023 corporate filings.
Phishing-resistant MFA: the new floor
Microsoft's Digital Defense Report 2025 is unambiguous: enforce phishing-resistant multifactor authentication across accounts, including administrative accounts. Push-notification MFA, SMS-OTP MFA, and TOTP MFA all fall to AiTM session-token theft and to MFA-fatigue prompt-bombing. Phishing-resistant MFA, defined by NIST SP 800-63B Authenticator Assurance Level 3 and the FIDO2 / WebAuthn standard, is the new defender baseline.
The 2025 adoption signal is real. The FIDO Alliance's 2024-2025 surveys report 75% of consumers now recognize passkeys, 53% have enabled passkeys on at least one account, and 22% have enabled them on every account where possible. Over 3 billion passkeys are in active use globally. NIST's updated digital-identity guidelines, SP 800-63-4 finalized in July 2025, now require multi-factor authentication to offer a phishing-resistant option as a built-in choice for relying parties.
Microsoft has reported 92% of employee productivity accounts protected by phishing-resistant authentication methods after embedding passkeys / FIDO2 keys into onboarding, transitions, and deactivation workflows. Passkey logins are reportedly three times faster than traditional passwords and eight times faster than a password plus traditional MFA, according to Microsoft's internal rollout data, with passkey implementations cutting credential-related support calls by approximately 70%.
The defender-side pattern in 2026:
Block legacy authentication. Legacy SMTP, POP3, IMAP, and basic-auth Microsoft 365 sign-ins skip MFA entirely. Block them at the identity provider.
Require phishing-resistant MFA on remote-access portals. No exceptions for "this VPN is just for the engineering team." Every remote-access path is a target.
Bind sessions to device. Conditional-access policies that require a managed device, a current OS patch level, and a known device ID. Refuse to issue session tokens to unenrolled devices.
Privileged-account separation. Admin accounts on dedicated tenant-isolated identities, with hardware FIDO2 keys, JIT elevation, and no inbox.
Rotate session lifetimes. Long-lived refresh tokens are an asset for an AiTM operator. Short token lifetimes plus continuous-access evaluation reduce blast radius.
For the deeper phishing-side cuts, see Stingrai's Phishing Statistics 2026.
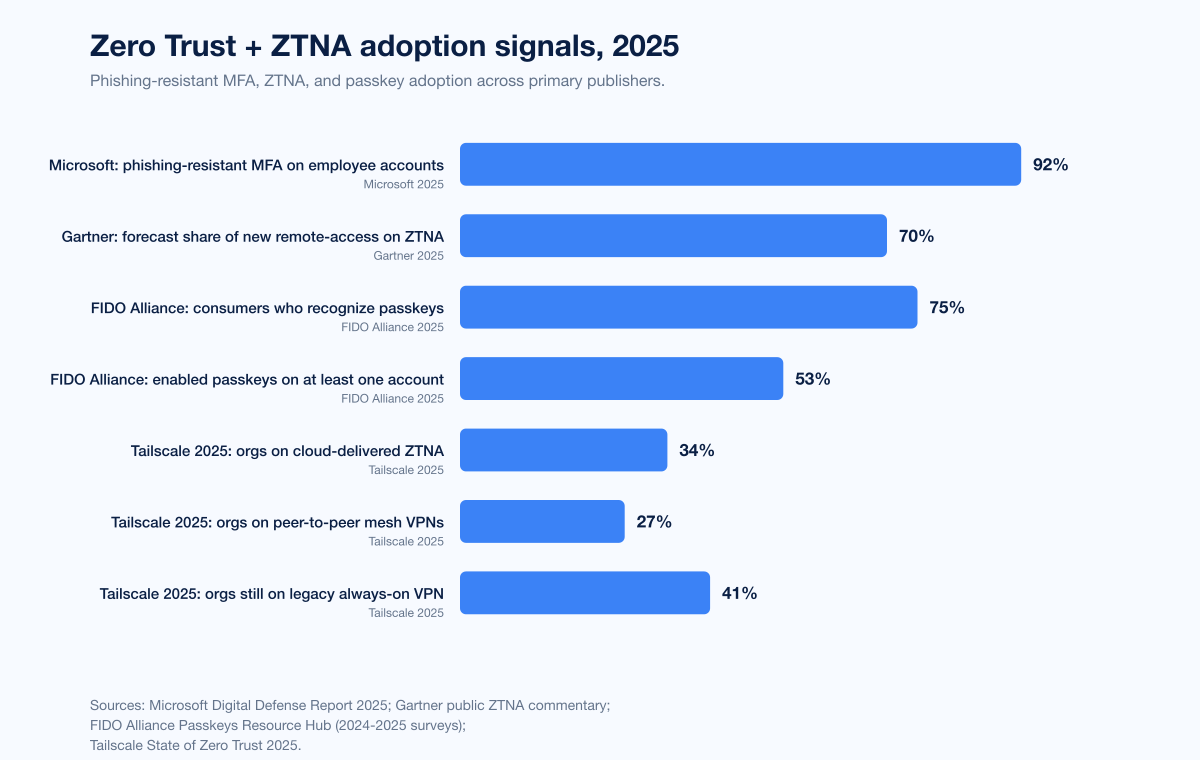
Figure 4: Zero Trust and ZTNA adoption signals 2025. Sources: FIDO Alliance; Microsoft Digital Defense Report 2025; NIST SP 800-63-4; Gartner public commentary on ZTNA replacement; Tailscale State of Zero Trust 2025.
Named incidents 2024 to 2025: where remote-work controls failed
Five corporate breaches between February 2024 and December 2024 illustrate the modal failure mode of 2026 remote-work security: a remote-access entry point that either lacked MFA, allowed legacy authentication, or hosted a known-exploitable CVE.
Change Healthcare / UnitedHealth Group, February 2024
Change Healthcare, the US's largest healthcare claims-clearing intermediary, was breached on February 12, 2024 when ALPHV / BlackCat ransomware affiliates used compromised credentials to remotely access a Change Healthcare Citrix portal that did not have multi-factor authentication enabled. The attackers moved laterally for nine days before deploying ransomware. UnitedHealth Group CEO Andrew Witty later confirmed in TechCrunch reporting that the attack did not exploit a Citrix CVE; the attackers simply used valid credentials against an MFA-less remote-access portal. The breach affected approximately 193 million Americans, the largest healthcare data breach in US history. UnitedHealth paid a US$22M ransom, and total costs topped US$2.8 billion by mid-2025. The single missing control was MFA on a remote-access portal.
Snowflake / UNC5537, April-July 2024
Mandiant's UNC5537 investigation traced ~165 organizations' Snowflake-instance compromises to stolen customer credentials primarily obtained from infostealer-malware campaigns on non-Snowflake-owned systems, some dating to 2020. None of the affected accounts had MFA enforced. Snowflake customer instances did not have network-policy rules limiting access to trusted locations. The attackers used Mullvad and Private Internet Access VPN IP addresses to access victim Snowflake environments. Public-record victims include AT&T, Ticketmaster / Live Nation, Santander Bank, LendingTree, Advance Auto Parts, Neiman Marcus, and Bausch Health. The single missing control was MFA on customer Snowflake accounts; the structural failure was that infostealer-derived credentials from a remote worker's compromised personal device propagated unchecked into corporate cloud-data-warehouse access.
MGM 2023 (referenced as foundational pattern)
Scattered Spider's September 2023 attack on MGM Resorts is the canonical 2026 lesson on help-desk vishing. The group identified an MGM employee via LinkedIn, called the IT help desk impersonating that employee, and was walked through a credential reset by a help-desk operator within ten minutes. The operator did not perform out-of-band callback verification. The attackers gained administrator privileges in MGM's Okta and Azure tenant environments, configured a new identity provider via Okta's inbound-federation feature, and within 24 hours had deployed ransomware to more than 100 ESXi hypervisors. The cost to MGM was approximately US$100M in lost revenue, legal fees, and remediation. The single missing control was identity-proofing on credential resets at the help desk.
PowerSchool, December 2024
PowerSchool's SIS Incident was the largest US K-12 student-data breach of 2024-2025. The threat actor accessed PowerSource, a customer-support remote-management portal, using a single compromised credential. Investigators later confirmed the same credentials were used against PowerSource between August 16 and September 17, 2024, months before the December 19-28, 2024 exfiltration window. The attacker performed "Maintenance Remote Support operations" through PowerSource, which enabled access to individual customer-organization SIS instances and exfiltrated student / teacher tables containing names, contact information, dates of birth, social security numbers, and limited medical-alert data. PowerSchool paid a ransom, and individual school districts received separate extortion demands by May 2025 using the same data. The DOJ identified the attacker as a 19-year-old Massachusetts university student. The single missing control was MFA on a customer-support remote-management portal.
Pattern across the four
In every case the entry vector was remote access. In every case the missing control was either MFA, MFA-enforcement-on-remote-portal, or out-of-band identity proofing. In none of the four was the entry point a sophisticated zero-day exploit. The 2026 remote-work threat model is not "what if Mandiant tells us our VPN concentrator was burned by a state-actor zero-day"; that risk is real but tail-distributed. The modal risk is "what if our help desk performs a password reset over a phone call, or our SaaS tenant has an admin without MFA, or our customer-support tool ships with a default credential."
What this means for security buyers
Three implications for the 2026 security-buying program follow directly from the data above.
Penetration testing must include remote-access edge. Annual external pentests that scope to a corporate website and a public IP range miss the actual 2026 attack surface. A remote-work-relevant pentest scope includes the VPN concentrator, the SSL VPN headend, the SSO portal, the customer-support remote-management tool, the cloud-identity provider, the conditional-access policy set, and the help-desk credential-reset workflow. Stingrai runs PTaaS programs across all of these surfaces, with continuous testing rather than annual point-in-time engagements. See Stingrai PTaaS and the Best PTaaS Providers 2026 reference.
The defender stack has expanded. "Antivirus + firewall + VPN + SIEM" was the 2015 remote-work stack. The 2026 minimum is phishing-resistant MFA, ZTNA, conditional access, EDR on every device that touches corporate data (including personal), MDM device-posture enforcement, secure browsers for high-sensitivity workloads, just-in-time admin, network segmentation, identity-threat detection (ITDR), DLP, secure web gateway, and continuous attack-surface management. Buyers should be evaluating remote-access vendors against this expanded stack, not against a 2015 reference architecture.
Compliance frameworks are catching up. NIST SP 800-63-4 finalized in July 2025 requires phishing-resistant MFA as an option. CISA's Zero Trust Maturity Model 2.0 makes "advanced" maturity contingent on phishing-resistant authentication and per-app access policies. PCI DSS 4.0 requirement 8.5 has extended MFA mandates beyond cardholder-data-environment access. SOC 2 Type II controls increasingly scrutinize remote-access policy enforcement. Stingrai's compliance-aligned PTaaS testing covers SOC 2, ISO 27001, HIPAA, PCI DSS 4.0, NIST SP 800-53 / 800-171, DORA, and NIS2.
For the broader compliance-side cuts, see Stingrai's posts on How to Prepare for SOC 2 Audits and Penetration Testing vs Vulnerability Assessment.
The Stingrai 2026 defender stack for remote work
The control set below maps directly to the failure modes documented above. Effort ratings reflect typical mid-market deployment complexity (1 = config flag, 5 = multi-quarter program).
Control | Defends against | Effort | Strength | Vendors / standards |
|---|---|---|---|---|
Phishing-resistant MFA (FIDO2 / passkeys) | AiTM session-token theft, password spray, MFA-fatigue prompt-bombing | 3 | High | Microsoft Entra ID + Authenticator passkeys, Yubico YubiKey 5, Google Titan, FIDO2 / WebAuthn |
Per-app ZTNA (replaces always-on VPN) | Edge-device zero-day RCE, lateral movement inside VPN trust zone | 4 | High | Cloudflare Access, Zscaler Private Access, Twingate, Tailscale, Microsoft Entra Private Access, Cisco Secure Access |
Conditional access binding sessions to device | Stolen credentials replayed from unmanaged endpoint | 3 | High | Microsoft Entra Conditional Access, Okta Adaptive MFA, Cisco Duo |
EDR on every endpoint touching corporate data | Infostealers, malware-free intrusions, credential harvest | 4 | High | Microsoft Defender for Endpoint, CrowdStrike Falcon, SentinelOne, Sophos Intercept X |
MDM / device-posture enforcement | BYOD compromise, lost-device exposure | 4 | High | Microsoft Intune, Jamf, VMware Workspace ONE |
Just-in-time / privileged-access management | Standing admin privilege as a target | 4 | High | Microsoft Entra PIM, BeyondTrust, AWS / GCP IAM workload identity, HashiCorp Boundary |
Identity threat detection and response (ITDR) | Compromised-credential signals, anomalous sign-in patterns | 4 | Medium-High | Microsoft Entra ID Protection, Okta ITP, Cisco Identity Intelligence |
Secure browser for high-sensitivity workloads | Data leakage on unmanaged contractor devices | 3 | Medium-High | Island, Talon, Chrome Enterprise Premium, Microsoft Edge for Business |
Network segmentation / microsegmentation | Lateral movement after edge-device compromise | 5 | High | Illumio, Cisco Secure Workload, Microsoft Azure Firewall, AWS Security Groups |
Continuous attack-surface management | Unknown internet-exposed remote-access tool | 3 | High | Microsoft Defender EASM, Tenable ASM, Palo Alto Cortex Xpanse |
Out-of-band callback identity proofing at help desk | Help-desk vishing | 2 | High | Process control plus call-back verification, employee-identity-proofing software |
Secure web gateway / SASE | Drive-by phishing, malicious-site delivery to remote endpoints | 4 | Medium-High | Cloudflare Gateway, Zscaler ZIA, Cisco Secure Access, Palo Alto Prisma SASE |
DLP / data-leak prevention on remote endpoints | Data exfiltration from unmanaged endpoints | 4 | Medium | Microsoft Purview DLP, Forcepoint, Trellix |
Continuous penetration testing (PTaaS) on remote-access stack | Latent CVE / configuration drift on VPN, SSO, customer-support portal | 3 | High | Stingrai PTaaS, peer PTaaS providers (see Best PTaaS Providers 2026) |
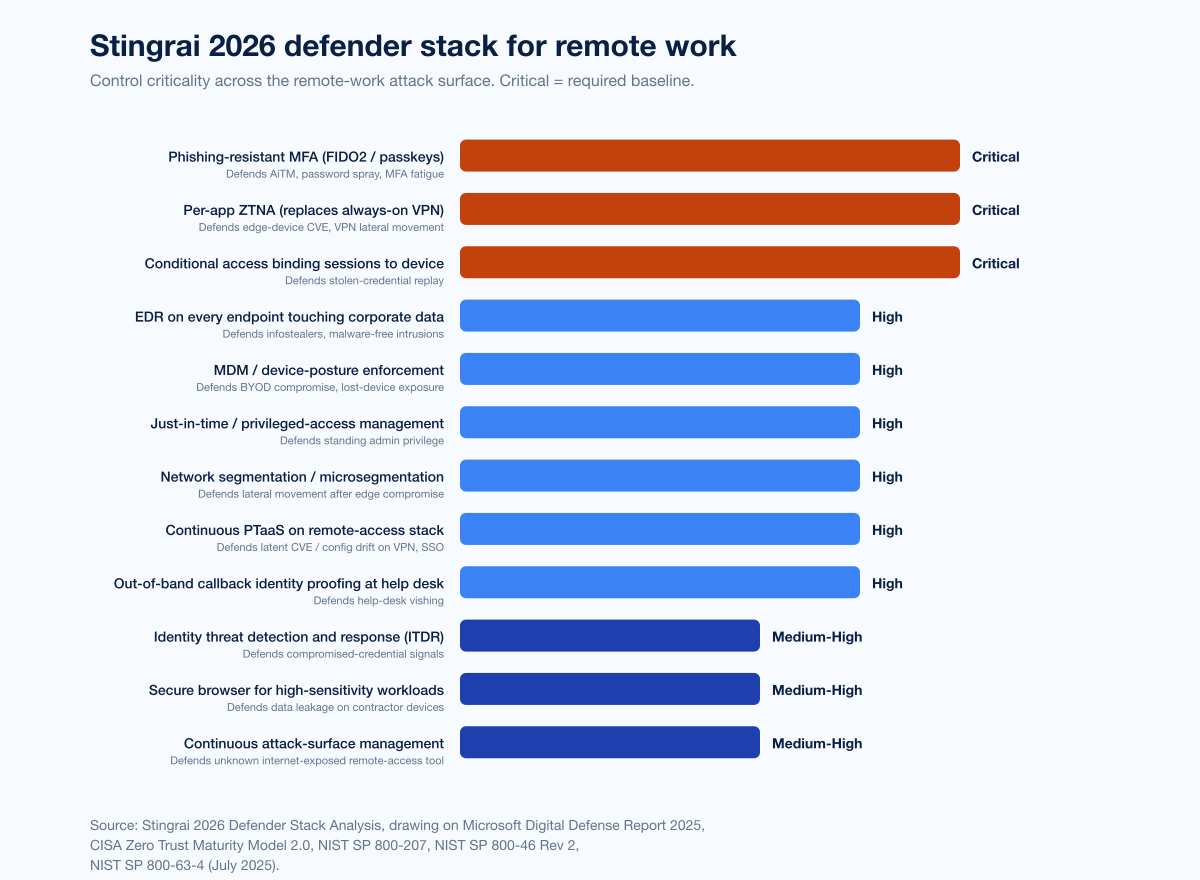
Figure 5: The Stingrai 2026 defender stack for remote work, by control criticality. Source: Stingrai 2026 Defender Stack Analysis, drawing on Microsoft Digital Defense Report 2025, CISA Zero Trust Maturity Model 2.0, NIST SP 800-207, and NIST SP 800-46 Rev 2.
How Stingrai tests remote-access security
Stingrai is a Toronto-headquartered offensive-security firm founded in 2021. Our team has published 18 CVEs and holds OSCE3, OSCP, OSWE, OSED, OSEP, CREST CRT, CISSP, CRTO, GCPN, CRTE, and eWPTX certifications. We run continuous PTaaS programs against the same VPN concentrators, identity providers, and remote-access tooling discussed above, plus AI-pentesting agent Snipe trained on 6,000+ HackerOne reports.
For remote-work-specific engagements, our typical scope includes:
External attack surface enumeration (continuous, via passive + active discovery)
VPN concentrator and SSL VPN headend testing (CVE chain validation, firmware version drift, config audit)
Identity provider and SSO portal testing (Okta, Microsoft Entra ID, Google Workspace, Ping)
Conditional-access policy validation (does the conditional-access posture actually block the cases it claims to block?)
AiTM session-token-theft simulation (Tycoon2FA-style attacks against MFA configurations)
Help-desk-vishing simulation (red-team callable engagement against credential-reset workflow)
Customer-support remote-tool testing (the PowerSchool failure mode)
Cloud-data-warehouse and SaaS-tenant configuration audit (the Snowflake / UNC5537 failure mode)
Compliance alignment: SOC 2, ISO 27001, HIPAA, PCI DSS 4.0, NIST SP 800-53 / 800-171, DORA, NIS2.
Frequently Asked Questions
What is the biggest remote work security risk in 2026?
Remote-access edge devices are the largest 2026 remote-work risk. Coalition's 2025 Cyber Claims Report finds remote access services served as the entry point for 87% of ransomware claims, with VPN compromises alone responsible for 73% of ransomware intrusions where an entry vector was identified, up from 38% in 2023 and 66% in 2024. At-Bay attributes 80% of 2024 ransomware claims to remote-access tools. The Verizon 2025 DBIR records zero-day exploitation against network edge devices and VPNs at 22% of all vulnerability-exploit breaches, up from 3% the prior period, an almost eight-fold increase. The structural failure mode is a corporate VPN concentrator, SSL VPN headend, customer-support remote-access tool, or identity-provider portal whose firmware patch landed last quarter and was never applied, or whose MFA was never enabled. Stingrai's recommendation: phishing-resistant MFA (FIDO2 / passkeys) on every remote-access path, ZTNA replacing always-on VPN where feasible, and continuous penetration testing of the remote-access stack.
Which CVEs should I patch first on my remote-access stack?
Prioritize the CVEs in the CISA Known Exploited Vulnerabilities catalog that affect your edge devices. As of April 2026 the highest-priority KEV-listed remote-access CVEs are CitrixBleed (CVE-2023-4966), CitrixBleed 2 (CVE-2025-5777), Ivanti Connect Secure (CVE-2025-0282 and CVE-2025-0283, with the RESURGE malware variant defeating naive mitigations), FortiOS SSL VPN (CVE-2024-21762, CVE-2024-23113, CVE-2024-55591), FortiManager (CVE-2024-47575), Cisco ASA / FTD (CVE-2025-20333, CVE-2025-20362, CVE-2025-20363), and F5 BIG-IP APM (CVE-2025-53521). Each is verified actively exploited in the wild. The median time between disclosure and mass exploitation against edge devices in the Verizon 2025 DBIR is zero days, so a 30-day patch SLA is operationally insufficient; treat KEV-listed remote-access CVEs as zero-day equivalents and patch within 72 hours.
How much do remote-work breaches cost in 2026?
The IBM 2025 Cost of a Data Breach Report places the global average breach cost at US$4.44M and the US average at a record US$10.22M. IBM does not publish a remote-work-specific delta in 2025, but reports shadow AI as a factor in 20% of breaches, adding US$670,000 to the average breach cost. Insurance-claims data from At-Bay show an average ransomware demand of US$958K against organizations in 2025. Named incident records: Change Healthcare cost UnitedHealth Group more than US$2.8 billion by mid-2025; MGM 2023 cost approximately US$100M; the PowerSchool breach is still in progress with district-level extortion demands ongoing as of mid-2025. The expensive failure mode in 2026 is not the breach itself, it is the operational downtime, customer notification, regulatory reporting, and class-action litigation that follow.
Should I replace my VPN with ZTNA in 2026?
For greenfield remote-access deployments, yes. Gartner forecasts at least 70% of new remote-access deployments will rely on ZTNA rather than VPN services by 2025. ZTNA replaces network-layer trust (any VPN-connected user reaching any network-reachable resource) with application-layer trust (this user, on this device, can reach this specific application). For brownfield environments with a large Citrix or F5 BIG-IP estate, the migration is typically incremental: migrate user-to-app traffic to ZTNA first, leave legacy admin and partner connectivity on the legacy concentrator, and aggressively segment what remains. Cloudflare Access, Zscaler Private Access, Twingate, Tailscale, Microsoft Entra Private Access, and Cisco Secure Access dominate the new-deployment market. The control to layer on top of either VPN or ZTNA is conditional access binding sessions to managed devices and current OS patch level.
What is phishing-resistant MFA and why does it matter for remote work?
Phishing-resistant MFA is multi-factor authentication that cannot be defeated by an attacker-in-the-middle reverse proxy phishing the OAuth dance. The two production-ready options in 2026 are FIDO2 / WebAuthn hardware keys (YubiKey 5, Google Titan) and platform passkeys (Apple, Google, Microsoft passkeys synced via the platform's secure element). Microsoft attributes 80% of MFA-bypass breaches to AiTM session-token theft and reports the Tycoon2FA AiTM kit accounting for ~62% of all phishing it blocked by mid-2025. Push-notification MFA, SMS-OTP MFA, and TOTP MFA all fall to AiTM. Phishing-resistant MFA on every remote-access path (VPN, SSO, customer-support portal, cloud-data-warehouse admin, identity-provider admin) is the 2026 defender baseline. NIST SP 800-63-4, finalized in July 2025, now requires multi-factor authentication to offer a phishing-resistant option as a built-in choice.
How do attackers use help-desk vishing in remote-work environments?
Help-desk vishing is the technique whereby an attacker, having researched a target employee via LinkedIn or social-media enumeration, calls the IT help desk impersonating that employee and walks the help-desk operator through a credential reset. CrowdStrike's 2025 Global Threat Report documented at least six distinct help-desk-impersonation campaigns through 2024 and a 442% rise in vishing between H1 and H2 2024. The canonical 2023 example is the Scattered Spider attack on MGM Resorts, in which a 10-minute phone call to MGM's IT help desk gained the attackers administrator privileges in MGM's Okta and Azure tenant environments and ultimately cost MGM approximately US$100M. The defender pattern: out-of-band callback verification on every credential reset, ticket-based identity proofing that the help desk cannot bypass, employee-identity-proofing software with second-factor verification before resetting MFA, and operational segmentation between help-desk privilege and identity-provider admin. Stingrai's Social Engineering Statistics 2026 covers the full vishing channel.
What should I do about BYOD in 2026?
Three options, in increasing order of control. First, ban personal-device access to corporate data outright and issue corporate-managed laptops to every remote worker. This is the highest-control, highest-cost option and is the standard for regulated industries. Second, allow BYOD but enforce device-posture checks via MDM (Microsoft Intune, Jamf, Workspace ONE) on every remote-access path: managed device, current OS patch level, EDR agent installed, full-disk encryption enabled. Conditional-access policies block any device that fails posture. Third, allow personal-device access only via a secure browser (Island, Talon, Chrome Enterprise Premium, Microsoft Edge for Business) that contains corporate data inside a managed browser session, with no full MDM enrollment of the device. Most mid-market enterprises will end up with a mix of all three, segmented by data sensitivity. The risk to avoid: an unmanaged personal laptop hosting an infostealer that harvests corporate credentials, the Snowflake / UNC5537 pattern.
How does Stingrai test remote-access security in a PTaaS engagement?
A Stingrai PTaaS engagement on the remote-access stack typically covers external attack-surface enumeration (continuous, via passive and active discovery), VPN concentrator and SSL VPN headend testing (CVE chain validation, firmware version drift, configuration audit), identity-provider and SSO portal testing across Okta / Microsoft Entra ID / Google Workspace / Ping, conditional-access policy validation, AiTM session-token-theft simulation against MFA configurations, help-desk vishing simulation against the credential-reset workflow, customer-support remote-tool testing, and cloud-data-warehouse and SaaS-tenant configuration audit. Findings ship continuously into the customer's ticketing system. Compliance alignment includes SOC 2, ISO 27001, HIPAA, PCI DSS 4.0, NIST SP 800-53 and 800-171, DORA, and NIS2. Stingrai's offensive team has published 18 CVEs and holds OSCE3, OSCP, OSWE, OSED, OSEP, CREST CRT, CISSP, CRTO, GCPN, CRTE, and eWPTX certifications. See Stingrai PTaaS for engagement detail.
Where can I get the latest remote-work security data?
Track the Verizon Data Breach Investigations Report (annual, May), the IBM Cost of a Data Breach Report (annual, July), Coalition Cyber Claims Report (annual, Q1), At-Bay InsurSec Report (annual, Q1 / Q2), Sophos State of Ransomware (annual, June), Mandiant M-Trends (annual, March), Microsoft Digital Defense Report (annual, October), CrowdStrike Global Threat Report (annual, February), the ENISA Threat Landscape (annual, October), and CISA Known Exploited Vulnerabilities catalog (continuous). The references list at the end of this post numbers every named primary publisher used for the data above; track each annually for full-year telemetry on remote-work-attacker behavior.
References
Verizon 2025 Data Breach Investigations Report and Executive Summary PDF, May 2025. 22,052 incidents and 12,195 confirmed breaches, November 2024 to October 2025.
IBM Cost of a Data Breach Report 2025, July 2025. Ponemon-led research with 600+ breached organizations.
IBM "2025 Cost of a Data Breach Report: Navigating the AI rush", July 2025.
Coalition 2025 Cyber Claims Report, Spring 2025.
Coalition Cyber Threat Index 2025, March 2025.
At-Bay 2026 InsurSec Report, April 2026.
At-Bay 2025 InsurSec Press Release, April 2025.
Sophos State of Ransomware 2025, June 2025. Survey of 3,400 IT/security leaders, 17 countries.
Sophos State of Ransomware 2025 blog, June 2025.
Mandiant M-Trends 2026, March 2026. ~450,000 hours of incident-response data, CY2025.
Mandiant M-Trends 2025, April 2025.
Mandiant UNC5537 Snowflake Investigation, June 2024.
Mandiant FortiManager Zero-Day Investigation (CVE-2024-47575), 2024.
Microsoft Digital Defense Report 2025, October 2025.
Microsoft Digital Defense Report 2025 PDF, October 2025.
Microsoft "Inside Tycoon2FA", March 2026.
CrowdStrike 2026 Global Threat Report, February 2026.
CrowdStrike 2025 Global Threat Report, February 2025.
CrowdStrike 2025 Threat Hunting Report, August 2025.
ENISA Threat Landscape 2025, October 2025. 4,875 incidents, July 2024 to June 2025.
CISA Ivanti Connect Secure Alert (CVE-2025-0282 / 0283), January 2025.
CISA Joint Advisory AA25-022A: Ivanti Cloud Service Applications, January 2025.
CISA Guidance for CVE-2023-4966 (CitrixBleed), November 2023.
CISA Fortinet Post-Exploitation Advisory, April 2025.
CISA Zero Trust Maturity Model 2.0, April 2023.
NIST SP 800-46 Rev 2 Guide to Enterprise Telework, July 2016.
NIST SP 800-46 Rev 3 (Pre-Draft Call), 2020-active.
NIST SP 800-207 Zero Trust Architecture, August 2020.
NIST SP 800-63-4 finalization announcement, July 2025.
Arctic Wolf "Updates on CitrixBleed 2 (CVE-2025-5777)", 2025.
Hadrian "F5 BIG-IP APM CVE-2025-53521 Active Exploitation", March 2026.
Tenable "CVE-2025-20333 / 20362 Cisco ASA Zero-Days FAQ", 2025.
Tenable "Verizon DBIR Snapshot", April 2025.
BleepingComputer "Change Healthcare hacked using stolen Citrix account with no MFA", 2024.
TechCrunch "Change Healthcare hackers broke in using stolen credentials and no MFA", April 2024.
TechTarget "PowerSchool data breach: Explaining how it happened", 2025.
Wikipedia "Snowflake data breach" (consolidated public-record reference).
Wikipedia "Scattered Spider" (consolidated public-record reference).
FIDO Alliance Passkeys Resource Hub, continuous.
Stingrai sibling research: Compromised Credential Statistics 2026, Phishing Statistics 2026, Insider Threat Statistics 2026, IoT Attack Statistics 2026, Vulnerability Statistics 2026, SIM Swap Statistics 2026, Top Industries Targeted by Hackers 2026, Social Engineering Statistics 2026, Best PTaaS Providers 2026.