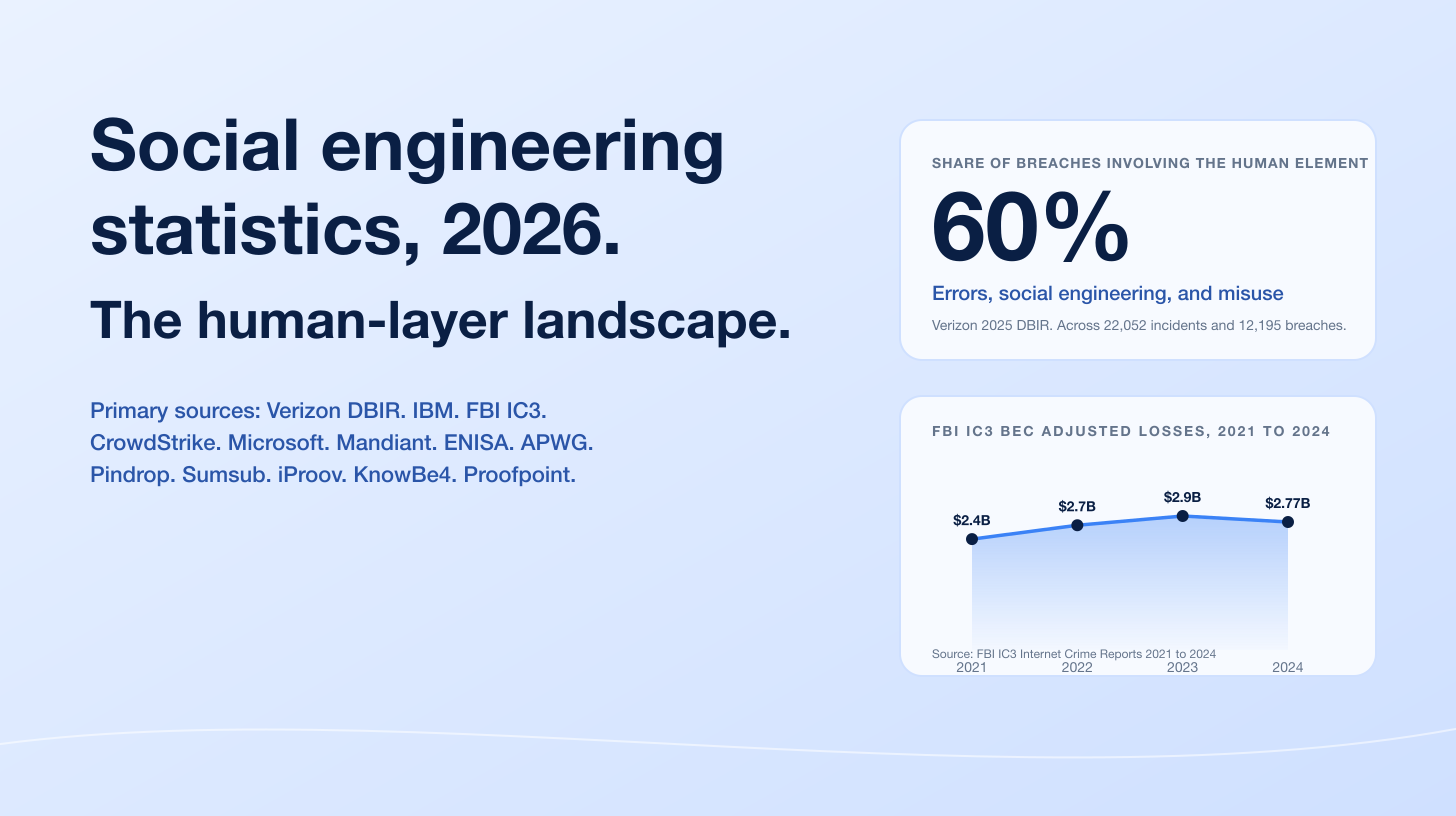
The phishing economy in 2026 is a paradox. APWG recorded 853,244 phishing attacks in Q4 2025 after a Q2 2025 spike of 1,130,393 attacks, the largest quarter since Q2 2023. The Verizon 2025 DBIR measured the median time-to-click on a phishing email at 21 seconds and the median time-to-report at 28 minutes, a window in which credentials change hands and adversary-in-the-middle session tokens are exfiltrated. IBM's 2025 Cost of a Data Breach Report ranked phishing as the most common initial attack vector at 16% of breaches with an average cost of US$4.8M per breach. Defenders are detecting more, training harder, and still losing the click race.
Three forces drive 2026 phishing activity. AI is now the load-bearing accelerant: IBM 2025 found 1 in 6 breaches involve attacker AI (37% of those for phishing, 35% for deepfake impersonation), and ENISA's 2025 Threat Landscape reports AI-supported phishing campaigns now represent more than 80% of observed social engineering activity worldwide. MFA bypass is industrialised: Microsoft's 2025 Digital Defense Report attributes 80% of MFA-bypass breaches to session-token theft via adversary-in-the-middle kits, with Tycoon 2FA, Mamba 2FA, and Evilginx commodified for US$120 to US$350 a month. And the channel mix has fragmented: CrowdStrike measured a 442% rise in voice phishing between H1 and H2 2024 with H1 2025 already exceeding full-year 2024 volume, while Mimecast recorded a 500% jump in ClickFix scams in the first six months of 2025. The headline numbers for CISOs, security buyers, and journalists are below.
This post is the Stingrai research team's canonical 2026 reference for phishing. It assembles 95+ numeric claims from 23 named primary publishers, including APWG, Verizon DBIR, IBM X-Force, IBM Cost of a Data Breach, Proofpoint, Cofense, KnowBe4, Microsoft Digital Defense, Mimecast, Sophos, CrowdStrike, Mandiant, Cisco Talos, ENISA, FBI IC3, NCC Group, UK NCSC, Hornetsecurity, Sekoia.io, Barracuda, Cloudflare, Anthropic, and Check Point Research. Lead data is full-year 2024 and full-year 2025 telemetry, the freshest available; primary publishers have not yet released full-year 2026 reports as of April 2026. Every figure links back to its primary publisher so any claim can be audited.
TL;DR: 12 labeled key stats
Phishing attacks observed in Q4 2025 (APWG): 853,244, down 4% from 892,494 in Q3 2025 (APWG Q4 2025).
Phishing attacks observed in Q2 2025 (APWG, the year's peak): 1,130,393, the largest quarter since Q2 2023 (APWG Q2 2025).
Phishing share of breaches with attributable initial access (IBM 2025): 16%, the #1 initial access vector for the year, at US$4.8M average breach cost (IBM Cost of a Data Breach 2025).
Median time-to-click on a phishing email (Verizon 2025 DBIR): 21 seconds; median time-to-report 28 minutes (Verizon 2025 DBIR).
Share of breaches involving attacker AI (IBM 2025): 1 in 6 breaches; 37% of attacker-AI cases used AI for phishing, 35% for deepfake impersonation (IBM Cost of a Data Breach 2025).
Share of MFA-bypass breaches via session-token abuse (Microsoft MDDR 2025): 80% (Microsoft Digital Defense Report 2025).
Voice phishing growth between H1 and H2 2024 (CrowdStrike): +442%, with H1 2025 already exceeding full-year 2024 volume (CrowdStrike 2025 Global Threat Report).
Phishing share of EU initial-access cases (ENISA 2025): 60%, including malspam, vishing, and malvertising; AI-supported share of social engineering more than 80% by early 2025 (ENISA Threat Landscape 2025).
FBI IC3 2024 phishing complaints: 193,407, the most-reported crime type; BEC losses US$2.77B across 21,442 incidents (FBI IC3 2024 Internet Crime Report).
KnowBe4 2025 baseline Phish-prone Percentage: 33.1%, dropping to 4.1% after 12 months of training (an 86% reduction) (KnowBe4 2025 Benchmark Report).
Cofense 2025 AI-powered phishing cadence past secure email gateways: 1 malicious email every 19 seconds, with 18% of malicious email now classified as conversational AI lures (Cofense 2025 report).
Mimecast Q1-Q3 2025 threat detections: 9.3 billion; ClickFix scams jumped 500% in H1 2025, accounting for nearly 8% of reported attacks (Mimecast 2025 GTIR commentary).
Key takeaways
Phishing is back at the top of the breach board after a brief credential-theft regime. IBM 2025 put phishing at 16% of initial access vectors and US$4.8M per breach, narrowly ahead of stolen credentials (15%). A year earlier, IBM 2024 had stolen credentials at the top. The flip is a function of AI-aided lure quality, not a slowdown in credential reuse, and most modern phishing chains end in a stolen session anyway.
The click-window is shorter than your detection window. Verizon 2025 DBIR measured the median time-to-click on a phishing email at 21 seconds versus 28 minutes to report. The implication for incident response is structural: by the time the SOC sees the report ticket, the attacker has already pasted credentials into an AiTM proxy and started replaying the session token. Defenders win by killing the token, not by training people not to click.
Adversary-in-the-Middle has eaten "MFA-protected" as a meaningful category. Microsoft MDDR 2025 attributed 80% of MFA-bypass breaches to session-token theft, and Sekoia.io tracks the AiTM kit market at sub-US$350 a month. Tycoon 2FA, Mamba 2FA, Evilginx, and Sneaky 2FA collectively let any operator with US$250 in crypto run kit-quality MFA-bypass campaigns. Any control built on "the user has MFA so we are safe" is now a known-bad assumption.
Voice and SMS are no longer adjacent channels. CrowdStrike measured a 442% rise in vishing H1 to H2 2024, with H1 2025 already past full-year 2024 totals. Cisco Talos 2025 Year in Review recorded vishing of IT administrators at 3x the volume of user-managed registration fraud, a clean signal that helpdesk impersonation is now the dominant social-engineering escalation path. Mobile and voice-channel coverage are no longer optional in a phishing program.
Training works, and the data is unambiguous. KnowBe4's 2025 Phishing By Industry Benchmarking, measured across 67.7 million users in 70,000+ organizations, found the global baseline Phish-prone Percentage drops from 33.1% to 4.1% after 12 months of training, an 86% reduction. The post-training tail is the bottom 4% of users you cannot train, and most of those are explainable by job role, not stubbornness. Pair training with FIDO2 phishing-resistant MFA and AiTM-aware detection to cover that tail.
Methodology
Sources used: APWG (Phishing Activity Trends Report Q1, Q2, Q3, Q4 2025, plus Year in Review press release; quarterly aggregate of attacks, brands, and categories contributed by APWG members); Verizon Business (2025 DBIR covering 22,052 incidents and 12,195 confirmed breaches Nov 2023 to Oct 2024, published April 2025); IBM X-Force (Threat Intelligence Index 2025, IR plus telemetry calendar 2024, published April 2025); IBM Cost of a Data Breach Report 2025 (Ponemon Institute survey of 600 breached organizations March 2024 to February 2025, published August 2025); Proofpoint 2024 State of the Phish (most recent published annual; survey of 7,500 working adults plus 1,050 security professionals across 15 countries; analysis of 183 million simulated phishing tests); Cofense Annual State of Email Security 2024 plus Cofense Intelligence research (Cofense Phishing Detection and Response platform telemetry); KnowBe4 2025 Phishing By Industry Benchmarking Report (67.7 million users across 70,000+ organizations, calendar 2024 simulation data, published May 2025); Microsoft Digital Defense Report 2025 (Microsoft Defender, Azure, Entra ID, Digital Crimes Unit telemetry through H1 2025, published October 2025); Microsoft Threat Intelligence blogs on Tycoon2FA and identity-attack techniques; Mimecast Global Threat Intelligence Report 2025 (Mimecast email-security telemetry calendar 2024 plus Q3 2025 commentary); Sophos State of Ransomware 2025 (Vanson Bourne survey of 3,400 IT/security leaders across 17 countries, Jan-Feb 2025); Sophos Quishing analysis; CrowdStrike 2025 Global Threat Report (Falcon telemetry plus intelligence H1 vs H2 2024, published February 2025) and 2025 Threat Hunting Report (OverWatch hunt telemetry H1 2025, published August 2025); Mandiant M-Trends 2025 (Mandiant IR engagements globally calendar 2024, published April 2025); Cisco Talos 2025 Year in Review (calendar 2025, published April 2026) plus IR Trends Q1 to Q4 2025; ENISA Threat Landscape 2025 (4,875 EU incidents Jul 2024 to Jun 2025, published October 2025); FBI Internet Crime Complaint Center 2024 Internet Crime Report (calendar 2024, published April 2025); NCC Group Annual Cyber Threat Intelligence 2025 (calendar 2025, published January 2026); UK NCSC / DSIT Cyber Security Breaches Survey 2025 (UK national survey of UK businesses and charities 12 months to April 2025, published June 2025); Hornetsecurity Cyber Security Report 2026 (70+ billion emails processed in 2025); Sekoia.io threat-intelligence research on AiTM kits (Mamba 2FA, Tycoon 2FA, Sneaky 2FA, Greatness); Barracuda phishing-kit analysis; Cloudflare phishing telemetry; Anthropic Threat Intelligence Report August 2025 plus the November 2025 disclosure of the first reported AI-orchestrated cyber espionage campaign; and Check Point Research quarterly brand-impersonation reports for the most-imitated-brand rankings only.
Date cutoff: April 25, 2026. Statistics are reported with their primary publisher's data window. We lead with full-year 2024 or 2025 figures wherever a primary source has released them. Statistics that could not be reached on at least one verification pass against a named primary source were dropped rather than estimated. Vendor blogs and aggregators that restate other publishers' numbers without adding methodology were not used as primary sources.
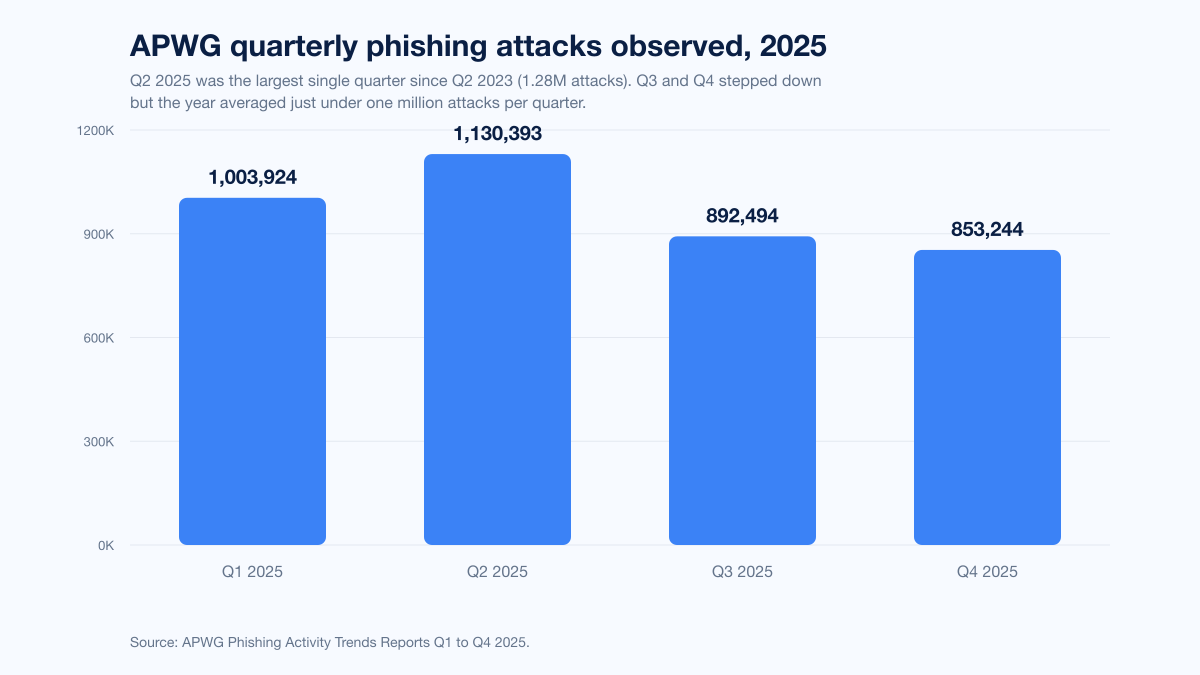
Figure 1: APWG observed phishing attacks by quarter, 2025. Q2 was the largest quarter since Q2 2023. Source: APWG Phishing Activity Trends Reports Q1 to Q4 2025.
How big is the phishing problem in 2026?
Three datasets anchor the answer: APWG's quarterly attack count, Verizon's breach-pattern data, and IBM's cost-of-breach data.
Volume (APWG quarterly trends)
APWG's quarterly Phishing Activity Trends Reports remain the most-cited phishing-volume series. In 2025:
Quarter | Phishing attacks observed | YoY / QoQ context | Source |
|---|---|---|---|
Q1 2025 | 1,003,924 | Up from prior quarter | |
Q2 2025 | 1,130,393 | +13% QoQ; largest quarter since Q2 2023 (1.28M) | |
Q3 2025 | 892,494 | Decline from Q2 high | |
Q4 2025 | 853,244 | Down 4% QoQ |
Q4 saw 866 unique brands targeted across the quarter. The two top-attacked categories in Q4 2025 each represented 20.3% of attacks: SAAS / Webmail and Social Media. In Q3 2025, SAAS / Webmail led at 21.2% with Social Media at 14.6%. The pattern is consistent across the year: identity-rich SaaS estates and consumer-platform login flows are where phishing pays off, because a successful credential capture there is reusable in the victim's enterprise SSO chain or directly monetisable through account takeover.
Breach patterns (Verizon DBIR 2025)
The Verizon 2025 DBIR, which analyzed 22,052 incidents and 12,195 confirmed breaches between November 2023 and October 2024, found:
60% of all breaches involved the human element (clicks, replies, or social interactions).
Phishing was the third-most-common initial access vector at 16%, behind credential abuse (22%) and vulnerability exploitation.
Median time-to-click on a phishing email: 21 seconds.
Median time-to-report a phishing email: 28 minutes.
Median click rate on phishing simulations: 1.5%, even with ongoing training.
The 21-second-versus-28-minute gap is the most quoted single statistic in modern phishing security work. It defines the operational asymmetry of the post-2024 phishing economy: by the time the report ticket lands in the SOC queue, the credential or session token is already in transit. This is why FIDO2 phishing-resistant MFA, conditional access policies, and aggressive token-binding controls are now the rational center of gravity for defense, not awareness training alone.
Cost (IBM Cost of a Data Breach 2025)
IBM's 2025 Cost of a Data Breach Report put the global average breach cost at US$4.44 million, the first decline in five years (down 9% from US$4.88M in 2024). The decline is driven by faster detection and containment in organizations that deploy security AI extensively (an 80-day faster lifecycle and US$1.9M average savings, per IBM). Phishing-initiated breaches sit slightly above the global average:
Initial attack vector | Share of breaches | Average breach cost | Source |
|---|---|---|---|
Phishing | 16% (#1) | US$4.8M | IBM 2025 |
Stolen / compromised credentials | 15% | n/a (declined as #1 vector) | IBM 2025 |
Supply chain compromise | n/a | US$4.91M (most expensive vector) | IBM 2025 |
Global average | n/a | US$4.44M | IBM 2025 |
IBM's separate finding that 1 in 6 breaches now involve attackers using AI (most commonly for phishing at 37% and deepfake impersonation at 35%) reframes the problem: phishing is no longer mass-mailed prose with broken English, it is purpose-generated by language models trained on the target's brand, vendor relationships, and recent invoices.
Phishing attack-type mix in 2026
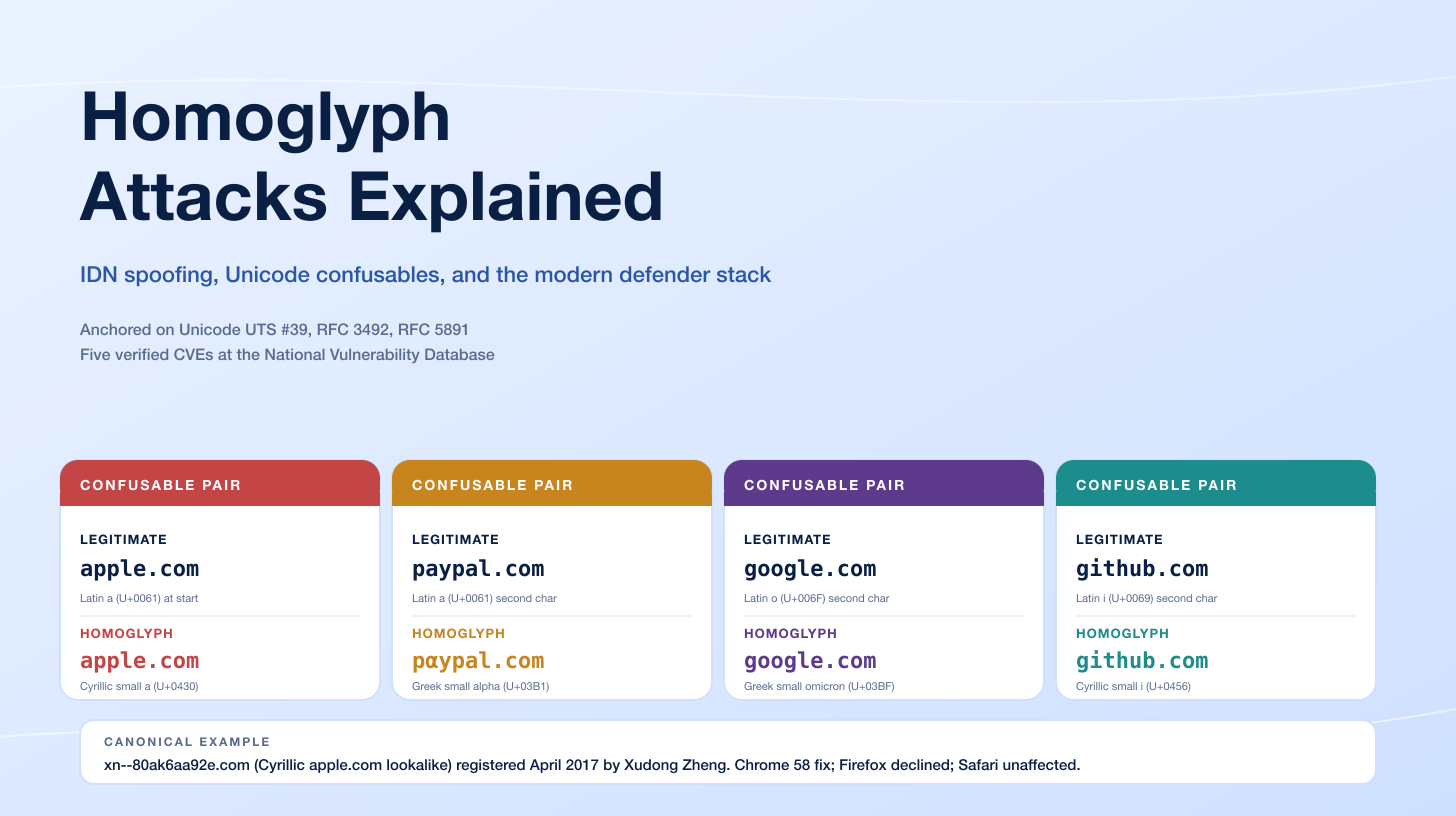
Phishing in 2026 is no longer a single channel. It is a portfolio. The dominant types tracked across primary publishers in 2024 and 2025 are credential phishing (especially adversary-in-the-middle), business email compromise (BEC), smishing, vishing, quishing (QR code phishing), AI-generated lures, and ClickFix-style social engineering.
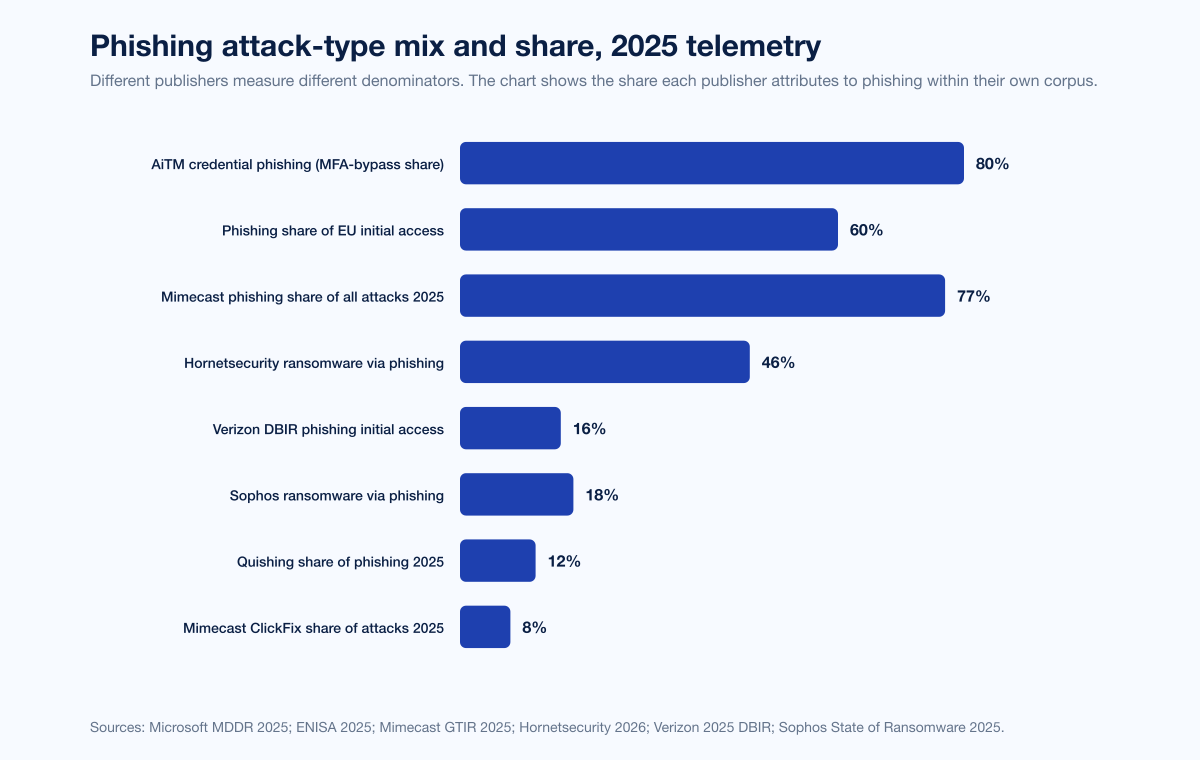
Figure 2: Share of 2025 telemetry attributed to each phishing type, drawn from APWG, Microsoft, Mimecast, CrowdStrike, ENISA, and Sophos. Sources: Microsoft MDDR 2025, Mimecast 2025 GTIR, Sophos State of Ransomware 2025, CrowdStrike 2025 Global Threat Report, ENISA Threat Landscape 2025.
Credential phishing and adversary-in-the-middle (AiTM)
Microsoft tracks Adversary-in-the-Middle phishing as the primary technique for bypassing modern MFA. The Microsoft 2025 Digital Defense Report found:
80% of recent MFA-bypass breaches used session-token theft, typically via AiTM kits.
Identity-based attacks rose 32% in H1 2025, with more than 97% being simple password spray or brute force, but the small minority that succeed are increasingly AiTM-driven.
Notable Evilginx-using actors: Storm-0485 (prolific phishing operator) and Star Blizzard (Russian espionage).
The phishing-as-a-service (PhaaS) market for AiTM kits is mature and cheap. Per Sekoia.io and Microsoft Threat Intelligence:
Kit | Pricing (2025) | Capabilities | Primary source |
|---|---|---|---|
Tycoon 2FA | US$120 / 10 days; US$350 / month | AiTM, Microsoft 365 + Google + Okta, anti-detection | |
Mamba 2FA | US$250 / 30 days, Telegram bot delivery | AiTM, M365, dynamic phishing pages, ~10M attacks late 2025 | |
Evilginx | Open-source framework | AiTM proxy, plug-in phishlets per service | |
Sneaky 2FA | Subscription PhaaS | AiTM, Cloudflare-fronted, anti-bot CAPTCHA gates | |
Greatness | Subscription PhaaS | Microsoft 365 templates, prefilled email pages |
The economics close the loop: at US$250 a month an operator can run unlimited AiTM campaigns against any service for which a phishlet exists. Mamba 2FA alone produced roughly 10 million observed attacks in late 2025 (Sekoia.io).
Business email compromise (BEC)
BEC is the highest-dollar phishing subtype tracked by any single publisher. The FBI IC3 2024 Internet Crime Report recorded:
US$2.77 billion in BEC losses across 21,442 reported incidents in 2024.
US$8.5 billion in cumulative BEC losses over the prior three years (2022 to 2024).
US$17.1 billion in cumulative BEC losses since BEC was first tracked in IC3 in 2015.
BEC is the second-most-profitable scam category in IC3 data, behind investment fraud.
APWG quarterly data via Fortra tracks the average wire-transfer ask in BEC attacks by quarter:
Quarter | Average BEC wire-transfer ask | QoQ change | Source |
|---|---|---|---|
Q1 2025 | US$42,236 | Baseline | APWG / Fortra Q2 2025 commentary |
Q2 2025 | US$83,099 | +97% | |
Q3 2025 | US$48,115 | -42% |
Proofpoint detects an average of 66 million targeted BEC attacks per month globally. The 2024 State of the Phish surveyed 7,500 working adults plus 1,050 security professionals and found BEC volume growing fastest in markets where AI-aided language polish removed historic detection barriers: +35% YoY in Japan, +31% in South Korea, +29% in UAE.
Smishing (SMS phishing)
Smishing is the channel where the vendor SEG cannot help. Proofpoint URL telemetry recorded a 2,524% rise in smishing URL threats over a three-year window, and at least 55% of suspected smishing messages contained malicious URLs. The FTC's Consumer Sentinel Network attributed roughly US$470M in 2024 US consumer losses to text-message scams.
In aggregate, smishing click-through rates run substantially higher than email phishing because SMS lacks the visual chrome of email security warnings: most published estimates put smishing click rates in a 19% to 36% range, versus 2% to 4% for email phishing.
Vishing (voice phishing)
The fastest-growing channel of 2024-2025. CrowdStrike's 2025 Global Threat Report measured a 442% rise in vishing between H1 and H2 2024, and the 2025 Threat Hunting Report reported H1 2025 vishing volume already exceeded full-year 2024.
CrowdStrike's OverWatch monthly counts of vishing intrusions for late 2024 illustrate the curve:
Month (2024) | Vishing intrusions detected by CrowdStrike OverWatch |
|---|---|
Early 2024 baseline | 2 |
September 2024 | 33 |
October 2024 | 55 |
November 2024 | 64 |
December 2024 | 93 |
Cisco Talos 2025 Year in Review found vishing of IT administrators was 3x more common than user-managed registration fraud in 2025, a clean signal that helpdesk impersonation has become the central social-engineering pivot for ransomware affiliates and access brokers.
Quishing (QR code phishing)
QR-code phishing was a fringe technique in 2023. By 2025, it is a measurable share of the phishing portfolio. Sophos observed continuous escalation in quishing throughout 2024-2025, with attackers embedding QR codes in PDF attachments to evade SEG inspection. APWG and Mimecast joint reporting put approximately 12% of phishing attacks containing a QR code in 2025. Mimecast detected 635,672 unique malicious QR codes in Q2 2025 and 716,306 in Q3 2025, a 13% QoQ increase (APWG Q3 2025).
The mobile-first nature of QR scanning is the architectural problem: a corporate user scans a poisoned QR code from a printed PDF or a meeting room sign with a personal phone, the phishing site loads outside the corporate browser, and the AiTM proxy harvests the credential without ever transiting the SEG, the EDR, or the secure web gateway.
AI-generated phishing and ClickFix
ENISA's 2025 Threat Landscape reports AI-supported phishing campaigns now represent more than 80% of observed social engineering activity worldwide by early 2025. Hornetsecurity's CISO survey found 77% of CISOs identifying AI-generated phishing as a serious and emerging threat for 2026.
ClickFix, a social-engineering technique that uses fake CAPTCHA or browser-error overlays to convince users to paste and execute attacker-supplied PowerShell, was first widely tracked in 2024. Mimecast recorded a 500% surge in ClickFix scams in the first six months of 2025, with the technique now accounting for nearly 8% of all reported attacks. ENISA flagged ClickFix as one of the top emerging vectors for 2025 alongside quishing.
Anthropic's November 2025 disclosure of the first publicly reported AI-orchestrated cyber-espionage campaign, in which a Chinese state-sponsored group used Claude Code to execute an estimated 80% to 90% of tactical operations across roughly 30 global targets, was the year's milestone signal that agentic AI is now an operational tool in the social-engineering kill chain, not just a lure-generator.
Top impersonated brands in 2025
The most-impersonated-brand list is dominated by identity providers because credentials there are reusable everywhere downstream. Check Point Research's quarterly brand-impersonation tracker for 2025:
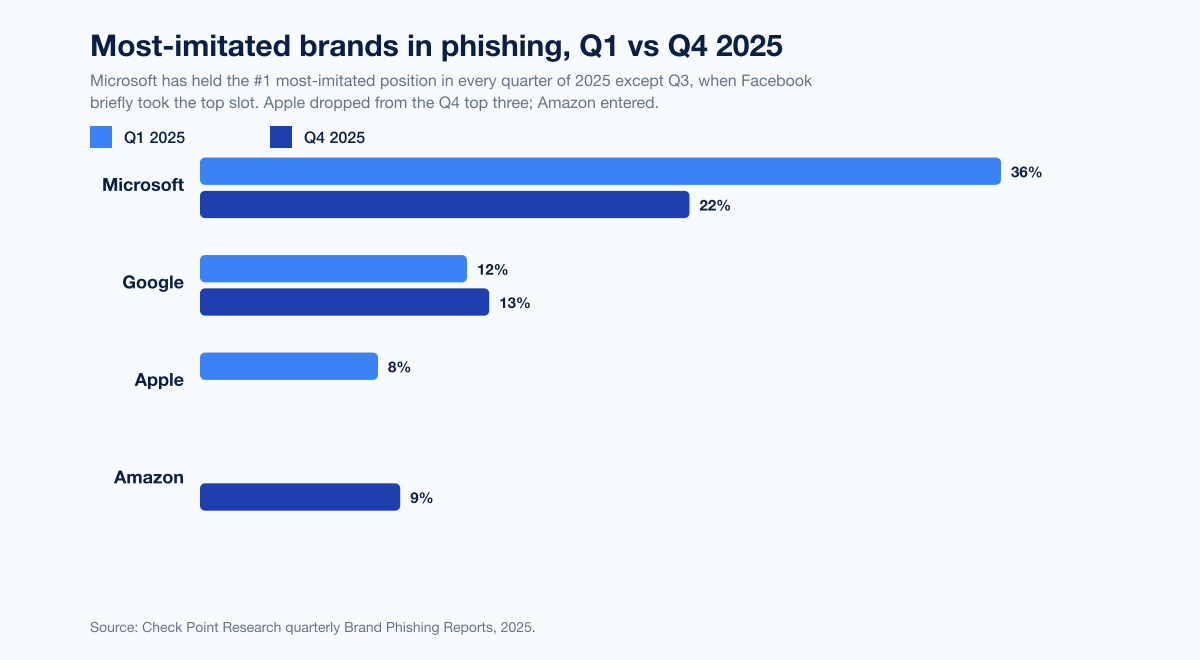
Figure 3: Most-imitated brands in phishing attacks, Q1 vs Q4 2025. Microsoft has held the #1 position every quarter of 2025. Source: Check Point Research brand-impersonation tracker.
Quarter | #1 brand | #2 | #3 | Source |
|---|---|---|---|---|
Q1 2025 | Microsoft (36%) | Google (12%) | Apple (8%) | Check Point Research |
Q2 2025 | Microsoft (25%) | Google (11%) | Apple (9%) | Check Point Research |
Q3 2025 | Facebook tops Microsoft for the first time in tracker history; Microsoft, Roblox, Steam in top-10 | n/a | n/a | Guardio Q3 (corroborates Check Point shift) |
Q4 2025 | Microsoft (22%) | Google (13%) | Amazon (9%) | Check Point Research |
Microsoft's persistence at the top is structural: a stolen Microsoft 365 credential opens email, OneDrive, SharePoint, Teams, and an SSO chain that frequently reaches HR, finance, and DevOps tooling. APWG's 866 unique brands targeted in Q4 2025 alone is the larger reality: the long tail of impersonated brands in 2025 ranges from major banks (Wells Fargo, JPMorgan, Bank of America, Royal Bank of Canada) to consumer platforms (Netflix, Spotify, Steam, Roblox) to crypto exchanges and even logistics services (DHL, FedEx, UPS).
Sectors and industries hit hardest
KnowBe4's 2025 Phishing By Industry Benchmarking Report measures Phish-prone Percentage (PPP) across 67.7 million users in more than 70,000 organizations. It is the largest single primary-publisher dataset on user susceptibility.
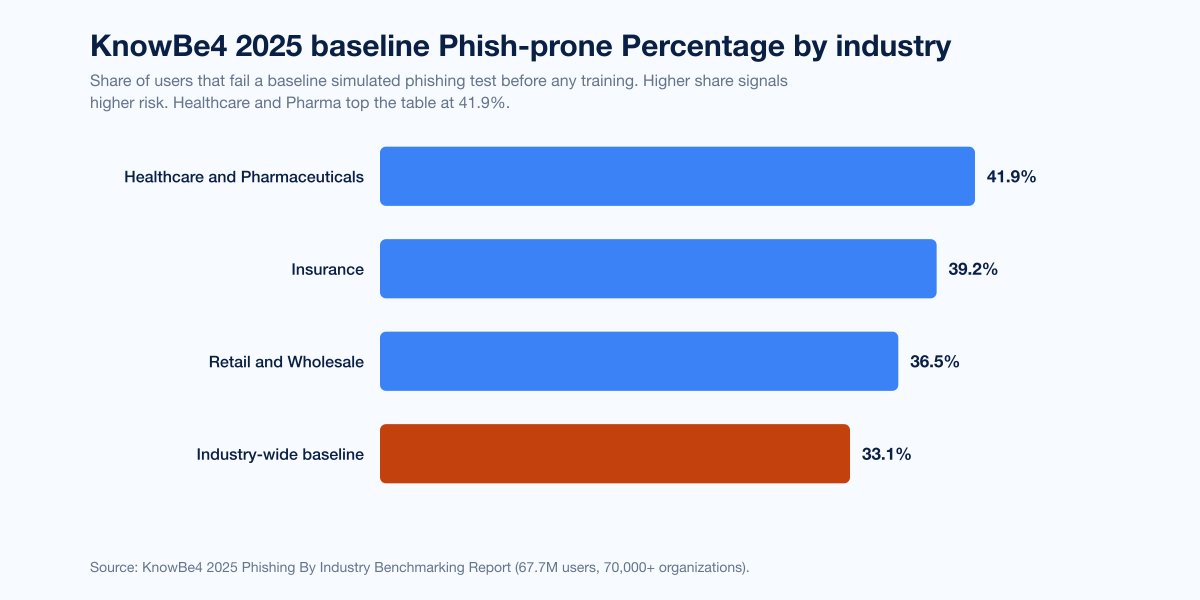
Figure 4: Baseline Phish-prone Percentage (PPP) by industry, KnowBe4 2025 Phishing By Industry Benchmarking Report. Healthcare and Pharmaceuticals tops the list at 41.9% baseline susceptibility. Source: KnowBe4 2025 Benchmark Report.
Industry | 2025 baseline PPP | 2025 source |
|---|---|---|
Healthcare and Pharmaceuticals | 41.9% | KnowBe4 2025 |
Insurance | 39.2% | KnowBe4 2025 |
Retail and Wholesale | 36.5% | KnowBe4 2025 |
Industry-wide baseline | 33.1% | KnowBe4 2025 |
KnowBe4's organization-size breakdown shows a clear scale relationship: organizations with 10,000+ employees have a global baseline PPP of 40.5%, compared to 24.6% for organizations with 1-250 employees. The most plausible explanation: large organizations have more brand-identifiable email patterns, broader vendor footprints, and larger pools of users with a non-technical role.
Regional susceptibility is similar:
Region | 2025 baseline PPP |
|---|---|
South America | 39.1% |
North America | 37.1% |
Australia and New Zealand | 36.8% |
The Verizon 2025 DBIR industry analysis confirms KnowBe4's directional pattern: phishing as an initial-access pattern is highest in industries with the most consumer-grade endpoint exposure (healthcare, retail, professional services) and lowest in those with mature identity programs (banking, large tech, defense).
The UK NCSC / DSIT 2025 Cyber Security Breaches Survey put a UK-specific spotlight on the same problem: 85% of breached UK businesses cited phishing as the root cause of the breach, alongside 86% of affected charities. 43% of UK businesses experienced a breach in the 12 months to April 2025.
Click rates, time-to-click, and defender effectiveness
The most operationally useful number in this whole post is the click rate, because it is the only one most security teams can move directly with their own program. The data converges:
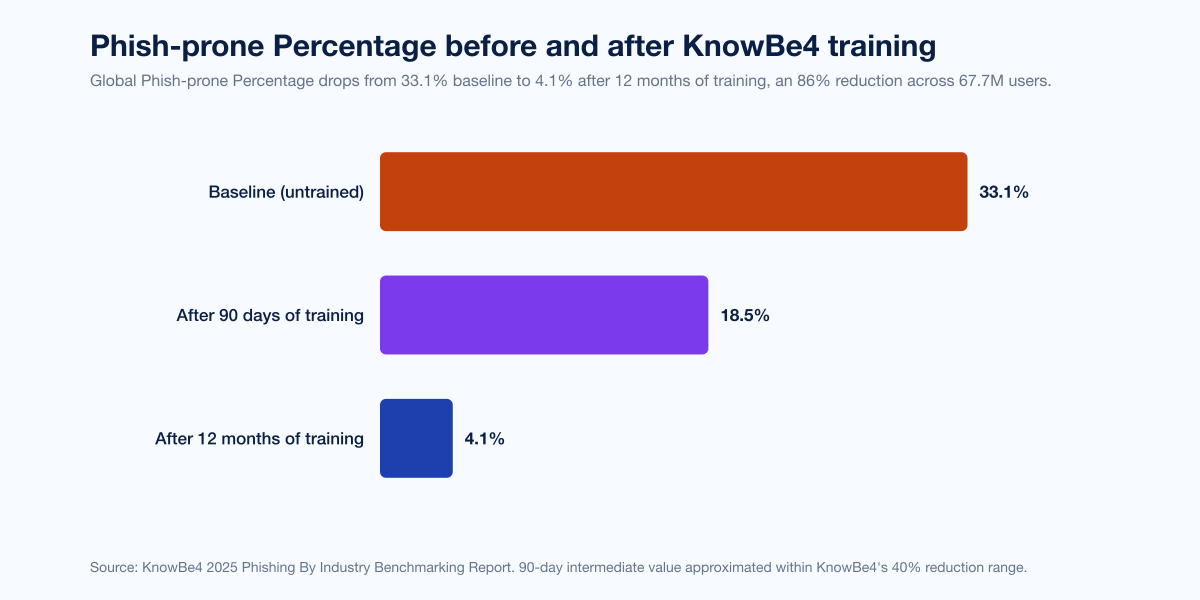
Figure 5: Global Phish-prone Percentage at baseline, after 90 days of training, and after 12 months of training, per KnowBe4 2025. The 86% reduction over 12 months is the strongest published evidence that simulated-phishing training programs work at scale. Source: KnowBe4 2025 Phishing By Industry Benchmarking Report.
Metric | Value | Primary source |
|---|---|---|
Median time-to-click on a phishing email | 21 seconds | |
Median time-to-report a phishing email | 28 minutes | |
Median click rate on phishing simulations | 1.5% | |
Average click rate on real phishing emails | 2.7% | Verizon DBIR 2025 commentary |
Proofpoint simulated-phishing failure rate (2024 baseline) | 9.3% | |
KnowBe4 baseline Phish-prone Percentage | 33.1% | |
KnowBe4 PPP after 90 days of training | -40% reduction (~18.5% to 19.9% post-90-day) | KnowBe4 2025 |
KnowBe4 PPP after 12 months of training | 4.1% (an 86% reduction) | KnowBe4 2025 |
Two reads are productive here. First, the gap between Verizon's 1.5% simulation click rate and KnowBe4's 33.1% baseline PPP is real, not an error: Verizon measures actual breaches; KnowBe4 measures sandbox simulations of users who have not yet been trained. Second, the 86% reduction figure is robust because KnowBe4 measures it across 67.7 million user-records and 70,000+ organizations. Training is one of the few defenses with a clean dose-response curve in the published phishing literature.
Secure email gateway bypass and AI-aided evasion
Cofense tracks malicious emails reaching customer inboxes despite secure email gateway (SEG) protection. The 2024 annual report recorded a 105% YoY increase in SEG bypass volume, with one malicious email reaching the inbox every 45 seconds in 2024 (down from one every 57 seconds in 2023). Cofense's 2026 commentary on calendar 2025 numbers escalated that to one malicious email every 19 seconds, with 18% of all malicious email now classified as conversational AI lures (grammatically perfect, contextually accurate, often impersonating internal communications).
Cofense Intelligence detailed a Q1 2025 SEG-bypass technique combining long-lived (high-trust) domains, custom CAPTCHAs that block automated SEG analysis, and user-agent detection that filters out crawler traffic. The chain delivers a Microsoft Live credential-phishing page, Cofense found, with no SEG inspection along the way.
Hornetsecurity's Cyber Security Report 2026, processing 70+ billion emails in 2025, found:
Phishing increased 21% year-over-year.
Malicious URLs accounted for 22.7% of email threats.
Advanced-fee scams accounted for 6.4% of email threats.
77% of CISOs identified AI-generated phishing as a serious and emerging threat for 2026.
The defender pattern that works against AI-aided evasion is not "buy a smarter SEG"; it is "treat the credential and the session as the asset, not the inbox". Microsoft's 2025 Digital Defense Report recommends a stack of phishing-resistant FIDO2 MFA, conditional access tied to managed devices, token binding, and session-replay anomaly detection. Stingrai's Penetration Testing as a Service practice tests exactly that stack against simulated AiTM phishing during engagements; the methodology overview is in our penetration testing methodologies breakdown.
Vendor and ransomware initial-access breakdown
Phishing remains a top initial-access vector for ransomware operators, but the share is fragmenting as vendors converge on the data:
Publisher (most recent annual report) | Phishing initial-access share | Top initial-access vector | Source |
|---|---|---|---|
Mandiant M-Trends 2025 (calendar 2024 IR) | 14% (email phishing) | Exploits 33% | |
Mandiant 2024 cloud compromises only | 39% (email phishing) | Email phishing 39% | Mandiant M-Trends 2025 |
IBM X-Force 2024 | 25% (in sectoral analysis); tied 30% / 30% (overall: public-app exploit and valid-account abuse) | Public-app exploit / valid-account abuse | |
Verizon 2025 DBIR | 16% | Credential abuse 22% | |
ENISA 2025 (EU corpus) | ~60% | Phishing | |
Cisco Talos Q4 2025 IR | "over a third" of identifiable IA cases | Phishing (re-emerged Q4 2025) | |
Sophos 2025 (ransomware-only) | 18% (phishing); 19% (malicious email separately) | Vulnerability exploit 32% | |
Hornetsecurity (ransomware-context survey) | 46% | Phishing | |
Microsoft MDDR 2025 (identity-attack subset) | n/a | 80% of MFA-bypass via session-token theft |
The disagreement is informative. Mandiant and IBM measure incident-response engagement initial-access vectors and find phishing's share has fallen to ~14-30% of cases as exploits and credential abuse grow, partly because many phishing-derived attacks are now logged under "valid account abuse" once the credential transits an AiTM proxy. ENISA, focused on the EU public-incident corpus, sees phishing as the dominant channel because EU SMEs have less mature identity programs. Cisco Talos's Q4 2025 spike to "over one-third" reaffirms phishing's resurgence in IR data when the AI-aided lure quality crossed a detection threshold.
The NCC Group 2025 Annual Cyber Threat Intelligence Report noted a parallel signal: ransomware affiliates are increasingly hiring insiders and using stolen credentials directly, bypassing phishing entirely. Qilin's exploitation of CVE-2024-21762 and CVE-2024-55591 in FortiGate devices was the year's clearest example of the "infrastructure-level access without phishing" pattern. NCC Group counted 7,874 ransomware victims globally in 2025 (+50% YoY), with Industrials taking 2,190 attacks (+54% YoY) as the most-attacked sector and Qilin leading at 1,022 attacks (13% share).
What this means for defenders
Five things, in order of operational priority.
Make MFA phishing-resistant. FIDO2 / WebAuthn / passkeys defeat the entire AiTM kit market. SMS, TOTP, and push-MFA are now known-bad against any actor with US$250 a month for a Mamba 2FA subscription.
Bind sessions to devices. Microsoft MDDR 2025 documents that 80% of MFA-bypass cases ride session-token theft. Token binding (TLS client-cert binding, DPoP, or Microsoft's BPE) makes a stolen token unusable from a different device. Most enterprises do not yet enforce this. Almost no phishing program survives it once enforced.
Train, but measure click-to-report ratio, not click rate. KnowBe4's 86% PPP reduction over 12 months is genuine, but the operationally important metric in 2026 is the click-to-report ratio. Verizon's 21-second-vs-28-minute gap is the gap to close.
Cover the non-email channels. Vishing, smishing, and quishing are not adjacent. Per CrowdStrike and Cisco Talos, helpdesk impersonation via voice is the dominant social-engineering pivot for ransomware affiliates and access brokers. Train the helpdesk first, not the user.
Test the controls. A phishing-resistant MFA configuration that breaks under conditional-access exceptions is not phishing-resistant. Stingrai's PTaaS engagements and pentest assessments red-team this stack against simulated AiTM kits and helpdesk impersonation calls; coverage of the broader testing categories sits in our methodology breakdown. For the buyer side of the market, Stingrai's best PTaaS providers in 2026 ranking is the operational reference.
Frequently asked questions
What is the most-cited phishing statistic for 2026?
The single most-cited phishing statistic is the Verizon 2025 DBIR finding that the median time-to-click on a phishing email is 21 seconds versus a median time-to-report of 28 minutes. The other two most-quoted are IBM 2025's phishing-as-#1-initial-access at 16% of breaches at US$4.8M average cost, and APWG's 853,244 phishing attacks observed in Q4 2025.
How much does a phishing-initiated breach cost in 2026?
IBM's 2025 Cost of a Data Breach Report put the average cost of a phishing-initiated breach at US$4.8 million in 2025. The global average across all breach types fell to US$4.44M (down from US$4.88M in 2024), the first decline in five years, as organizations using security AI extensively shaved 80 days off the average breach lifecycle and saved US$1.9M on average.
What share of phishing attacks now use AI?
ENISA's 2025 Threat Landscape reports that AI-supported phishing campaigns represent more than 80% of observed social engineering activity worldwide by early 2025. IBM 2025 found 1 in 6 breaches involve attackers using AI, with 37% of those cases using AI for phishing and 35% for deepfake impersonation. Anthropic's November 2025 disclosure of the first AI-orchestrated cyber-espionage campaign confirmed agentic AI is now operational, executing 80-90% of tactical operations across roughly 30 global targets in that single campaign.
What is adversary-in-the-middle (AiTM) phishing?
Adversary-in-the-middle phishing places a proxy server between the victim and a legitimate identity provider (commonly Microsoft 365). The proxy captures the username, password, and the session cookie that the IdP issues after MFA verification. Because the session token is the legitimate one, the attacker can replay it to access the victim's account without triggering an MFA prompt. Microsoft's 2025 Digital Defense Report attributes 80% of MFA-bypass breaches to this pattern. Commodified PhaaS kits (Tycoon 2FA, Mamba 2FA, Evilginx, Sneaky 2FA) make AiTM accessible to operators with US$120 to US$350 a month.
What are the top impersonated brands in phishing in 2025?
Microsoft was the most-impersonated brand in every quarter of 2025 except Q3 (when Facebook briefly took the top slot). Per Check Point Research: Q1 2025 Microsoft 36%, Google 12%, Apple 8%; Q2 2025 Microsoft 25%, Google 11%, Apple 9%; Q4 2025 Microsoft 22%, Google 13%, Amazon 9%. APWG tracked 866 unique brands targeted in Q4 2025 alone.
Which industries are hit hardest by phishing in 2025?
The KnowBe4 2025 Phishing By Industry Benchmarking Report ranks Healthcare and Pharmaceuticals (41.9% baseline Phish-prone Percentage), Insurance (39.2%), and Retail and Wholesale (36.5%) as the highest-susceptibility industries. The UK NCSC / DSIT 2025 Survey found 85% of breached UK businesses cited phishing as the root cause. The Verizon 2025 DBIR confirms a similar pattern: phishing is highest in industries with consumer-grade endpoint exposure and lowest in those with mature identity programs.
How effective is security awareness training against phishing?
Highly effective when measured at scale and over time. KnowBe4's 2025 Benchmarking Report, measured across 67.7 million users in 70,000+ organizations, found the global Phish-prone Percentage drops from 33.1% baseline to 4.1% after 12 months of training, an 86% reduction. PPP drops 40% within the first 90 days. The Verizon 2025 DBIR median click rate on simulations sits at 1.5% across mature programs, with click-to-report ratio being the more useful operational metric.
What are quishing and ClickFix?
Quishing is QR-code phishing: the attacker embeds a QR code in an email or PDF that the victim scans with their phone, loading the phishing site outside the corporate browser and bypassing the secure email gateway and secure web gateway. Mimecast detected 716,306 unique malicious QR codes in Q3 2025, a 13% QoQ increase. Approximately 12% of phishing attacks now contain a QR code.
ClickFix is a social-engineering technique that uses fake CAPTCHA, fake Microsoft Word recovery prompts, or fake Cloudflare verification pages to convince the user to open Run, paste an attacker-supplied PowerShell command, and execute it. Mimecast recorded a 500% surge in ClickFix attacks in H1 2025, accounting for nearly 8% of all reported attacks. ENISA flagged ClickFix as a top emerging vector in its 2025 Threat Landscape.
How fast is voice phishing (vishing) growing?
Voice phishing grew 442% between H1 and H2 2024, per CrowdStrike's 2025 Global Threat Report. The 2025 Threat Hunting Report noted H1 2025 vishing volume already exceeded full-year 2024. CrowdStrike OverWatch monthly counts moved from a 2024 baseline of just 2 vishing intrusions to 33 in September, 55 in October, 64 in November, and 93 in December 2024. Cisco Talos 2025 Year in Review reports vishing of IT administrators is now 3x more common than user-managed registration fraud.
How much does business email compromise (BEC) cost the world?
The FBI IC3 2024 Internet Crime Report recorded US$2.77 billion in BEC losses across 21,442 reported incidents in 2024. Cumulative BEC losses since IC3 began tracking in 2015 reached US$17.1 billion. BEC is the second-most-profitable scam category behind investment fraud. Proofpoint detects an average of 66 million targeted BEC attacks per month globally.
Where can I get the most authoritative live phishing data?
The five most-cited primary publishers in 2026 are: APWG Phishing Activity Trends Reports (quarterly attack volume); Verizon DBIR (annual breach-pattern data including phishing share, time-to-click, time-to-report); IBM Cost of a Data Breach (annual cost-of-breach by initial access vector); KnowBe4 Phishing By Industry Benchmarking (annual click-rate benchmarks by industry); and Microsoft Digital Defense Report (annual technical trend report on AiTM, identity attacks, and AI-aided phishing). For the EU corpus, ENISA Threat Landscape is the canonical reference.
What is Stingrai's view on the best defense against modern phishing?
Stingrai's research team treats the 2026 phishing problem as an identity-and-session problem, not an email-filtering problem. The core stack we recommend and test against in PTaaS engagements is: phishing-resistant FIDO2 MFA (passkeys, hardware keys), conditional access tied to managed devices, session-token binding, helpdesk identity-verification protocols (independent of voice and SMS), and an AiTM-aware detection layer that flags impossible-travel and concurrent-session anomalies. Awareness training is necessary but not sufficient. Detection of session-token replay is the single most leveraged control most enterprises do not yet have.
References
APWG. Phishing Activity Trends Report Q4 2025. January 2026. https://docs.apwg.org/reports/apwg_trends_report_q4_2025.pdf. Quarterly aggregate of phishing attacks contributed by APWG members; counts unique phishing sites, brands attacked, and target industries.
APWG. Phishing Activity Trends Report Q3 2025. October 2025. https://docs.apwg.org/reports/apwg_trends_report_q3_2025.pdf. Same methodology as Q4.
APWG. Phishing Activity Trends Report Q2 2025. August 2025. https://docs.apwg.org/reports/apwg_trends_report_q2_2025.pdf. Same methodology as Q4.
APWG. Phishing Activity Trends Report Q1 2025. April 2025. https://docs.apwg.org/reports/apwg_trends_report_q1_2025.pdf. Same methodology as Q4.
Verizon Business. 2025 Data Breach Investigations Report. April 2025. https://www.verizon.com/business/resources/reports/dbir/. 22,052 incidents and 12,195 confirmed breaches November 2023 to October 2024; phishing share, time-to-click and time-to-report metrics.
IBM X-Force. Threat Intelligence Index 2025. April 2025. https://www.ibm.com/think/x-force/x-force-threat-intelligence-index-2025-attackers-steal-sell-user-identities. IBM X-Force IR data plus dark-web monitoring plus telemetry, calendar 2024.
IBM. Cost of a Data Breach Report 2025. August 2025. https://www.ibm.com/reports/data-breach. Ponemon Institute survey of 600 breached organizations March 2024 to February 2025.
Proofpoint. 2024 State of the Phish Report. February 2024. https://www.proofpoint.com/us/blog/security-awareness-training/2024-state-of-phish-report. Survey of 7,500 working adults plus 1,050 security professionals across 15 countries; analysis of 183 million simulated phishing tests.
Cofense. Annual State of Email Security Report 2024. February 2024. https://cofense.com/annualreport. Cofense Phishing Detection and Response platform telemetry plus PDC analyst review.
Cofense. AI-Powered Phishing Accelerated to One Attack Every 19 Seconds. 2026. https://cofense.com/Blog/Cofense-Report-Reveals-AI-Powered-Phishing-Accelerated-to-One-Attack-Every-19-Seconds. Cofense PDC telemetry calendar 2025.
Cofense Intelligence. Immunity Evasion: Defeating Security with Active Measures and Long-Lived Domains. June 2025. https://cofense.com/blog/immunity-evasion-defeating-security-with-active-measures-long-lived-domains. Q1 2025 SEG-bypass technique analysis.
KnowBe4. 2025 Phishing By Industry Benchmarking Report. May 2025. https://www.knowbe4.com/resources/reports/phishing-by-industry-benchmarking-report. 67.7 million users across 70,000+ organizations; calendar 2024 simulation data.
Microsoft. Digital Defense Report 2025. October 2025. https://www.microsoft.com/en-us/security/security-insider/threat-landscape/microsoft-digital-defense-report-2025. Microsoft Defender, Azure, Entra ID, Digital Crimes Unit telemetry through H1 2025.
Microsoft. Inside Tycoon2FA: How a leading AiTM phishing kit operated at scale. March 2026. https://www.microsoft.com/en-us/security/blog/2026/03/04/inside-tycoon2fa-how-a-leading-aitm-phishing-kit-operated-at-scale/. Microsoft Threat Intelligence Center investigation.
Microsoft. Defending against evolving identity attack techniques. May 2025. https://www.microsoft.com/en-us/security/blog/2025/05/29/defending-against-evolving-identity-attack-techniques/. Microsoft Threat Intelligence analysis.
Mimecast. Global Threat Intelligence Report 2025 commentary, "AI Phishing and ClickFix Attacks Explode". October 2025. https://cybermagazine.com/news/mimecast-report-ai-phishing-and-clickfix-attacks-explode. First nine months of 2025 telemetry.
Sophos. State of Ransomware 2025. June 2025. https://www.sophos.com/en-us/content/state-of-ransomware. Vanson Bourne survey of 3,400 IT/security leaders across 17 countries.
Sophos. From QR to compromise: The growing 'quishing' threat. 2025. https://www.sophos.com/en-us/blog/quishing. Sophos AI threat-research analysis.
CrowdStrike. 2025 Global Threat Report. February 2025. https://www.crowdstrike.com/en-us/press-releases/crowdstrike-releases-2025-global-threat-report/. CrowdStrike Falcon telemetry plus intelligence H1 vs H2 2024.
CrowdStrike. 2025 Threat Hunting Report. August 2025. https://www.crowdstrike.com/en-us/resources/reports/threat-hunting-report/. CrowdStrike OverWatch hunt telemetry H1 2025.
Mandiant / Google Cloud. M-Trends 2025. April 2025. https://cloud.google.com/blog/topics/threat-intelligence/m-trends-2025. Mandiant IR engagements globally calendar 2024.
Cisco Talos. 2025 Year in Review: Speed, scale, and staying power. April 2026. https://blog.talosintelligence.com/2025-talos-year-in-review-speed-scale-and-staying-power/. Cisco Talos IR plus product telemetry calendar 2025.
Cisco Talos. IR Trends Q4 2025. January 2026. https://blog.talosintelligence.com/ir-trends-q4-2025/. Cisco Talos IR engagements Q4 2025.
Cisco Talos. IR Trends Q1 2025. April 2025. https://blog.talosintelligence.com/ir-trends-q1-2025/. Cisco Talos IR engagements Q1 2025.
ENISA. Threat Landscape 2025. October 2025. https://www.enisa.europa.eu/publications/enisa-threat-landscape-2025. 4,875 EU incidents July 2024 to June 2025.
FBI Internet Crime Complaint Center. 2024 Internet Crime Report. April 2025. https://www.ic3.gov/AnnualReport/Reports/2024_IC3Report.pdf. Victim-complaint data calendar 2024; 859,532 complaints, US$16.6B losses.
NCC Group. Annual Cyber Threat Intelligence 2025. January 2026. https://www.nccgroup.com/newsroom/ncc-group-annual-cyber-threat-intelligence-2025/. NCC Group Threat Intelligence telemetry plus leak-site monitoring calendar 2025.
UK Government / NCSC / DSIT. Cyber Security Breaches Survey 2025. June 2025. https://www.gov.uk/government/statistics/cyber-security-breaches-survey-2025/cyber-security-breaches-survey-2025. UK national survey of UK businesses and charities 12 months to April 2025.
Hornetsecurity. Cyber Security Report 2026. Early 2026. https://www.hornetsecurity.com/en/blog/cybersecurity-report-2026-press-release/. 70+ billion emails processed in 2025.
Sekoia.io. Mamba 2FA: A new contender in the AiTM phishing ecosystem. October 2024. https://blog.sekoia.io/mamba-2fa-a-new-contender-in-the-aitm-phishing-ecosystem/. Sekoia.io threat-intelligence analysis of the Mamba 2FA AiTM kit.
Sekoia.io. Global analysis of Adversary-in-the-Middle phishing threats. June 2025. https://blog.sekoia.io/global-analysis-of-adversary-in-the-middle-phishing-threats/. Sekoia.io aggregate analysis January-May 2025.
Sekoia.io. Sneaky 2FA: exposing a new AiTM Phishing-as-a-Service. January 2025. https://blog.sekoia.io/sneaky-2fa-exposing-a-new-aitm-phishing-as-a-service/. Sekoia.io threat-intelligence breakdown of the Sneaky 2FA AiTM kit.
Barracuda. Threat Spotlight: How phishing kits evolved in 2025. January 2026. https://blog.barracuda.com/2026/01/07/threat-spotlight-phishing-kits-evolved-2025. Barracuda threat-intelligence analysis calendar 2025.
Cloudflare. Top 50 most impersonated brands in phishing attacks. 2025. https://blog.cloudflare.com/50-most-impersonated-brands-protect-phishing/. Cloudflare aggregate phishing-detection telemetry calendar 2025.
Anthropic. Threat Intelligence Report August 2025. August 2025. https://www.anthropic.com/news/detecting-countering-misuse-aug-2025. Anthropic threat-intel team review of misuse cases observed on Claude in 2025.
Anthropic. Disrupting the first reported AI-orchestrated cyber espionage campaign. November 2025. https://www.anthropic.com/news/disrupting-AI-espionage. Anthropic incident report on a Chinese state-sponsored campaign that misused Claude Code.
Check Point Research. Microsoft Remains the Most Imitated Brand in Phishing Attacks in Q4 2025. January 2026. https://blog.checkpoint.com/research/microsoft-remains-the-most-imitated-brand-in-phishing-attacks-in-q4-2025/. Quarterly brand-impersonation tracker Q4 2025.
Stingrai's PTaaS and pentest engagements test exactly the scenarios above: AiTM kit replays, helpdesk impersonation calls, and quishing-PDF delivery into corporate inboxes. The methodology breakdown is in our penetration testing methodologies post; for buyer-side context, see the best PTaaS providers in 2026 ranking.