Full-scope, multi-layered attack simulations designed to test your people, processes, and technology without prior knowledge given to your defense teams. Led by elite white-hat hackers through our PTaaS platform.
Led by expert white-hat hackers and delivered through our Penetration Testing as a Service (PTaaS) platform.


Red Teaming engagements go far beyond traditional penetration testing by simulating the full attack lifecycle of sophisticated threat actors. Our operators replicate the tactics, techniques, and procedures of real-world adversaries to test your organization's ability to detect, respond to, and contain advanced threats.
Our team delivers a comprehensive report detailing the attack narrative, exploitation results, and business impact along with prioritized remediation guidance.
By conducting Red Teaming exercises, your organization gains resilience against:
Advanced Persistent Threats (APTs)
Ransomware and extortion campaigns
Supply chain compromises
Insider threats and credential abuse

Assumed Breach
We operate under the assumption that an attacker has already breached the perimeter (e.g., via a compromised laptop or stolen credentials). This bypasses the initial access phase to focus entirely on internal resilience, outlining the potential scope of a compromise and identifying weak internal controls.

Black Box Full Chain
A "no-knowledge" simulation where Stingrai starts with zero inside information, mirroring an external threat actor's perspective. Experience the full impact of a targeted attack as we demonstrate exactly how a bad actor identifies an entry point, exploits it, and navigates your network.

Threat Intelligence-Led
We partner with globally respected threat intelligence providers to design attack scenarios based on the specific threats targeting your industry and region. Essential for complying with regulatory frameworks like DORA and TIBER-EU, this tests the resiliency of critical systems against the threats you actually face.



On-Premise Red Teaming
Passive and active intelligence gathering on employees, physical locations, and digital footprint to build custom payloads.
Initial access via social engineering (phishing, vishing), physical entry, or exploiting external-facing vulnerabilities.
Lateral movement through privilege escalation, credential harvesting (e.g., Kerberoasting), and internal exploits.
Objective execution simulating data exfiltration, ransomware deployment, or disruption of critical business processes.

Cloud Red Teaming
Cloud reconnaissance enumerating public buckets, exposed APIs, and analyzing leaked credentials in public repositories.
Identity and access exploitation abusing over-permissive IAM roles, compromising service principals, or bypassing MFA.
Control plane compromise moving from compromised workloads to the management plane for broader cloud estate control.
Container and serverless attacks exploiting vulnerabilities in Kubernetes clusters, Docker containers, or Lambda functions.
Global Red Team Expertise
Access to industry-leading Red Team experts recruited from around the globe. Our operators hold elite accreditations from CBEST and CREST, bringing extensive experience across the most demanding adversary simulation frameworks.
Advanced Tactics & Techniques
We use innovative, cutting-edge techniques relevant to your specific technical environment. Our engagements are powered by actionable threat intelligence, ensuring you are testing against reality, not just theory.
Client-Centric Approach
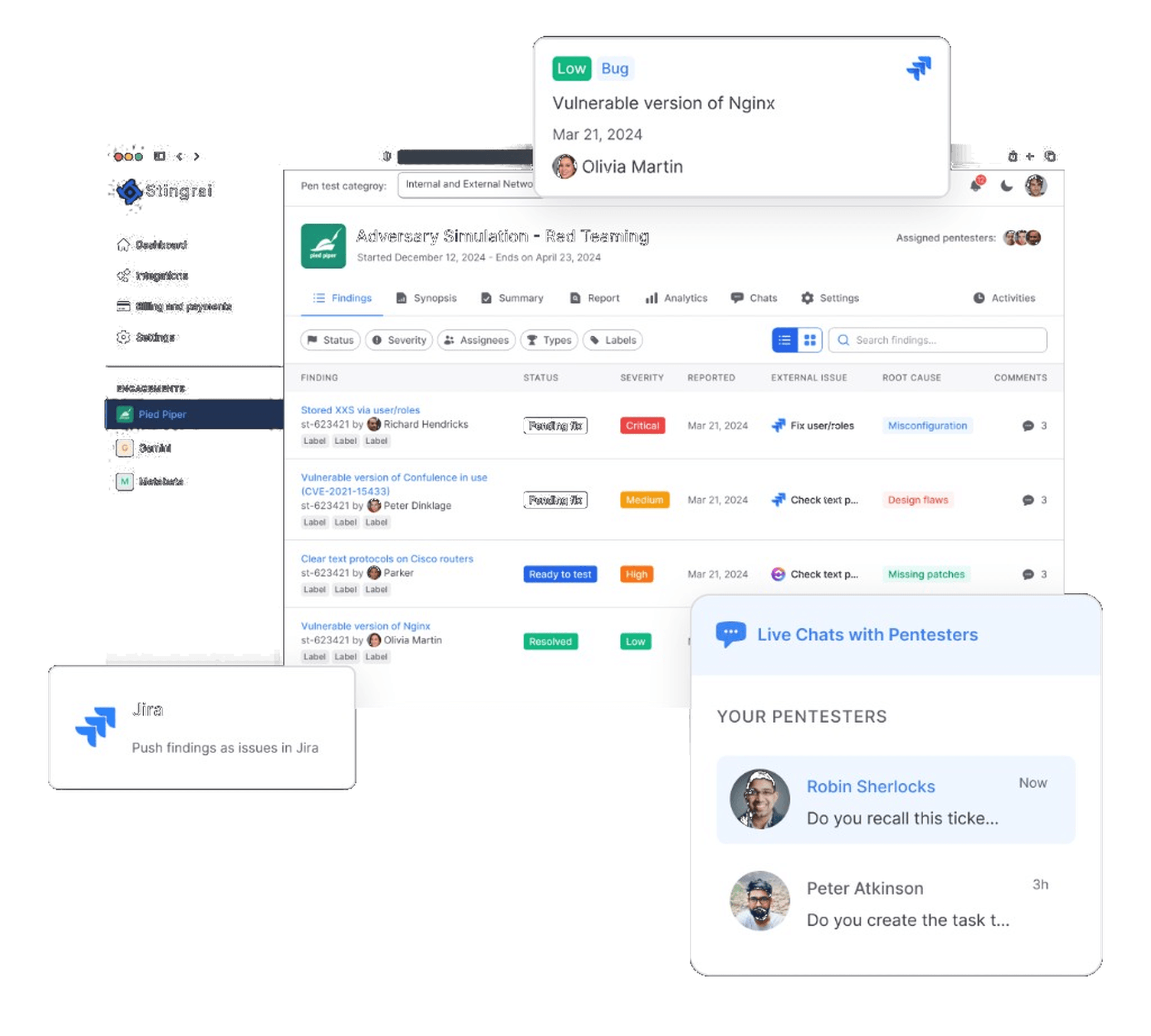
We prioritize your needs and work closely with you throughout the process, offering clear communication, regular updates, and ongoing support through our PTaaS platform.
Real-World Simulation
Our scenarios replicate the exact behaviors of the world's most dangerous attacker groups. Whether it's nation-state data theft or ransomware cartel tactics, we replicate the kill chain step-by-step.
Expert Remediation Support
Stingrai offers detailed remediation steps along with free on-call support, ensuring our clients receive expert guidance to efficiently fix vulnerabilities and strengthen their security.
Accessible to All
We believe advanced security should be accessible to all. That's why Stingrai offers competitive pricing without compromising on quality. Protect your organization with top-tier red teaming tailored to your budget.
Our red team engagements operate under realistic constraints including full evasion, extended duration, and a defined objective. The final report documents the complete path from initial foothold to crown-jewel access alongside every detection opportunity your blue team missed.

