The global connected device population reached 21.1 billion at the end of 2025, growing 14% year-over-year and on a 13.2% CAGR trajectory toward 39 billion by 2030, per IoT Analytics' State of IoT 2025. The attack surface scaled with it. SonicWall's 2025 Cyber Threat Report recorded a +124% year-over-year jump in IoT attacks during 2024 and prevented over 17 million attacks targeting IoT cameras alone. Cloudflare mitigated a 5.6 Tbps Mirai-based DDoS in October 2024 from 13,000 compromised devices, then a 29.7 Tbps Aisuru flood in Q3 2025 sourced from an estimated 300,000 to 700,000 hijacked routers, DVRs, and IP cameras. The volume and the variety both went up, and the lag between proof of concept and weaponization compressed.
Four forces define 2026. Botnet capacity has 5x'd in 12 months, with Cloudflare mitigations rising from 5.6 Tbps in October 2024 to 29.7 Tbps in Q3 2025 and Microsoft Azure absorbing a 15.72 Tbps single-attack flood on October 24, 2025 powered by Aisuru. Edge devices became the #1 initial-access vector: Verizon DBIR 2025 reported edge and VPN exploitation surged from 3% to 22% of all vulnerability-driven breaches, an eightfold increase YoY. OT ransomware crossed an inflection point, with Dragos counting 1,693 attacks against industrial organizations in 2024, a +87% YoY surge, and 75% of those incidents causing partial operational shutdowns. Regulation tightened: the EU Cyber Resilience Act starts requiring vulnerability and incident notifications from manufacturers on September 11, 2026, with full conformity obligations on December 11, 2027. CISOs, security buyers, OT operators, and journalists need a single source-of-truth reference. This post is it.
This post is the Stingrai research team's canonical 2026 reference for IoT, IIoT, and OT attack activity. It assembles 75 numeric claims from 18 named primary publishers, including SonicWall, Cloudflare, Microsoft, NETSCOUT, IoT Analytics, Forescout Vedere Labs, Palo Alto Networks Unit 42, Verizon DBIR, Dragos, Nozomi Networks Labs, ENISA, IBM X-Force, Bitdefender + NETGEAR, Asimily, Phosphorus, the FCC, the EU Commission, the UK Office for Product Safety and Standards, Krebs on Security with XLab, and the German BSI. Lead data is full-year 2024 and 2025 telemetry, the freshest available; primary publishers have not yet released full-year 2026 reports as of April 2026. Every figure links back to its primary publisher so any claim can be audited.
TL;DR: 12 labeled key stats
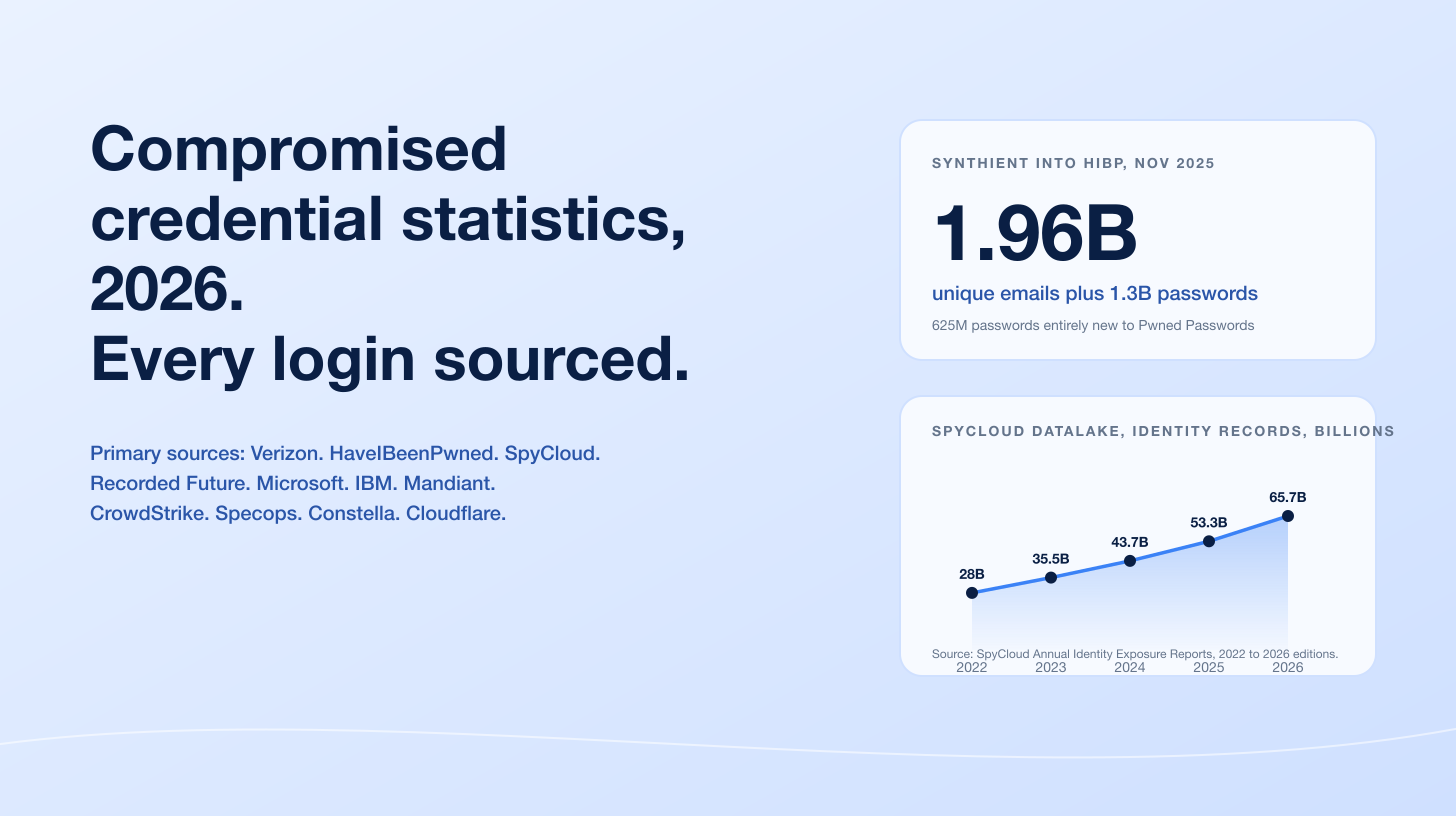
Global connected IoT devices, end of 2025: 21.1 billion (+14% YoY) (IoT Analytics State of IoT 2025).
Cloudflare peak DDoS, Q3 2025 (Aisuru botnet): 29.7 Tbps and 14.1 billion packets per second (Cloudflare Q3 2025 DDoS Threat Report).
Microsoft Azure peak DDoS, October 24, 2025 (Aisuru): 15.72 Tbps from 500,000+ source IPs (The Hacker News on Microsoft Azure).
IoT attacks YoY 2024 (SonicWall corpus): +124% (SonicWall 2025 Cyber Threat Report).
Attacks blocked on IoT cameras 2024 (SonicWall): 17 million+ (SonicWall 2025).
Ransomware attacks against industrial organizations, 2024: 1,693 (+87% YoY) (Dragos 2024 Year in Review).
Industrial ransomware incidents causing partial OT shutdown, 2024: 75% (Dragos 2024).
CISA ICS advisories published, 2025: 508 (up from 423 in 2024) (SOCRadar aggregation of CISA data).
Edge / VPN share of initial-access exploitation, 2025: 22% (up from 3%, an 8x rise) (Verizon DBIR 2025).
Aisuru botnet compromised devices: 300,000 to 700,000 routers, DVRs, IP cameras (Krebs on Security; BSI Aisuru profile).
Hospitals managing IoMT devices with Known Exploited Vulnerabilities, 2025: 99% (Asimily 2025 IoMT report).
IoT devices deployed with default passwords: 75% (Phosphorus).
Key takeaways
Botnet horsepower has gone parabolic, but the recipe has not changed. Aisuru's 300,000+ nodes propagate exactly the way Mirai did in 2016: scan the public internet for Telnet, SSH, or known router CVEs and brute-force or exploit. The defensive playbook is unchanged. The cost of getting it wrong has scaled by a factor of 30 because the adversary is now selling residential-proxy access on top of DDoS-for-hire (Krebs on Security).
Edge devices are the new ransomware front door. Verizon DBIR 2025 found edge and VPN exploitation rose nearly eightfold from 3% to 22% of all initial-access exploits, with median time-to-mass-exploitation of zero days for the most critical edge CVEs (Verizon, 2025). Patching the edge before patching the endpoint is the default in 2026.
OT ransomware is no longer a tail risk. Dragos's 1,693 industrial-targeted ransomware incidents in 2024 are an +87% YoY rise, and 75% led to partial production shutdown. The financial-impact gap between IT-only and OT-impacting ransomware is now wide enough that boards are starting to ring-fence capex specifically for OT segmentation and IR retainers (Dragos, 2024).
Hospitals are running known-exploited code on devices that touch patients. Asimily's 2025 IoMT data: 99% of hospitals manage devices with KEVs, 96% of those KEVs are linked to ransomware campaigns, and 6.2 vulnerabilities per medical device on average (Asimily, 2025). This is the next regulatory chokepoint for HHS, the FDA, and the EU CRA.
Regulation is finally catching up. EU CRA's 24-hour vulnerability-disclosure clock starts September 11, 2026; UK PSTI Act has been live since April 29, 2024 with up to £10 million in penalties; the US Cyber Trust Mark labeling regime is under ioXt Alliance administration as of April 13, 2026 (FCC public notice). Buyers should now expect "secure by design" claims to be backed by SBOMs and signed firmware, not marketing copy.
Methodology
Sources used: IoT Analytics State of IoT 2024 (released October 2024) and State of IoT 2025 (released October 2025); SonicWall 2025 Cyber Threat Report (released February 2025, covering CY 2024); Cloudflare DDoS Threat Reports (Q4 2024 and Q3 2025 quarterly editions); Microsoft Threat Intelligence blog and Microsoft Azure DDoS Protection telemetry; NETSCOUT DDoS Threat Intelligence Report Issue 16 (released March 2026, covering 2H 2025); Forescout Vedere Labs Riskiest Connected Devices 2025 (April 2025); Palo Alto Networks 2025 Device Security Threat Report (analyzing 27M+ devices across 1,803 enterprises); Verizon 2025 Data Breach Investigations Report (April 2025); Dragos 8th Annual OT Cybersecurity Year in Review (covering CY 2024); Nozomi Networks Labs OT/IoT Cybersecurity Trends Reports (February 2025 and July 2025 editions); ENISA Threat Landscape 2025 (analyzing ~4,900 incidents between July 2024 and June 2025); IBM X-Force Threat Intelligence Index 2025 and IBM Cost of a Data Breach Report 2025; Bitdefender + NETGEAR 2025 IoT Security Landscape Report (analyzing 13.6 billion attacks across 6.1 million smart homes); Asimily 2025 IoMT report and Phosphorus 2025 default-password research; the EU Commission Cyber Resilience Act (in force December 10, 2024), UK GOV PSTI Act material, FCC Cyber Trust Mark public notices and orders; and Krebs on Security with XLab attribution and the German Federal Office for Information Security (BSI) Aisuru botnet profile.
Date cutoff: April 25, 2026. We lead with full-year 2024 or 2025 telemetry where a primary publisher has released it, and label any 2026 figure explicitly as a forecast or projection. Statistics that could not be reached via a named primary source on at least one verification pass were dropped rather than estimated. Secondary news outlets (The Hacker News, BleepingComputer, The Register, Industrial Cyber, SecurityWeek, HIPAA Journal) are cited only when they constitute the public record of a primary publisher's release that is not directly retrievable on this verification pass.
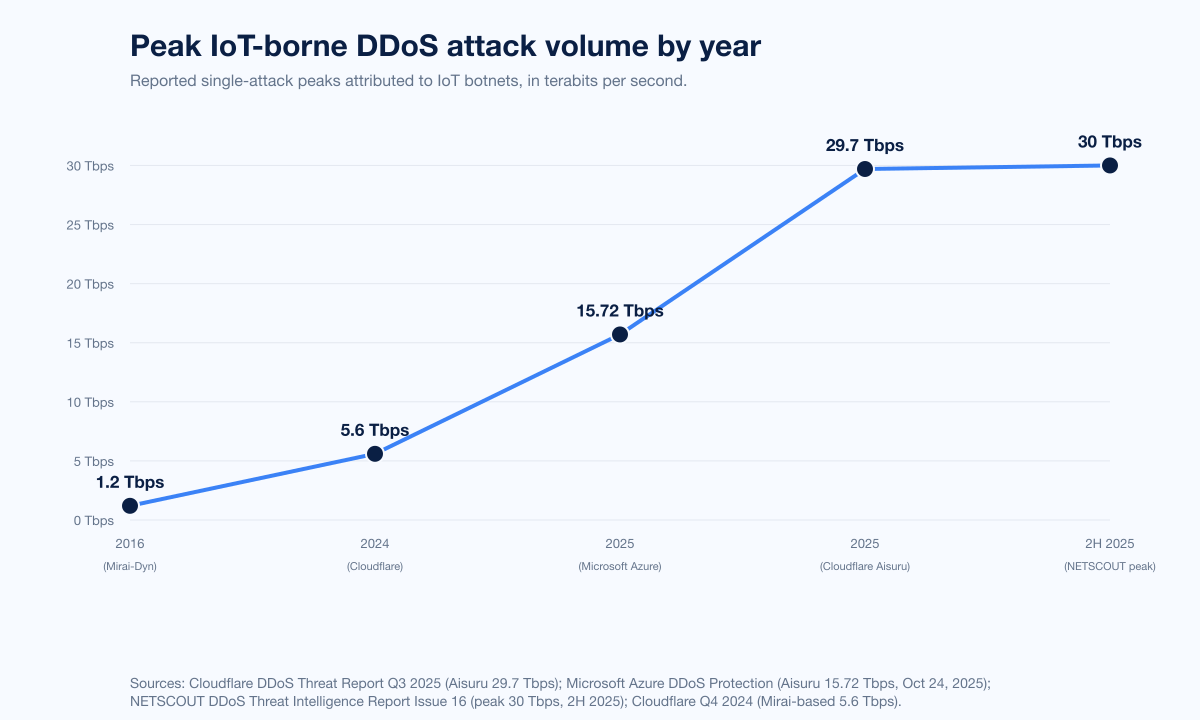
Figure 1: Peak public DDoS attack volume attributed to IoT botnets, 2016 through 2H 2025. Mirai's 2016 1.2 Tbps Dyn attack remained the textbook reference until 2024. Sources: Cloudflare Q3 2025 DDoS Threat Report; NETSCOUT DDoS Threat Intelligence Report Issue 16.
How big is the IoT problem in 2026?
Three datasets anchor the answer.
Connected device population (IoT Analytics)
IoT Analytics' State of IoT 2025, released October 2025, set the global connected IoT device population at 21.1 billion at the end of 2025 (+14% YoY), up from 18.8 billion at the end of 2024 (State of IoT 2024). The firm projects 39 billion connected devices by 2030 on a 13.2% CAGR. Connectivity mix: Wi-Fi 32%, Bluetooth 24%, cellular IoT 22%, with the remainder split across LPWAN, satellite, Zigbee, Thread, and proprietary protocols.
Year | Connected IoT devices (billions) | YoY growth | Source |
|---|---|---|---|
2024 (end) | 18.8 | +13% | IoT Analytics State of IoT 2024 |
2025 (end) | 21.1 | +14% | IoT Analytics State of IoT 2025 |
2030 (forecast) | 39.0 | 13.2% CAGR | IoT Analytics State of IoT 2025 |
IoT attack volume (SonicWall)
SonicWall's 2025 Cyber Threat Report is the most-cited annual IoT-attack telemetry corpus. Headline figures for 2024:
IoT attacks, YoY 2024: +124%.
Attacks blocked on IoT cameras, 2024: 17 million+.
Top exploited IoT camera CVEs: Hikvision Command Injection (CVE-2021-36260) and Authentication Bypass (CVE-2017-7921), both years-old, both still rampant.
Encrypted threats, YoY 2024: +93%.
Never-before-seen malware variants, 2024: 210,258 (~630 new strains per day).
Exploits weaponized within 48 h of public PoC: 61%.
Exploits within 4 days of PoC: 75%.
Average duration of a critical attack, 2024: 68 days.
APAC India IoT attack rise, 2024: +97%.
The single most important takeaway from SonicWall's data is that the most-exploited IoT camera CVEs are 4 to 8 years old. Defensively, this is good news. Operationally, it is a referendum on patch management: the same Hikvision flaws that powered Mirai variants in 2018 are still landing on victim networks in 2024 because the cameras shipped with default credentials, the firmware was never updated, and the device sat on a flat network with internet exposure.
Edge devices and the rise of vuln exploitation as initial access (Verizon DBIR 2025)
Verizon's 2025 Data Breach Investigations Report, released April 23, 2025, recorded another 34% YoY rise in successful vulnerability exploits, on top of the 180% surge in 2024. Vulnerability exploitation became the initial-access vector in 20% of breaches. The most striking finding is the eightfold jump in edge-device and VPN exploitation share:
Metric | 2024 (DBIR) | 2025 (DBIR) | Source |
|---|---|---|---|
Vuln exploitation YoY growth | +180% | +34% | Verizon DBIR 2025 |
Edge / VPN share of vuln exploitation breaches | 3% | 22% | Verizon DBIR 2025 |
Edge vulnerabilities fully remediated by org | n/a | 54% | Verizon DBIR 2025 |
Median days to remediate edge vulns | n/a | 32 days | Verizon DBIR 2025 |
Median days from CVE publication to mass exploitation (critical edge CVEs) | n/a | 0 | Verizon DBIR 2025 |
Edge devices in DBIR's framing include firewalls, VPN concentrators, remote-access gateways, and connected appliances at the network perimeter. Many of the same products are how IoT and OT environments are reached.
Top IoT botnets and their compromised-device counts
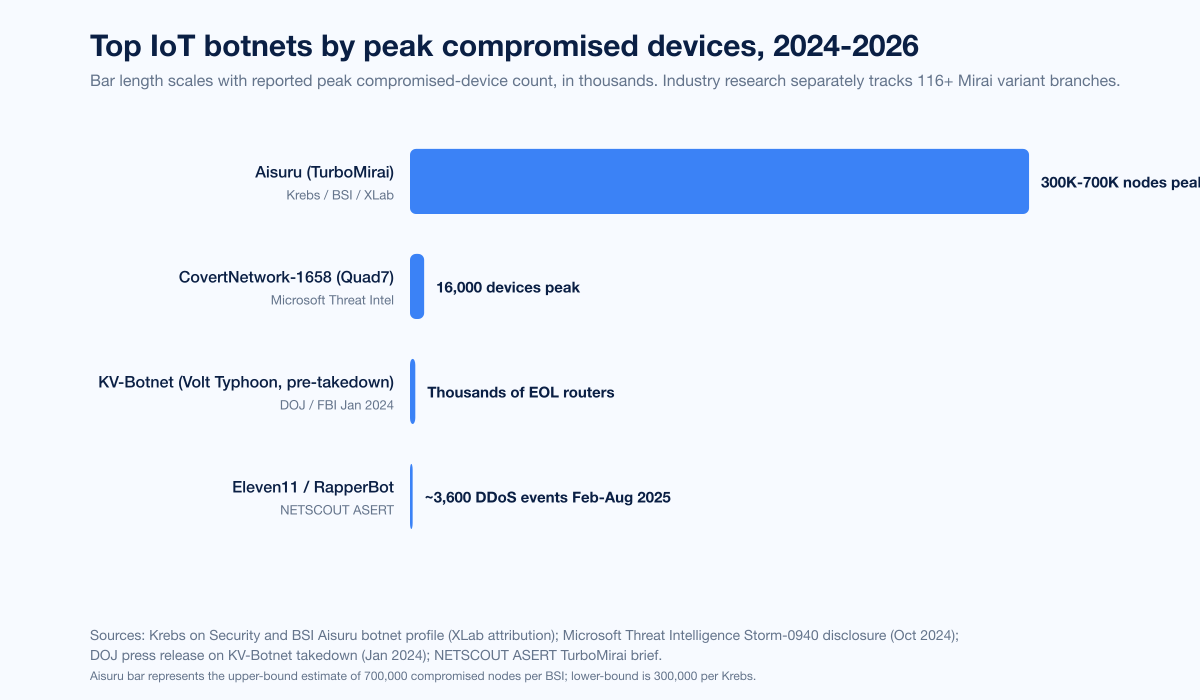
Figure 2: Top IoT botnet families and their reported compromised-device counts, 2024 to early 2026. Sources: Krebs on Security; BSI Aisuru profile; Microsoft Threat Intelligence; NETSCOUT ASERT Aisuru summary.
Aisuru (TurboMirai class)
Aisuru is the headline IoT botnet of 2024-2026. First identified by XLab in August 2024 and detailed by Brian Krebs in October 2025, Aisuru spreads by scanning Telnet (port 23) for default credentials and exploiting known router and CCTV CVEs, including some never-publicly-disclosed zero-days. Compromised devices are primarily consumer-grade broadband routers, online CCTV recorders, and DVR systems running similar OEM firmware variants. Headline metrics:
Estimated compromised devices: 300,000 to 700,000 (Krebs on Security; BSI; XLab attribution).
Cloudflare Q3 2025 hyper-volumetric attacks attributed to Aisuru: 1,304 (+54% QoQ) (Cloudflare Q3 2025).
Cloudflare peak attack from Aisuru: 29.7 Tbps and 14.1 billion packets per second across a 69-second UDP carpet-bombing flood targeting an average of 15,000 destination ports per second (Cloudflare).
Microsoft Azure peak attack from Aisuru: 15.72 Tbps and 3.64 billion packets per second from 500,000+ source IPs on October 24, 2025 (The Hacker News on Microsoft Azure).
Operator pivot: Aisuru operators began offering compromised devices as residential proxies in late 2025, expanding monetization beyond DDoS-for-hire (Krebs).
CovertNetwork-1658 / Quad7 (Storm-0940)
Microsoft Threat Intelligence attributed CovertNetwork-1658 (also called the Quad 7 / 7777 botnet) to the Chinese threat actor Storm-0940 in October 2024. Headlines:
Peak compromised devices: 16,000+, predominantly TP-Link consumer routers.
Active devices at any time: ~8,000.
Share of active devices conducting password spray: 20%.
Targets: Microsoft 365 accounts at North American and European think tanks, government agencies, NGOs, law firms, and defense industrial base.
Active since at least: 2021.
KV-Botnet (Volt Typhoon, pre-takedown)
The FBI and DOJ disrupted the KV-Botnet in January 2024, which had been packed with end-of-life Cisco, Netgear, and Fortinet routers acting as a covert traffic-relay layer for Volt Typhoon. Volt Typhoon began rebuilding the infrastructure within weeks of the takedown, per BleepingComputer reporting and the joint US-led advisory updates from CISA, FBI, and NSA.
Eleven11 / RapperBot
NETSCOUT ASERT tracked the Eleven11 / RapperBot TurboMirai botnet through ~3,600 DDoS events between late February and August 2025. The same botnet category, the same propagation recipe.
Mirai variant ecosystem
Mirai's 2016 source-code release seeded what is now a sprawling fork tree. Industry research consolidated by Mazebolt tracks 116+ distinct Mirai variant branches as of 2025, with a 50% increase in Mirai-related command-and-control infrastructure year-over-year. Cloudflare's October 2024 5.6 Tbps record-setting Mirai-based DDoS was launched from a 13,000-device Mirai variant against an Eastern Asian ISP and lasted 80 seconds. The attack had no impact on the target because mitigation was fully autonomous.
Aggregate scale, 2H 2025 (NETSCOUT)
NETSCOUT's DDoS Threat Intelligence Report Issue 16, covering July to December 2025, recorded:
8 million+ DDoS attacks worldwide in 2H 2025.
Peak demonstration attacks at 30 Tbps and 4 billion packets per second, primarily IoT-botnet-driven.
20,000+ botnet-driven attacks in a single July 2025 surge.
Compromised IoT and customer-premises equipment in some cases producing outbound floods exceeding 1 Tbps from broadband and mobile networks.
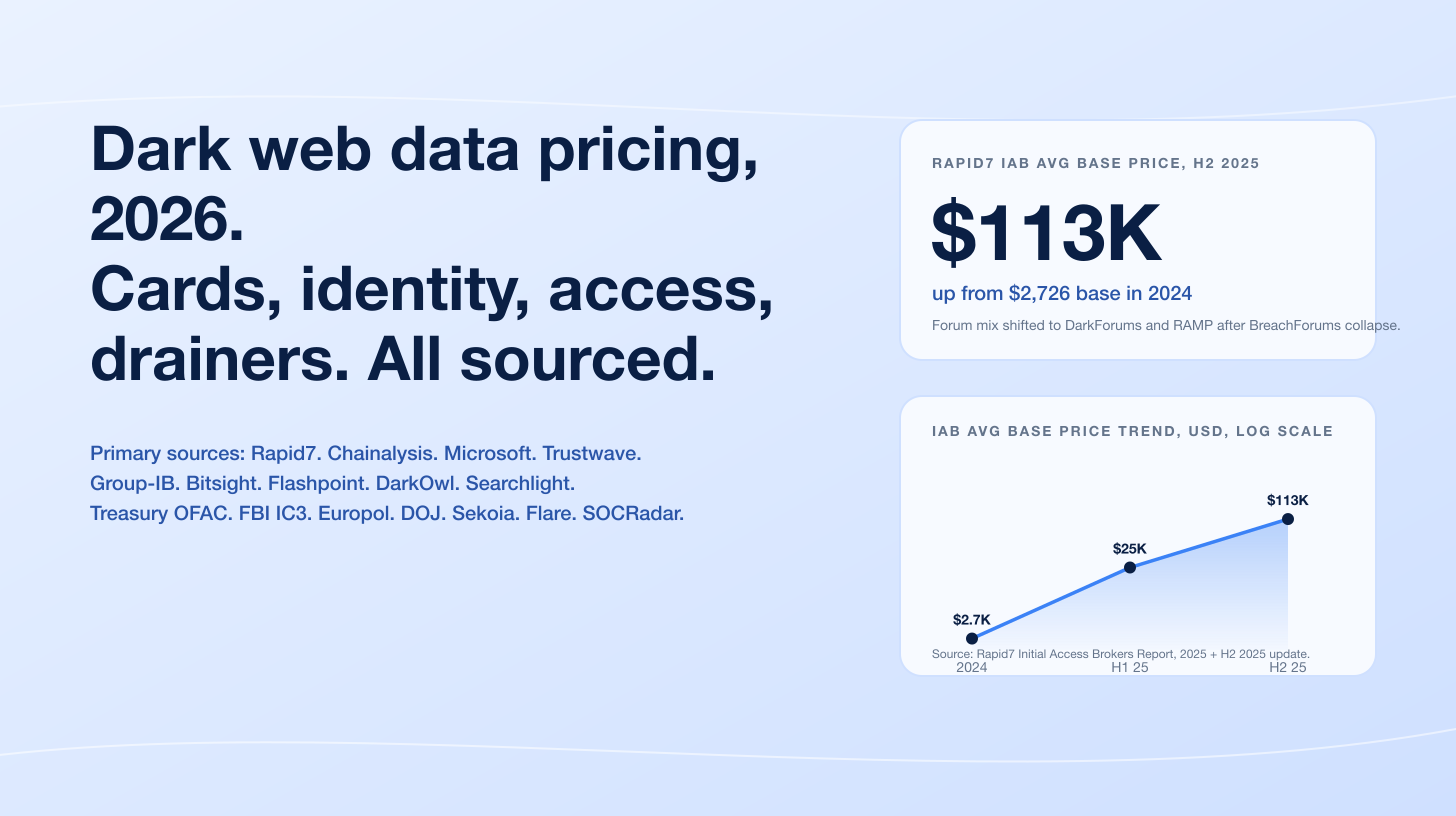
DDoS-for-hire platforms now integrating dark-web LLMs and conversational AI; underground forum mentions of malicious AI tools rose 219%.
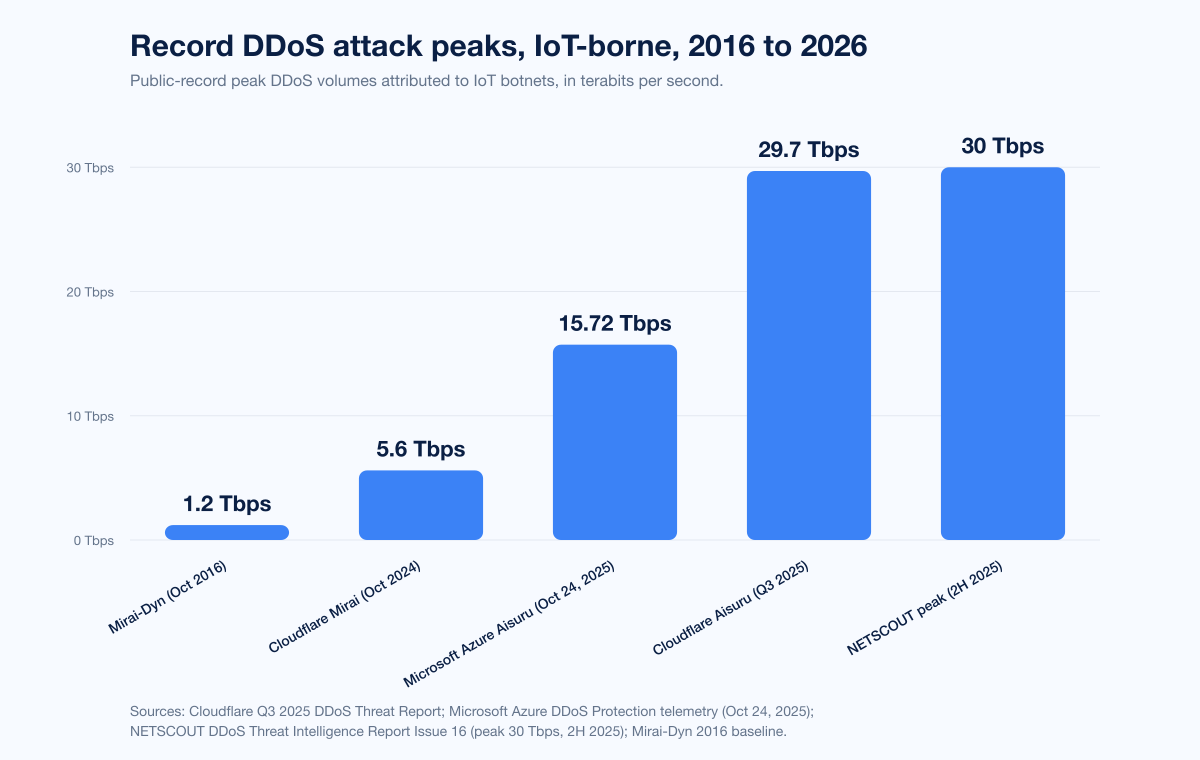
Figure 3: Record DDoS peak attack volumes 2016 through 2H 2025, all attributed to IoT-borne botnets. The Mirai-Dyn 1.2 Tbps attack of 2016 stayed the canonical reference for nearly a decade until October 2024. Sources: Cloudflare Q3 2025 DDoS Threat Report; NETSCOUT DDoS Threat Intelligence Report Issue 16; The Hacker News on Microsoft Azure.
Top exploited protocols, ports, and vulnerabilities
The targeted-protocol data is consistent across SonicWall, Kaspersky ICS-CERT honeypot data, and Aisuru's documented spread mechanics: Telnet (port 23) and SSH (port 22) remain the highest-traffic IoT attack surfaces, with HTTP-based router admin interfaces second.
Vector | Why it matters in 2026 | Anchor source |
|---|---|---|
Telnet (port 23) | Aisuru's primary auto-spread mechanism on consumer routers and CCTV systems; default credentials remain widespread | |
SSH (port 22) | Continued top target across Kaspersky's IoT honeypot corpus | |
HTTP / HTTPS router admin (ports 80, 443, 8080) | Aisuru exploits known router CVEs for un-credentialed RCE; CovertNetwork-1658 leverages the same path on TP-Link | |
RTSP / ONVIF (port 554) and Hikvision proprietary management ports | Direct path to IP camera takeover via CVE-2021-36260 and CVE-2017-7921 | |
Modbus TCP (port 502) | FrostyGoop's first-of-its-kind direct ICS Modbus abuse, used in Lviv heating-utility attack | |
TCP port 7777 (Quad7 botnet C2) | CovertNetwork-1658 hallmark |
The Hikvision command-injection and authentication-bypass CVEs from 2017 and 2021 lead SonicWall's 2024 most-exploited list. Both have been patched for years. Both still get exploited tens of millions of times because the cameras run firmware that was never updated, on networks that were never segmented.
Vulnerability disclosures
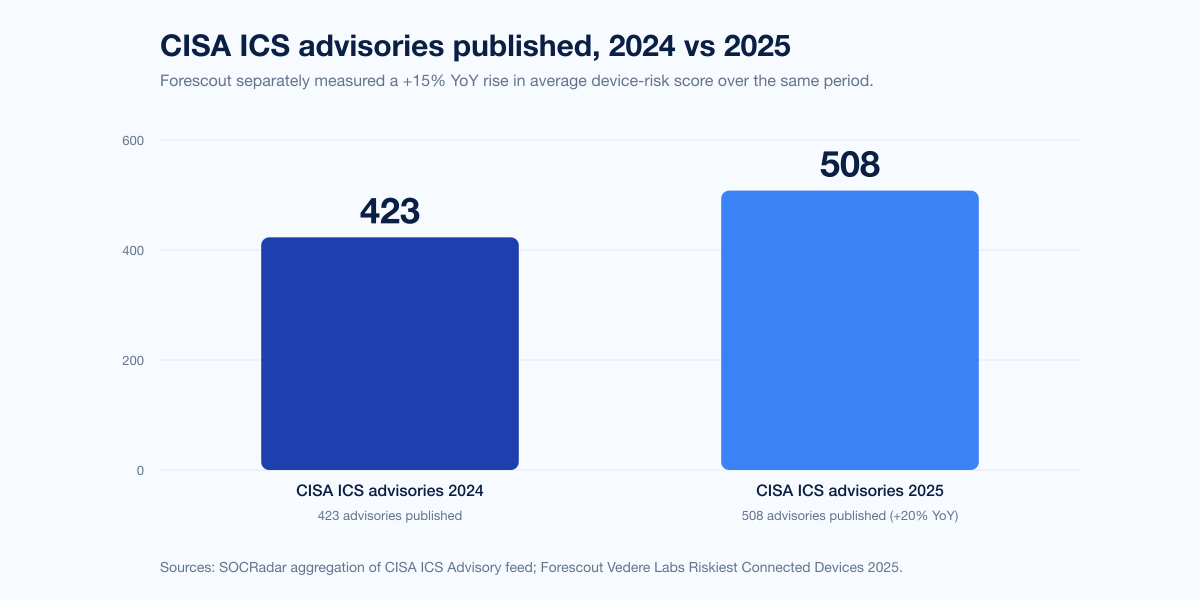
Figure 4: CISA ICS advisory counts published per calendar year, 2024 vs 2025. Forescout Vedere Labs measured a +15% YoY increase in average device risk score over the same period. Sources: SOCRadar aggregation of CISA data; Forescout Vedere Labs Riskiest Connected Devices 2025.
CISA ICS advisories
SOCRadar's aggregation of CISA's ICS advisory feed tabulates:
2024: 423 ICS advisories.
2025: 508 ICS advisories.
2024-2025 cumulative coverage: Hundreds of vulnerabilities disclosed across 200+ vendors and 700+ products.
High-severity CVEs, 2024: 929. High-severity CVEs, 2025: 796.
Medium-severity CVEs, 2025: 1,019, up sharply.
Nozomi Networks Labs OT/IoT Security trends (Feb 2025 6-month window)
Nozomi Networks Labs, reviewing the previous six months of CISA ICS advisories alongside its anonymized customer telemetry and IoT honeypot data, reported:
Critical manufacturing accounted for 75% of all CISA ICS CVEs in the period, the top sector.
Of the top vulnerabilities, 4 were already on the CISA Known Exploited Vulnerabilities (KEV) list, and 20 had EPSS scores indicating >1% probability of being exploited in the wild.
Only 6% of more than 500,000 wireless networks analyzed were adequately protected against wireless deauthentication attacks, leaving most networks (including those in mission-critical environments) highly exposed.
Forescout Vedere Labs Riskiest Connected Devices 2025
Forescout's fifth annual riskiest-devices report, published April 9, 2025, analyzed millions of devices in Forescout's Device Cloud:
Average device risk, YoY: +15%.
Routers' share of devices with the most dangerous vulnerabilities: more than 50%.
New asset types added in 2025: 12, the largest single-year change in the report's history.
Riskiest sector: Retail, followed by financial services, government, healthcare, and manufacturing.
Top-risk IoT device classes: Network video recorders (NVRs), VoIP phones, IP cameras, network attached storage (NAS), and (newly added) point-of-sale systems.
Forescout's framing matches the SonicWall data: network infrastructure is now riskier than endpoints, and has been since 2024. Edge gear sits at the perimeter, runs administrative interfaces, and ships with default ports open.
Palo Alto Networks Unit 42 Device Security Threat Report 2025
Palo Alto Networks' 2025 Device Security Threat Report analyzed 27 million devices across 1,803 enterprise customers:
Average enterprise network: 35,000 devices spanning 80 device types.
Connections from high-risk IoT devices to corporate IT systems: 48.2%.
Devices operating outside IT control (BYOD plus rogue IoT): 32.5%.
Networks with poor segmentation: 77.74%, meaning a smart coffee maker and a financial server can talk on the same VLAN.
IoT devices with at least one known vulnerability: ~21%.
Default credentials remain endemic
Phosphorus reports that 75% of devices are deployed with default passwords across IoT, OT, IoMT, and IIoT classes. Cameras, printers, HVAC controllers, medical devices, kiosks, and badge readers ship with vendor-default credentials and almost never have them rotated post-deployment. Aisuru's primary spread mechanism is precisely this gap: scan Telnet, try the default, and on success enroll the device.
OT and ICS attacks
The OT side of the data tells a parallel story.
Dragos 2024 Year in Review
Dragos's 8th annual OT Cybersecurity Year in Review, released February 2025 covering CY 2024:
Ransomware attacks targeting industrial organizations, 2024: 1,693, a +87% YoY increase.
Ransomware incidents producing partial OT shutdown: 75%.
Ransomware incidents producing full OT shutdown: 25%.
Tracked OT threat groups: 23 worldwide, 9 active in OT operations during 2024.
New OT threat groups identified in 2024: 2 (GRAPHITE and BAUXITE).
VOLTZITE: technical overlaps with Volt Typhoon; exfiltrates GIS data, OT network diagrams, and ICS operating instructions used to plan targeted attacks.
ICS-specific malware families discovered in 2024: 2 new entries (Fuxnet, FrostyGoop), bringing the total known ICS malware family count to 9.
FrostyGoop in Lviv
FrostyGoop is the first publicly documented ICS-specific malware to abuse the Modbus TCP protocol on port 502 to directly manipulate industrial process commands. The January 2024 attack against a Lviv, Ukraine municipal district energy company cut central heating to more than 600 apartment buildings during winter sub-zero conditions. Operators caused temperature controllers to report inaccurate measurements (water "hot" while in fact cold), water heaters never engaged, and remediation took nearly two days.
Kaspersky ICS-CERT global telemetry
Kaspersky ICS-CERT reports the share of ICS computers on which malware was blocked, quarter by quarter:
Quarter | Global share of ICS computers with blocked malware |
|---|---|
Q1 2025 | 21.9% |
Q2 2025 | 20.5% |
Q4 2025 (Middle East regional) | 22.9% |
Roughly one in five ICS computers globally had malware blocked on it through 2025. The figure is remarkably stable quarter on quarter and across regions.
ENISA EU corpus
ENISA's Threat Landscape 2025 analyzed approximately 4,900 cybersecurity incidents between July 2024 and June 2025:
OT threats share of identified categories: 18.2%.
Top targeted EU sector: Public administration at 38.2%.
Manufacturing share of EU attacks: 2.9%, with 59.3% of those attacks being cybercriminal.
Phishing emails using AI tooling, early 2025: 80%+.
Distinct ransomware variants observed: 82.
ENISA's report is the EU mirror to Dragos and Verizon DBIR; it reflects a different sample (incidents reported to EU authorities) but the OT-as-target signal is consistent.
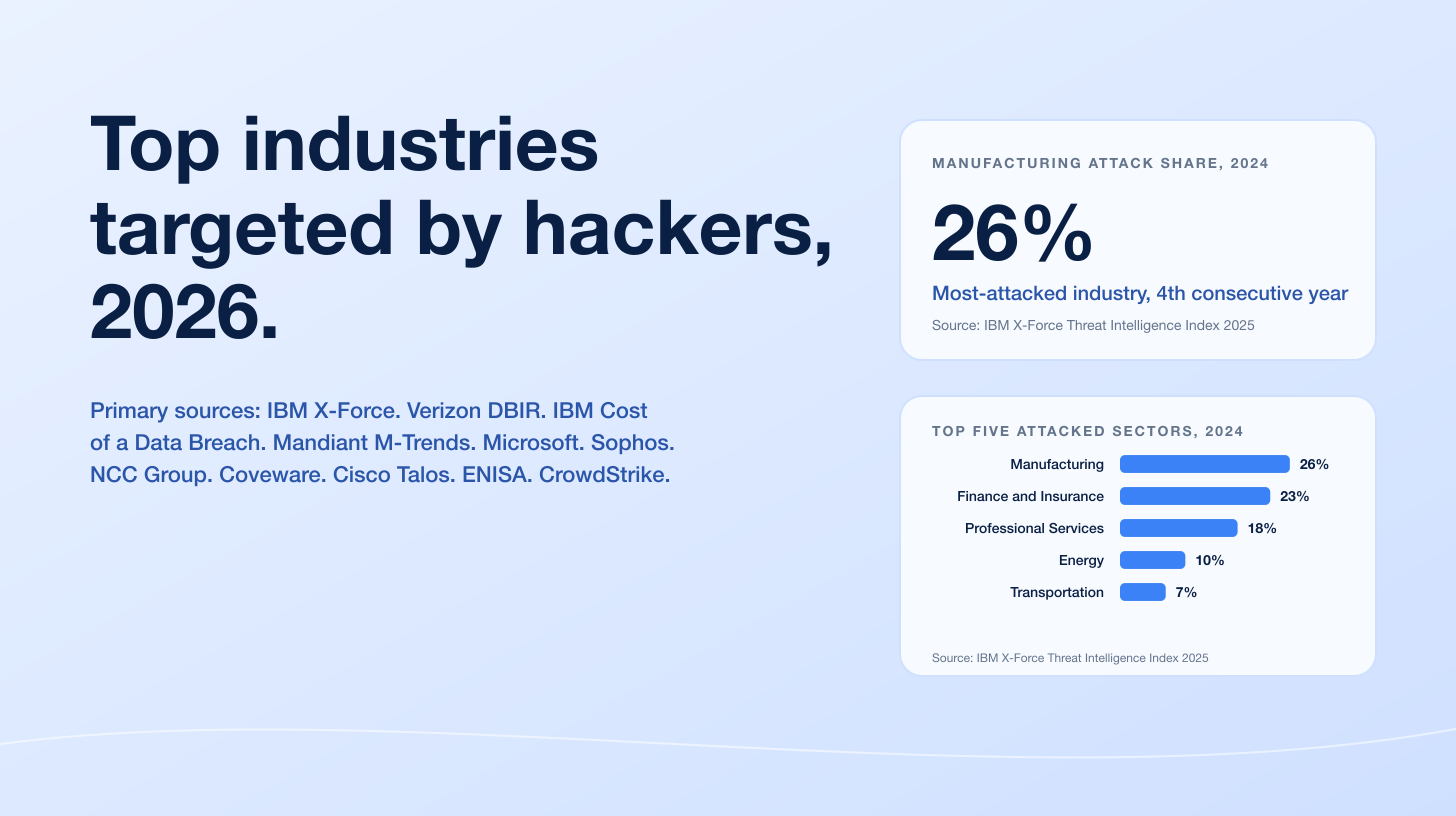
IBM X-Force on manufacturing
IBM X-Force Threat Intelligence Index 2025 reports manufacturing as the #1-targeted industry for four consecutive years. Of attacks on manufacturing in 2024:
Extortion share: 29%.
Data theft share: 24%.
The economics are unsurprising. Manufacturers cannot tolerate downtime, ransomware operators know it, and every hour of plant offline produces measurable financial pressure to pay.
IoT-driven impact by vertical
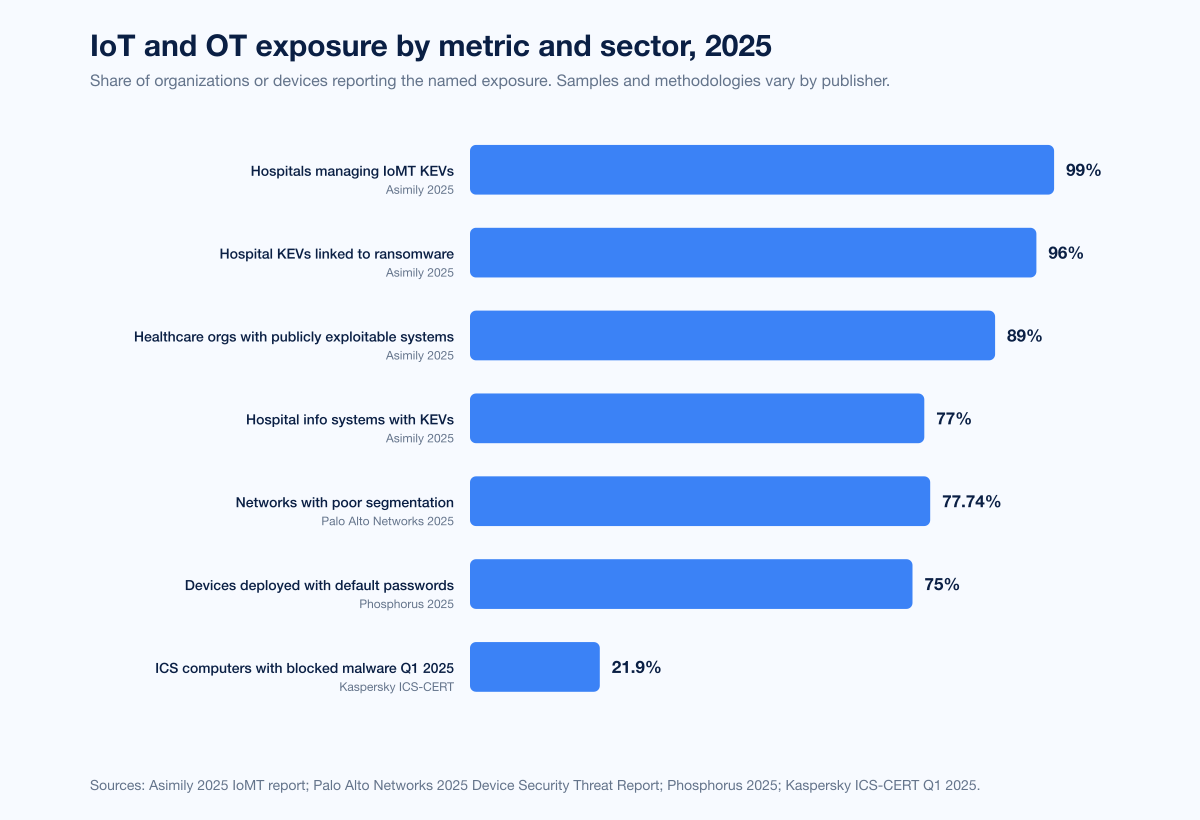
Figure 5: IoT and OT incident exposure by sector and metric. Sources: Asimily 2025 IoMT report; Dragos 2024 Year in Review; Kaspersky ICS-CERT Q1 2025.
Healthcare and IoMT
Asimily's 2025 IoMT research is the most-cited corpus on connected medical devices in 2025 and 2026:
Hospitals managing IoMT devices with Known Exploited Vulnerabilities: 99%.
Hospitals with KEVs linked to ransomware campaigns: 96%.
Healthcare orgs running publicly exploitable systems: 89% (Asimily, via Infosecurity Magazine).
Hospital information systems with KEVs: 77%.
Clinical IoT devices with KEVs: 35%.
Average flaws per medical device: 6.2.
Share of medical devices end-of-life: 60%.
IBM Cost of a Data Breach Report 2025:
Average healthcare data breach cost, 2025: US$7.42 million (-24% YoY from 2024).
IBM Cost of a Data Breach 2024 (industrial sector, the OT analogue):
Average industrial sector breach cost, 2024: US$5.56 million (+18% YoY).
Time to identify industrial breach: 199 days vs 194 global average.
Time to contain industrial breach: 73 days vs 64 global average.
The combination of a year-long detection window and a +18% YoY cost trajectory is what makes industrial IT/OT spend uniquely difficult to right-size.
Consumer / smart-home (Bitdefender + NETGEAR)
Bitdefender and NETGEAR's 2025 IoT Security Landscape Report, based on telemetry from 6.1 million smart homes across North America, Europe, and Australia between January and October 2025:
IoT attacks analyzed: 13.6 billion.
Vulnerability exploitation attempts: 4.6 billion.
Connected devices per household: 22 (average).
Attacks per household per day, 2025: 29 (up from 10 per day in 2024).
Share of IoT exploits targeting already-known and patched CVEs: 99.4%.
Top vulnerable categories: Streaming devices, smart TVs, and IP cameras account for "more than half" of all known vulnerabilities.
BadBox Android-based device infections: 1 million+ before leaving the factory in some 2025 cases.
22.2 Tbps consumer-router-driven DDoS: traced to compromised home routers in a 2025 incident detailed in the same report.
The headline is that the average North American household now sits at 22 connected devices and absorbs 29 attempted attacks per day. Consumer-grade gear is a meaningful contributor to global botnet horsepower, not just a personal-privacy concern.
Manufacturing, energy, transportation
Manufacturing's #1-targeted industry status from IBM and ENISA, paired with Dragos's 1,693 industrial-targeted ransomware attacks, makes manufacturing the modal IoT and OT incident vertical in 2026. Energy and water utilities sit close behind. Transportation and digital infrastructure follow per ENISA's EU sample.
Smart cities and government
ENISA's 38.2% public-administration share is the bellwether for smart-city programs. The same exposed wireless networks and consumer-grade IP cameras Forescout flags as enterprise risk also sit on municipal CCTV grids and transit networks.
Notable named incidents
Lviv heating utility, January 2024 (FrostyGoop, US dollar cost not publicly disclosed). First publicly documented ICS Modbus-abuse malware. 600+ apartment buildings without heat for nearly two days mid-winter (The Register; Dragos).
Volt Typhoon KV-Botnet takedown, January 2024. FBI and DOJ remotely killed China-linked covert router botnet built on EOL Cisco, Netgear, and Fortinet gear (DOJ press release). Volt Typhoon began rebuilding the botnet within weeks.
CovertNetwork-1658 / Quad7 / Storm-0940, October 2024. Microsoft attributed a 16,000-router (mostly TP-Link) botnet to Chinese threat actor Storm-0940 conducting Microsoft 365 password spray (Microsoft Threat Intelligence).
Cloudflare 5.6 Tbps Mirai-based DDoS, October 29, 2024. Eastern Asia ISP target, 13,000-device Mirai variant, 80-second duration, fully autonomous mitigation, no impact (Cloudflare).
Microsoft Azure 15.72 Tbps Aisuru DDoS, October 24, 2025. 3.64 Bpps, 500,000+ source IPs (The Hacker News on Microsoft Azure).
Cloudflare 29.7 Tbps Aisuru DDoS, late 2025. 14.1 Bpps, 69-second UDP carpet-bomb, 15,000 destination ports per second (Cloudflare Q3 2025).
NETSCOUT 30 Tbps peak demonstration attack, 2H 2025. 4 Bpps, primarily IoT-botnet-driven (NETSCOUT Issue 16).
Regulatory landscape
The legal scaffolding around connected products is finally in place.
EU Cyber Resilience Act (CRA)
The EU CRA entered into force on December 10, 2024 with phased application:
June 11, 2026: Notification of conformity assessment bodies provisions begin.
September 11, 2026: Manufacturers must notify ENISA and the relevant national authority of actively exploited vulnerabilities and severe incidents within 24 hours of becoming aware.
December 11, 2027: Main obligations apply across all "products with digital elements," including connected home cameras, fridges, TVs, and toys. About 90% of products fall in the default risk class (consumer electronics and lower-risk IoT). Higher-risk classes face conformity assessments.
UK PSTI Act
The UK Product Security and Telecommunications Infrastructure Act 2022 and the 2023 PSTI Regulations entered into force on April 29, 2024. Manufacturers, importers, and distributors of connectable consumer products sold in the UK must comply with security requirements including a ban on universal default passwords, vulnerability disclosure mechanisms, and a published support period for security updates. The UK Office for Product Safety and Standards (OPSS) enforces. Maximum penalties: £10 million or 4% of global qualifying turnover, whichever is greater.
US Cyber Trust Mark
The FCC voted on March 14, 2024 to adopt rules for a voluntary cybersecurity labeling program for wireless consumer IoT products. The rule became effective August 29, 2024. UL Solutions was named Lead Administrator initially, then withdrew effective December 19, 2025. ioXt Alliance assumed Lead Administrator duties on April 13, 2026 (FCC public notice). Eligible product categories include internet-connected home security cameras, voice-activated shopping devices, smart appliances, fitness trackers, garage door openers, and baby monitors. The program is voluntary, but federal agency procurement and consumer pressure are expected to drive de facto adoption through 2026 and 2027.
NIST and ETSI standards
NIST's IoT Cybersecurity for the Federal Government program (under the IoT Cybersecurity Improvement Act of 2020) produced the foundational profile (NISTIR 8259 series). ETSI EN 303 645 is the European functional analogue, and the UK PSTI requirements borrow heavily from it. Both are now de facto buyer baselines.
What this means for defenders
Treat the perimeter and the edge as the new ransomware front door. Verizon DBIR 2025's eightfold rise in edge-device exploitation, paired with median time-to-mass-exploitation of zero days for the most critical CVEs, means edge patching beats endpoint patching for initial-access prevention. Use the Stingrai network penetration testing service to validate that VPN, firewall, and remote-access devices are not your softest path in.
Inventory and segment connected devices before negotiating the next firewall renewal. Palo Alto Networks' 77.74% poor-segmentation finding is the operative number. If a smart coffee maker and an Active Directory domain controller can talk, no amount of EDR will prevent lateral movement post-compromise. Segmentation is plumbing, not feature work.
Rotate default credentials. Every device. Every time. Phosphorus's 75% default-password figure is the easiest, cheapest, highest-impact control on the list. Aisuru's primary spread mechanism is exactly this gap. Deploy automated credential rotation if manual rotation does not stick.
Pull IoMT into your KEV remediation cadence. Asimily's 99% / 96% / 89% / 77% / 35% sequence on hospital IoMT devices means the bulk of medical devices in service are already on CISA's KEV list. The HHS HPH Cybersecurity Performance Goals and FDA pre-market guidance are tightening; do the work before regulators do it for you.
Build OT incident response retainer relationships now. Dragos's 75% partial-OT-shutdown rate among ransomware incidents is the operating-impact baseline. IBM's 199-day-to-identify and 73-day-to-contain industrial breach windows are the cost driver. The Stingrai red team and adversary simulation engagements include OT scoping and tabletop exercises.
Map the regulatory clock to your product roadmap. EU CRA reporting starts September 11, 2026. UK PSTI is live now. US Cyber Trust Mark labeling is coming through ioXt in 2026 and 2027. SBOM, signed firmware, vulnerability disclosure, and a published security update window are no longer differentiators; they are buyer-mandatory in regulated jurisdictions.
Run controlled offensive drills. Stingrai's penetration testing engagements, founded in 2021, include device-class testing for cameras, NVRs, gateways, and routers. We rehearse the same Telnet brute force, default-credential pivot, and CVE-exploitation paths Aisuru uses, on customer-permitted scope. The data above tells defenders what to expect; controlled drills tell defenders where their environment actually breaks.
Forward projection (2026 trajectory)
Projections should be labeled as projections. The named primary publishers project the following through 2026 and 2027:
IoT Analytics: 21.1B connected IoT devices end of 2025, on a 13.2% CAGR toward 39B by 2030 (State of IoT 2025).
Cloudflare: continued hyper-volumetric DDoS growth driven by Aisuru and successor TurboMirai variants, with operators monetizing residential-proxy access on top of DDoS-for-hire (Cloudflare Q3 2025).
NETSCOUT: further integration of dark-web LLMs into DDoS-for-hire platforms; underground forum mentions of malicious AI tools rose 219% through 2H 2025 and the trajectory is upward (NETSCOUT Issue 16).
Dragos: continued growth in OT-targeting threat groups beyond the 23 currently tracked, with VOLTZITE and Volt Typhoon overlap driving infrastructure-mapping at scale (Dragos 2024).
EU Commission: September 11, 2026 CRA reporting threshold and December 11, 2027 main-obligations cliff (EU Commission).
No primary source known to us as of April 25, 2026 has published a credible full-year 2026 IoT attack number; we list no 2026 retrospective stats because none exist yet.
FAQ
What is the most-cited IoT attack statistic for 2026?
For attack volume, SonicWall's 2025 Cyber Threat Report +124% YoY rise in IoT attacks in 2024, with 17 million+ blocked attacks against IoT cameras alone, is the most-cited single number. For botnet horsepower, Cloudflare's 29.7 Tbps Q3 2025 Aisuru attack and Microsoft Azure's 15.72 Tbps Aisuru attack on October 24, 2025 anchor the DDoS conversation. For OT impact, Dragos's 1,693 industrial ransomware attacks in 2024 (+87% YoY) is the canonical reference.
How big is the IoT botnet problem in 2026?
The largest known IoT botnet, Aisuru, sits at an estimated 300,000 to 700,000 compromised devices (Krebs on Security; BSI). Industry research tracks 116+ Mirai variant branches and a 50% YoY rise in Mirai-related command-and-control infrastructure. NETSCOUT counted 8 million+ DDoS attacks in 2H 2025 alone, with peak attacks reaching 30 Tbps and 4 billion packets per second.
Which industries were hit hardest by IoT and OT attacks in 2024 and 2025?
Manufacturing has been the #1-targeted industry for four consecutive years per IBM X-Force Threat Intelligence Index 2025. Dragos counted 1,693 ransomware attacks against industrial organizations in 2024, 87% more than 2023. Healthcare and connected medical devices come close behind: Asimily's 2025 IoMT data reports 99% of hospitals manage IoMT devices with KEVs and 96% of those KEVs are linked to ransomware. ENISA's EU corpus puts public administration at 38.2% of incidents, transport at 7.5%, finance at 4.5%, and manufacturing at 2.9% (with 59.3% of manufacturing attacks being cybercriminal).
What is the largest IoT-driven DDoS attack on record?
Cloudflare's Q3 2025 mitigation of a 29.7 Tbps and 14.1 billion packets per second Aisuru attack, lasting 69 seconds in a UDP carpet-bombing pattern across an average of 15,000 destination ports per second, is the largest single attack on public record at this writing. NETSCOUT separately recorded peak demonstration attacks of 30 Tbps and 4 billion packets per second across 2H 2025 (NETSCOUT Issue 16). Microsoft Azure's 15.72 Tbps Aisuru attack on October 24, 2025 from 500,000+ source IPs is the largest cloud-platform-recorded single attack to date.
What are the most-exploited IoT vulnerabilities?
SonicWall's 2025 Cyber Threat Report names two Hikvision IP camera CVEs as the most-exploited IoT flaws of 2024: CVE-2021-36260 (command injection) and CVE-2017-7921 (authentication bypass). Both are years old, both have public patches, both still account for tens of millions of attempted exploitations because the cameras run firmware that was never updated. Verizon DBIR 2025 found edge-device and VPN exploitation surged from 3% to 22% of all initial-access exploits, with median time from CVE publication to mass exploitation of zero days for the most critical edge CVEs.
How many ICS advisories did CISA publish in 2024 and 2025?
CISA published 423 ICS advisories in 2024 and 508 in 2025, per SOCRadar's aggregation of the official CISA feed. The 2024 to 2025 period covered hundreds of vulnerabilities across more than 200 vendors and 700+ products. Critical manufacturing accounted for 75% of all CISA ICS CVEs in the six-month window analyzed by Nozomi Networks Labs in February 2025.
What share of IoT devices ship with default passwords?
Phosphorus's 2025 research put the figure at 75% across IoT, OT, IoMT, and IIoT classes. Vendor-default credentials persist on cameras, printers, HVAC controllers, medical devices, kiosks, and badge readers, and they are the primary spread mechanism for the Aisuru botnet, which scans Telnet for default credentials and enrolls compromised devices automatically.
What does the EU Cyber Resilience Act require of IoT manufacturers?
The EU Cyber Resilience Act entered into force December 10, 2024. Vulnerability and incident reporting begin September 11, 2026, with manufacturers required to notify ENISA and their national authority within 24 hours of becoming aware of an actively exploited vulnerability or severe incident. Main obligations apply from December 11, 2027 across all "products with digital elements," including consumer IoT. About 90% of products sit in the default risk class. Penalties for non-compliance can reach 2.5% of global annual turnover or 15 million euros, whichever is higher (per the Regulation text).
What does the UK PSTI Act require?
The UK PSTI Act has been in force since April 29, 2024. Manufacturers, importers, and distributors of consumer connectable products in the UK must ban universal default passwords, publish vulnerability disclosure mechanisms, and declare a minimum security-update support period. The Office for Product Safety and Standards (OPSS) enforces. Maximum penalties: £10 million or 4% of global qualifying turnover, whichever is greater.
What is the US Cyber Trust Mark?
The US Cyber Trust Mark is the FCC's voluntary cybersecurity labeling program for wireless consumer IoT products. The rule became effective August 29, 2024 after the March 14, 2024 FCC vote. ioXt Alliance assumed Lead Administrator responsibilities on April 13, 2026, after UL Solutions withdrew on December 19, 2025. Eligible product categories include connected home security cameras, voice-activated shopping devices, smart appliances, fitness trackers, garage door openers, and baby monitors.
How much does an IoT or OT incident cost?
IBM's Cost of a Data Breach 2025 reports an average healthcare data breach cost of US$7.42 million in 2025 (-24% YoY). IBM's 2024 Industrial Sector report put the industrial-sector average breach cost at US$5.56 million (+18% YoY), with 199 days to identify and 73 days to contain versus the global averages of 194 days and 64 days. Direct OT-impact costs (production stoppage, regulatory penalties, equipment replacement) are not always captured in these averages and can run substantially higher in named incidents.
How can organizations defend against IoT and OT attacks?
Six practical steps that the data supports. First, inventory connected devices and segment them at the network layer; Palo Alto Networks' 77.74% poor-segmentation figure is the modal exposure. Second, rotate default credentials on every device; Phosphorus's 75% number is the explanatory variable behind Aisuru's spread. Third, patch edge devices ahead of endpoints; Verizon DBIR 2025's eightfold rise in edge exploitation says where the front door has moved. Fourth, treat IoMT KEVs as a board-level remediation priority; Asimily's 99% / 96% sequence is the regulator-attention-attractor. Fifth, run controlled offensive drills against device-class scope; the Stingrai penetration testing and red team services cover IoT, OT, and connected-device assessments. Sixth, monitor the EU CRA, UK PSTI, and US Cyber Trust Mark clocks against your product roadmap so security disclosures and update windows are buyer-grade.
Where can I get the latest IoT and OT attack data?
The primary publishers to track are SonicWall (annual Cyber Threat Report and mid-year update), Cloudflare (quarterly DDoS Threat Reports on their Radar dashboard), NETSCOUT (semi-annual DDoS Threat Intelligence Report), Microsoft (Microsoft Threat Intelligence blog and annual Digital Defense Report), Dragos (annual OT Cybersecurity Year in Review), Nozomi Networks Labs (semi-annual OT/IoT Security Report), Forescout Vedere Labs (annual Riskiest Connected Devices report and ad-hoc vulnerability disclosures), Palo Alto Networks Unit 42 (annual Device Security Threat Report and threat-bulletin newsletter), Verizon (annual Data Breach Investigations Report), IBM X-Force (annual Threat Intelligence Index and Cost of a Data Breach Report), Bitdefender + NETGEAR (annual IoT Security Landscape Report), Asimily and Phosphorus (vendor research on healthcare and IoT respectively), CISA (ICS Advisories feed), and ENISA (annual Threat Landscape report). The Stingrai research blog mirrors these updates as they publish.
References
IoT Analytics. State of IoT 2025: Number of Connected IoT Devices Growing 14% to 21.1 Billion Globally. October 2025. https://iot-analytics.com/number-connected-iot-devices/. Hamburg-based research firm tracking the global connected device population, by connectivity type and forecast trajectory.
IoT Analytics. State of IoT 2024: Number of Connected IoT Devices Growing 13% to 18.8 Billion. September 2024. https://iot-analytics.com/wp-content/uploads/2024/09/INSIGHTS-RELEASE-Number-of-connected-IoT-devices-vf.pdf. Prior-year baseline.
SonicWall. 2025 Cyber Threat Report: The Need for Speed. February 2025. https://www.sonicwall.com/resources/white-papers/2025-sonicwall-cyber-threat-report. Capture Labs telemetry across IoT, malware, encrypted traffic, and exploit-weaponization speed for CY 2024.
Cloudflare. DDoS Threat Report Q3 2025, including Aisuru, the apex of botnets. November 2025. https://blog.cloudflare.com/ddos-threat-report-2025-q3/. Quarterly mitigation telemetry across the Cloudflare network.
The Hacker News on Microsoft Azure DDoS Protection. Microsoft Mitigates Record 15.72 Tbps DDoS Attack Driven by AISURU Botnet. November 2025. https://thehackernews.com/2025/11/microsoft-mitigates-record-572-tbps.html. Public record of the October 24, 2025 attack.
NETSCOUT. DDoS Threat Intelligence Report Issue 16: Findings from 2H 2025. March 2026. https://www.netscout.com/threatreport/wp-content/uploads/2026/03/NETSCOUT-2H-2025-Threat-Report.pdf. ATLAS telemetry covering July to December 2025.
NETSCOUT ASERT. Threat Summary: Aisuru and Related TurboMirai Botnet DDoS Attack Mitigation and Suppression, October 2025 v1.0. October 2025. https://www.netscout.com/blog/asert/asert-threat-summary-aisuru-and-related-turbomirai-botnet-ddos. Source for Eleven11 / RapperBot tracking.
Krebs on Security. Aisuru Botnet Shifts from DDoS to Residential Proxies. October 2025. https://krebsonsecurity.com/2025/10/aisuru-botnet-shifts-from-ddos-to-residential-proxies/. Aisuru attribution and operator-monetization analysis based on XLab data.
Bundesamt für Sicherheit in der Informationstechnik (BSI). Botnet Profile: Aisuru. 2025. https://www.bsi.bund.de/EN/Themen/Verbraucherinnen-und-Verbraucher/Cyber-Sicherheitslage/Methoden-der-Cyber-Kriminalitaet/Botnetze/Steckbriefe-aktueller-Botnetze/Steckbriefe/Aisuru/aisuru.html. German federal botnet profile.
Microsoft Threat Intelligence. Chinese Threat Actor Storm-0940 Uses Credentials from Password Spray Attacks from a Covert Network. October 31, 2024. https://www.microsoft.com/en-us/security/blog/2024/10/31/chinese-threat-actor-storm-0940-uses-credentials-from-password-spray-attacks-from-a-covert-network/. CovertNetwork-1658 / Quad7 disclosure.
US Department of Justice. US Government Disrupts Botnet People's Republic of China Used to Conceal Hacking of Critical Infrastructure. January 31, 2024. https://www.justice.gov/archives/opa/pr/us-government-disrupts-botnet-peoples-republic-china-used-conceal-hacking-critical. Volt Typhoon KV-Botnet takedown.
Verizon. 2025 Data Breach Investigations Report. April 2025. https://www.verizon.com/business/resources/T16f/reports/2025-dbir-data-breach-investigations-report.pdf. Annual breach corpus with edge / VPN exploitation analysis.
Forescout Vedere Labs. The Riskiest Connected Devices of 2025. April 2025. https://www.forescout.com/research-labs/the-riskiest-devices-of-2025/. Fifth annual Device Cloud risk-scoring research.
Palo Alto Networks. 2025 Device Security Threat Report. 2025. https://www.paloaltonetworks.com/resources/infographics/device-security-threat-2025. Telemetry across 27M devices and 1,803 enterprise customers.
Dragos. 8th Annual OT Cybersecurity Year in Review. February 2025. https://www.dragos.com/blog/dragos-8th-annual-ot-cybersecurity-year-in-review-is-now-available. CY 2024 OT incident corpus.
Dragos. Intel Brief: Impact of FrostyGoop ICS Malware on Connected OT Systems. July 2024. https://hub.dragos.com/report/frostygoop-ics-malware-impacting-operational-technology. FrostyGoop disclosure.
Nozomi Networks Labs. OT/IoT Cybersecurity Trends and Insights, February 2025. February 2025. https://www.nozominetworks.com/ot-iot-cybersecurity-trends-insights-february-2025. CISA ICS CVE analysis plus customer telemetry.
ENISA. Threat Landscape 2025. October 2025. https://www.enisa.europa.eu/publications/enisa-threat-landscape-2025. EU corpus across ~4,900 incidents July 2024 to June 2025.
IBM X-Force. Threat Intelligence Index 2025. April 2025. https://www.ibm.com/reports/threat-intelligence. Annual threat-actor and industry-targeting analysis.
IBM Security. Cost of a Data Breach Report 2025. July 2025. https://www.ibm.com/reports/data-breach. Healthcare and global breach economics.
IBM Security. Cost of a Data Breach Report 2024 (Industrial Sector). 2024. https://www.ibm.com/think/insights/cost-of-a-data-breach-industrial-sector. Industrial-sector breach cost and timeline.
Bitdefender + NETGEAR. 2025 IoT Security Landscape Report. October 2025. https://blogapp.bitdefender.com/hotforsecurity/content/files/2025/10/2025_iot_security_report.pdf. Smart-home telemetry across 6.1M households.
Asimily (via HIPAA Journal). 99% of Healthcare Orgs Managing IoMT Devices with Known Exploited Vulnerabilities. 2025. https://www.hipaajournal.com/99-of-healthcare-orgs-managing-iomt-devices-with-known-exploited-vulnerabilities/. Asimily 2025 IoMT data.
Asimily (via Infosecurity Magazine). 89% of Healthcare Organizations Use the Most Vulnerable IoT Devices. 2025. https://www.infosecurity-magazine.com/news/healthcare-vulnerable-iot-devices/. Additional Asimily data points.
Phosphorus. It's 2025. Are You Ok With Default Passwords? 2025. https://phosphorus.io/its-2025-are-you-ok-with-default-passwords/. IoT default-credential research.
Kaspersky ICS-CERT. Threat Landscape for Industrial Automation Systems, Q1 2025. May 2025. https://ics-cert.kaspersky.com/publications/reports/2025/05/15/threat-landscape-for-industrial-automation-systems-q1-2025/. Quarterly ICS blocked-malware percentages.
EU Commission. Cyber Resilience Act. December 2024 in force. https://digital-strategy.ec.europa.eu/en/policies/cyber-resilience-act. Authoritative regulation text and timeline.
UK GOV. Product Security and Telecommunications Infrastructure (Product Security) Regime. Effective April 29, 2024. https://www.gov.uk/government/publications/the-uk-product-security-and-telecommunications-infrastructure-product-security-regime. UK PSTI Act and Regulations.
FCC. US Cyber Trust Mark Program. Rule effective August 29, 2024. https://www.fcc.gov/CyberTrustMark. FCC public materials and program updates.
FCC Public Notice DA-26-18A1. Approval of ioXt Alliance as Lead Administrator for the U.S. Cyber Trust Mark Program. April 13, 2026. https://docs.fcc.gov/public/attachments/DA-26-18A1.pdf.
Mazebolt. Aisuru Turbo Mirai-class IoT Botnet: Lessons for Continuous DDoS Readiness. November 2025. https://mazebolt.com/blog/aisuru-turbo-mirai-class-iot-botnet-lessons-for-continuous-ddos-readiness. Aggregation of Mirai-variant tracking and C2 infrastructure growth.
Securelist (Kaspersky). Desktop and IoT Malware Report Q3 2025. Q3 2025. https://securelist.com/malware-report-q3-2025-pc-iot-statistics/118020/. SSH and Telnet honeypot telemetry.
The Register. FrostyGoop ICS Malware Used to Shut Down Heat in Ukraine Attack. July 23, 2024. https://www.theregister.com/2024/07/23/frostygoop_ics_malware/. Public record of the Lviv heating-utility incident.
BleepingComputer. Volt Typhoon Rebuilds Malware Botnet Following FBI Disruption. 2024. https://www.bleepingcomputer.com/news/security/volt-typhoon-rebuilds-malware-botnet-following-fbi-disruption/. Post-takedown KV-Botnet activity.
SOCRadar. CISA Industrial Control Systems (ICS) Advisories Recap for 2025. Early 2026. https://socradar.io/blog/cisa-industrial-control-systems-ics-advisories-2025/. Aggregation of CISA ICS advisory feed counts.
This is the Stingrai research team's 2026 IoT, IIoT, and OT attack-statistics reference. Stingrai, founded in 2021, is an offensive security firm running penetration testing, red team, and adversary-simulation engagements for global customers. If you want to see how your edge devices, connected gear, or OT environment hold up against the Aisuru-style propagation patterns documented above, our services page lists what we run and how to start a scoping call.