A working username and password remained the single most reliable on-ramp into a 2025 enterprise breach. Verizon's 2025 Data Breach Investigations Report pinned compromised credentials as the initial access vector in 22% of the 12,195 confirmed breaches it analyzed, leading vector for the second consecutive year, and 88% of Basic Web Application attacks involved stolen credentials. HaveIBeenPwned absorbed the Synthient Credential Stuffing corpus on November 5, 2025, adding 1,957,476,021 unique email addresses and 1.3 billion unique passwords, of which 625 million had never previously appeared in the Pwned Passwords service. Microsoft's Digital Defense Report 2025 confirmed that more than 97% of identity attacks are password attacks and that identity-based attacks surged 32% in the first half of 2025 alone. The credential is the breach.
Three forces drove the 2025-2026 picture. Stealer-log volume. Recorded Future's 2025 Identity Threat Landscape Report detected 1.95 billion malware combo-list credential exposures across the calendar year and 276 million credentials with active session cookies usable to bypass MFA. Identity-data-broker scale. SpyCloud's 2026 Identity Exposure Report grew the recaptured datalake 23% YoY to 65.7 billion distinct identity records, recapturing 8.6 billion stolen session cookies and 642.4 million credentials from 13.2 million infostealer infections during 2025. Cost of compromise. IBM's 2025 Cost of a Data Breach Report priced compromised-credential breaches at US$4.67M per incident with a 246-day mean time to identify and contain. The data is for CISOs, identity teams, journalists, and security buyers building 2026 budget cases.
This post is the Stingrai research team's canonical 2026 reference for compromised credentials. It assembles 75+ numeric claims from 22 named primary publishers, including Verizon, HaveIBeenPwned, SpyCloud, Recorded Future, Microsoft, IBM, Mandiant (Google Cloud), CrowdStrike, Specops Software (Outpost24), Constella Intelligence, Cloudflare, Akamai, Auth0/Okta, Cofense, Rapid7, Anthropic, FBI IC3, ITRC, Flare, SOCRadar, Europol, and the U.S. SEC (via 8-K filings). Lead data is full-year 2024 and 2025 telemetry, the freshest available; primary publishers have not yet released full-year 2026 reports as of April 2026. Every figure carries its source, year, and methodology window so any claim can be audited inline. For password-composition behavior such as top-200 most-common passwords, NIST SP 800-63B guidance, MFA adoption, and passkey rollouts, see Stingrai's complementary Password Statistics 2026.
TL;DR: 12 labeled key stats
Compromised credentials as initial breach vector (Verizon 2025 DBIR): 22% of 12,195 confirmed breaches, leading vector for the second consecutive year (Verizon 2025 DBIR).
Stolen credentials in Basic Web Application attacks (Verizon 2025 DBIR): 88% (Verizon 2025 DBIR).
Synthient Credential Stuffing corpus loaded into HIBP (November 5, 2025): 1,957,476,021 unique emails, 1.3 billion unique passwords, 625 million passwords entirely new to Pwned Passwords (Troy Hunt).
Synthient Stealer Log corpus (October 21, 2025): 23 billion records, 183 million unique emails, 16.4 million entirely new (Troy Hunt).
Malware combo-list credential exposures indexed in 2025 (Recorded Future): 1.95 billion, with 276 million carrying active session cookies (Recorded Future, March 2026).
SpyCloud 2026 datalake (recaptured identity records): 65.7 billion (+23% YoY); 8.6 billion stolen session cookies recaptured in 2025 alone; 642.4 million credentials from 13.2 million infostealer infections (SpyCloud 2026 IER).
Specops 2026 Breached Password Report (malware-stolen passwords analyzed in 2025): more than 6 billion, with LummaC2 accounting for nearly 60% of credentials attributable to infostealers (Specops 2026).
Microsoft daily identity attacks tracked: 600 million, more than 99% password-based (Microsoft Digital Defense Report 2024 update, carried forward 2025); 80% of MFA-bypass breaches now via session-token theft via AiTM kits (MDDR 2025).
Microsoft Lumma takedown (May 2025): 394,000 Windows devices infected between March 16 and May 16, 2025; 2,300 malicious domains seized (Microsoft Security Blog, 21 May 2025).
Cost of compromised-credential breaches (IBM 2025): US$4.67M per incident, 246-day mean time to identify and contain (IBM Cost of a Data Breach 2025).
Snowflake 2024 incident (Mandiant disclosure): approximately 165 customer organizations notified; 79.7% of accounts UNC5537 used had prior credential exposure from infostealers, some dating back to 2020 (Mandiant / Google Cloud); AT&T disclosed nearly 110 million customers impacted on July 12, 2024, in an SEC 8-K (Cybersecurity Dive).
Cloudflare login telemetry (March 2025): 64% of all authorization requests, 65% of bot requests, and 44% of human requests used leaked credentials; 41% of successful logins on protected sites involve compromised passwords (Cloudflare Radar / Cloudflare blog, March 2025).
Key takeaways
Stolen credentials remained the leading initial breach vector for the second straight year, even as IBM's 2025 attribution shifted phishing slightly ahead in absolute frequency. Verizon's 2025 DBIR measured credentials at 22% of initial vectors. IBM's 2025 Cost of a Data Breach Report priced phishing at 16% of breaches and US$4.8M, and credential breaches at US$4.67M with a 246-day containment window. The underlying outcome converged: an attacker entering with a working username and password.
Infostealer logs and combo-list credentials are now the dominant supply pipeline, not brute force. Recorded Future indexed 1.95 billion malware combo-list credential exposures in 2025, with the average compromised device yielding 87 stolen credentials. SpyCloud recaptured 642.4 million credentials from 13.2 million infostealer infections in 2025 alone, and Specops analyzed more than 6 billion malware-stolen passwords across the same year, with LummaC2 alone accounting for nearly 60% of credentials.
Session-cookie theft via adversary-in-the-middle kits is the dominant MFA-bypass route in 2025. Microsoft's 2025 Digital Defense Report attributed 80% of MFA-bypass breaches to session-token theft, and Recorded Future found 276 million indexed credentials carried active session cookies. Tycoon 2FA alone accounted for about 62% of phishing attempts Microsoft blocked by mid-2025, generating tens of millions of phishing emails per month before the Europol-led takedown in March 2026.
Snowflake's 2024 cluster of incidents was the marquee proof point for the credential-economy thesis. Mandiant attributed 79.7% of the accounts UNC5537 used to prior infostealer compromise, some of those credentials dating back to 2020. AT&T's July 12, 2024 SEC 8-K disclosure named 110 million affected customers, on instances without MFA configured.
The dark-web credential economy now prices on freshness and access scope, not raw count. Stealer-log subscriptions run US$100 to US$200 per month; individual stealer logs sell for US$5 to US$50 each; initial-access broker transactions averaged US$1,328 per Rapid7's 2025 dataset, with Fortune 500 listings ranging up to US$50,000. AiTM kits like Tycoon 2FA list at US$120 for 10 days or US$350 a month. The economics now favor renting access rather than cracking it.
Methodology
Sources used: Verizon 2025 DBIR (12,195 confirmed breaches, 22,052 incidents, May 2024 to October 2024 collection window, published May 2025) and supporting research notes on credential stuffing; HaveIBeenPwned + Troy Hunt blog posts on the Synthient Stealer Log Threat Data (loaded October 21, 2025) and the Synthient Credential Stuffing Threat Data (loaded November 5, 2025); SpyCloud Annual Identity Exposure Report 2025 (March 2025) and 2026 (March 2026); Recorded Future 2025 Identity Threat Landscape Report (March 2026, full-year 2025 indexing); Microsoft Digital Defense Report 2025 (October 2025) and Microsoft Security Blog Lumma takedown (May 21, 2025) plus Tycoon 2FA inside-look (March 2026); IBM Cost of a Data Breach 2025 (August 2025) and IBM X-Force Threat Intelligence Index 2025 (April 2025) plus 2026 (February 2026); Mandiant M-Trends 2025 (April 2025) and Google Cloud blog on UNC5537 Snowflake activity (June 2024); CrowdStrike 2025 Global Threat Report (February 2025); Specops Breached Password Report 2026 (January 2026) and 2025 (January 2025); Constella Intelligence 2025 Identity Breach Report (April 2025); Cloudflare credential reuse and Radar bot analyses (March 2025); Auth0 Customer Identity Trends Report 2025 (March 2025); Akamai State of the Internet historical anchor; Cofense 2025 Annual State of Phishing; Rapid7 Initial Access Broker Report 2025 (December 2025); Anthropic Threat Intelligence Reports for August 2025 and November 2025; FBI IC3 2024 Internet Crime Report (April 2025); ITRC 2024 Annual Data Breach Report (January 2025); Flare and SOCRadar on stealer-log dark-web pricing; Europol coordinated takedown notices for Lumma (May 2025) and Tycoon 2FA (March 2026). Coinbase 8-K (May 14, 2025) and AT&T 8-K (July 12, 2024) used for incident-specific disclosures.
Date cutoff: April 25, 2026. Lead data is full-year 2024 or 2025 telemetry where a primary publisher has released it. No 2026 retrospective stats appear because no primary publisher has released a credible full-year 2026 report yet. Statistics that could not be reached on at least one verification pass against a named primary source were dropped rather than estimated. Vendor blogs, AI-generated summaries, and aggregator articles are cited only where they constitute the public record of an event the primary source has not republished directly. Where multiple primary publishers tracked the same metric (e.g., total credentials exposed in 2025), the post reconciles each publisher's scope explicitly rather than averaging or selecting a single headline number.
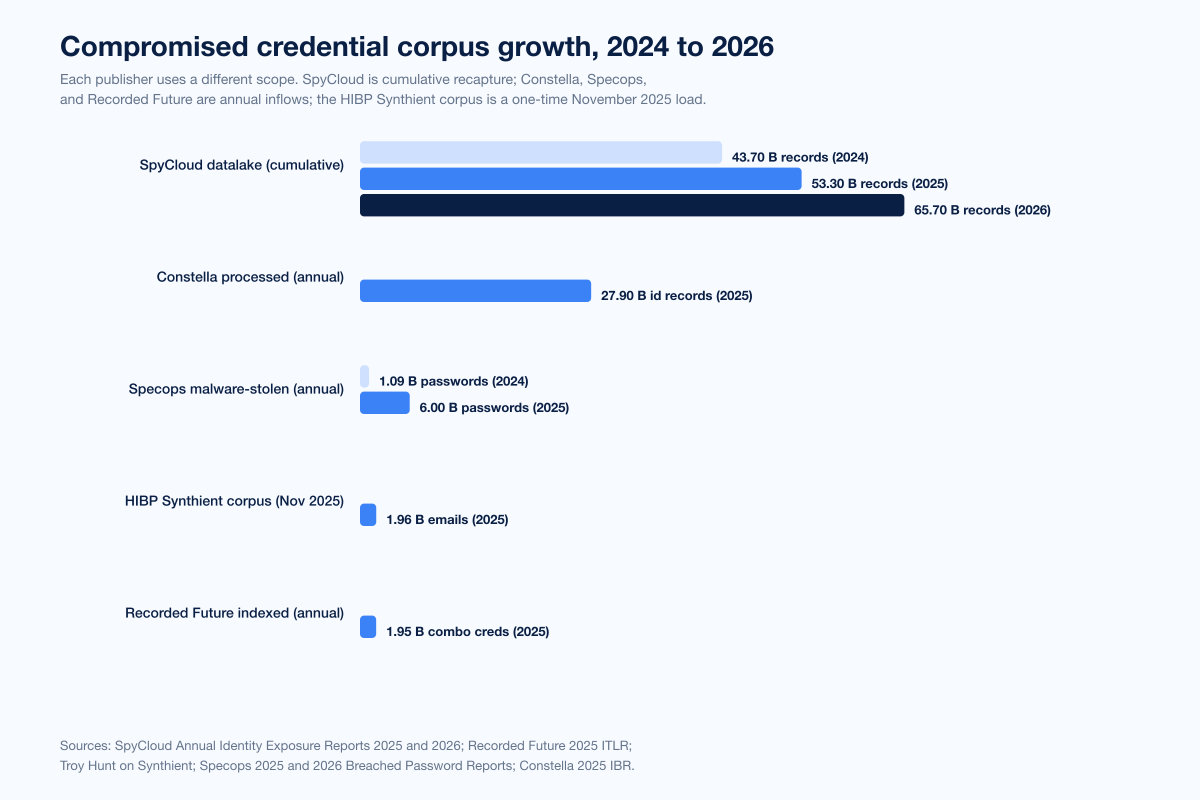
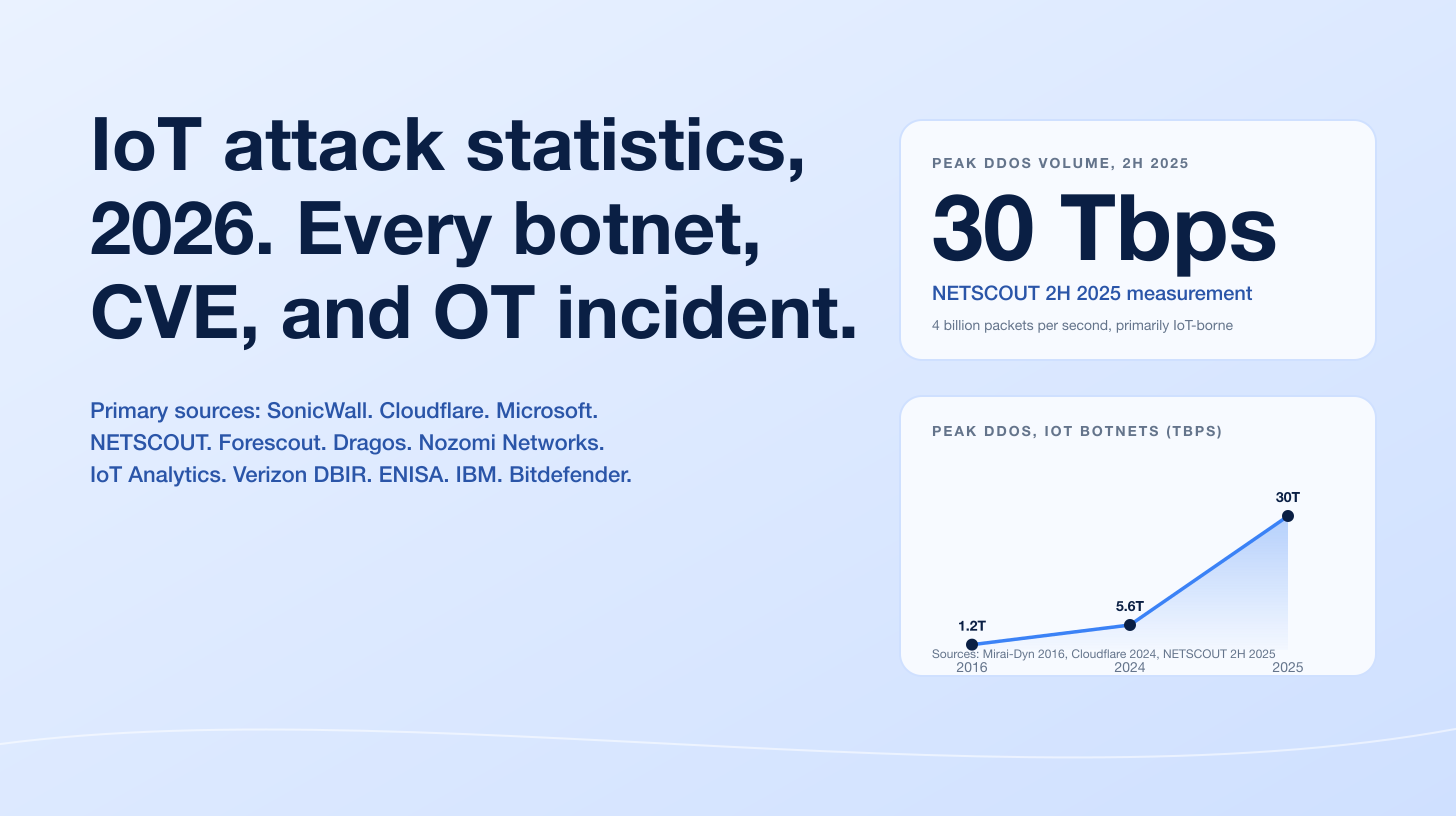
Figure 1: Compromised-credential corpus growth across primary publishers, 2021 to 2026. SpyCloud's recaptured datalake grew from 43.7B identity records in 2024 to 53.3B in 2025 to 65.7B in 2026. Recorded Future indexed 1.95B malware combo-list credentials in 2025. HaveIBeenPwned added 1.96B unique emails and 1.3B unique passwords from the Synthient Credential Stuffing corpus alone in November 2025. Constella processed 27.9B identity records during 2025. Sources: SpyCloud 2025 IER and SpyCloud 2026 IER; Recorded Future 2025 ITLR; Troy Hunt on Synthient; Constella 2025 IBR.
How big is the credential-exposure problem in 2026?
Three independently-collected datasets agree on the trajectory and disagree on the absolute level. Each publisher uses a different scope. Reconciling them is what lets a CISO answer the simple question "how many of my users are already in a stealer log?"
Breach-level data (Verizon DBIR)
Verizon's 2025 DBIR is the primary annual reference for breach root-cause analysis. It analyzed 22,052 incidents including 12,195 confirmed data breaches. Headline credential-related findings:
Metric | 2025 DBIR figure | Source |
|---|---|---|
Compromised credentials as initial access vector | 22% (leading vector, 2nd year running) | Verizon 2025 DBIR |
Vulnerability exploitation as initial access vector | 20% | Verizon 2025 DBIR |
Stolen credentials in Basic Web Application attacks | 88% | Verizon 2025 DBIR |
Median daily share of credential stuffing in SSO authentication | 19% | |
Peak credential stuffing daily share for some orgs | up to 44% | Verizon 2025 DBIR research note |
Distinctness of passwords across services in infostealer corpora (median user) | 49% | Verizon 2025 DBIR research note |
Compromised infostealer systems that were enterprise-licensed devices | 30% | Verizon 2025 DBIR via SpyCloud summary |
Compromised systems with corporate logins that were non-managed (BYOD) | 46% | Verizon 2025 DBIR via SpyCloud summary |
Ransomware victims with prior credential exposure in infostealer logs | 54% | Verizon 2025 DBIR via SpyCloud summary |
Ransomware victims whose prior infostealer logs contained corporate emails | 40% | Verizon 2025 DBIR via SpyCloud summary |
The 49% distinctness figure is the practical mechanism behind credential stuffing: in the median infostealer-stolen account view, only roughly half of a user's passwords across different services were unique. The 19% SSO median daily share, with peak organizations hitting 44%, is the practical scale on the receiving end.
Identity-data-broker datasets (SpyCloud and Constella)
SpyCloud's 2026 Identity Exposure Report, released March 2026, summarized full-year 2025 recapture activity:
Metric | 2026 IER figure | YoY change |
|---|---|---|
Total recaptured identity records | 65.7 billion | +23% from 53.3B in 2025 IER |
Stolen session cookies/artifacts recaptured in 2025 | 8.6 billion | New, distinct from 17.3B-cumulative figure in 2025 IER |
Credential pairs recaptured in 2025 | 5.3 billion | Of which 80% of corporate credentials were plaintext |
Credentials from infostealer infections during 2025 | 642.4 million from 13.2 million infections | Granular infection-mapped figure |
API keys/tokens exposed in 2025 | 18.1 million | Non-human-identity exposure |
AI-tool credentials/cookies exposed in 2025 | 6.2 million | New 2026 NHI category |
Organizations reporting an identity-related incident in past year | 91% | Survey response |
Constella Intelligence's 2025 Identity Breach Report tracked the same problem from a different sourcing pipeline: 219,000 breach events and 107 billion exposed records analyzed for the 2024 dataset. Constella's curated identity datalake spans more than 230 billion identity records and 1.1 trillion identity assets. In 2025, Constella processed 27.9 billion identity records, a 135% YoY jump, and indexed 2.3 billion web addresses where credentials had been used (the "what platforms does this victim access" intelligence layer).
The average exposed individual in SpyCloud's 2025 dataset carries 52 usernames and 141 credential pairs across 229 exposure records tied to their identity. That is the target surface adversaries attack at scale.
Combo-list and stealer-log datasets (Recorded Future and HaveIBeenPwned)
Recorded Future's 2025 Identity Threat Landscape Report ran across full calendar year 2025:
Metric | 2025 figure | Source |
|---|---|---|
Malware combo-list credential exposures indexed | 1.95 billion | Recorded Future ITLR |
Database combo-list credential exposures indexed | 36 million | Recorded Future ITLR |
Indexed credentials with active session cookies (MFA bypass) | 276 million | Recorded Future ITLR |
Average stolen credentials per compromised device | 87 | Recorded Future ITLR |
Infostealer malware families monitored | 30+ | Recorded Future methodology |
H2 2025 vs H1 2025 indexed-credential volume increase | +50% | Recorded Future ITLR |
Q4 2025 vs Q1 2025 indexed-credential volume increase | +90% | Recorded Future ITLR |
The volume curve is the most-cited finding: H2 2025 added 50% more indexed credentials than H1, and Q4 alone produced 90% more than Q1. Compromise scale accelerated through the year, not the inverse.
HaveIBeenPwned's two Synthient corpora absorbed in late 2025 extended HIBP's coverage substantially:
Synthient corpus | Date loaded into HIBP | Records | Unique emails | New emails | Unique passwords | New passwords |
|---|---|---|---|---|---|---|
October 21, 2025 | 23 billion | 183 million | 16.4 million | not published | not published | |
November 5, 2025 | 1.96 billion email/password pairs | 1,957,476,021 | not specified | 1.3 billion | 625 million |
Among HIBP's subscribers, 2.9 million were already in the Synthient Credential Stuffing dataset, meaning roughly half of users who actively self-monitor for breach exposure were already exposed. Synthient pulled the underlying data from cybercriminal forums, Telegram channels, Tor-accessible markets, and social media leak feeds.
For per-password-composition behavior (top-200 most-common passwords, NIST guidance, complexity rules, MFA adoption, passkey rollouts) that this post deliberately does not duplicate, see the companion Password Statistics 2026 post. This post focuses on the credential economy that runs after a password leaves the user's machine.
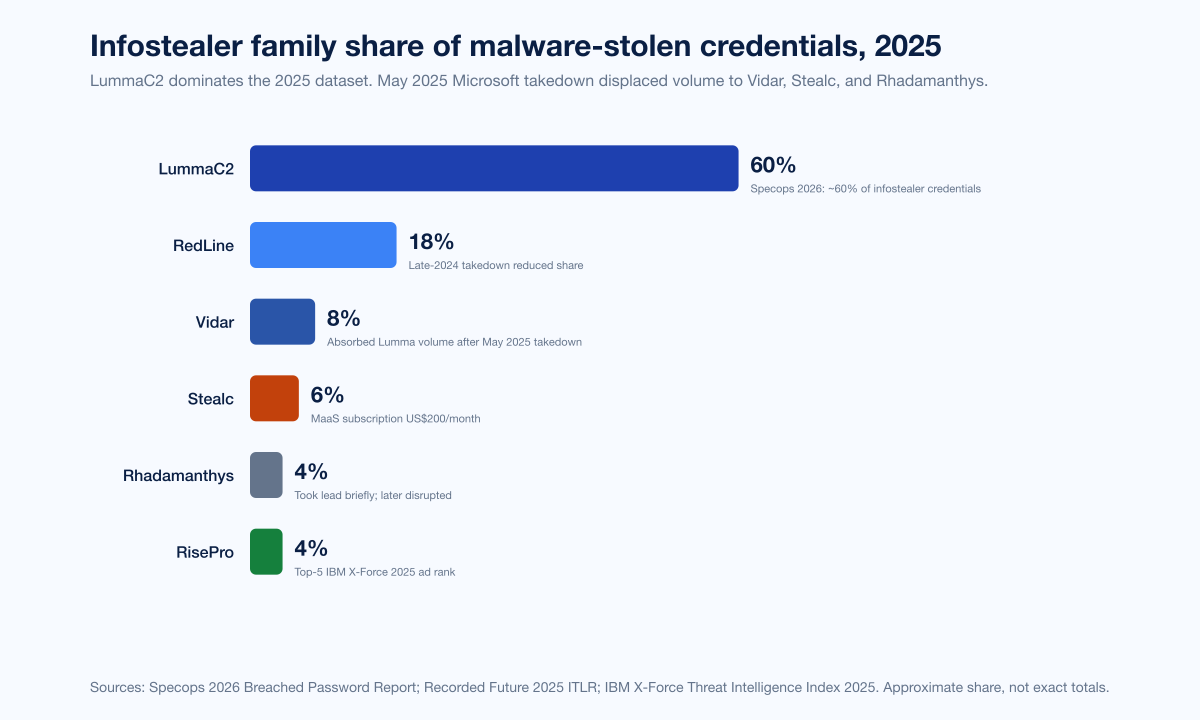
Figure 2: 2025 stealer-log family share by malware-stolen credentials. LummaC2 led nearly 60% of credentials attributed to infostealers in the Specops 2026 dataset, followed by RedLine, Vidar, Stealc, Rhadamanthys, and RisePro. Sources: Specops 2026 Breached Password Report; Recorded Future 2025 ITLR; IBM X-Force 2025.
Inside the infostealer economy
The infostealer-as-a-service market is what makes the credential numbers above actually move. A small set of malware families harvests browser-saved credentials, session cookies, MFA tokens, crypto wallets, and OAuth refresh tokens; pushes the logs into Telegram and forum-hosted markets; and the logs are bought by initial-access brokers, ransomware affiliates, and account-takeover crews.
Family share
The Specops 2026 Breached Password Report, built on more than 6 billion malware-stolen passwords from the KrakenLabs threat-intelligence team at Specops's parent Outpost24, found LummaC2 accounting for nearly 60% of credentials attributable to infostealer malware in the 2025 dataset. The 2026 edition's 6-billion total is roughly six times the 1,089,342,532 stolen passwords analyzed in the 2025 edition, reflecting both faster scale and broader ingestion.
IBM's X-Force Threat Intelligence Index 2025 added the dark-web ad-volume layer: dark-web infostealer advertisements rose 12% in 2024 over 2023, with Lumma the number-one listing by a wide margin, followed by RisePro, Vidar, Stealc, and RedLine. IBM also flagged an 84% weekly average increase in infostealers delivered via phishing emails in 2024 versus 2023, treating credential phishing as a "shadow infection vector for valid account compromise."
Recorded Future's 2025 ITLR tracked the family timeline through the year: late-2024 law enforcement action against RedLine and META consolidated activity around LummaC2 through Q2 2025; Microsoft's May 2025 Lumma takedown displaced volume to Vidar, StealC, and Rhadamanthys; Rhadamanthys was taken down later in the year, leaving Vidar in the lead position by December.
Microsoft's May 2025 Lumma takedown
Lumma takedown metric | Figure | Source |
|---|---|---|
Windows devices identified as infected, March 16 to May 16, 2025 | over 394,000 | |
Malicious domains seized | approximately 2,300 | |
Domains transferred or seized to Microsoft + redirected to sinkholes | over 1,300 | Microsoft on the Issues |
Domains coordinated with Europol | 300 | Microsoft on the Issues |
Court venue | U.S. District Court, Northern District of Georgia | Microsoft on the Issues |
Lumma is sold under a malware-as-a-service model with subscription tiers. Capabilities target browser-saved passwords, credit cards, bank accounts, cryptocurrency wallets, and session tokens; ransomware operators including Octo Tempest (Scattered Spider) used Lumma logs for initial access, per Microsoft.
Pricing across the credential economy
Flare and SOCRadar tracked stealer-log subscription and per-log pricing through 2025:
Asset | Listed price | Source |
|---|---|---|
Lumma / RedLine / Vidar / Raccoon / StealC subscription | US$100 to US$200 per month | |
StealC subscription, monthly | US$200 | |
StealC subscription, six months | US$800 | SOCRadar |
Individual stealer log (per machine) | US$5 to US$50 | Flare |
Average dark-web stealer-log bot | ~US$10 | Flare |
AiTM kit (Tycoon 2FA) admin panel, monthly | US$350 | |
AiTM kit (Tycoon 2FA), 10-day starter | US$120 | Barracuda summary |
Initial-access broker bundle, average base price | US$2,726 | |
IAB bundle, average transaction price | US$1,328 | Rapid7 IAB Report 2025 |
IAB bundle, low-end (small business access) | from US$500 | Rapid7 IAB Report 2025 |
IAB bundle, top-tier (Fortune 500 with Domain Admin) | up to US$50,000 | Rapid7 IAB Report 2025 |
Premium pricing stacks on freshness. A stealer log generated in the last 24 to 48 hours has not yet had its session tokens rotated by the victim, so the same data sells for many multiples of an aged log.
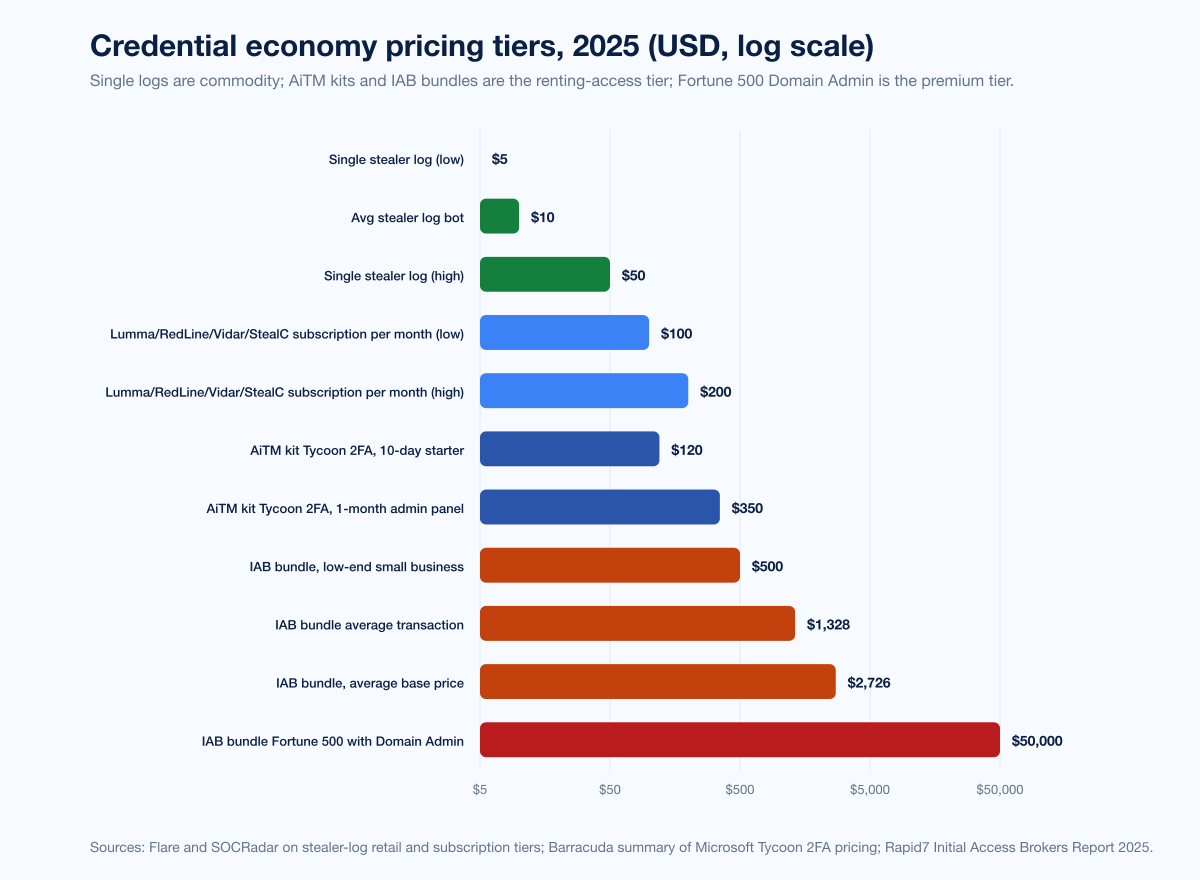
Figure 3: 2025 dark-web credential economy pricing tiers across stealer-log subscriptions, per-log retail, AiTM kits, and initial-access broker transactions. Sources: Flare; SOCRadar; Barracuda summary; Rapid7 IAB Report 2025.
Account takeover and credential stuffing telemetry
ATO is the consumer-side load that the wholesale credential economy creates. The numbers below come straight from the platforms catching the requests.
Microsoft and Cloudflare daily volume
Source | Metric | 2024 to 2025 figure |
|---|---|---|
Daily customer attacks tracked | 600 million | |
Microsoft Digital Defense Report | Identity attacks that are password-based | over 99% |
Password attacks blocked per second | 7,000 | |
Identity attacks that are password attacks | more than 97% | |
Microsoft Digital Defense Report 2025 | H1 2025 identity-attack growth | +32% |
Microsoft Digital Defense Report 2025 | MFA-bypass breaches via session-token theft | 80% (per Flare summary) |
Successful logins involving compromised passwords | 41% (Sept-Nov 2024) | |
All authorization requests using leaked credentials | 64% (first week March 2025) | |
Cloudflare Radar, March 2025 | Bot authorization requests using leaked credentials | over 65% |
Cloudflare Radar, March 2025 | Human authorization requests using leaked credentials | over 44% |
Cloudflare blog, March 2025 | Login attempts with leaked passwords from bots | 95% |
Cloudflare blog, March 2025 | WordPress sites: leaked-password login attempt success rate | 76% |
The Microsoft 7,000-per-second figure is from the 2024 MDDR; the 2025 edition emphasized different framing (97% of identity attacks being password attacks, the 80% MFA-bypass via session theft) but did not republish the per-second count. Both are still in circulation as cited by Microsoft.
Verizon SSO and Auth0 / Akamai anchors
Verizon's 2025 DBIR research note measured credential-stuffing share against SSO providers. The median daily percentage of credential stuffing was 19% of all authentication attempts; for some organizations, up to 44% of all authentication attempts on a given day were active credential stuffing.
Auth0's Customer Identity Trends Report 2025 measured 46% of all 2024 registration attempts on the Auth0 platform as signup attacks (bot-driven account-creation abuse, often paired with stolen identity data). For the retail and e-commerce sector, fraudulent sign-ups outnumbered legitimate ones by 120 times during a multi-month attack peak. The historical baseline from Auth0's 2022 State of Secure Identity measured 34% of all auth traffic on the Auth0 network as credential stuffing, totaling nearly 10 billion attempts.
Akamai's State of the Internet credential-stuffing baseline recorded 193 billion credential-stuffing attempts in 2020, providing the historical curve against which the 2024-2025 platform telemetry should be read. Akamai's 2025 SOTI continued tracking app + API attack volume but does not republish a single global credential-stuffing-attempt count.
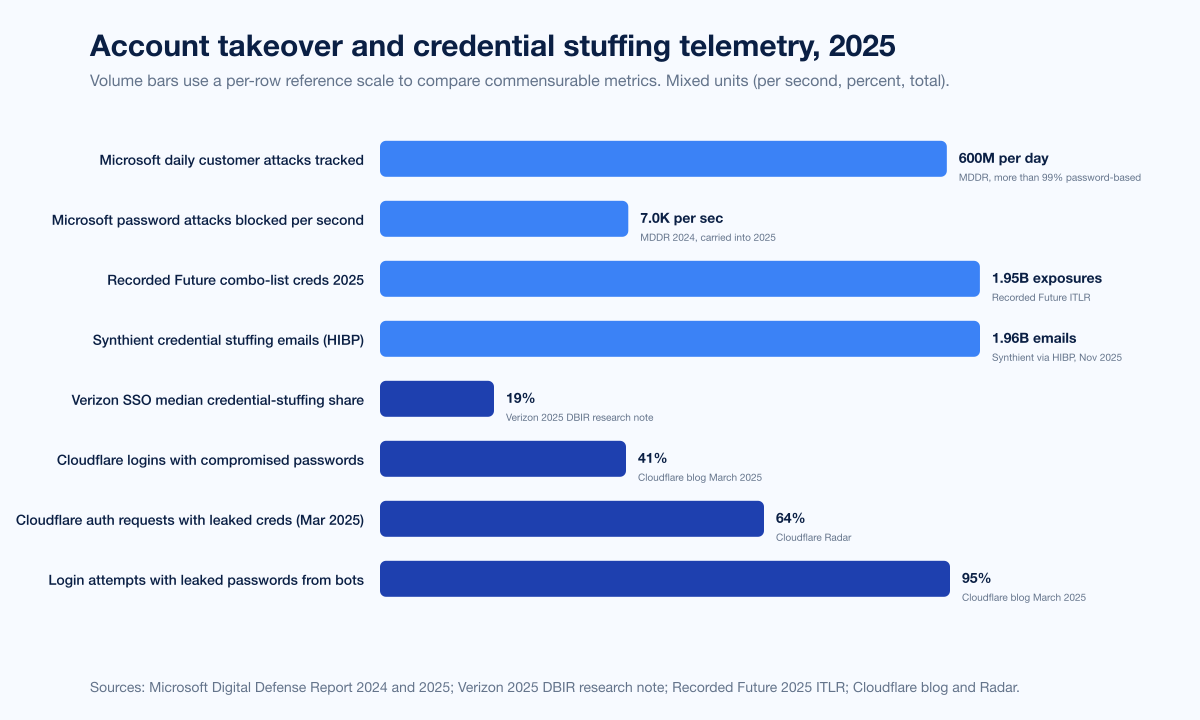
Figure 4: Account takeover and credential stuffing telemetry across Microsoft, Verizon, Auth0, and Cloudflare in 2025. 600M daily Microsoft Entra identity attacks; 7,000 password attacks per second blocked; 19% SSO median credential-stuffing share; 41% Cloudflare successful logins with compromised passwords; 64% all auth requests with leaked credentials; 95% of leaked-password attempts from bots. Sources: Microsoft Digital Defense Report 2025 and 2024; Verizon 2025 DBIR research note; Cloudflare and Cloudflare Radar.
Adversary-in-the-middle kits: the dominant MFA-bypass route in 2025
A working credential without MFA is one breach. A working credential with a stolen post-MFA session cookie is the same breach plus invisibility. AiTM phishing kits industrialized the second model.
Microsoft's 2025 Digital Defense Report attributed 80% of MFA-bypass breaches to session-token theft via adversary-in-the-middle attacks. The named kits powering this share are Tycoon 2FA (Storm-1747 actor cluster), Mamba 2FA, Evilginx, and Sneaky 2FA.
Tycoon 2FA scale and takedown
Microsoft's March 2026 inside-look at Tycoon 2FA described it as one of the most widespread phishing-as-a-service platforms by 2025: at peak, Tycoon-driven campaigns sent tens of millions of phishing messages reaching over 500,000 organizations each month worldwide. By mid-2025, Tycoon 2FA accounted for about 62% of phishing attempts Microsoft blocked, including more than 30 million emails in a single month, per Barracuda's threat spotlight. The Europol-led takedown in March 2026 linked Tycoon 2FA to 64,000+ phishing incidents, seizing tens of thousands of phishing domains.
Tycoon 2FA pricing on Telegram and Signal:
Tier | Price | Source |
|---|---|---|
10-day access | US$120 | |
1-month admin panel | US$350 | Barracuda summary |
That price tag, together with an off-the-shelf hosting tier, is what dropped the technical bar for AiTM operators to "anyone with a credit card and a Telegram account."
Why session-cookie theft matters
Recorded Future found 276 million indexed credentials carried active session cookies in 2025, enabling MFA bypass without re-authentication. The recommended mitigation in the report: treat any infostealer log exposure as a potential authentication bypass, not just a password-reset trigger. Shorten session-token lifetimes for high-risk applications (admin consoles, identity-provider portals, financial dashboards). SpyCloud's 2026 IER recaptured 8.6 billion stolen session cookies and artifacts in 2025 alone. Once a cookie is in the wild, the only durable defense is rotation.
Snowflake 2024 and the AT&T disclosure
The single best documented case study for the credential-economy thesis is the Snowflake cluster of 2024 incidents, where infostealer-stolen credentials (some dating back to 2020) were used to access Snowflake customer instances that lacked MFA configuration.
Mandiant attribution and scope
Mandiant tracked the campaign as UNC5537:
Snowflake / UNC5537 metric | Figure | Source |
|---|---|---|
Customer organizations notified by Mandiant + Snowflake | approximately 165 | |
Accounts UNC5537 used that had prior credential exposure | at least 79.7% | |
Source of credentials | infostealer malware on non-Snowflake-owned systems | Mandiant |
Earliest known exposure date for credentials used | as far back as 2020 | Mandiant |
MFA configuration on impacted accounts | absent | Mandiant |
Named victim disclosures included AT&T, Ticketmaster, Santander, LendingTree, and Advance Auto Parts. The threat actor extorted affected organizations; financial losses and illicit gains exceeded US$2 million by the time arrests were made.
AT&T's July 12, 2024 SEC 8-K disclosure
AT&T's SEC filing on July 12, 2024 was the largest single Snowflake-cluster disclosure:
AT&T disclosure detail | Figure |
|---|---|
Customers affected | nearly 110 million |
Snowflake instance compromise window | 11 days in April 2024 |
Records stolen | calls and texts, May 1 to October 31, 2022, plus a small number through January 2, 2023 |
MFA configuration on impacted account | absent |
Filing type | SEC 8-K |
Filing date | July 12, 2024 |
Connor Moucka arrest | November 2024 (Ontario, Canada) |
John Erin Binns arrest | separately, related to 2021 T-Mobile breach |
The AT&T metadata stolen did not include names, SSNs, or financial data, but did include phone-number-to-phone-number metadata and (for some customers) cell-tower identifiers usable for location inference. The original credential compromise predated the breach by years.
Coinbase May 2025: the insider variant
Coinbase disclosed in a May 14, 2025 SEC 8-K that 69,461 customers had identifying data exposed via a different mechanism: external attackers bribed and recruited overseas contract support agents to exfiltrate Coinbase data from internal support tooling. Coinbase confirmed passwords and private keys were not compromised; data exposed included names, addresses, masked bank account numbers, last four digits of SSNs, government ID images, and account balances. The threat actor demanded US$20 million; Coinbase refused and instead established a US$20 million reward for information leading to arrest. Coinbase's 8-K estimated remediation costs and reimbursements at US$180-400 million.
The Coinbase incident is the variant pattern that augments the broader credential-economy thesis: when external infostealer-fed pipelines are not the path of least resistance, attackers will rent insiders. The ultimate signal is the same: identity is the perimeter.
Cost of compromised-credential breaches
IBM's 2025 Cost of a Data Breach Report, the canonical Ponemon-aligned annual analysis published August 2025, ran through full-year 2024 and early-2025 incidents:
IBM 2025 metric | Figure | Source |
|---|---|---|
Cost of breaches with compromised-credential initial access | US$4.67M per breach | |
Mean time to identify and contain credential breach | 246 days | IBM 2025 |
Cost of phishing-initiated breaches | US$4.8M | IBM 2025 |
Phishing share of all initial vectors (IBM scope) | 16% (now leading by frequency) | IBM 2025 |
Cost of breaches taking >200 days to contain | nearly US$5.5M | IBM 2025 |
Global average breach cost, 2025 | US$4.44M (down from US$4.88M in 2024) | |
US average breach cost, 2025 | US$10.22M (record) | IBM 2025 |
Healthcare average breach cost, 2025 | US$7.42M (down from US$9.77M, still highest by industry) | IBM 2025 |
Mandiant's M-Trends 2025 added the dwell-time picture for 2024 incidents:
M-Trends 2025 metric | Figure |
|---|---|
Stolen credentials as initial vector | 16% (#2 globally, behind exploits at 33%) |
Global median dwell time | 11 days (up from 10 in 2023) |
Median dwell time when externally notified | 26 days |
Median dwell time when notified by adversary (ransomware) | 5 days |
Median dwell time when discovered internally | 10 days |
CrowdStrike's 2025 Global Threat Report measured 79% of initial-access attacks in 2024 as malware-free, relying on stolen credentials, social engineering, and abuse of legitimate remote-access tools. Access broker advertisements rose 50% YoY, identity-based intrusions appeared in 35% of cloud incidents, and vishing surged 442% between H1 and H2 2024.
IBM's X-Force Threat Intelligence Index 2025 tied with public-facing-application exploitation at 30% of initial access in 2024, both as the joint top vector. The 2026 X-Force Threat Index noted 300,000+ ChatGPT credentials exposed via infostealer logs and a 44% surge in public-facing-app-exploitation attacks during 2025.
Government and law-enforcement signal
The FBI IC3 2024 Internet Crime Report, published April 2025, recorded the loss landscape:
FBI IC3 2024 metric | Figure |
|---|---|
Total reported losses | US$16.6 billion (+33% YoY) |
Business Email Compromise losses | US$2.77 billion across 21,442 incidents |
Phishing/spoofing complaints | 193,407 (top reported crime category) |
Cyber-enabled fraud share of all losses | nearly 83%, US$13.7 billion |
The ITRC 2024 Annual Data Breach Report, released January 2025, reported:
ITRC 2024 metric | Figure |
|---|---|
US data compromises tracked | 3,158 (-1% YoY, near-record) |
Victim notices issued | 1,728,519,397 (+312% YoY) |
Mega-breaches (100M+ notices each) | 6 events accounting for over 1.4 billion notices |
Mega-breaches preventable with MFA | 4 of 6 |
Cumulative ITRC database history | 21,900+ tracked compromises, ~12 billion victim notices, ~60 billion records |
The throughline across both: credentials with no MFA, no rotation, and no monitoring against published breach corpora produced multi-billion-dollar loss outcomes that were preventable with controls already on the market.
AI-orchestrated credential harvesting
The 2025-2026 edge of this category is AI agents performing the credential-harvesting and lateral-movement work that humans previously performed step-by-step. Two specific public disclosures.
Anthropic disclosed in November 2025 that its Threat Intelligence team had disrupted what it characterized as the first largely autonomous AI-orchestrated cyber espionage campaign. Designation: GTG-1002, a Chinese state-sponsored actor:
Anthropic disclosure detail | Figure |
|---|---|
Detection date | mid-September 2025 |
Share of campaign performed by AI | 80% to 90% |
Human intervention points per campaign | 4 to 6 critical decisions |
Peak request rate | thousands of requests, often multiple per second |
Specific credential-related actions | "extract user credentials, system configurations, and sensitive information" then produce comprehensive documentation of stolen credentials |
Anthropic's August 2025 misuse report described a separate disruption: a sophisticated cybercriminal used Claude Code to commit large-scale theft and extortion across at least 17 distinct organizations including healthcare, emergency services, and government, with ransoms exceeding US$500,000.
The signal is not that AI is doing something fundamentally new; the signal is that AI is industrializing credential extraction at peak rates that would be physically impossible for human operators. IBM's X-Force 2026 Threat Index attached a number to one piece of the AI dimension: 300,000+ ChatGPT credentials surfaced in infostealer dark-web listings during 2025, giving attackers direct on-ramps into employee AI assistant memories.
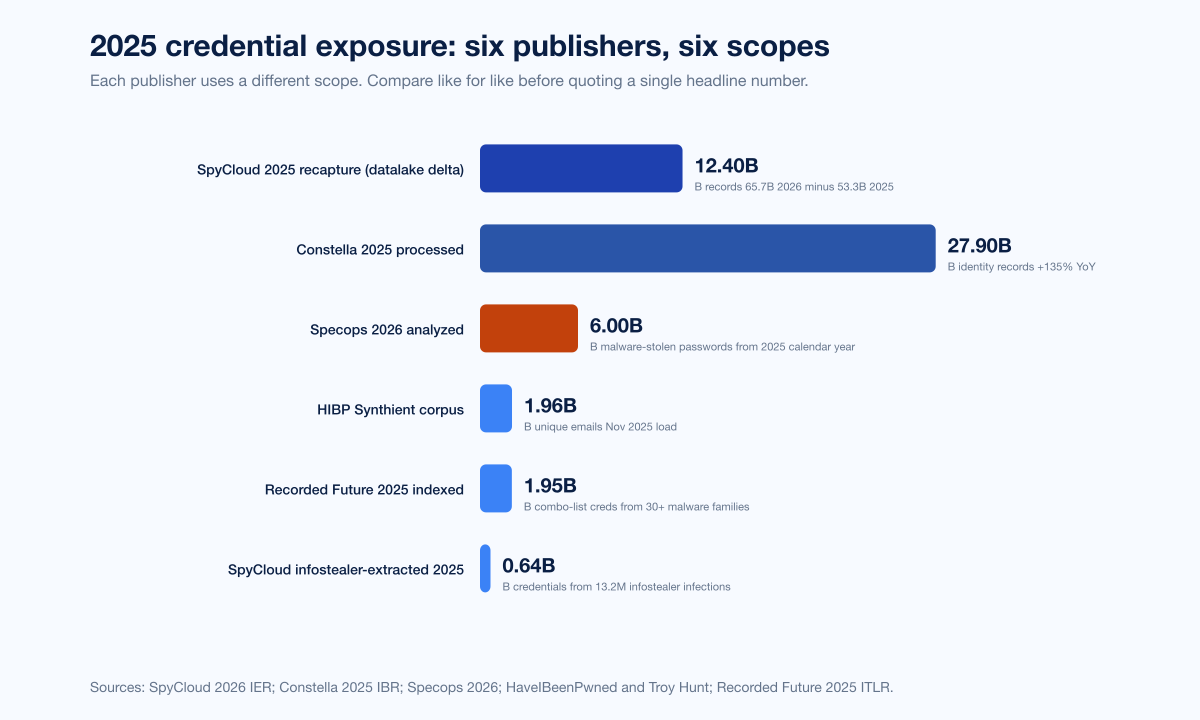
Figure 5: Per-publisher reconciliation of 2025 credential-exposure totals across HaveIBeenPwned (Synthient corpora), Recorded Future (combo-list credentials), SpyCloud (infostealer-extracted), Specops (malware-stolen passwords analyzed), and Constella (identity records processed). Each publisher uses a different scope; compare like for like. Sources: Troy Hunt; Recorded Future; SpyCloud 2026 IER; Specops 2026; Constella.
Recovery, rotation, and detection
The 246-day mean time to identify and contain a credential breach in IBM's 2025 dataset is the central recovery number. The dwell-time-by-discovery-channel breakdown in Mandiant's M-Trends 2025 shows external notification (26 days) is markedly worse than internal discovery (10 days). The fastest detection channel, paradoxically, is when an adversary itself notifies the victim (5 days, mostly via ransomware notes).
Constella's 48-hour analysis measured the window between an infostealer infection on a victim machine and the resulting log appearing for sale on dark-web markets at 48 hours or less. Detection mechanisms must operate inside that window to be useful.
What good looks like in 2026 detection terms:
Continuous monitoring of breached-password and stealer-log corpora against the org's email-domain footprint via Specops, SpyCloud, Recorded Future, Constella, Flare, or similar identity-data-broker integrations. Each measures a different slice; layered coverage closes blind spots.
Session-token rotation policies triggered on infostealer-log exposure, not just password-reset workflows.
Phishing-resistant MFA (FIDO2 / passkeys / hardware keys) on at minimum admin, finance, identity-provider, and CI/CD console accounts. Microsoft's MDDR data shows phishing-resistant MFA stops more than 99% of identity attacks.
Dark-web monitoring for the org's specific corporate email-domain patterns, with alert-to-action SLAs measured in hours, not weeks.
Quarterly credential-stuffing red-team simulation through the actual customer-facing login flow (not just internal SSO) using leaked-password lists curated from HIBP and Specops, to discover production blind spots before attackers do.
What this means for defenders
Inventory your authentication surface. Every consumer-facing login flow, every SSO provider connection, every legacy basic-auth endpoint that still answers requests, every API key, every OAuth refresh token. The 2025 credential economy proved that any of those surfaces can become the breach if attackers find a stale credential and an absent MFA enforcement. SpyCloud's 2026 NHI category (18.1M API keys, 6.2M AI-tool credentials in 2025) is the new target surface; the inventory should reflect it.
Treat infostealer log exposure as authentication bypass, not just a password-reset trigger. If a session cookie was lifted, rotating the password does not invalidate the cookie. Force a session reset and rotate any application secrets that the compromised browser had access to.
Phishing-resistant MFA on the highest-risk accounts is non-negotiable. Admin consoles, identity-provider portals, finance approval flows, CI/CD pipelines, AI-assistant accounts. The 80% MFA-bypass figure in MDDR 2025 specifically describes session-cookie theft, which phishing-resistant MFA blocks at the cryptographic layer.
Run continuous external-credential monitoring against your corporate email-domain footprint. Specops, SpyCloud, Recorded Future, Constella, and HIBP each pull from a different sourcing pipeline. Treat them as overlapping radars with imperfect overlap. The gap between an exposed credential and an attacker using it can be measured in hours.
Penetration-test the human path. Stingrai's offensive testing teams routinely lift session cookies via AiTM frameworks against client production environments under engagement, including in PTaaS and adversary simulation programs. The 80% figure in MDDR 2025 is not academic; it reflects the techniques used inside engagements every quarter. The defenses that hold up are the ones that survive the same tools an adversary uses.
Invest in detection-and-response on the exposed-credential side, not only the post-breach side. IBM's 2025 dataset showed organizations using AI and automation extensively reduced breach lifecycle by 108 days versus organizations without. The investment that compounds is the one that closes the detection-to-rotation window.
Forward outlook
What primary publishers explicitly project for 2026:
SpyCloud's 2026 IER flagged non-human-identity exposure (API keys, AI tool credentials) as the fastest-growing 2025 category and projects further growth in 2026 as organizations expand AI-platform deployments without rotating long-lived service-account credentials at the cadence required.
Recorded Future's 2025 ITLR noted that volume curves accelerated through 2025 (Q4 +90% over Q1) and warned that family-level disruption (Lumma May 2025, Rhadamanthys later 2025) creates short-lived vacuums quickly filled by competing families.
Microsoft's MDDR 2025 signaled that MFA-bypass via session theft will dominate identity-attack signal in 2026 as adversaries shift from credential-only attacks to credential + cookie pairs, and called out increasing PhaaS commodification.
IBM's X-Force 2026 Index projected continued credential-theft growth centered on AI-platform credentials and authentication tokens, with infostealer logs feeding directly into AI-assistant compromise scenarios.
Anthropic's November 2025 disclosure anchored 2026 expectations around AI-orchestrated credential harvesting at request rates impossible for human operators, with limited human-in-the-loop intervention required per campaign.
What primary publishers have NOT released as of April 25, 2026: full-year 2026 victim-notice or breach-cost numbers; full-year 2026 stealer-log volume; full-year 2026 IAB market sizing. This post will be updated when those primary sources publish.
Frequently Asked Questions
How many compromised credentials were exposed in 2025?
The honest answer is that the total depends on which publisher's scope you accept, because each runs a different sourcing pipeline. HaveIBeenPwned added 1.96 billion unique emails and 1.3 billion unique passwords on November 5, 2025 from the Synthient Credential Stuffing corpus alone. Recorded Future indexed 1.95 billion malware combo-list credential exposures across 2025. SpyCloud recaptured 5.3 billion credential pairs and 8.6 billion stolen session cookies in 2025. Specops analyzed more than 6 billion malware-stolen passwords. The reconciled headline most CISOs use: low billions of unique-email exposures, with multi-billion credential pairs once duplicates and reused passwords are counted in. For per-password composition, see Stingrai's Password Statistics 2026 post.
What is the share of breaches that start with stolen credentials in 2026?
Verizon's 2025 DBIR measured compromised credentials as the initial access vector in 22% of 12,195 confirmed breaches, leading vector for the second consecutive year. IBM's X-Force 2025 Threat Intelligence Index measured valid account credentials at 30% of initial-access incidents, tied with public-facing application exploitation. Mandiant's M-Trends 2025 measured stolen credentials at 16%, second behind exploit at 33%. The three publishers use different scopes (DBIR is breach-confirmed, IBM X-Force is incident response, Mandiant is engagement-led); use the relevant publisher for the scope you care about.
What is the cost of a compromised-credential breach?
IBM's 2025 Cost of a Data Breach Report priced compromised-credential breaches at US$4.67M per incident with a 246-day mean time to identify and contain. The global average breach cost in 2025 was US$4.44M (down from US$4.88M in 2024). The US average breach cost reached a record US$10.22M. Long-tail breaches (>200 days dwell) averaged nearly US$5.5M.
How many session cookies are stolen and circulating?
SpyCloud's 2026 Identity Exposure Report recaptured 8.6 billion stolen session cookies and authentication artifacts in 2025 alone. SpyCloud's 2025 IER had cited 17.3 billion stolen session cookies in the cumulative dataset. Recorded Future found 276 million indexed credentials carried active session cookies in 2025. Once a session cookie is in the wild, MFA does not block its replay; rotation of the underlying session is the only durable defense.
What is the most common infostealer family in 2025?
Specops's 2026 Breached Password Report found LummaC2 accounting for nearly 60% of credentials attributable to infostealers in its 6-billion-password dataset. Recorded Future's 2025 ITLR ranked LummaC2 as the most widely deployed infostealer of 2025, followed by Rhadamanthys, Vidar, and StealC. Microsoft's coordinated takedown of Lumma in May 2025 displaced volume to those successors. IBM X-Force 2025 ranked Lumma first by dark-web ad volume, ahead of RisePro, Vidar, Stealc, and RedLine.
How much does a stealer log cost on the dark web?
Flare and SOCRadar tracked 2025 pricing: infostealer subscriptions for Lumma, RedLine, Vidar, Raccoon, and StealC at US$100 to US$200 per month; StealC at US$200/month or US$800 for six months; individual stealer logs at US$5 to US$50 each, averaging around US$10 per bot in dark-web shops. Premium tiers for fresh logs (under 48 hours old) command multiples of those prices because session tokens have not yet expired.
What is an adversary-in-the-middle (AiTM) attack and how common is it?
An AiTM attack uses a reverse-proxy phishing kit to intercept credentials and post-MFA session cookies in real time, allowing attackers to bypass MFA by replaying the session. Microsoft's 2025 Digital Defense Report attributed 80% of MFA-bypass breaches to AiTM session-token theft. Tycoon 2FA, Mamba 2FA, Evilginx, and Sneaky 2FA are the most-used kits; Tycoon 2FA alone accounted for about 62% of phishing attempts Microsoft blocked by mid-2025, before the Europol-led takedown in March 2026 linked it to 64,000+ phishing incidents.
What was the Snowflake 2024 breach and how many customers were affected?
Mandiant tracked the 2024 Snowflake-cluster breach as UNC5537. Approximately 165 customer organizations were notified. The threat actor used credentials previously stolen via infostealer malware on non-Snowflake systems; 79.7% of the accounts UNC5537 used had prior credential exposure, some from infostealer infections dating back to 2020, on accounts without MFA configured. Named victim disclosures included AT&T (110 million customers, SEC 8-K July 12, 2024), Ticketmaster, Santander, LendingTree, and Advance Auto Parts.
How long does it take to detect a credential breach?
IBM's 2025 Cost of a Data Breach Report measured the mean time to identify and contain credential-initiated breaches at 246 days. Mandiant's M-Trends 2025 measured global median dwell time at 11 days for 2024 incidents, with 26 days when externally notified, 10 days when discovered internally, and 5 days when adversaries themselves notified the victim (typically via ransomware). Constella measured the window between infostealer infection and dark-web sale of the resulting log at 48 hours or less.
Are passkeys safe from credential theft?
Passkeys (FIDO2 hardware-bound credentials) are not exfiltratable from a victim machine the way browser-saved passwords are, because the private key never leaves the authenticator. This is the architectural reason Microsoft's MDDR data shows phishing-resistant MFA stops more than 99% of identity attacks. Session cookies issued after a passkey login can still be stolen via AiTM proxy phishing, which is why short session lifetimes plus device binding remain important. For passkey adoption metrics across FIDO Alliance, Apple, Google, and Microsoft, see Stingrai's Password Statistics 2026 post.
Where can I get the latest compromised-credential statistics?
The primary publishers tracked in this post: Verizon DBIR (annual, May), HaveIBeenPwned + Troy Hunt's blog (ongoing breach loads), SpyCloud Annual Identity Exposure Report (March), Recorded Future Identity Threat Landscape Report (March), Microsoft Digital Defense Report (October) plus Microsoft Security Blog disclosures, IBM Cost of a Data Breach (August) and IBM X-Force Threat Intelligence Index (February to April), Mandiant M-Trends (April), CrowdStrike Global Threat Report (February), Specops Breached Password Report (January), Constella Identity Breach Report (April), FBI IC3 Internet Crime Report (April), ITRC Annual Data Breach Report (January). Stingrai's research team will refresh this post when full-year 2026 reports release.
References
Verizon. 2025 Data Breach Investigations Report. May 2025. https://www.verizon.com/business/resources/T16f/reports/2025-dbir-data-breach-investigations-report.pdf. Analyzed 22,052 incidents and 12,195 confirmed breaches; canonical breach root-cause analysis for the year.
Verizon. Additional 2025 DBIR research on credential stuffing. 2025. https://www.verizon.com/business/resources/articles/credential-stuffing-attacks-2025-dbir-research/. Per-SSO median credential-stuffing share, peak organizational share, and password-distinctness in infostealer corpora.
Troy Hunt. Inside the Synthient Threat Data. October 21, 2025. https://www.troyhunt.com/inside-the-synthient-threat-data/. Synthient Stealer Log corpus loaded into HaveIBeenPwned: 23 billion records, 183 million unique emails, 16.4 million entirely new.
Troy Hunt. 2 Billion Email Addresses Were Exposed, and We Indexed Them All in Have I Been Pwned. November 5, 2025. https://www.troyhunt.com/2-billion-email-addresses-were-exposed-and-we-indexed-them-all-in-have-i-been-pwned/. Synthient Credential Stuffing Threat Data: 1,957,476,021 unique emails, 1.3 billion unique passwords, 625 million previously unseen.
SpyCloud. 2025 Annual Identity Exposure Report. March 2025. https://spycloud.com/blog/2025-annual-identity-exposure-report/. 53.3 billion recaptured identity records, +22% YoY; 17.3 billion cumulative session cookies; per-identity exposure averages.
SpyCloud. 2026 Annual Identity Exposure Report. March 2026. https://spycloud.com/blog/2026-annual-identity-exposure-report/. 65.7 billion recaptured identity records, +23% YoY; 8.6 billion stolen session cookies and 642.4 million credentials from 13.2 million infostealer infections in 2025.
Recorded Future. 2025 Identity Threat Landscape Report. March 2026. https://www.recordedfuture.com/blog/identity-trend-report-march-blog. 1.95 billion malware combo-list credential exposures indexed in 2025; 276 million with active session cookies; family timeline.
Microsoft. Microsoft Digital Defense Report 2025. October 2025. https://blogs.microsoft.com/on-the-issues/2025/10/16/mddr-2025/. 97% of identity attacks are password attacks; 80% of MFA-bypass breaches via session-token theft.
Microsoft Security Blog. Lumma Stealer: Breaking down the delivery techniques and capabilities of a prolific infostealer. May 21, 2025. https://www.microsoft.com/en-us/security/blog/2025/05/21/lumma-stealer-breaking-down-the-delivery-techniques-and-capabilities-of-a-prolific-infostealer/. 394,000 infected Windows devices identified March 16 to May 16, 2025.
Microsoft Security Blog. Inside Tycoon2FA: How a leading AiTM phishing kit operated at scale. March 4, 2026. https://www.microsoft.com/en-us/security/blog/2026/03/04/inside-tycoon2fa-how-a-leading-aitm-phishing-kit-operated-at-scale/. Tycoon 2FA reached over 500,000 organizations per month at peak.
IBM. Cost of a Data Breach Report 2025. August 2025. https://www.ibm.com/reports/data-breach. Compromised-credential breach cost US$4.67M, 246-day mean time to identify and contain; US average US$10.22M record.
IBM. X-Force Threat Intelligence Index 2025. April 2025. https://www.ibm.com/thought-leadership/institute-business-value/report/2025-threat-intelligence-index. Valid accounts and public-facing app exploit each 30% of initial access; infostealer ad volume +12% YoY.
IBM. X-Force Threat Intelligence Index 2026. February 2026. https://www.ibm.com/think/x-force/threat-intelligence-index-2026-securing-identities-ai-detection-risk-management. 300,000+ ChatGPT credentials in stealer logs; +44% surge in public-facing app exploitation.
Mandiant / Google Cloud. M-Trends 2025. April 2025. https://cloud.google.com/blog/topics/threat-intelligence/m-trends-2025. Stolen credentials = 16% of initial vectors (#2); global median dwell time 11 days.
Mandiant / Google Cloud. UNC5537 Targets Snowflake Customer Instances for Data Theft and Extortion. June 10, 2024. https://cloud.google.com/blog/topics/threat-intelligence/unc5537-snowflake-data-theft-extortion. 165 customer organizations notified; 79.7% of accounts had prior infostealer credential exposure.
CrowdStrike. 2025 Global Threat Report. February 2025. https://www.crowdstrike.com/en-us/blog/crowdstrike-2025-global-threat-report-findings/. 79% of initial-access attacks malware-free; access broker advertisements +50% YoY.
Specops Software (Outpost24). 2026 Breached Password Report. January 2026. https://specopssoft.com/blog/new-research-6-billion-compromised-passwords-2026/. 6+ billion malware-stolen passwords analyzed; LummaC2 nearly 60% of credentials attributable to infostealers.
Constella Intelligence. 2025 Identity Breach Report. April 2025. https://constella.ai/2025-identity-breach-report-what-107-billion-exposed-records-reveal-about-cyber-risk/. 219,000 breach events and 107 billion exposed records analyzed.
Cloudflare. Password reuse is rampant: nearly half of observed user logins are compromised. March 2025. https://blog.cloudflare.com/password-reuse-rampant-half-user-logins-compromised/. 41% of successful logins involve compromised passwords; 95% of leaked-password attempts from bots.
Cloudflare. Extending Cloudflare Radar's security insights with new DDoS, leaked credentials, and bots datasets. March 2025. https://blog.cloudflare.com/cloudflare-radar-ddos-leaked-credentials-bots/. 64% of all auth requests, 65% of bot, 44% of human use leaked credentials in March 2025.
Auth0 / Okta. Customer Identity Trends Report 2025. March 2025. https://www.okta.com/newsroom/articles/customer-identity-trends-report-2025--securing-customer-trust-in/. 46% of 2024 registration attempts on Auth0 were signup attacks.
Akamai. State of the Internet historical credential stuffing baseline. 2020. https://www.akamai.com/newsroom/press-release/state-of-the-internet-security-retail-attacks-and-api-traffic. 193 billion credential-stuffing attempts globally; historical curve anchor.
Cofense. 2025 Annual State of Email Security Report. 2025. https://cofense.com/Blog/Cofense-Report-Reveals-AI-Powered-Phishing-Accelerated-to-One-Attack-Every-19-Seconds. 1 malicious email every 19 seconds; 18% of malicious email is conversational AI lure.
Rapid7. Initial Access Brokers have Shifted to High-Value Targets and Premium Pricing. December 2025. https://www.rapid7.com/blog/post/tr-initial-access-broker-shift-high-value-targets-premium-pricing/. Average IAB transaction US$1,328; range US$500 to US$50,000.
Anthropic. Disrupting the first reported AI-orchestrated cyber espionage campaign. November 2025. https://www.anthropic.com/news/disrupting-AI-espionage. 80-90% of campaign performed by AI; Claude exfiltrated user credentials autonomously.
Anthropic. Detecting and countering misuse of AI: August 2025. August 2025. https://www.anthropic.com/news/detecting-countering-misuse-aug-2025. Cybercriminal targeted at least 17 distinct organizations using Claude Code.
FBI Internet Crime Complaint Center. 2024 Internet Crime Report. April 2025. https://www.ic3.gov/AnnualReport/Reports/2024_IC3Report.pdf. US$16.6 billion total losses; US$2.77 billion BEC; 193,407 phishing complaints.
Identity Theft Resource Center. 2024 Annual Data Breach Report. January 2025. https://www.idtheftcenter.org/post/2024-annual-data-breach-report-near-record-compromises/. 1.728 billion victim notices; 6 mega-breaches accounted for 1.4 billion of those.
Cybersecurity Dive. Massive Snowflake-linked attack exposes data on nearly 110M AT&T customers. July 12, 2024. https://www.cybersecuritydive.com/news/att-cyberattack-snowflake-environment/721235/. AT&T SEC 8-K disclosure scope and root-cause analysis.
Coinbase. Protecting Our Customers, Standing Up to Extortionists. May 14, 2025. https://www.coinbase.com/blog/protecting-our-customers-standing-up-to-extortionists. Insider-bribery breach affecting 69,461 customers; US$180-400M remediation estimate.
Flare. Stealer Logs: Guide for Security Teams. Ongoing. https://flare.io/glossary/stealer-logs. Stealer log retail and subscription pricing reference.
SOCRadar. Top 10 Stealer Logs. 2025. https://socradar.io/blog/top-10-stealer-logs/. Per-family pricing tables; StealC subscription pricing.
The Hacker News. Snowflake Breach Exposes 165 Customers' Data in Ongoing Extortion Campaign. June 2024. https://thehackernews.com/2024/06/snowflake-breach-exposes-165-customers.html. Independent confirmation of Mandiant 165-customer notification figure.
The Hacker News. Europol-Led Operation Takes Down Tycoon 2FA Phishing-as-a-Service Linked to 64,000 Attacks. March 2026. https://thehackernews.com/2026/03/europol-led-operation-takes-down-tycoon.html. Tycoon 2FA takedown scope.
Barracuda Networks. Threat Spotlight: Tycoon 2FA didn't die, it's scattered everywhere. April 16, 2026. https://blog.barracuda.com/2026/04/16/threat-spotlight-tycoon-2fa-scattered-everywhere. Tycoon 2FA Telegram pricing and post-takedown distribution analysis.
Help Net Security. Average global data breach cost now $4.44 million. August 4, 2025. https://www.helpnetsecurity.com/2025/08/04/ibm-cost-data-breach-report-2025/. Independent reporting on IBM 2025 global average.
Enzoic. IBM's Cost of a Data Breach Report 2025. August 2025. https://www.enzoic.com/blog/ibm-cost-of-a-data-breach-report-2025/. IBM 2025 phishing/credential vector breakdown summary.
Tripwire. Key Takeaways from the IBM X-Force 2025 Threat Intelligence Index. April 2025. https://www.tripwire.com/state-of-security/key-takeaways-ibm-x-force-threat-intelligence-index. IBM X-Force 2025 infostealer ad-volume rankings.
Flare. Attack on Identity: Dissecting the 2025 Microsoft Digital Defense Report. October 2025. https://flare.io/learn/resources/blog/2025-microsoft-digital-defense-report/. MDDR 2025 80% MFA-bypass figure and PhaaS pricing summary.
Constella Intelligence. 48 Hours: The Window Between Infostealer Infection and Dark Web Sale. April 2026. https://constella.ai/blog/48-hours-the-window-between-infostealer-infection-and-dark-web-sale/. 48-hour exposure-to-sale window finding.
For organizations evaluating their detection-to-rotation gap on stolen credentials, Stingrai's PTaaS and adversary simulation practices include AiTM credential and session-cookie testing against production identity flows under engagement, simulating the techniques recorded in the primary-source telemetry above. The Stingrai team carries OSCE3, OSCP, OSWE, OSED, OSEP, CREST CRT, and CISSP certifications, has 18 published CVEs in the wild, and presents research at DEFCON and BSIDES. For password-composition and authentication-strategy data complementary to this post, see Password Statistics 2026.