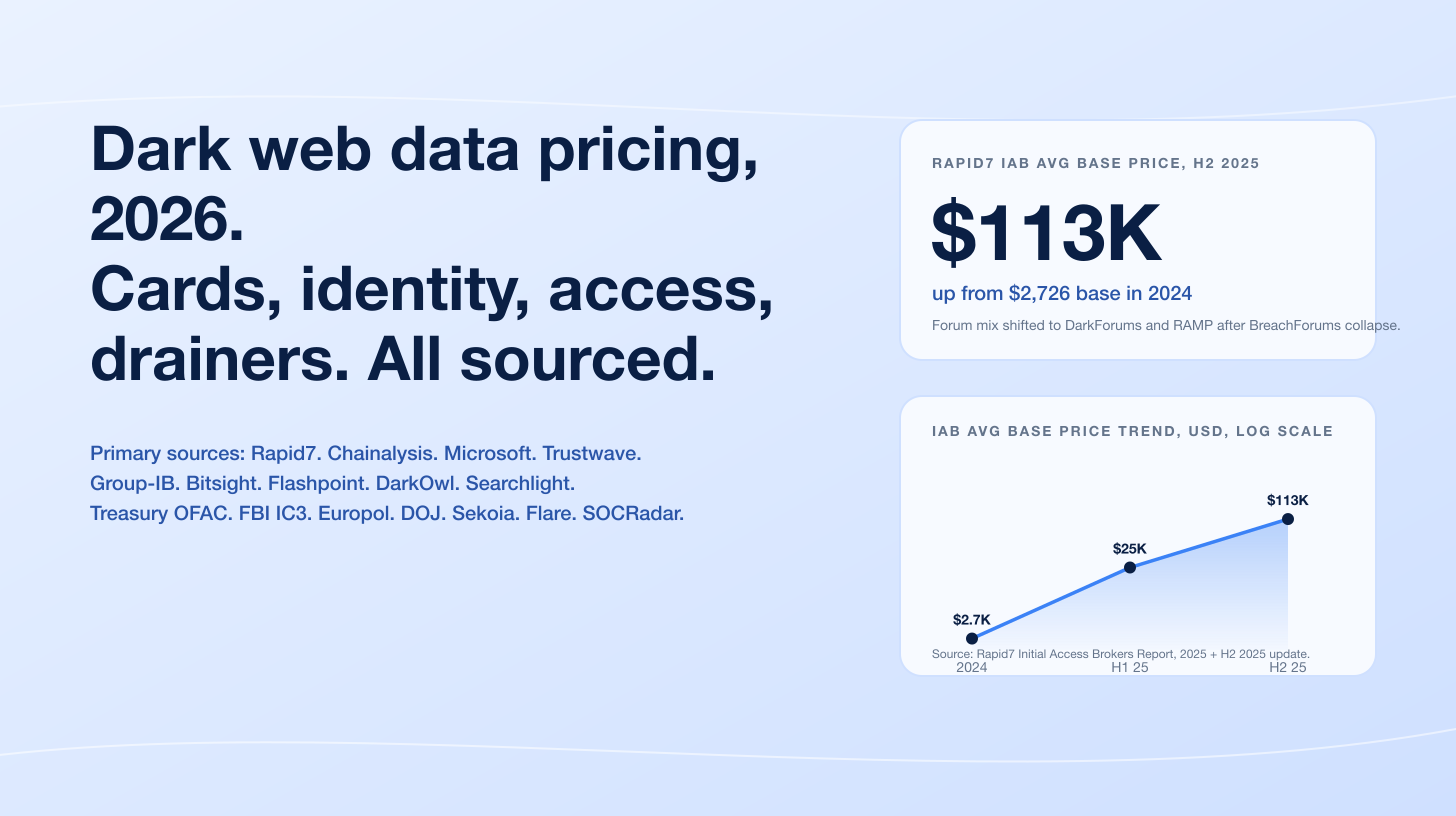
The FBI Internet Crime Complaint Center logged US$25,983,946 in SIM swap losses across 982 complaints in 2024, down from US$48.8M in 2023 and US$72.7M in 2022 (FBI IC3 2024 Internet Crime Report). The November 2022 FTX SIM swap, in which co-conspirators transferred over US$400M in cryptocurrency from FTX hot wallets after a single AT&T retail-store SIM swap, remains the largest publicly attributed loss on record. Princeton CITP's empirical study (Lee, Kaiser, Mayer, and Narayanan, 2020) showed all five major US prepaid carriers used insecure authentication that an attacker could subvert, with 39 of 50 attempted SIM swaps succeeding. The headline volume is shrinking; the per-incident leverage is not.
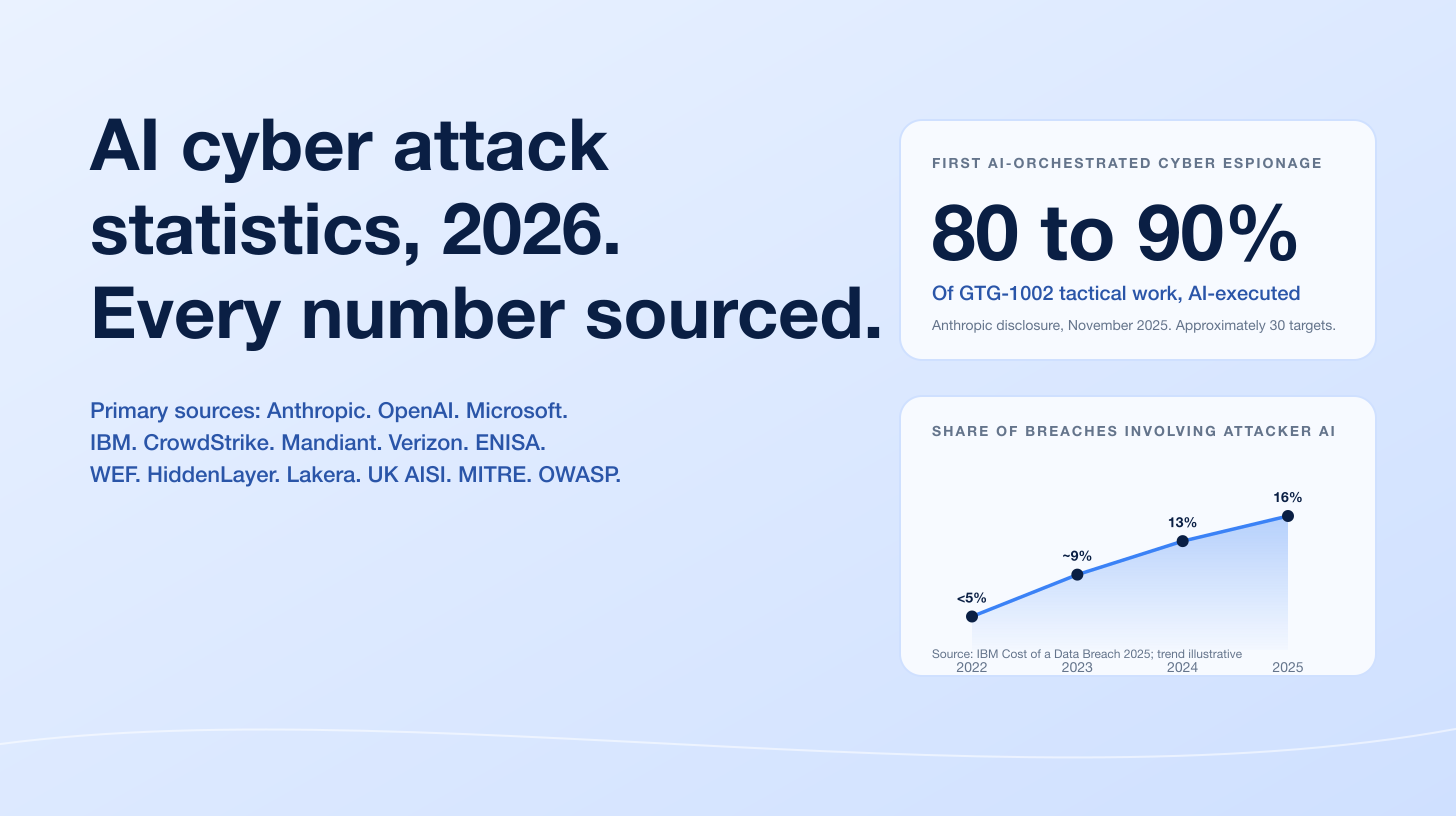
Three forces drive the 2026 numbers. The FCC's final SIM swap rule (FCC 23-95A) was adopted November 15, 2023 and required carrier alerting and authentication overhauls that took effect through summer 2024 (FCC). NIST SP 800-63B Rev 4 (2025) formally reclassifies SMS and PSTN one-time passcodes as a restricted authenticator, the first time NIST has created that designation (NIST SP 800-63B-4). And Scattered Spider / UNC3944 has converted SIM swap from a consumer-cryptocurrency vector into an enterprise initial-access technique that took down MGM Resorts and Caesars in 2023 and yielded a five-defendant DOJ indictment in November 2024 (CISA AA23-320A v2, July 29, 2025). For CISOs, fraud teams, telecoms, and journalists covering identity attacks in 2026, this is the canonical reference page.
This post is the Stingrai research team's canonical 2026 reference for SIM swap activity. It assembles 72 numeric claims from 18 named primary publishers including the FBI Internet Crime Complaint Center, the Federal Communications Commission, NIST, CISA, the US Department of Justice, MITRE ATT&CK, Princeton CITP (Lee et al., 2020), Mandiant, Microsoft Threat Intelligence, CrowdStrike, Sumsub, Javelin Strategy & Research, Chainalysis, Cifas, the UK Action Fraud aggregator, Krebs on Security (for court-record corroboration only), and named SEC 8-K disclosures from Caesars Entertainment and MGM Resorts. Lead data is full-year 2024 telemetry where a primary publisher has released it, with Q1-Q3 2025 partial-year figures where useful; primary publishers have not yet released full-year 2026 reports as of April 2026. Every figure carries its source, year, and methodology window so any claim can be audited inline.
TL;DR: 11 labeled key stats
FBI IC3 SIM swap losses, 2024: US$25,983,946 across 982 complaints (FBI IC3 2024 Internet Crime Report).
FBI IC3 SIM swap losses, peak year (2022): US$72,652,571 across 2,026 complaints (FBI IC3 2022 Internet Crime Report).
Largest publicly attributed SIM swap loss: US$400M+ (FTX, November 11, 2022; DOJ DC indictment unsealed January 2024) (CNBC, Feb 2 2024).
Princeton CITP carrier study (2020): 39 of 50 attempted SIM swaps succeeded across 5 major US prepaid carriers, 17 of more than 140 surveyed websites vulnerable to SIM-swap-only account takeover (issms2fasecure.com).
CrowdStrike vishing surge, H1 to H2 2024: +442%, attributed to help desk impersonation tradecraft pioneered by Scattered Spider (CrowdStrike 2025 Global Threat Report).
MGM Resorts Scattered Spider attack, Sept 11 2023: approximately 10 days of system downtime, ~US$100M financial impact (MGM Resorts SEC 8-K, Oct 5 2023).
Caesars Entertainment Scattered Spider ransom, Aug to Sept 2023: US$15M paid out of US$30M demand (Caesars Entertainment SEC 8-K, Sept 7 2023).
November 20, 2024 DOJ indictment: 5 alleged Scattered Spider members charged in the Central District of California (DOJ press release).
Tyler Buchanan victim funds controlled (admitted, April 2026): US$26M+, with US$8M+ admitted stolen from individual victims (Krebs on Security, Apr 2026).
UK Cifas SIM swap surge, 2024: +1,055% YoY to 2,961 cases at the National Fraud Database (Cifas, March 2025).
NIST SP 800-63B Rev 4 (2025): SMS and PSTN one-time passcodes are now formally a restricted authenticator, the first time NIST has created that category (NIST SP 800-63B-4).
Key takeaways
The headline stat trend is downward, but the cause is unsettled. FBI IC3 reported losses fell from US$72.7M (2022) to US$48.8M (2023) to US$26.0M (2024). The FCC SIM swap rule, carrier-side alerting investments, the rollout of port-out PINs, and Operation Endgame-style enforcement all coincide with the decline. So does a likely shift in how victims report, since SIM swap is now usually a means to a downstream loss (account takeover, brokerage drain, crypto theft) that gets reported under a different category. Treat the trend as real but not yet causally clean.
One SIM swap is the most expensive minute on the internet. US$400M moved out of FTX hot wallets in less than a day after one carrier-side SIM swap (DOJ DC indictment, January 2024). The headline IC3 average loss per complaint, US$26,460 in 2024, masks a fat-tailed distribution where named cryptocurrency cases run into eight and nine figures.
Scattered Spider weaponized SIM swap into an enterprise vector. The MGM and Caesars 2023 attacks turned what was a consumer cryptocurrency story into a board-level hospitality-and-gaming story. CrowdStrike, Microsoft, CISA, and the DOJ all now describe Scattered Spider's tradecraft as help-desk vishing plus SIM swap plus MFA bypass. The November 2024 indictment is the first time five alleged members have faced federal charges concurrently.
SMS 2FA is officially restricted. NIST SP 800-63B Rev 4 (2025) put SMS and PSTN OTP into a new "restricted authenticator" category. Verifiers SHOULD consider device swap, SIM change, and number porting as risk indicators before delivering an out-of-band code over the PSTN. Practically: if a high-value account still relies on SMS in 2026, the post-mortem is already written.
Carriers know this is a process problem, not a technology problem. The Princeton CITP study showed 39 of 50 attempted SIM swaps succeeded against the five biggest US prepaid carriers, and the failures were almost always at the help desk: agents accepting biographical info, recent payment numbers, or call detail records as authentication. The FCC final rule explicitly bars those as standalone authentication methods. Carriers are now alerting on SIM changes and requiring out-of-band reauthentication, but the human help desk remains the bypass.
Methodology
Sources used in this post: FBI Internet Crime Complaint Center (FBI IC3) annual Internet Crime Reports for 2018, 2021, 2022, 2023, and 2024, plus FBI IC3 PSA I-020822-PSA (February 8, 2022); Federal Communications Commission Report and Order FCC 23-95A (adopted November 15, 2023; published in the Federal Register December 8, 2023) and the FCC consumer affairs notice on the July 2024 compliance waiver; National Institute of Standards and Technology Special Publication 800-63B Revision 4 (final, 2025); Cybersecurity and Infrastructure Security Agency advisory AA23-320A v1 (November 16, 2023) and v2 (July 29, 2025) authored jointly with the FBI, ASD, RCMP, and AFP; US Department of Justice press releases and superseding indictments unsealed in November 2024 (Central District of California) and January 2024 (District of Columbia); MITRE ATT&CK technique T1451 (SIM Card Swap, Mobile) and Group G1015 (Scattered Spider) profile, including campaign C0027 (June to December 2022); the Princeton Center for Information Technology Policy paper "An Empirical Study of Wireless Carrier Authentication for SIM Swaps" by Kevin Lee, Ben Kaiser, Jonathan Mayer, and Arvind Narayanan, presented at SOUPS 2020 (January 2020 corpus); Mandiant / Google Threat Intelligence published profiles of UNC3944; Microsoft Threat Intelligence's Octo Tempest blog (October 25, 2023) and follow-up coverage of Storm-0875; CrowdStrike 2025 Global Threat Report (February 2025) including the H1-versus-H2 2024 vishing comparison; Sumsub Identity Fraud Report 2025-2026 (released October 2025); Javelin Strategy & Research 2025 Identity Fraud Study "Breaking Barriers to Innovation" (March 2025) and the 2026 follow-up "The Illusion of Progress" (April 2026); Chainalysis crypto-crime publications and the Chainalysis SIM swap blog; Cifas press release on the UK National Fraud Database SIM swap surge (March 2025); UK Action Fraud aggregator data through November 2024; SEC 8-K filings from MGM Resorts International (Form 8-K, October 5 2023) and Caesars Entertainment Inc. (Form 8-K, September 7 2023); and Krebs on Security court-record corroboration for the Buchanan, Urban, Truglia, and Council Jr. cases. Date cutoff: April 25, 2026. Statistics that could not be reached via a named primary source on at least one verification pass were dropped rather than estimated.
The FBI IC3 trend line
The FBI Internet Crime Complaint Center has reported SIM swap as a separate crime category since 2018. The longitudinal series is the cleanest publicly available US dataset and the one most often cited in regulatory filings.
Year | Complaints | Losses (US$) | Average per complaint | Source |
|---|---|---|---|---|
2018-2020 (cumulative) | 320 | ~12,000,000 | ~US$37,500 | |
2021 | 1,611 | 68,000,000+ | ~US$42,210 | FBI IC3 PSA I-020822-PSA |
2022 | 2,026 | 72,652,571 | ~US$35,860 | |
2023 | 1,075 | 48,798,103 | ~US$45,393 | |
2024 | 982 | 25,983,946 | ~US$26,460 |
Three points worth noting before reading too much into the decline. First, IC3 captures only victim-initiated complaints to the FBI; financial institutions, carriers, and crypto exchanges are not required to file. Second, SIM swap is increasingly the front half of a multi-stage attack, and victims often report the downstream symptom (identity theft, brokerage account drain, crypto theft) rather than the SIM swap itself, so the headline complaint count is a lower bound. Third, the 2024 sample (982 complaints) is small enough that a single high-loss event could move the average by several thousand dollars; the long-tail distribution remains.
The FBI's 2022 PSA I-020822-PSA framed the 2018-2021 escalation in plain terms: 320 complaints across the 2018-2020 window with about US$12M in losses, then 1,611 complaints in 2021 alone with more than US$68M in losses. The 2022 peak at US$72.65M coincides with the FTX hack year and with the Scattered Spider ramp-up. The 2024 floor at US$26M coincides with the FCC rule taking effect and a parallel CrowdStrike-documented shift toward help-desk vishing as a faster initial access path than SIM swap on its own.
The Princeton CITP study still defines the baseline
The single most-cited piece of academic SIM swap research is "An Empirical Study of Wireless Carrier Authentication for SIM Swaps" by Kevin Lee, Ben Kaiser, Jonathan Mayer, and Arvind Narayanan, published at SOUPS 2020. It is also the cleanest demonstration of why the FCC eventually moved.
The methodology was direct. The authors purchased 50 prepaid mobile accounts (10 each across AT&T, T-Mobile, Tracfone, US Mobile, and Verizon Wireless), built up a usage history that mirrored a normal customer, then called each carrier's customer service line and attempted a SIM swap. The conclusion: all five carriers used insecure authentication challenges that could be easily subverted by attackers, and 39 of 50 attempted swaps succeeded when attackers had only readily available biographical data (Lee et al., 2020, p. 1).
The downstream finding is the one that drove the FCC rulemaking. The team reverse-engineered the authentication policies of more than 140 websites that supported phone-based authentication. 17 websites were found vulnerable to SIM-swap-only account takeover, meaning a successful swap by itself, without the original password, was enough to break in because the site allowed SMS as both the second factor and the recovery channel. Nine of those 17 companies had not remediated by the time the paper was published (Lee et al., 2020, p. 14). The paper has been cited in subsequent FCC notices of proposed rulemaking and is the academic backbone of the "SMS 2FA is structurally fragile" argument.
The FCC final rule and what it actually changed
The FCC adopted FCC 23-95A on November 15, 2023 (FCC press release). The Report and Order revised the Customer Proprietary Network Information rules and the Local Number Portability rules to attack SIM swap and port-out fraud. It was published in the Federal Register on December 8, 2023.
What the rule requires:
Wireless providers must adopt a secure method of authenticating a customer before redirecting a customer's phone number to a new device or to a new provider.
Wireless providers must immediately notify customers whenever a SIM change or port-out request is made on their account.
Providers must retain records of SIM change requests and the authentication measures used.
The Commission concluded that methods relying on readily available biographical information, account information, recent payment information, and call detail information are NOT secure methods of authentication for SIM swaps and port-outs (Federal Register, December 8 2023).
The compliance date was set at July 8, 2024. On July 5, 2024 the FCC granted a partial waiver to a CTIA / CCA / NCTA petition and deferred the operative compliance date until the Office of Management and Budget completed Paperwork Reduction Act review (FCC consumer affairs notice, July 2024). OMB approval came later in 2024. The practical result for carriers: build customer-set port-out PINs, immediate alerting on SIM changes, mandatory authentication-method record retention, and removal of biographical fallback flows from help-desk scripts.
CTIA, the wireless carrier trade group, asked for an additional year of delay during the rulemaking and was partially accommodated. By Q1 2026, every major US wireless carrier publicly documents customer-set port-out PINs, in-app SIM-change toggles, and SMS plus email alerting on swap requests.
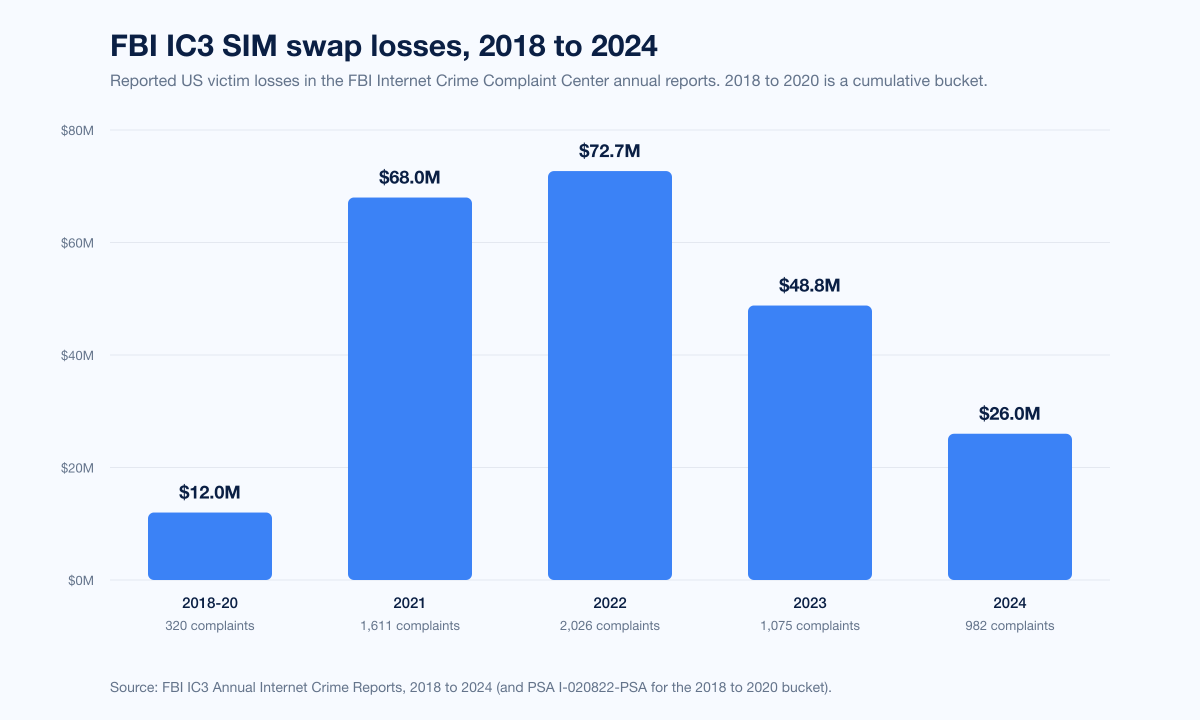
Scattered Spider: the enterprise SIM swap operator
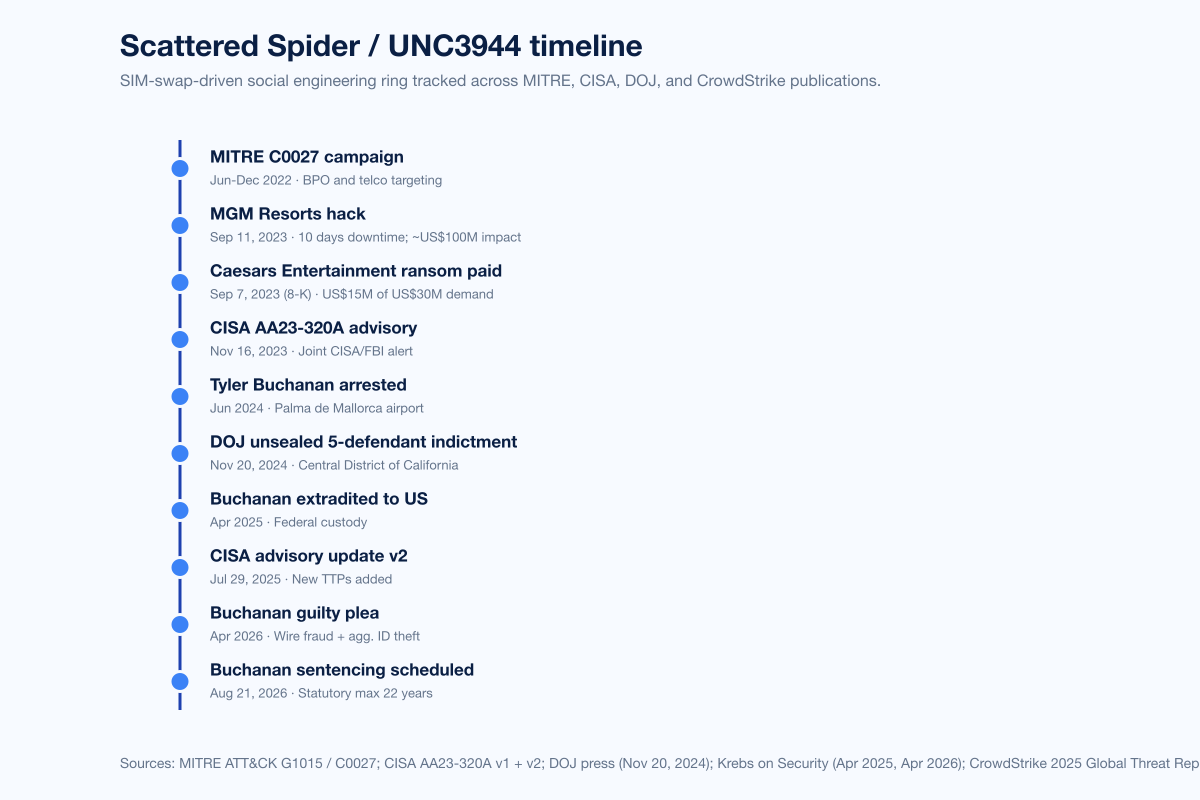
The story that pushed SIM swap from "consumer crypto" to "board-level enterprise risk" is Scattered Spider, also tracked as UNC3944, Octo Tempest, Storm-0875, Muddled Libra, Roasted 0ktapus, and Scatter Swine. CISA's AA23-320A advisory, originally published November 16, 2023 and updated July 29, 2025, describes the group as native English-speaking and cites individuals "primarily between the ages of 19 and 22 as of September 2023" (CISA AA23-320A).
The CISA advisory and Microsoft's October 25, 2023 Octo Tempest writeup (Microsoft Security Blog) describe a consistent tradecraft pattern: SMS phishing of help-desk personnel, vishing of internal IT support to request password resets, MFA push bombing, and SIM swap of the targeted user's mobile carrier account to capture the SMS one-time passcode that the help desk re-issues during the fake reset. CrowdStrike's 2025 Global Threat Report attributes a +442% surge in vishing attacks H1 to H2 2024 to this exact tradecraft pattern (CrowdStrike 2025 Global Threat Report).
MGM Resorts (September 11, 2023)
MGM Resorts disclosed in a Form 8-K filed October 5, 2023 that it had suffered a ransomware-driven outage spanning approximately ten days, with an estimated US$100M of financial impact to the company. The incident-response narrative captured by CISA, by Mandiant, and by independent reporting (Bloomberg, The Wall Street Journal, Krebs) is that Scattered Spider operators called MGM's internal IT helpdesk, impersonated a legitimate employee whose details they had pulled from LinkedIn, requested a password reset, and bypassed MFA via a SIM swap. From there they pivoted to identity infrastructure and detonated ALPHV / BlackCat ransomware. MITRE attributes the campaign to G1015.
Caesars Entertainment (August to September 2023)
Caesars Entertainment disclosed in its Form 8-K filed September 7, 2023 that it had experienced a "social engineering attack on an outsourced IT support vendor" and had paid an "approximately US$15M" ransom to a threat actor that demanded US$30M. The Caesars filing names neither Scattered Spider nor ALPHV, but Recorded Future, Mandiant, and CISA all attribute the intrusion to the same operator-and-affiliate pair as the MGM event. The 50% ransom discount Caesars negotiated is unusually well-documented in public filings.
November 20, 2024: the five-defendant DOJ indictment
On November 20, 2024 the US Attorney's Office for the Central District of California unsealed criminal charges against five alleged Scattered Spider members:
Tyler Robert Buchanan, 24, Dundee, Scotland
Ahmed Hossam Eldin Elbadawy (a.k.a. "AD"), 24, College Station, Texas
Joel Martin Evans (a.k.a. "joeleoli"), 26, Jacksonville, North Carolina
Evans Onyeaka Osiebo, 21, Dallas, Texas
Noah Michael Urban, 21, Palm Coast, Florida
Buchanan was arrested in June 2024 at the airport in Palma de Mallorca while trying to board a flight to Italy, extradited to the United States in April 2025, and pleaded guilty in April 2026 to conspiracy to commit wire fraud and aggravated identity theft. Buchanan admitted controlling more than US$26M stolen from victims and at least US$8M in cryptocurrency taken directly from individuals; sentencing is scheduled for August 21, 2026 with a statutory maximum of 22 years in federal prison (Krebs on Security, April 2026). Noah Urban was sentenced separately to 10 years in federal prison plus US$13M in restitution in 2025 (Krebs on Security, April 2025). Elbadawy, Evans, and Osiebo still face criminal charges as of April 2026.
The CISA advisory was updated on July 29, 2025 to add new TTPs, additional malware variants, and updated extortion techniques associated with the group (CISA AA23-320A v2 PDF). CrowdStrike's 2025 Global Threat Report describes the group as "resurg[ing] in 2025 with faster and more aggressive tradecraft, leveraging vishing and help desk impersonation to reset credentials, bypass MFA, and move laterally across SaaS and cloud environments" (CrowdStrike 2025 GTR).
Named SIM swap incidents and the long tail
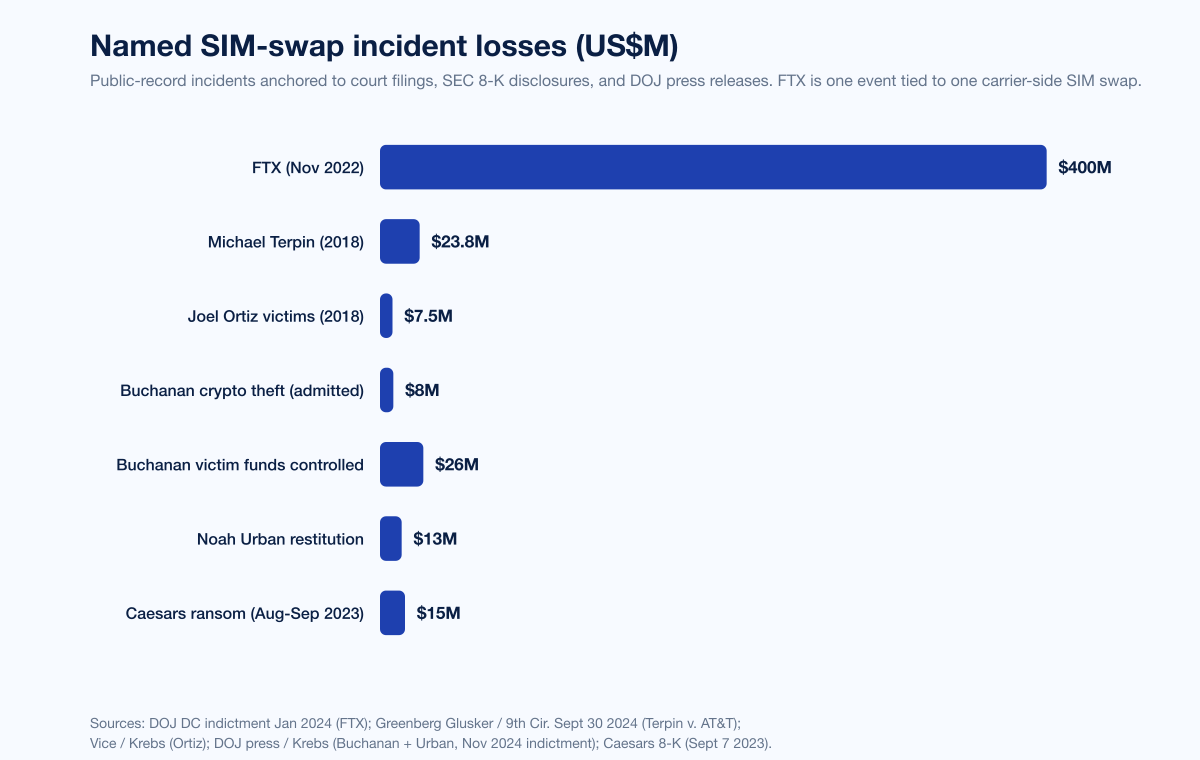
The headline FBI IC3 average loss per complaint hides a fat-tailed distribution. Most cases involve five-figure consumer losses; a handful of named cryptocurrency cases account for the vast majority of dollar value.
Joel Ortiz (February 2019, first US SIM swap conviction)
On February 1, 2019, Joel Ortiz, then 20, pleaded guilty in Santa Clara County Superior Court to stealing more than US$5M in cryptocurrency from at least 40 victims via SIM swap. He was sentenced to 10 years in California state prison. Different sources cite total stolen value at US$5M (Vice) or US$7.5M (Coindesk, BitcoinMagazine), reflecting the difference between confirmed and alleged victim losses. Ortiz is the first person convicted in the United States for SIM swapping (Vice, February 2019).
Michael Terpin v. AT&T (2018-2026, ongoing)
Crypto investor Michael Terpin was SIM-swapped on January 7, 2018. Ellis Pinsky, then 15 years old, bribed an AT&T employee to transfer Terpin's number to a SIM card in Pinsky's possession; the attackers then drained US$23.8M in cryptocurrency. Terpin sued AT&T for US$23.8M in compensatory damages plus US$200M in punitive damages. The district court granted AT&T summary judgment in 2020. The Ninth Circuit Court of Appeals revived Terpin's Federal Communications Act claim against AT&T on September 30, 2024 (9th Cir. opinion via Justia; Greenberg Glusker firm announcement). Terpin's lead counsel Pierce O'Donnell told reporters he will pursue US$24M in damages plus at least US$14M in interest plus attorney's fees, totaling at least US$45M.
Nicholas Truglia (2018 SIM swap, December 2022 plea, July 2025 resentencing)
Nicholas Truglia, a Terpin co-conspirator, was sentenced in December 2022 to 18 months in federal prison and ordered to pay US$20M in restitution to Terpin. After Truglia failed to make any restitution payments, US District Judge Alvin Hellerstein resentenced Truglia on July 10, 2025 to 12 years in federal prison (Decrypt, July 2025). Truglia was held in contempt and was released to make payments after serving the 18-month original sentence; he made no payments and the resentence followed.
FTX (November 11-12, 2022)
The largest publicly attributed SIM-swap-driven theft on record. On November 11, 2022, the same day FTX filed for Chapter 11, Robert Powell, Carter Rohn, and Emily Hernandez worked together to obtain stolen personally identifiable information of more than 50 victims. Hernandez traveled to a local AT&T retail store with a forged ID containing her photograph and an FTX employee's information, executed a SIM swap of the FTX employee's number, and forwarded authentication codes to Powell. Co-conspirators then transferred over US$400M in virtual currency from FTX wallets to wallets controlled by the co-conspirators (CNBC, February 2 2024; Krebs on Security, February 2024; Cloud Security Alliance writeup, September 2025). The DOJ DC indictment was unsealed in January 2024.
SEC X account hijack (January 9, 2024)
On January 9, 2024 the @SECGov X account was used to post a false claim that the SEC had approved spot Bitcoin ETFs. Bitcoin spiked from roughly US$45,000 to nearly US$48,000 before SEC Chairman Gary Gensler corrected the post and prices reversed roughly US$2,000 (Fortune, January 22 2024). The SEC subsequently confirmed the account was taken over via a SIM swap of the phone number associated with the @SECGov account, which lacked two-factor authentication. Eric Council Jr., of Alabama, pleaded guilty in February 2025 and was sentenced in May 2025 to 14 months in federal prison (CNBC, February 10 2025). The legitimate Bitcoin ETF approval was issued the following day.
Jack Dorsey Twitter hijack (August 30, 2019)
The Chuckling Squad group SIM-swapped Twitter CEO Jack Dorsey's mobile number on August 30, 2019 and held the @jack account for approximately 20 minutes before Twitter recovered control. The group exploited the legacy Cloudhopper SMS-to-tweet integration to post bomb threats and racist content. A minor was arrested in Santa Clara County, California, in November 2019.
Jonathan Katz (March 2024 plea)
On March 12, 2024, Jonathan Katz, a 42-year-old former telecom store manager from Marlton, New Jersey, pleaded guilty before US Chief District Judge Renee Marie Bumb (D.N.J. Camden) to conspiracy to gain unauthorized access to a protected computer. Katz admitted to swapping SIM numbers associated with customer phone numbers into mobile devices controlled by another individual, enabling that individual to access victims' electronic accounts (DOJ press release). Katz is one of the cleanest published examples of the carrier-insider bribery pathway the Princeton CITP paper warned about.
Carrier-side context: T-Mobile, AT&T, and the insider problem
The 2021 T-Mobile breach is often conflated with SIM swap activity. It was not. In August 2021 T-Mobile disclosed that attackers had obtained data on approximately 76.6 million individuals, including 40M+ former and prospective applicants for credit, 7.8M existing postpaid customers, and 850k prepaid customers. Exposed fields included names, dates of birth, Social Security numbers, and driver's license / ID numbers (TechCrunch, August 2021). T-Mobile agreed to a US$350M class-action settlement in late 2022 and accepted a US$15M FCC fine in 2024.
Separately, in February 2021, T-Mobile disclosed that threat actors targeted hundreds of users in SIM swap attacks after gaining access to an internal T-Mobile customer service application. That incident is the SIM-swap-relevant one and matters more for risk modeling than the broader 2021 breach.
The structural lesson across T-Mobile, AT&T (the Terpin case), and the Katz / Marlton plea is that insider bribery and help-desk social engineering are the dominant SIM swap pathways, not technical compromise of SS7 or HLR systems. The FCC final rule does not address insider bribery directly; it works on the front-of-house help-desk authentication problem. Insider risk programs at carriers and at the BPO companies that staff carrier customer service are the missing layer.
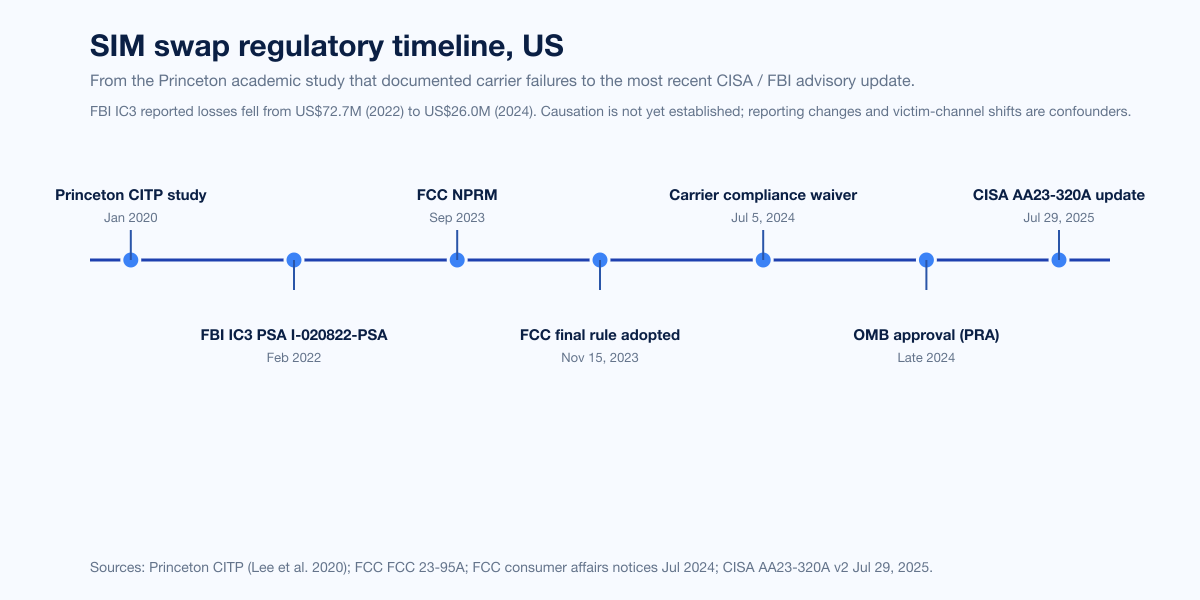
Sumsub, Javelin, and Cifas: where SIM swap lives in the wider identity-fraud landscape
SIM swap, when treated as a category, is small. The same vector dominates as a stage in larger account takeover and identity fraud losses.
Javelin Strategy & Research's 2025 Identity Fraud Study, "Breaking Barriers to Innovation" reported US$27.2 billion in total US identity fraud losses in 2024, a +19% YoY increase (Javelin, March 2025). Account takeover fraud accounted for US$16 billion of the US$27 billion+ total, with 39% of ATO victims reporting compromise of checking accounts and 23% reporting compromise of email accounts. Javelin's 2026 follow-up "The Illusion of Progress" (April 21, 2026) reported that fraud losses had stabilized at the 2024 level but that AI-driven threats were eroding consumer trust (Javelin, April 2026).
Sumsub's Identity Fraud Report 2025-2026 released October 2025 reported that the global fraud rate fell from 2.6% in 2024 to 2.2% in 2025, but the share of multi-step attacks rose from 10% in 2024 to 28% in 2025, a +180% YoY growth in "sophisticated" fraud (Sumsub press release, October 2025). Sumsub explicitly identifies SIM swap as one of the techniques attackers use to "hijack verified accounts" and inherit the trust signal from completed KYC. Account takeover ranks second among Sumsub-tracked third-party fraud schemes at 19%, behind identity theft at 28% and ahead of card testing (17%), social engineering (16%), and bot attacks (12%).
Cifas, the UK fraud-prevention body, reported 2,961 unauthorized SIM swap cases filed to the National Fraud Database in 2024, a +1,055% YoY increase from 289 cases in 2023 (Cifas, March 2025). Action Fraud, the separate UK national reporting centre, recorded 2,037 SIM swap cases through end of November 2024. 48% of all UK account takeover cases in 2024 involved mobile phone accounts, and victims aged 61 and over made up 29% of account takeover cases (a +90% YoY increase in that demographic). Combined UK losses tied to SIM swap fraud across 2023 and 2024 were GBP 5.35M (about US$6.7M at March 2026 FX).
The UK and US trends diverge because the FCC final rule does not apply to UK carriers and Ofcom has not yet issued an equivalent. A regulatory delta between US and UK SIM swap fraud levels is consistent with what the Princeton CITP paper would predict: where carrier authentication remains soft, SIM swap volumes rise.
Crypto exposure: Chainalysis, TRM Labs, and the SIM-swap subset
Chainalysis documented US$2.2B stolen from crypto platforms in 2024 across 303 hacking incidents, a +21% YoY increase (Chainalysis crypto-hacking blog). DPRK-linked groups accounted for US$1.34B across 47 incidents in 2024, up sharply from US$660.5M and 20 incidents in 2023. Chainalysis's full-year 2025 update (published February 2026) reported US$3.4B in stolen crypto for 2025 (Chainalysis 2025 EOY).
The SIM-swap subset of those numbers is harder to isolate, because Chainalysis's methodology aggregates across exchange hacks, DeFi exploits, and individual wallet drains. The firm's dedicated SIM-swap blog post documents one canonical investigation: a victim approached Chainalysis after losing more than US$25,000 to a Poloniex Exchange SIM swap; the firm traced the funds and supported recovery via blockchain analysis (Chainalysis SIM swap blog). The same blog references the Terpin case as a precedent: a 15-year-old New York high school student successfully SIM-swapped a cryptocurrency entrepreneur and stole nearly US$24M in cryptocurrency.
NIST SP 800-63B Rev 4 and the formal reclassification of SMS
The most important authoritative shift in 2025 is NIST SP 800-63B Rev 4 (final PDF), which formally classifies SMS and PSTN one-time passcodes as a restricted authenticator. This is the first time NIST has created a "restricted" tier in the authenticator hierarchy. Rev 3 (the predecessor) had cautions about SMS but permitted it as a regular authenticator; the Rev 4 second public draft initially proposed retiring SMS entirely, but practical impact on federal agencies and on relying parties forced a compromise.
Key Rev 4 language relevant to SIM swap:
Verifiers SHOULD consider risk indicators such as device swap, SIM change, number porting, or other abnormal behavior before using the PSTN to deliver an out-of-band authentication secret.
Verifier SHALL verify that the pre-registered telephone number being used is associated with a specific physical device (not a VoIP number, not a forwarded number).
Organizations using SMS must offer alternatives, inform users of the risks, mitigate the risks, update risk assessments, and maintain a migration plan away from SMS.
The downstream practical impact: every Federal agency, every FedRAMP authorized cloud service, and every relying party that maps to NIST SP 800-63 (a long list, including most US financial services) is now on a documented obligation to move off SMS as a primary factor and to gate SMS delivery on SIM-change risk indicators. Carrier-side telemetry on number portability, SIM swap activity, and CNAM lookups becomes a compliance signal, not just a fraud-prevention signal.
Mitigation: what to do, ranked from weakest to strongest
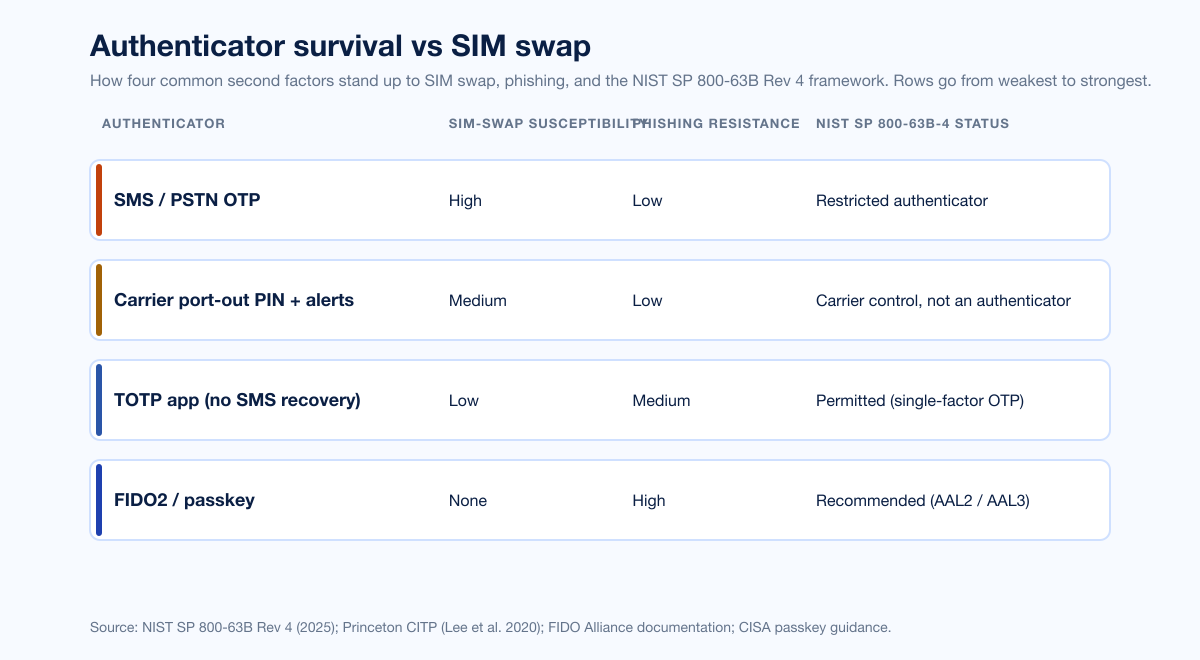
The mitigation ladder for individual users and for organizations follows the same shape: replace the bypass first, then the attack vector.
Authenticator | SIM-swap susceptibility | Phishing resistance | NIST SP 800-63B Rev 4 status | Recommendation |
|---|---|---|---|---|
SMS / PSTN OTP | High | Low | Restricted authenticator | Treat as fallback only; gate on SIM-change risk indicators |
Carrier port-out PIN + SIM-change alerts | Medium | Low | Carrier control, not an authenticator | Set on every line; do not reuse account password |
TOTP app (no SMS recovery) | Low | Medium | Permitted (single-factor OTP) | Acceptable interim for legacy services |
FIDO2 / passkey | None | High | Recommended (AAL2 / AAL3) | Default for every privileged user |
For consumers: set a port-out PIN with the carrier (the FCC rule requires US carriers to support customer-set authentication), enable SIM-change SMS plus email alerts, move every recoverable account to passkeys or FIDO2, switch from SMS 2FA to TOTP where passkey is unsupported, and remove the phone number from account recovery wherever the relying party offers an alternative. The Princeton CITP "17 vulnerable websites" finding is the reason the recovery option matters: a SIM swap that succeeds against a site allowing SMS recovery is sufficient by itself to take over the account.
For organizations: every privileged user moves to FIDO2 or passkeys. Help-desk callers verify identity through a corporate IDP out-of-band channel, never through phone-based callback, and never by accepting biographical data, recent payment numbers, or call detail records as authentication. Help-desk social engineering is the actual attack surface; SIM swap is the bypass. The November 2024 Scattered Spider indictment is the strongest argument that this matters. Help-desk staff, including outsourced BPO providers, get tabletop exercises against the Octo Tempest tradecraft, and the corporate IDP is the source of truth for any reset.
What this means for defenders
Treat SIM swap as a stage, not a category. The IC3 numbers say SIM swap is shrinking; the Javelin and Sumsub numbers say account takeover is not. SIM swap is now usually the SMS-2FA bypass step in a larger help-desk-vishing or AiTM attack, and the post-mortem categorizes it under the larger event. Threat models should follow the actual flow.
Move every privileged user to passkey or FIDO2 before 2026 ends. NIST SP 800-63B Rev 4 forces the conversation; the CISO who waits is the CISO whose name is in the next 8-K. The technology is mature; the rollout cost is the migration plan, not the device cost.
Build the help-desk runbook before the help-desk vishing call lands. The MGM, Caesars, and 2024 Scattered Spider indictments all begin with a help-desk impersonation call. Adversary-emulation engagements that exercise the help-desk identity-verification flow find more issues per dollar than almost any other red team scope right now.
Set the carrier-side controls on the executives whose accounts most matter. Every C-suite executive, every board member, every IR-team key contact: set a carrier port-out PIN, enable SMS-change alerts, and document the incident response number that calls through if the executive's phone unexpectedly loses service. The FCC rule requires the carrier to offer the controls; you have to opt in.
Reassess SMS dependency in every IDP, every VPN, every recovery flow. The Princeton "17 vulnerable websites" finding is institution-agnostic: anywhere SMS doubles as recovery and as second factor, a successful SIM swap is sufficient on its own. Audit the recovery options on every account that matters.
A red team scoped against the help-desk identity-verification flow, modeled on the Octo Tempest tradecraft, is the single highest-leverage exercise an enterprise can run in 2026 against this threat. Stingrai's adversary simulation engagements and PTaaS cover this scope; the Scattered Spider tradecraft case study walks through one such engagement in detail.
Frequently asked questions
What were total US SIM swap losses in 2024?
The FBI Internet Crime Complaint Center reported US$25,983,946 in SIM swap losses across 982 complaints in 2024, down from US$48,798,103 across 1,075 complaints in 2023 and US$72,652,571 across 2,026 complaints in 2022 (FBI IC3 2024 Internet Crime Report). The decline coincides with the FCC's November 2023 SIM swap rule and broader carrier alerting, but reporting-channel shifts confound a clean causation claim.
What is the largest SIM swap loss on record?
The November 2022 FTX hack, in which co-conspirators transferred over US$400M in cryptocurrency from FTX hot wallets after a SIM swap of an FTX employee at an AT&T retail store, is the largest publicly attributed SIM-swap-driven loss. Robert Powell, Carter Rohn, and Emily Hernandez were indicted in DC in January 2024 (CNBC, February 2 2024).
What did the FCC's SIM swap rule actually require?
The FCC adopted FCC 23-95A on November 15, 2023. It requires wireless carriers to use secure customer authentication before redirecting a number to a new device or new provider, immediately notify customers of any SIM change or port-out request, retain records of the authentication method used, and explicitly bars biographical information, account information, recent payment information, or call detail information as standalone authentication. The compliance date was July 8, 2024, deferred until OMB completed Paperwork Reduction Act review (FCC consumer affairs notice, July 2024).
Who is Scattered Spider and how do they use SIM swaps?
Scattered Spider (also tracked as UNC3944, Octo Tempest, Storm-0875, Muddled Libra) is a native English-speaking cybercrime ring active since 2022. CISA advisory AA23-320A (updated July 29, 2025) describes the group as combining help-desk vishing, MFA push bombing, and SIM swaps to bypass MFA and gain initial access. CrowdStrike's 2025 Global Threat Report attributes a +442% surge in vishing attacks H1 to H2 2024 to this tradecraft.
How many websites are vulnerable to SIM-swap-only account takeover?
The Princeton CITP study by Lee, Kaiser, Mayer, and Narayanan (2020) found 17 websites where a successful SIM swap, by itself, was sufficient to take over a user account, even without password compromise. The study examined more than 140 websites with phone-based authentication. 9 of the 17 vulnerable companies had not remediated by the time the paper was published.
Is SMS 2FA still safe in 2026?
NIST SP 800-63B Rev 4 (2025) classifies SMS and PSTN one-time passcodes as a restricted authenticator, the first time NIST has formally created that designation. Verifiers using SMS for out-of-band authentication SHALL verify the pre-registered telephone number is associated with a specific physical device and SHOULD consider risk indicators including device swap, SIM change, and number porting. Practically, treat SMS as a fallback factor only, not as a primary authenticator for high-value accounts.
How did the SEC X account get hijacked in January 2024?
On January 9, 2024 the SEC's @SECGov X account was hijacked via a SIM swap of the phone number associated with the account. The account did not have two-factor authentication enabled, so the SIM swap and a single password reset were the only steps needed. A false post claiming spot Bitcoin ETF approval briefly moved BTC roughly US$3,000. Eric Council Jr. of Alabama pleaded guilty in February 2025 and received a 14-month federal prison sentence in May 2025.
What is the average loss per SIM swap victim?
Across the FBI IC3 2024 Internet Crime Report, average loss per complaint was approximately US$26,460 in 2024 (US$25.98M / 982), down from approximately US$45,393 per complaint in 2023 and US$35,860 per complaint in 2022. The averages mask a long-tail distribution: most cases involve five-figure consumer losses, while a handful of named cryptocurrency cases account for tens of millions per incident.
What did the November 2024 Scattered Spider indictment charge?
On November 20, 2024 the US Attorney's Office for the Central District of California unsealed criminal charges against five alleged Scattered Spider members: Tyler Robert Buchanan (Scotland), Ahmed Hossam Eldin Elbadawy (Texas), Joel Martin Evans (North Carolina), Evans Onyeaka Osiebo (Texas), and Noah Michael Urban (Florida). Urban was sentenced to 10 years federal prison plus US$13M in restitution. Buchanan pleaded guilty in April 2026 to conspiracy to commit wire fraud and aggravated identity theft and admitted controlling US$26M+ from victims; sentencing is scheduled for August 21, 2026 with a 22-year statutory maximum.
How big is the SIM swap problem in the UK?
Cifas reported that unauthorized SIM swap cases filed to the UK National Fraud Database rose +1,055% in 2024 to 2,961 cases, up from 289 in 2023. Action Fraud, the separate national reporting centre, recorded 2,037 SIM swap cases through end of November 2024. 48% of all UK account takeover cases in 2024 involved mobile phone accounts, and victims aged 61 and over made up 29% of account takeover cases (a 90% YoY increase in that demographic).
What should organizations do today to mitigate SIM swap risk?
Treat SMS as a restricted authenticator. Move every privileged user to FIDO2 / passkeys, set port-out PINs at the carrier (separate from the account password), require help-desk callers to verify identity through an out-of-band channel (corporate IDP, not phone-based callback), enable carrier SIM-change alerts, and rehearse the help-desk social engineering scenario in red team exercises. The 2024 Scattered Spider indictments make clear that the social-engineering surface is where the attacker actually lands; SMS 2FA is the bypass, not the attack vector. Stingrai's adversary simulation services cover this scope.
References
Federal Bureau of Investigation, Internet Crime Complaint Center. 2024 Internet Crime Report. Released April 2025. https://www.ic3.gov/AnnualReport/Reports/2024_IC3Report.pdf. The annual aggregation of US victim complaints to the IC3, including SIM swap as a separate crime category. Source for all 2024 SIM swap loss and complaint figures.
Federal Bureau of Investigation, Internet Crime Complaint Center. 2023 Internet Crime Report. Released April 2024. https://www.ic3.gov/AnnualReport/Reports/2023_IC3Report.pdf. Source for 2023 SIM swap loss and complaint figures.
Federal Bureau of Investigation, Internet Crime Complaint Center. 2022 Internet Crime Report. Released March 2023. https://www.ic3.gov/AnnualReport/Reports/2022_ic3report.pdf. Source for 2022 peak SIM swap loss and complaint figures.
Federal Bureau of Investigation, Internet Crime Complaint Center. Public Service Announcement I-020822-PSA: Criminals Increasing SIM Swap Schemes to Steal Millions of Dollars from US Public. February 8, 2022. https://www.ic3.gov/PSA/2022/PSA220208. Source for 2018 to 2020 cumulative complaints and 2021 figures.
Federal Communications Commission. Report and Order FCC 23-95A: Protecting Consumers from SIM-Swap and Port-Out Fraud. Adopted November 15, 2023. https://www.fcc.gov/document/fcc-protects-cell-phone-customers-against-sim-swap-scams. The final rule adopting customer authentication and notification requirements for SIM swap and port-out.
Federal Communications Commission. Notice on Effective Compliance Date for SIM Swapping Item. July 2024. https://www.fcc.gov/consumer-governmental-affairs/fcc-announces-effective-date-sim-swapping-item. The compliance-date waiver that deferred operative implementation until OMB Paperwork Reduction Act review.
Federal Register. Protecting Consumers from SIM-Swap and Port-Out Fraud. December 8, 2023. https://www.federalregister.gov/documents/2023/12/08/2023-26338/protecting-consumers-from-sim-swap-and-port-out-fraud. Federal Register publication of FCC 23-95A.
National Institute of Standards and Technology. Special Publication 800-63B-4: Digital Identity Guidelines, Authentication and Authenticator Management. Final, 2025. https://nvlpubs.nist.gov/nistpubs/SpecialPublications/NIST.SP.800-63B-4.pdf. Reclassifies SMS and PSTN OTP as a restricted authenticator and codifies SIM-change risk-indicator obligations.
Cybersecurity and Infrastructure Security Agency. Joint Cybersecurity Advisory AA23-320A: Scattered Spider. Original November 16, 2023; updated v2 July 29, 2025. https://www.cisa.gov/news-events/cybersecurity-advisories/aa23-320a. Joint CISA / FBI / RCMP / ASD / AFP advisory describing Scattered Spider tradecraft including SIM swap and help-desk vishing.
Princeton CITP, Kevin Lee, Ben Kaiser, Jonathan Mayer, and Arvind Narayanan. An Empirical Study of Wireless Carrier Authentication for SIM Swaps. Proceedings of the 16th Symposium on Usable Privacy and Security (SOUPS), 2020. https://www.issms2fasecure.com/assets/sim_swaps-01-10-2020.pdf. The empirical study of US carrier authentication failures and downstream website vulnerability.
MITRE ATT&CK. Technique T1451: SIM Card Swap (Mobile). https://attack.mitre.org/techniques/T1451/. The ATT&CK technique entry covering carrier-side SIM swap social engineering, insider attacks, and forged-identity pathways.
MITRE ATT&CK. Group G1015: Scattered Spider and Campaign C0027: 2022 Scattered Spider BPO and telecommunications targeting. https://attack.mitre.org/groups/G1015/. Adversary group profile and named campaign covering June through December 2022 SIM swap activity.
Microsoft Threat Intelligence. Octo Tempest crosses boundaries to facilitate extortion, encryption, and destruction. October 25, 2023. https://www.microsoft.com/en-us/security/blog/2023/10/25/octo-tempest-crosses-boundaries-to-facilitate-extortion-encryption-and-destruction/. Microsoft's profile of the Storm-0875 / Octo Tempest cluster and its SIM-swap tradecraft.
CrowdStrike. 2025 Global Threat Report. February 2025. https://www.crowdstrike.com/en-us/blog/crowdstrike-2025-global-threat-report-findings/. Source for the +442% H1-to-H2 2024 vishing growth metric and the 2025 Scattered Spider resurgence narrative.
United States Department of Justice, US Attorney's Office for the Central District of California. Five Defendants Charged Federally for Running Scheme that Stole Millions from Victims' Bank Accounts. November 20, 2024. Source for the five-defendant Scattered Spider indictment and Buchanan, Elbadawy, Evans, Osiebo, and Urban defendant list.
United States Department of Justice, US Attorney's Office for DC. Powell, Rohn, Hernandez indictment. Unsealed January 2024. Source for the FTX SIM swap indictment, US$400M figure, and PII-fraud-ring scope.
United States Department of Justice, US Attorney's Office for the District of New Jersey. Former Telecommunications Company Manager Admits Role in SIM Swapping Scheme. March 12, 2024. https://www.justice.gov/usao-nj/pr/former-telecommunications-company-manager-admits-role-sim-swapping-scheme. Jonathan Katz plea, telecom-store-manager insider case.
MGM Resorts International. Form 8-K, Item 8.01. Filed October 5, 2023. Source for the approximately ten-day downtime and US$100M financial impact disclosure.
Caesars Entertainment Inc. Form 8-K, Item 1.05. Filed September 7, 2023. Source for the Caesars approximately US$15M ransom payment of a US$30M demand.
Sumsub. Identity Fraud Report 2025-2026. Released October 2025. https://sumsub.com/fraud-report-2025/. Source for the global fraud rate trend, the 180% YoY sophisticated-fraud growth metric, and SIM swap as an account-takeover vector.
Javelin Strategy & Research. 2025 Identity Fraud Study: Breaking Barriers to Innovation. March 2025. https://javelinstrategy.com/research/2025-identity-fraud-study-breaking-barriers-innovation. Source for the US$27.2B 2024 identity fraud total, US$16B account takeover share, and 39% checking / 23% email ATO breakdown.
Javelin Strategy & Research. 2026 Identity Fraud Study: The Illusion of Progress. April 21, 2026. https://javelinstrategy.com/whitepapers/2026-identity-fraud-study-illusion-progress. Follow-up study cited for the 2025 stabilization narrative.
Chainalysis. Funds Stolen from Crypto Platforms Fall 54% in 2024 (US$2.2B total). February 2025. https://www.chainalysis.com/blog/crypto-hacking-stolen-funds-2025/. Source for 2024 crypto-theft totals and DPRK incident attribution.
Chainalysis. Fighting Back Against SIM Swap Attacks with Blockchain Analysis. https://www.chainalysis.com/blog/sim-swap-attacks/. Methodology and casework on tracing SIM-swap-driven cryptocurrency theft.
Cifas. 1,055% surge in unauthorised SIM swaps as mobile and telecoms sector hit hard by rising fraud. March 2025. https://www.cifas.org.uk/newsroom/huge-surge-see-sim-swaps-hit-telco-and-mobile. UK National Fraud Database SIM swap surge figures, ATO mobile-account share, and age-61+ trend.
Krebs on Security. Alleged 'Scattered Spider' Member Extradited to U.S. April 2025. https://krebsonsecurity.com/2025/04/alleged-scattered-spider-member-extradited-to-u-s/. Court-record corroboration for Buchanan extradition timeline and Urban sentence.
Krebs on Security. 'Scattered Spider' Member 'Tylerb' Pleads Guilty. April 2026. https://krebsonsecurity.com/2026/04/scattered-spider-member-tylerb-pleads-guilty/. Court-record corroboration for Buchanan April 2026 plea and US$26M / US$8M figures.
Krebs on Security. Arrests in $400M SIM-Swap Tied to Heist at FTX? February 2024. https://krebsonsecurity.com/2024/02/arrests-in-400m-sim-swap-tied-to-heist-at-ftx/. Court-record corroboration for the FTX indictment.
Decrypt. SIM Swapper Who Stole $20 Million in Crypto Resentenced to 12 Years in Prison. July 2025. https://decrypt.co/329658/sim-swapper-20-million-crypto-resentenced-12-years-prison. Source for the Truglia July 10, 2025 resentencing.
Greenberg Glusker. Greenberg Glusker Wins Precedent-Setting Appeal for Cryptocurrency Investor Michael Terpin. September 2024. https://www.greenbergglusker.com/publications/greenberg-glusker-wins-precedent-setting-appeal-for-cryptocurrency-investor-michael-terpin-reviving-landmark-suit-on-federal-communications-act-violations/. Counsel's announcement of the Ninth Circuit revival of Terpin v. AT&T.
Justia. Terpin v. AT&T Mobility, LLC, No. 23-55375 (9th Cir. 2024). September 30, 2024. https://law.justia.com/cases/federal/appellate-courts/ca9/23-55375/23-55375-2024-09-30.html. Ninth Circuit opinion text.
Fortune. SEC blames 'SIM swap' attack for disastrous X hack ahead of Bitcoin ETF approval. January 22, 2024. https://fortune.com/crypto/2024/01/22/sec-x-hack-bitcoin-etfs-cybersecurity/. Source for the SEC @SECGov SIM swap and absent-2FA detail.
CNBC. Three people indicted in $400 million FTX crypto hack conspiracy. February 2, 2024. https://www.cnbc.com/2024/02/02/three-people-indicted-in-400-million-ftx-hack-conspiracy.html. Court-record corroboration for the FTX SIM swap indictment.
CNBC. Guilty plea in SEC X account hack touting bitcoin ETF. February 10, 2025. https://www.cnbc.com/2025/02/10/man-pleads-guilty-in-hack-of-secs-x-account-that-claimed-approval-of-bitcoin-etfs.html. Source for the Eric Council Jr. plea.
TechCrunch. T-Mobile says at least 47M current and former customers affected by hack. August 18, 2021. https://techcrunch.com/2021/08/18/t-mobile-says-at-least-47m-current-and-former-customers-affected-by-data-breach/. Carrier-side breach-context source for the 2021 T-Mobile incident.