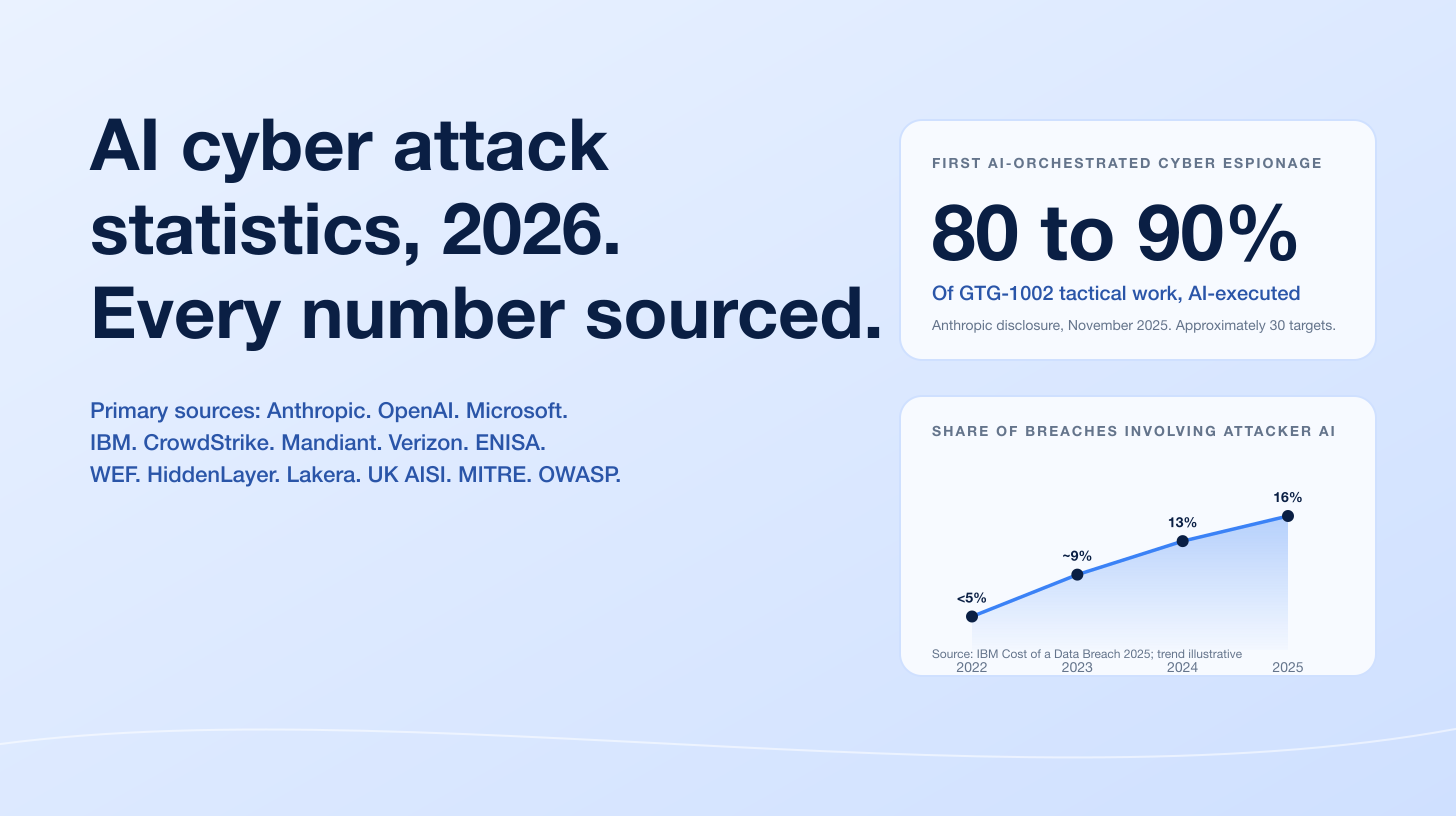
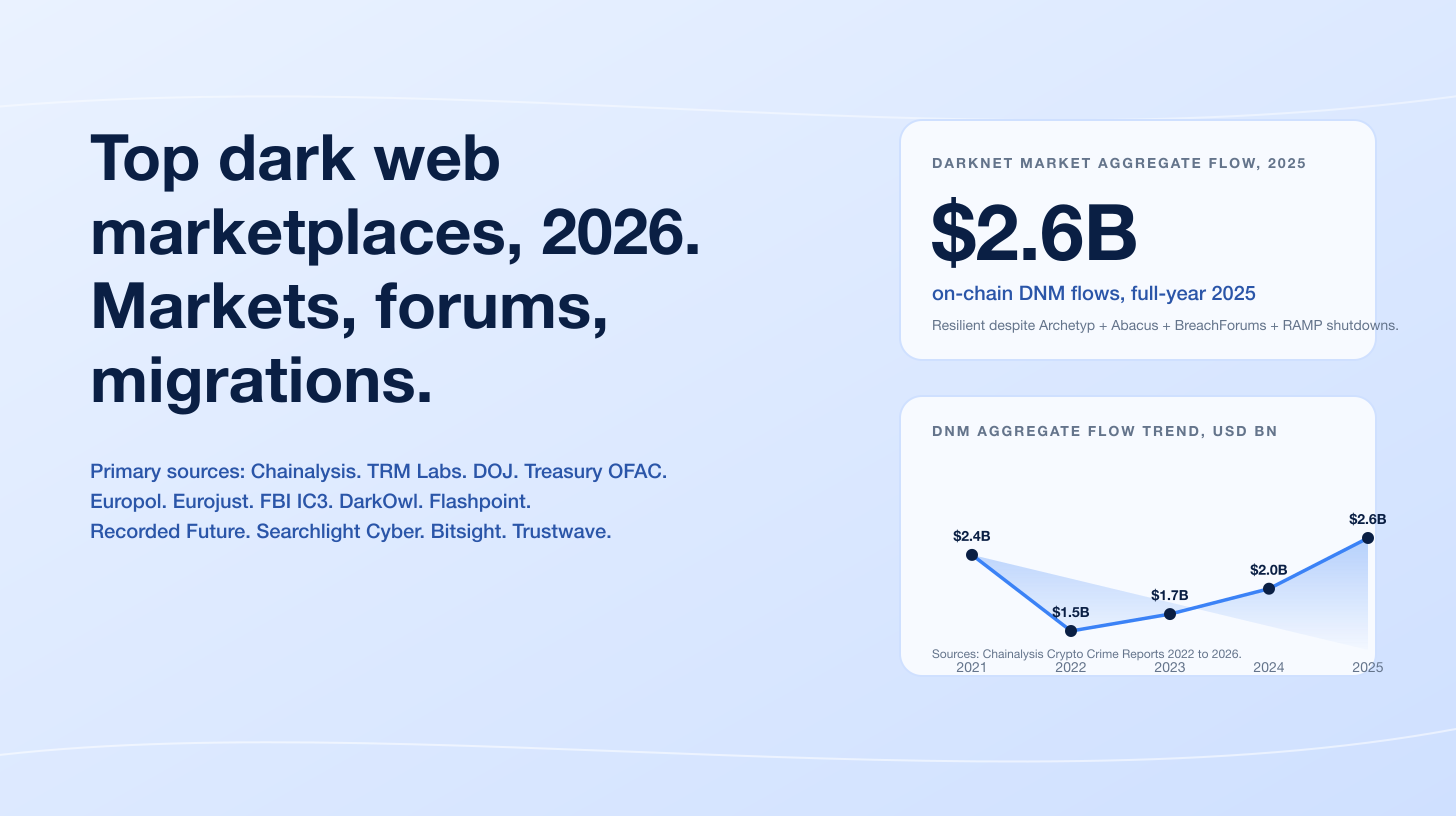
The average organization spent US$17.4 million in 2025 dealing with insider risks, and the 2026 edition of the Ponemon Cost of Insider Risks Global Report puts the same figure at US$19.5 million, a 12% year-over-year climb. Verizon's 2025 Data Breach Investigations Report, which analyzed 12,195 confirmed breaches between November 2023 and October 2024, attributed 30% of breaches to insiders globally, with regional spreads of 29% in EMEA, 5% in North America, and 1% in APAC. IBM's 2025 Cost of a Data Breach Report named malicious insiders the most expensive attack vector overall at US$4.92M per incident, more than half a million dollars above the global average. The insider is no longer a tail-risk talking point; it is the second-most expensive class of breach to live through, behind only nation-state-grade APT activity.
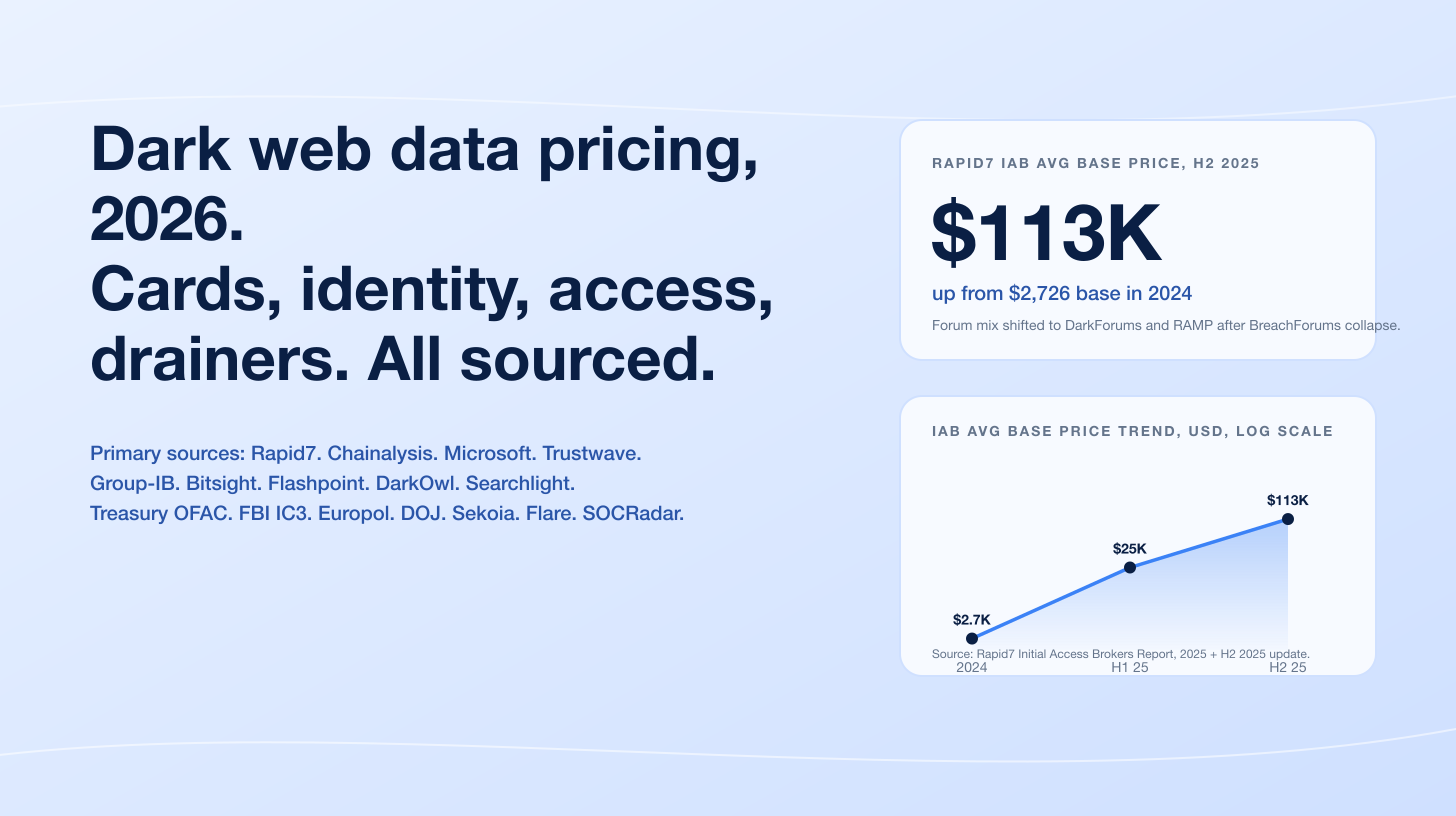
Three forces drove the 2025-2026 picture. Negligent users dominate volume. Ponemon's 2025 report classifies 55% of insider incidents as negligent at an average annual cost of US$8.8M per organization, with malicious actors at 25% (US$3.7M) and credential theft at 20% (US$4.8M) per DTEX's official summary of the Ponemon 2025 findings. DPRK IT-worker infiltration is now the single largest insider-attribution story of the year. CrowdStrike's 2025 Threat Hunting Report measured a 220% year-over-year rise in DPRK-nexus IT-worker activity, Mandiant's M-Trends 2025 reported that fraudulent North Korean IT workers (UNC5267) accounted for 5% of all investigated incidents in 2024, and the DOJ's June 30, 2025 enforcement sweep raided 29 laptop farms across 16 states. AI is the new insider channel. Cyberhaven measured a 30x increase in data sent to generative AI apps in a single year with 22% of files sent containing sensitive corporate information, and Gurucul's 2026 Insider Risk Report found 94% of organizations report AI is increasing exposure. The three forces converge: more access, more concealed access, more places for stolen data to land.
This post is the Stingrai research team's canonical 2026 reference for insider threat statistics. It assembles 75+ verified numeric claims from 22 named primary publishers, including Ponemon Institute (sponsored by DTEX), Verizon, IBM, Mandiant (Google Cloud), Microsoft, CrowdStrike, the U.S. Department of Justice, U.S. Treasury OFAC, FBI IC3, ENISA, CERT/CC at Carnegie Mellon, Cyberhaven, KnowBe4, Gurucul, Coveware (Veeam), Cybersecurity Insiders / Insider Risk Index, EY, Code42 / Mimecast, Securonix, BeyondTrust, Forcepoint, and Anthropic. Lead data is full-year 2024 and 2025 telemetry plus the 2026-edition Ponemon DTEX report and the 2026 Gurucul Insider Risk Report, the freshest available. Many primary publishers have not yet released full-year 2026 data as of April 2026. Every figure carries its source, year, and methodology window so any claim can be audited inline. For complementary identity-side data on stolen credentials, MFA bypass, and infostealer logs, see Stingrai's Compromised Credential Statistics 2026; for upstream phishing telemetry that frequently triggers insider mistakes, see Phishing Statistics 2026; for the workforce supply-side context, see Cybersecurity Skills Gap Statistics 2026.
TL;DR: 12 labeled key stats
Average annual cost of insider risk per organization (2025): US$17.4M (Ponemon 2025 Cost of Insider Risks Global Report, sponsored by DTEX).
2026 update, average annual insider risk cost per organization: US$19.5M, +12% YoY (Ponemon 2026 / DTEX).
Insider share of confirmed breaches (Verizon 2025 DBIR): 30% globally; 29% EMEA, 5% North America, 1% APAC (Verizon 2025 DBIR).
Cost per malicious-insider breach (IBM 2025): US$4.92M, the most expensive attack vector overall (IBM Cost of a Data Breach 2025).
Insider incident mix (Ponemon 2025): negligent 55% (US$8.8M annual), malicious 25% (US$3.7M), credential theft 20% (US$4.8M) (DTEX 2025 takeaways).
Per-incident cost, credential theft (highest of three): US$779,707; malicious US$715,366; negligent US$676,517 (Ponemon 2025).
Mean time to contain an insider incident (2025): 81 days, down from 86 in 2023 (Ponemon 2025).
Containment-time cost gap (2026 DTEX edition): US$14.2M when contained inside 30 days, US$21.9M when containment exceeds 90 days (Kiteworks summary of DTEX 2026).
DPRK IT worker incidents YoY: +220% in the last 12 months, 320+ companies infiltrated (CrowdStrike 2025 Threat Hunting Report); UNC5267 accounted for 5% of all Mandiant-investigated incidents in 2024 (Mandiant M-Trends 2025).
DPRK IT-worker estimated 2024 revenue: nearly US$800M, channeled to weapons programs (DOJ press release, June 30 2025).
DOJ June 2025 enforcement sweep: 29 laptop farms searched across 16 states; 100+ US companies impacted; Christina Chapman sentenced to 102 months for a US$17M Arizona laptop-farm operation that hit 300+ companies (DOJ, July 24 2025).
AI as insider channel: 30x rise in data sent to generative AI apps in 12 months; 22% of uploaded files contain sensitive corporate data; 77% of employees share data with ChatGPT or peers (Cyberhaven 2025). 94% of organizations say AI is increasing insider exposure (Gurucul 2026 Insider Risk Report).
Key takeaways
Insider risk is now an annual nine-figure line item for global enterprises, not a tail-risk talking point. Ponemon priced 2025 at US$17.4M and 2026 at US$19.5M per organization, a 12% YoY climb across the full sample of 1,176 surveyed firms (Ponemon 2025 and Ponemon 2026 / DTEX). North American organizations alone average US$22.2M, with EMEA at US$20.3M.
Negligent users drive volume, but credential theft drives per-event cost. 55% of incidents are negligent (Ponemon 2025), but credential theft costs US$779,707 per incident, the highest of the three categories. The lesson is dual: invest in user-behavior analytics for the long tail of careless data handling and lock down privileged credentials with PAM controls. DTEX's 2026 edition shows privileged access management delivers US$6.1M in annual savings, the single highest control ROI.
Insider activity now blurs into outsider activity through DPRK fake employment. CrowdStrike tracks FAMOUS CHOLLIMA, Mandiant tracks UNC5267, Microsoft tracks Jasper Sleet, and DTEX i3 publishes its own indicator set. Treasury says the scheme generated nearly US$800M in 2024. After the KnowBe4 disclosure in July 2024, the DOJ has moved aggressively, including an indictment of five defendants in January 2025 and a coordinated enforcement sweep on June 30, 2025 that raided 29 laptop farms across 16 states.
Time to contain is the single biggest cost lever. Ponemon shows mean time to contain dropped from 86 days in 2023 to 81 days in 2025. The 2026 DTEX edition shows incidents contained in under 30 days cost US$14.2M while those exceeding 90 days cost US$21.9M. A 60-day reduction in containment time is worth roughly US$8M to the average organization.
Generative AI is creating a new class of unintentional insider. Cyberhaven measured 30x growth in data flowing to GenAI apps year over year, with 22% of files and 4.37% of prompts containing sensitive corporate information. IBM's 2025 CODB found shadow AI added US$670,000 to the average global breach cost and 63% of researched organizations have no AI governance policies in place.
Verizon's 30% insider share is the citation for "how often is insider involvement actually present." Use it for board decks. The Privilege Misuse pattern is 6% of breaches in the 2025 DBIR; Misuse-style activity within insider breaches sits at 8%, while unintentional mistakes account for 19%. The remainder is the Misdelivery / Misconfiguration / Publishing-error long tail.
Methodology
Sources used: Ponemon Institute 2025 Cost of Insider Risks Global Report (sponsored by DTEX, surveyed 1,176 IT and security professionals across 8 country regions, 8,000+ insider incidents, published February 2025); Ponemon 2026 Cost of Insider Risks Global Report (DTEX, published February 2026); Verizon 2025 Data Breach Investigations Report (12,195 confirmed breaches over 22,052 incidents between 1 November 2023 and 31 October 2024, published April 2025); IBM Cost of a Data Breach Report 2025 (600 organizations, breaches between March 2024 and February 2025, published July 2025); Mandiant M-Trends 2025 (Google Cloud frontline incident data, calendar year 2024, published April 2025); Mandiant UNC5267 reporting (Google Cloud blog series, 2024 and 2025); Microsoft Digital Defense Report 2025 (Microsoft threat telemetry July 2024 to June 2025, published October 2025); Microsoft Threat Intelligence Jasper Sleet reporting (Microsoft Security Blog, June 30, 2025 and December 11, 2025); CrowdStrike 2025 Global Threat Report (full-year 2024 incident data, published February 2025) and 2025 Threat Hunting Report (12-month-trailing data through July 2025, published August 2025); CrowdStrike FAMOUS CHOLLIMA tracking; Cyberhaven Insider Risk Report and Cyberhaven 2025 generative-AI insider risk research; KnowBe4 corporate disclosure (July 23, 2024); Gurucul 2026 Insider Risk Report and 2024 Insider Threat Report (published with Cybersecurity Insiders); Coveware Q3 2025 Quarterly Ransomware Report (published October 24, 2025); ENISA Threat Landscape 2025 (4,875 incidents 1 July 2024 to 30 June 2025, published October 2025); CERT Insider Threat Center at Carnegie Mellon University Software Engineering Institute (700+ insider cyber crimes catalogued since 2001); FBI IC3 2024 Internet Crime Report (859,532 complaints, published April 2025); U.S. Department of Justice press releases (January 2025, June 2025, July 2025); U.S. Treasury OFAC sanctions designations (2024 and 2025); Insider Risk Index 2025 / Cybersecurity Insiders 2025 Insider Risk Report; EY 2025 Cybersecurity Study; Code42 / Mimecast Annual Data Exposure Report; Securonix 2024 Insider Threat Report; Anthropic threat reports; and named corporate disclosures for Tesla 2023, Snowflake / UNC5537 2024, KnowBe4 July 2024, and Christina Chapman / Arizona laptop farm 2025.
Date cutoff: April 25, 2026. Stats that could not be verified against a named primary source on at least one verification pass were dropped rather than estimated. Where two reports cover the same metric on overlapping data windows (Ponemon 2025 vs Ponemon 2026), both figures are presented to show YoY trajectory.
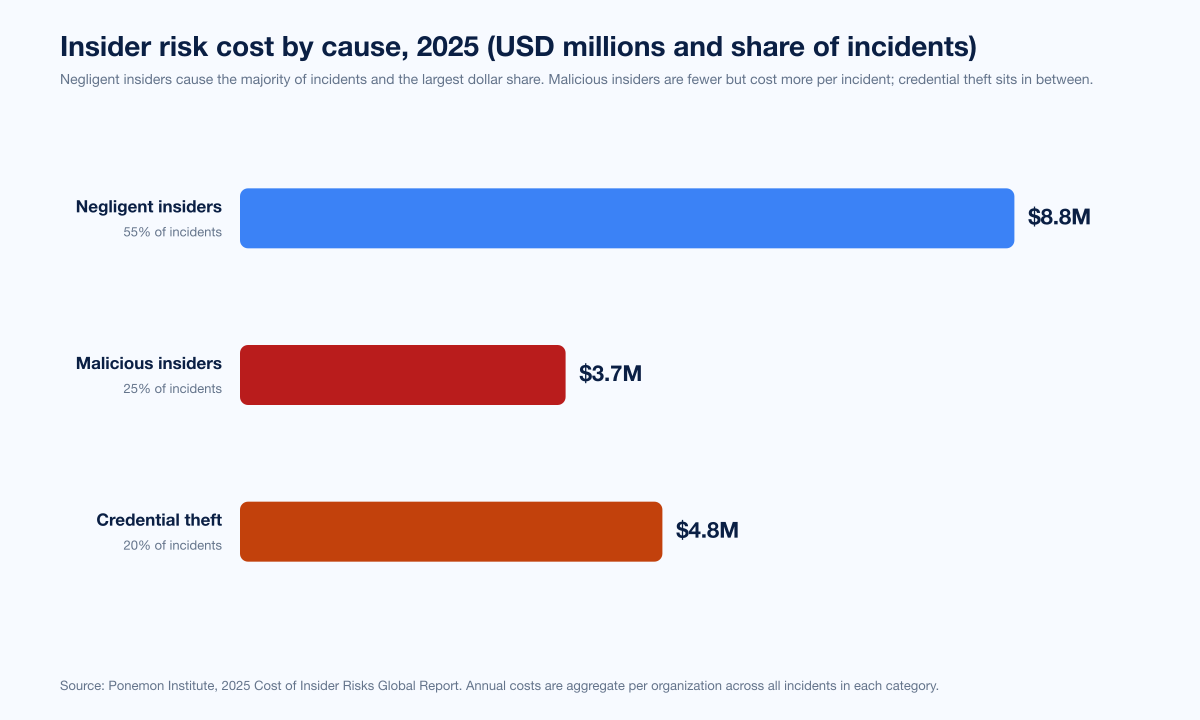
Figure 1: Insider incident mix by cause, share of incidents and average annual cost per organization. Source: Ponemon 2025 Cost of Insider Risks Global Report, summarized by DTEX, March 2025.
How big is the insider threat problem in 2026?
Three datasets anchor the answer, and they line up.
Ponemon 2025 and 2026 (whole-of-program cost lens)
Ponemon's 2025 Cost of Insider Risks Global Report, released in February 2025 in partnership with DTEX Systems, surveyed 1,176 IT and security professionals across 8 country regions and analyzed roughly 8,000 insider incidents. The headline figures:
Metric | 2025 | 2026 (Ponemon DTEX update) | Source |
|---|---|---|---|
Average annual cost per organization | US$17.4M | US$19.5M | Ponemon 2025 / Ponemon 2026 |
North America average | US$22.2M | not yet reported | Ponemon 2025 |
EMEA average | US$20.3M | not yet reported | Ponemon 2025 |
Mean time to contain | 81 days | not yet reported (was 67 days in 2024 update) | Ponemon 2025 |
Negligent insider share of incidents | 55% | 53% | Ponemon 2025 / Ponemon 2026 |
Negligent insider annual cost | US$8.8M | US$10.3M (+17% YoY) | Ponemon 2025 / Ponemon 2026 |
Malicious insider share | 25% | 27% | Ponemon 2025 / Ponemon 2026 |
Malicious insider annual cost | US$3.7M | US$4.7M | Ponemon 2025 / Ponemon 2026 |
Credential theft / outsmarted share | 20% | 20% | Ponemon 2025 / Ponemon 2026 |
Credential theft / outsmarted annual cost | US$4.8M | US$4.5M | Ponemon 2025 / Ponemon 2026 |
IT-security budget share for insider risk programs | 16.5% (up from 8.2% in 2023) | continues climb | Ponemon 2025 |
Organizations with or planning IRM program | 81% | continues climb | Ponemon 2025 |
The 2026 DTEX framing of the 2026 Ponemon edition reports a per-incident cost gap that hits the bottom line directly: incidents contained in under 30 days cost US$14.2M annually; those exceeding 90 days cost US$21.9M (Kiteworks summary of DTEX 2026 Insider Risk Report). Note also that Ponemon spent US$211,021 per insider incident on containment versus US$37,756 on monitoring, an inverted-funnel spending pattern that the 2026 edition explicitly calls out as a missed opportunity.
Verizon 2025 DBIR (actor-attribution lens)
Verizon's 2025 Data Breach Investigations Report is the largest dataset in DBIR history, analyzing 12,195 confirmed data breaches over 22,052 incidents between November 1, 2023 and October 31, 2024. The actor-attribution split for 2025:
Actor | Share of breaches | Source |
|---|---|---|
External actors | 67% | Verizon 2025 DBIR |
Insiders | 30% | Verizon 2025 DBIR |
Partners | 4% | Verizon 2025 DBIR |
Multiple actors | 1% | Verizon 2025 DBIR |
Insider share by region (Verizon 2025 DBIR):
EMEA: 29% of breaches originated from within the organization
North America: 5% from internal actors
APAC: 1% from internal actors
The Privilege Misuse pattern, the closest direct mapping to "intentional malicious insider," accounted for 6% of breaches in the 2025 DBIR, with espionage motivation declining sharply to 10% (from 46% the prior year) and direct financial gain becoming the dominant driver. Within insider breaches specifically, 8% involved misuse (unauthorized use of data violating organizational policies) and 19% were attributed to unintentional mistakes, leaving the residual to Misdelivery, Misconfiguration, and Publishing-error patterns. End-users were 9% of all observed actor varieties and Misdelivery accounted for 72% of End-user actions.
IBM Cost of a Data Breach 2025 (financial-damage lens)
IBM's 2025 Cost of a Data Breach Report, released July 2025 and based on 600 organizations breached between March 2024 and February 2025, gives the per-incident dollars. The headline:
Global average breach cost (all attack vectors): US$4.44M, down 9% YoY from US$4.88M
Mean time to identify and contain (any vector): 241 days (lowest in 9 years)
Malicious insider average breach cost: US$4.92M, the most expensive attack vector overall
Phishing average breach cost: US$4.8M (16% of incidents, second-most expensive)
United States average: more than US$10.2M, more than double the global figure
Healthcare average: US$7.42M, the highest across industries
Shadow AI added cost: US$670,000, per Anti AI Audit
Organizations with no AI governance: 63% of those researched
Malicious-insider breaches do not just have a higher mean dollar cost; they also carry a longer mean time to identify and contain because the attacker has legitimate access. IBM's framing in the 2025 edition is unambiguous: insiders are harder to detect, harder to scope, and harder to remove than any external threat actor.
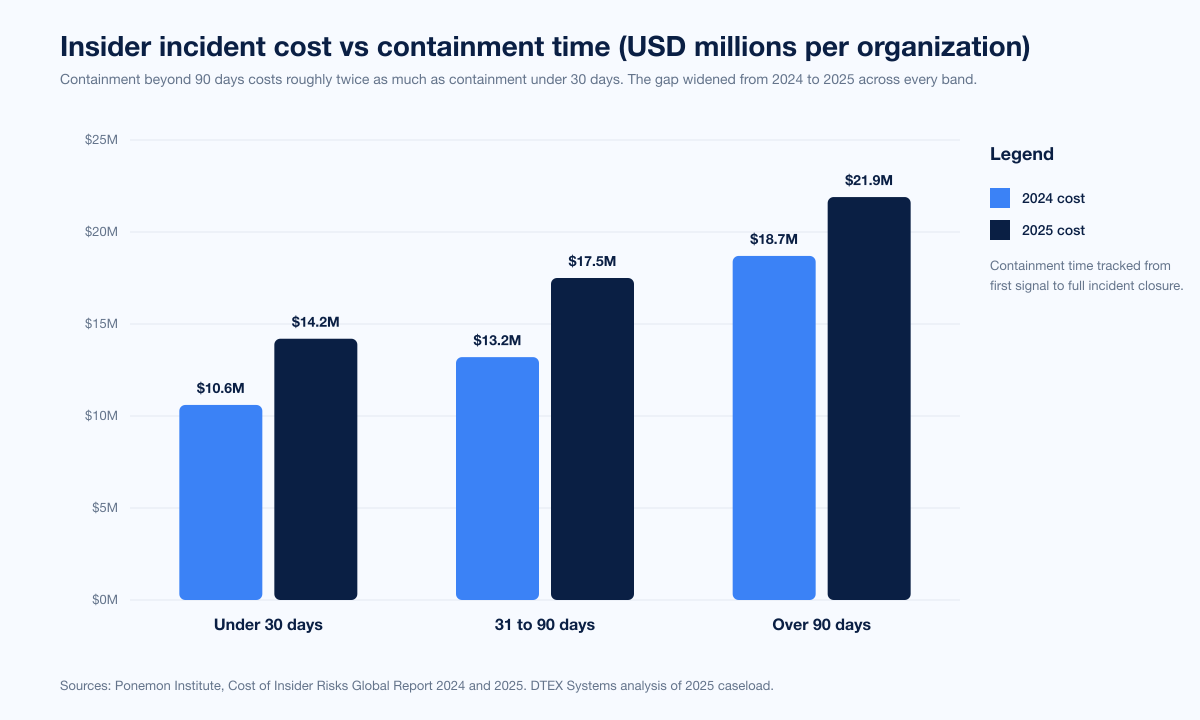
Figure 2: Annual insider risk cost per organization by containment-time bracket. Source: DTEX 2026 Insider Risk Report (Ponemon) and Ponemon 2025 Cost of Insider Risks.
Insider threat by cause: negligent, malicious, credential theft
Negligent insiders dominate volume
Ponemon 2025 classifies 55% of insider incidents as negligent or careless, with an annual cost to organizations of US$8.8M. The 2026 edition holds the share roughly steady at 53% but the annual cost climbs 17% YoY to US$10.3M (DTEX summary). The dominant patterns:
Misdelivered email or file shares
Misconfigured cloud storage (Verizon 2025 DBIR Misconfiguration is now in the top three of Miscellaneous Errors)
Publishing data to the wrong audience (publishing errors moved into the top three)
Accidental copy or paste of sensitive data into a generative-AI tool, the fastest-growing 2025 vector
Cyberhaven's research on AI-driven insider risk measured a 30x increase in data sent to GenAI apps in a single year, with the average organization sharing more than 7.7GB of data with AI tools per month. 22% of files and 4.37% of prompts contained sensitive information, including source code, access credentials, proprietary algorithms, M&A documents, customer or employee records, and internal financial data. Among users who paste to GenAI tools, the average is 6.8 pastes per day, of which more than half (3.8 pastes) include sensitive corporate data. Copy-paste into GenAI is now ranked the single biggest vector for corporate data leaving enterprise control.
Malicious insiders carry the highest per-event dollar cost
Malicious insiders are 25% of incidents per Ponemon 2025 at US$715,366 per incident and US$3.7M annually per organization. The IBM 2025 Cost of a Data Breach Report puts the malicious insider mean breach cost at US$4.92M, the most expensive attack vector overall (IBM CODB 2025). Why so high?
The actor has legitimate access, so the breach takes longer to detect than an external campaign.
The breach often involves intellectual property or regulated data (healthcare, financial services, defense), where regulatory penalties bite.
Containment requires forensic preservation, HR coordination, and often legal action, which costs more than purely technical remediation.
Reputation damage is concentrated. Customers and journalists react more harshly to "rogue employee" stories than to "ransomware actor" stories.
The Tesla insider data theft of 2023 is the canonical recent example. Two former Tesla employees leaked more than 23,000 internal documents containing 100GB of confidential data, including personal information for 75,000+ employees, customer bank details, production secrets, and customer complaints about Full Self-Driving features (TechCrunch). Tesla pursued lawsuits to seize the former employees' devices. The pattern, leaked-to-press over a multi-month exfiltration window, is what every executive-team forensic playbook now anticipates.
Credential theft sits between the two
Ponemon 2025 puts credential theft as the third insider-incident category at 20% of incidents with US$4.8M annual cost and US$779,707 per incident, the highest per-event cost of the three. The 2024 Snowflake / UNC5537 campaign demonstrates the scale: 165 customer organizations were notified by Mandiant, and 79.7% of accounts UNC5537 used had prior credential exposure from infostealers, some dating back to 2020 (Mandiant / Google Cloud). AT&T disclosed nearly 110 million customers impacted in an SEC 8-K on July 12, 2024. The "insider" wasn't a Snowflake employee; it was an external attacker using credentials harvested from infected non-Snowflake endpoints, then deployed against Snowflake without MFA. For credential-theft volume context across the broader 2025 cycle, see Stingrai's Compromised Credential Statistics 2026.
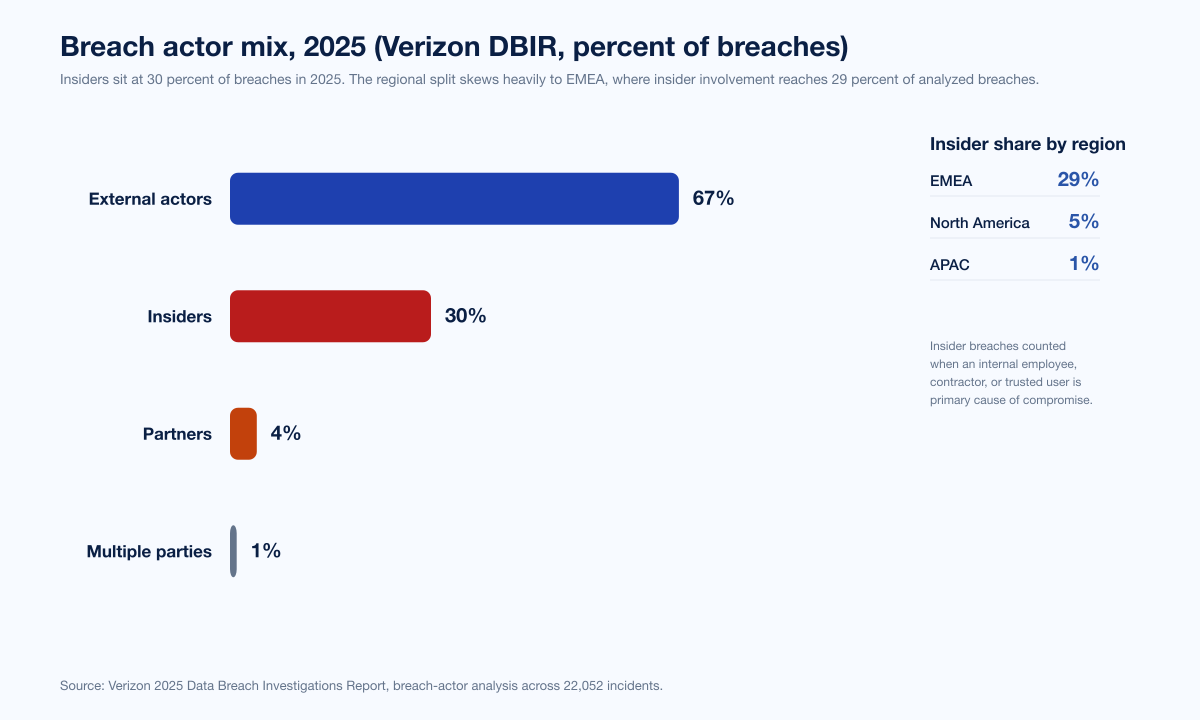
Figure 3: Breach actor mix per Verizon 2025 DBIR. Source: Verizon 2025 Data Breach Investigations Report, 12,195 confirmed breaches November 1, 2023 to October 31, 2024.
Industry exposure: who gets hit hardest
Insider risk concentration tracks IP value and regulatory exposure. DTEX's 2024 i3 Foreign Interference report, based on 1,300+ insider investigations, found:
Sector | IP-theft incident share | Source |
|---|---|---|
Tech | 41% | DTEX i3 2024 |
Pharmaceutical | 20% | DTEX i3 2024 |
Critical infrastructure | 14% | DTEX i3 2024 |
IBM's industry-by-industry breach cost ranking puts healthcare at US$7.42M average breach cost, the highest of any sector for the 14th year running (IBM CODB 2025). Healthcare insider incidents skew toward unauthorized access to medical records, with HHS OCR's breach portal showing 725 healthcare data breaches of 500+ records in 2024 affecting 170 million patient records, though only a minority were attributable directly to insiders.
Financial services and tech see the highest density of malicious-insider IP theft, while government and defense agencies see the highest density of foreign-interference-driven insider activity. DTEX measured a 70% rise in customer demand for foreign-interference protection since 2022 and reported that 77% of sophisticated malicious insiders attempt to conceal their activity to evade detection.
The DPRK IT-worker scheme: the single biggest insider story of 2024 and 2025
This is the largest insider attribution story of the cycle and earns its own deep-dive. The basic structure: skilled North Korean IT workers, operating from China, Russia, and a handful of other locations, apply for fully remote roles at Western (mostly US) companies using stolen identities, AI-altered photos, and laptop-farm proxies. The worker shows up to interviews via deepfake-augmented video, gets hired, has a corporate laptop shipped to a US-based intermediary's house (the "laptop farm"), and works from overseas through KVM-over-IP and remote-management software. They draw a salary, send most of it back to Pyongyang to fund the regime's weapons programs, and frequently exfiltrate IP or extort their employers on the way out.
Scale and attribution
Multiple security vendors track the same activity cluster under different names:
Tracking name | Vendor | Source |
|---|---|---|
FAMOUS CHOLLIMA | CrowdStrike | |
Nickel Tapestry | SecureWorks | Industry tracking |
UNC5267 | Mandiant / Google Cloud | |
Wagemole | Various | Industry tracking |
Jasper Sleet | Microsoft (formerly Storm-0287) |
The 2024-2025 telemetry:
CrowdStrike 2025 GTR: FAMOUS CHOLLIMA was behind 304 incidents in 2024, with 40% involving insider threat operations where adversaries operated under the guise of legitimate employment (CrowdStrike 2025 GTR).
CrowdStrike 2025 Threat Hunting Report: FAMOUS CHOLLIMA infiltrated 320+ companies in the last 12 months, a 220% YoY increase (CrowdStrike 2025 Threat Hunting Report).
Mandiant M-Trends 2025: Fraudulent North Korean IT workers (UNC5267) accounted for 5% of all Mandiant-investigated incidents in 2024, and Mandiant noted late-2024 spikes in extortion attempts by terminated DPRK contractors (Mandiant M-Trends 2025).
Microsoft Threat Intelligence: Microsoft suspended 3,000 known consumer accounts (Outlook / Hotmail) created by North Korean IT workers and rolled detections into Microsoft Entra ID Protection and Microsoft Defender XDR (Microsoft Security Blog, June 30 2025).
DOJ enforcement (June 30 2025): Coordinated nationwide actions including 2 indictments, 1 information and plea agreement, 1 arrest, searches of 29 known or suspected laptop farms across 16 states, and seizure of 29 financial accounts and 21 fraudulent websites. DOJ alleged North Korean IT workers used stolen or fraudulent identities to obtain employment with more than 100 US companies (DOJ press release).
U.S. government 2024 revenue estimate: Nearly US$800 million generated by DPRK IT workers in 2024 (DOJ June 2025).
DPRK regime wage retention: Up to 90% of wages earned by DPRK overseas IT workers are withheld by the government per Mandiant's UNC5267 reporting.
KnowBe4: the canonical disclosure case
KnowBe4's July 23 2024 disclosure is the gold standard for what good catches look like. The candidate passed a multi-stage interview process including background checks, verified references, and four video-conference interviews using a stolen US-based identity and an AI-augmented stock photo. KnowBe4 shipped a corporate Apple laptop to the address provided. Within hours of receipt, the device began loading malware. KnowBe4's EDR caught the activity at 9:55pm EST on July 15, 2024 and shut down the worker's onboarding access within 25 minutes of the first security alert. KnowBe4 then engaged Mandiant and the FBI to corroborate; both confirmed the worker was a North Korean operator. KnowBe4's public write-up explicitly recommends: video-on for full interviews, payment-routing scrutiny, identity verification beyond resume references, and EDR + endpoint baselines from Day 1.
DOJ January 2025 indictment (the US$866K case)
The DOJ January 2025 indictment charged five defendants: two North Korean nationals (Jin Sung-Il and Pak Jin-Song), one Mexican national (Pedro Ernesto Alonso De Los Reyes), and two US nationals (Erick Ntekereze Prince and Emanuel Ashtor). Between April 2018 and August 2024, the defendants and unindicted co-conspirators obtained work from at least 64 US companies, generating at least US$866,255 in revenue from 10 of those companies that the defendants then laundered through a Chinese bank account. Charges include conspiracy to cause damage to a protected computer, conspiracy to commit wire fraud and mail fraud, conspiracy to commit money laundering, and conspiracy to transfer false identification documents. Jin and Pak face additional charges of conspiracy to violate the International Emergency Economic Powers Act. Each faces a maximum penalty of 20 years.
Christina Chapman and the Arizona laptop farm
The most high-profile 2025 sentencing is Christina Chapman, an Arizona woman sentenced on July 24, 2025 to 102 months (8.5 years) in federal prison for assisting North Korean IT workers in obtaining remote positions at 300+ US companies. The scheme generated more than US$17 million in illicit revenue. Between October 2020 and 2023, Chapman:
Operated a "laptop farm" at her home, hosting computers from US companies and deceiving them into believing the work was performed in the US.
Shipped 49 laptops and other devices supplied by US companies to overseas locations, including multiple shipments to a Chinese city on the border with North Korea.
Stole dozens of identities of US citizens for use by North Korean workers.
Companies impacted include a top-five major television network, a Silicon Valley technology company, an aerospace manufacturer, an American carmaker, a luxury retail store, and a US media and entertainment company. Chapman was ordered to forfeit US$284,555.92 that was to be paid to the North Koreans and pay a judgment of US$176,850.
Detection indicators (what actually catches them)
Cross-vendor consensus (Microsoft Jasper Sleet, Mandiant UNC5267, DTEX i3, CrowdStrike Falcon Identity Protection, KnowBe4 case study):
Indicator category | Specific signal | Source |
|---|---|---|
Behavioral | Productivity-masking tools (caffeine.exe, owly, mouse jigglers) | DTEX i3 |
Behavioral | Evidence of multiple remote-management tools installed immediately after laptop shipment | Mandiant UNC5267 |
Behavioral | Spike in impossible-travel alerts in first 30 days post-onboarding | Microsoft Jasper Sleet |
Identity | AI-augmented or stock-photo identity documents reused across personas | Microsoft Jasper Sleet, KnowBe4 |
Identity | Resume inconsistencies, suspicious Zoom backgrounds, time-zone mismatch | DTEX i3, KnowBe4 |
Network | Astrill VPN usage from corporate endpoints | Mandiant UNC5267 |
Network | IP-based KVM device on the corporate laptop | Mandiant UNC5267 |
Endpoint | Authentication secrets saved as plaintext on desktop | DTEX i3 |
Endpoint | EDR detection of malware loading within hours of laptop receipt | KnowBe4 case |
Workforce | Sudden API spikes against Workday Recruiting endpoints from unusual IPs | Microsoft Jasper Sleet |
Mandiant's now-quoted line summarizes the operational reality bluntly: "If you aren't seeing DPRK IT workers in your environment, you just aren't detecting them."
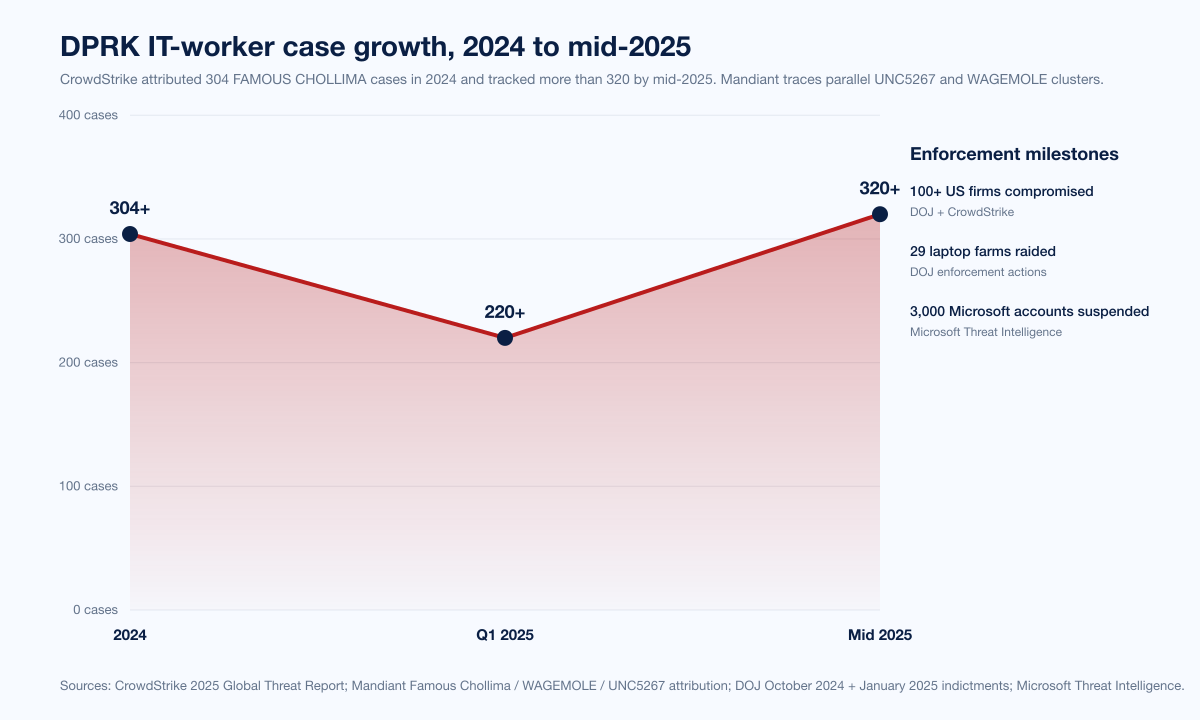
Figure 4: DPRK IT-worker case growth indicators, 2024 to 2025. Sources: CrowdStrike 2025 GTR (FAMOUS CHOLLIMA, 304 cases in 2024), CrowdStrike 2025 Threat Hunting Report (320+ companies, +220% YoY), DOJ June 2025 enforcement sweep, Microsoft Jasper Sleet, June 30 2025.
Insider risk and ransomware: the Coveware Q3 2025 inflection
A new and important wrinkle in 2025: ransomware operators are now actively bribing insiders. Coveware's Q3 2025 report documented Medusa ransomware approaching a BBC employee with a 15% cut of the ransom payment in exchange for network access. Coveware framed it as a structural shift away from the "purely opportunistic" approach that characterized 99% of the ransomware market for years, toward targeted bribery and helpdesk social engineering. Other Q3 2025 figures from Coveware:
Average ransom payment, Q3 2025: US$376,941, down 66% from Q2 2025
Median ransom payment, Q3 2025: US$140,000, down 65%
Median victim company size: 362 employees, up 27% QoQ
Helpdesk social engineering, formerly a Scattered Spider hallmark, is now widely adopted by ransomware affiliates, blurring the boundary between "external attacker" and "social-engineered insider." For broader ransomware data, see Stingrai's Ransomware Payout Statistics 2026.
Generative AI as the new insider channel
The fastest-growing insider risk vector of 2024 and 2025 is unintentional. Cyberhaven's 2025 generative-AI insider research, the most-cited source on the topic, found:
30x increase in data sent to generative AI apps in a single year
77% of employees share sensitive corporate data via ChatGPT or peer GenAI tools
22% of files uploaded to GenAI contain sensitive data, including source code, credentials, M&A documents, customer or employee records, and internal financial data
4.37% of prompts contain sensitive information
Average 6.8 pastes per day per GenAI user, with 3.8 pastes containing sensitive corporate data
Copy/paste into GenAI is now the #1 vector for corporate data leaving enterprise control
IBM's Cost of a Data Breach 2025 priced shadow AI at US$670,000 in additional cost per incident and reported that 63% of researched organizations had no AI governance policies in place to manage worker AI use. Gurucul's 2026 Insider Risk Report found:
90% of organizations experienced at least one insider incident in the past 12 months, more than half costing US$500K+ to remediate
94% of organizations said AI is increasing their exposure to insider threats
The Insider Risk Index 2025 (Cybersecurity Insiders) ranks insider concerns by future driver:
Remote and hybrid work: 75% of security leaders cite as primary driver
AI and automation: 69%
Cloud-based collaboration: 66%
By specific insider risk type, AI-driven phishing and social engineering tops the list at 69% concern, followed by automated data exfiltration (61%), credential abuse (53%), and AI-generated malware (46%). The Insider Risk Index also reports that 72% of security leaders admit they lack full visibility into how users interact with sensitive data across endpoints, SaaS apps, and GenAI tools, and only 18% of organizations have reached Level 3 maturity (unified strategy, cross-functional governance) on a 0 to 3 maturity scale.
Departing-employee data theft: the insider-risk archetype
The departing-employee window remains the highest-leverage moment for insider data theft. Cyberhaven's longitudinal Insider Risk Report, based on 1.4 million workers and 360,000 data exfiltration incidents across 11% of the Fortune 100, established the baseline that insider risk research still cites:
9.4% of employees exfiltrate data over a six-month period (baseline)
+83.1% increased risk in the two weeks before resignation
+23.1% increased risk the day before termination
+109.3% increased risk the day of termination
Top 1% of "super stealers" are responsible for 7.7% of incidents
Top 10% of stealers are responsible for 34.9% of incidents
53.8% of incidents involve data moving 2+ steps before exfiltration
27.5% of incidents: personal cloud storage (Dropbox 44.8% within that)
18.7% of incidents: personal email
Most stolen artifact types: customer lists, source code, financial models, internal strategy documents
DTEX i3's 2024 Foreign Interference data adds nuance for IP-heavy industries: 15% of "leavers" take sensitive IP while 76% take non-proprietary data (industry-norm assets they perceive as theirs). The implication for offboarding policy is direct: monitor data movement in the trailing 30 days before resignation and the 24 hours around termination. Almost all post-termination IP litigation comes from this window.
Detection: what actually catches insiders
DTEX 2026 Insider Risk Report (Ponemon) ranked control effectiveness by annual savings:
Control | Annual savings | Deployment share |
|---|---|---|
Privileged Access Management (PAM) | US$6.1M | not reported |
User and Entity Behavior Analytics (UEBA) | US$5.1M | not reported |
User training and awareness | US$4.8M | 83% (most-deployed) |
SIEM | US$4.6M | not reported |
Notable: user training is the most deployed control by a wide margin (83%) but produces less than half the financial impact of PAM. The 2026 DTEX edition explicitly calls this out as a misallocation of insider-risk spend: most organizations under-invest in privileged-access controls and over-invest in awareness training.
Mandiant M-Trends 2025 reported the global median dwell time across all attack types as 11 days (up slightly from 10 days in 2023, but down from 205 days in 2014). Insider-specific dwell is harder to quantify because the "actor" was already inside, but Mandiant's adversary-notified dwell time of 5 days captures cases where ransomware operators reveal themselves; external-partner-notified dwell averages 26 days, and 45.1% of intrusions are discovered within one week.
ENISA's Threat Landscape 2025 report catalogues a much smaller insider share (0.8% of unauthorized access incidents out of 4,875 EU-tracked incidents) primarily because ENISA's collection methodology weights toward externally observable infrastructure attacks; phishing alone accounted for 60% of observed cases. The takeaway: relative insider share depends entirely on the data window. Verizon's 30% (broad breach attribution) and Ponemon's 100% (insider-only sample) both stand; ENISA's 0.8% reflects a different scope.
For long-running historical context, the CERT Insider Threat Center at Carnegie Mellon University has catalogued 700+ insider cyber crimes since 2001. Its work on the Insider Incident Data Exchange Standard (IIDES), published November 2024, is the academic baseline most insider-risk research uses for behavioral indicators.
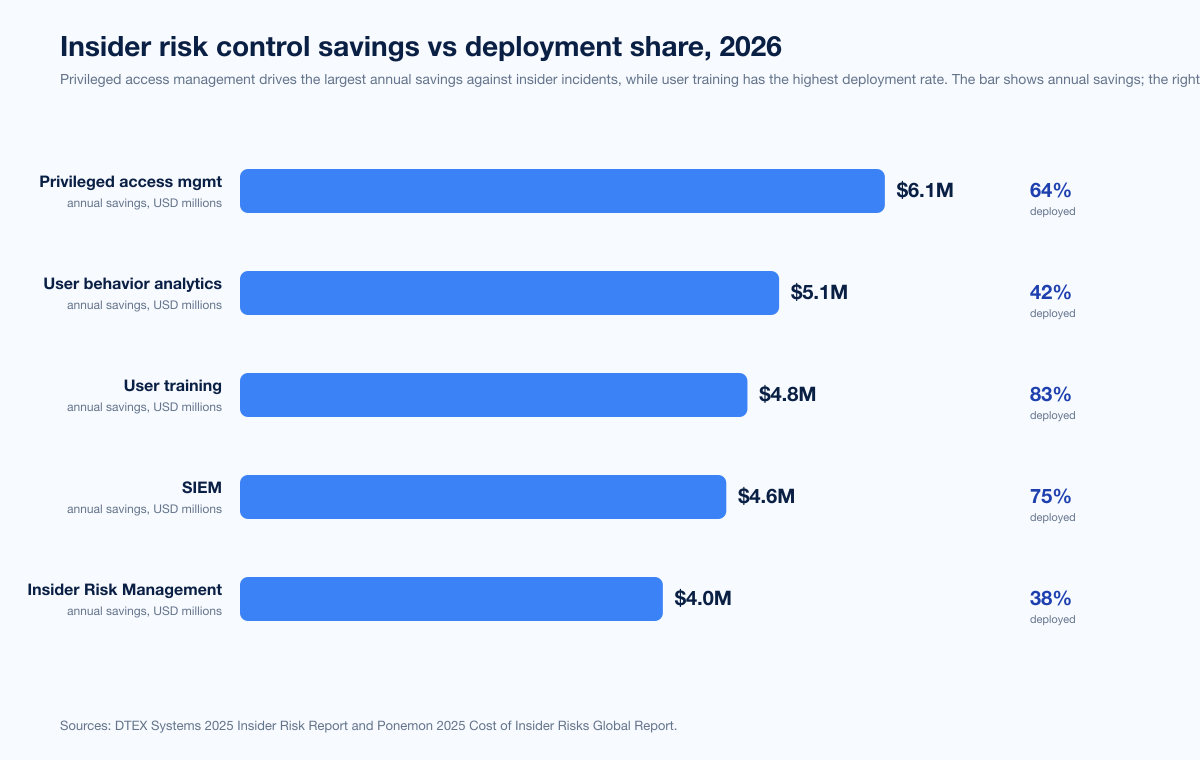
Figure 5: Annual savings by insider-risk control, 2026 DTEX edition. Source: DTEX 2026 Insider Risk Report (Ponemon).
CISO perspective and governance
EY's 2025 Cybersecurity Study measured a stark perception gap: 47% of CISOs say their organization has experienced an insider-driven cybersecurity incident in the past three years, compared with 31% of the rest of the C-suite. This 16-percentage-point gap is the operational reality of insider risk: CISOs see the incident counts; their boards do not.
Also from EY 2025:
84% of C-suite leaders consider cybersecurity investments a cost center
68% of C-suite leaders say their organization prioritizes short-term revenue investments over cybersecurity
46% of CISOs say their operating budget is the same as last year; 39% have an increased budget
The Insider Risk Index 2025 found:
73% of security leaders cite careless, negligent, or uninformed users as the primary insider-risk source
51% of organizations operate at Level 2 maturity (fragmented tools)
18% have reached Level 3 (unified strategy, cross-functional governance)
72% lack full visibility into user data interaction across endpoints, SaaS, and GenAI
Flashpoint's 2025 insider-threat tracking observed 91,321 instances of insider recruiting, advertising, and threat actor discussions involving insider-related illicit activity in 2025, a clear signal that the cybercrime underground actively shops for insiders.
Insider total-cost growth, longitudinal view
Year-over-year growth in insider risk cost has been almost monotonic. The Ponemon Institute (and predecessors) datasets:
Reporting year | Annual cost per organization | Year-over-year change | Source |
|---|---|---|---|
2018 | US$8.3M | baseline | Ponemon historical |
2020 | US$11.5M | +39% (vs 2018) | Ponemon historical |
2022 | US$15.4M | +34% (vs 2020) | Ponemon historical |
2023 | US$16.2M | +5% YoY | Ponemon 2023 |
2025 | US$17.4M | +7.4% YoY | |
2026 | US$19.5M | +12% YoY |
The total average cost of insider threat incidents has increased 109% between 2018 and 2024 (Insider Risk Index 2025 longitudinal analysis). The structural drivers are consistent: more remote work, more SaaS sprawl, more cloud collaboration, more unsanctioned AI tools.
What this means for defenders
The data is unambiguous about where to spend the next dollar.
Lock down privileged access first. PAM delivers US$6.1M in annual savings per the 2026 DTEX edition, the highest-ROI control by a wide margin. Anyone with admin, root, domain controller, cloud-IAM-admin, or git-write-to-protected-branch privileges should be on a just-in-time access workflow with session recording. CrowdStrike's own internal incident data corroborates: most malicious-insider incidents start when an attacker reaches an over-privileged service account.
Operationalize a 30-day departure-monitoring window. Cyberhaven's research is unambiguous: the +83.1% pre-resignation and +109.3% day-of-termination spikes are reproducible across industries. Tag every notice-of-resignation in HRIS, lock down outbound file transfers to personal cloud storage and personal email for that user, and require SOC review of any sensitive-data download in the trailing 30 days.
Stand up a DPRK IT-worker detection playbook now. This is no longer optional for any company hiring remote engineering talent. Mandiant, Microsoft, CrowdStrike, KnowBe4, and DTEX all published detection guidance in 2024 and 2025. The minimum is: video-on full interviews, payment-routing scrutiny against known facilitator accounts, identity-document verification beyond resume references, EDR with day-1 baselines, and impossible-travel monitoring in the first 30 days post-onboarding.
Govern generative AI like you govern SaaS. Cyberhaven's 30x growth and 22% sensitive-file rate, combined with IBM's US$670K shadow-AI cost premium, make the case. Push official AI tools, block unsanctioned ones at the proxy, deploy DLP that inspects GenAI prompts, and run targeted user training that names the specific data classes employees keep pasting.
Validate the controls with adversary simulation. The gap between "we have a control" and "the control catches a determined insider" is wide. Penetration testing engagements that explicitly include departing-employee scenarios, privileged-account-abuse paths, and synthetic-employee onboarding tests are the only way to know your detection actually fires before a US$15M incident does the validation for you. Stingrai runs pentests and adversary simulations with a senior team that has 18 published CVEs and a 5.0/5.0 across 19 Clutch reviews. Our Snipe AI agent carries out continuous testing trained on 6,000+ HackerOne reports, useful when you need detection-tuning runs that exercise insider-style patterns at scale rather than once per year.
Pair the insider-risk picture with credential-side telemetry from Stingrai's Compromised Credential Statistics 2026, the upstream phishing volume from Phishing Statistics 2026, and the workforce-side context from Cybersecurity Skills Gap Statistics 2026.
Frequently asked questions
What is the average cost of an insider threat in 2026?
The average annual cost of insider risk per organization is US$19.5M in the 2026 Ponemon DTEX edition, up 12% YoY from US$17.4M in Ponemon 2025. On a per-incident basis, IBM's Cost of a Data Breach 2025 prices a malicious-insider-driven breach at US$4.92M, the most expensive attack vector overall. Per-incident insider costs across all categories range from US$676,517 (negligent) to US$779,707 (credential theft), per Ponemon 2025.
What percentage of breaches are caused by insiders?
Verizon's 2025 Data Breach Investigations Report, analyzing 12,195 confirmed breaches between November 2023 and October 2024, attributes 30% of breaches to insiders globally, with regional variation: 29% in EMEA, 5% in North America, and 1% in APAC. The Privilege Misuse pattern alone, the closest direct mapping to "intentional malicious insider," is 6% of all breaches. Within insider breaches specifically, 8% involve misuse and 19% involve unintentional mistakes; the rest are Misdelivery, Misconfiguration, and Publishing-error patterns.
Which type of insider is most expensive?
By per-event cost, credential theft is the most expensive at US$779,707 per incident (Ponemon 2025). By annual cost to the organization, malicious insiders are most expensive at US$4.92M per breach (IBM CODB 2025). By share of incidents, negligent insiders are the largest category at 55% (Ponemon 2025), but their per-event cost is the lowest of the three.
Who are FAMOUS CHOLLIMA, UNC5267, and Jasper Sleet?
These are different vendor names for the same activity cluster: North Korean IT workers using stolen identities and AI-altered photos to obtain remote employment at Western (mostly US) companies. CrowdStrike tracks them as FAMOUS CHOLLIMA, Mandiant as UNC5267 (also Wagemole, Nickel Tapestry), and Microsoft as Jasper Sleet (formerly Storm-0287). CrowdStrike's 2025 Threat Hunting Report measured a 220% YoY rise in FAMOUS CHOLLIMA insider operations and 320+ companies infiltrated. Mandiant's M-Trends 2025 reports UNC5267 accounted for 5% of all investigated incidents in 2024.
How much money does the DPRK IT-worker scheme generate?
The U.S. government estimates DPRK IT workers generated nearly US$800 million in 2024, with proceeds funding the regime's weapons programs (DOJ press release, June 30 2025). The DPRK government withholds up to 90% of overseas worker wages per Mandiant's UNC5267 reporting.
What was the KnowBe4 fake IT worker case?
In July 2024, KnowBe4 disclosed hiring a North Korean IT worker who passed a multi-stage interview process using a stolen US-based identity and an AI-augmented stock photo. KnowBe4's EDR caught suspicious activity at 9:55pm EST on July 15, 2024, within hours of the corporate laptop being shipped, and contained the incident within 25 minutes of the first alert. KnowBe4 then engaged Mandiant and the FBI to corroborate. The case became the canonical "what good detection looks like" reference for hiring-side insider risk.
How long does it take to contain an insider threat?
Ponemon 2025 puts the mean time to contain an insider incident at 81 days, down from 86 days in 2023. IBM's 2025 Cost of a Data Breach Report reports a 241-day mean time to identify and contain across all attack vectors. Containment time has a direct cost impact: DTEX 2026 shows incidents contained within 30 days cost US$14.2M annually while those exceeding 90 days cost US$21.9M.
Are AI tools causing more insider incidents?
Yes, by a significant margin. Cyberhaven's research measured a 30x increase in data sent to generative AI apps in a single year, with 22% of files and 4.37% of prompts containing sensitive data. 77% of employees share sensitive corporate data via AI tools. IBM 2025 reports shadow AI added US$670,000 to the average breach cost and 63% of organizations have no AI governance policies. Gurucul's 2026 Insider Risk Report found 94% of organizations said AI is increasing their insider exposure.
Which industries face the highest insider risk?
DTEX i3 2024 found tech (41%), pharmaceutical (20%), and critical infrastructure (14%) had the highest IP-theft incident shares. By breach cost, IBM 2025 ranks healthcare highest at US$7.42M per breach (14th consecutive year). Financial services and tech see the highest density of malicious-insider IP theft; government and defense agencies see the highest density of foreign-interference-driven activity.
What are the best controls against insider threats?
By annual savings per DTEX 2026: Privileged Access Management (US$6.1M), User and Entity Behavior Analytics (US$5.1M), User training (US$4.8M), and SIEM (US$4.6M). User training is the most-deployed control at 83% adoption but produces less than half the financial impact of PAM. Operationally, the highest-leverage moves are: just-in-time PAM with session recording, 30-day departing-employee monitoring, DPRK detection playbooks for remote-hiring pipelines, GenAI DLP, and adversary simulation that exercises insider scenarios.
What does the CERT Insider Threat Center at Carnegie Mellon track?
Since 2001, CERT/CC at Carnegie Mellon University's Software Engineering Institute has catalogued 700+ insider cyber crimes, ranging from national-security espionage to trade-secret theft. CERT publishes the Insider Incident Data Exchange Standard (IIDES, November 2024) and the canonical "Critical Pathway to Insider Risk" academic framework, both widely used by enterprise insider-risk programs. CERT's work is the academic baseline behind most behavioral-indicator insider tooling.
Where can I get the latest insider threat data?
The primary publishers to track are Ponemon Institute (annual Cost of Insider Risks Global Report, sponsored by DTEX), Verizon (annual Data Breach Investigations Report), IBM (annual Cost of a Data Breach Report), Mandiant / Google Cloud (annual M-Trends), Microsoft (annual Digital Defense Report and ad-hoc Threat Intelligence blogs), CrowdStrike (annual Global Threat Report and Threat Hunting Report), DTEX Systems (i3 Insider Risk Investigations Reports), Cyberhaven (insider-risk and AI-insider research), Gurucul and Cybersecurity Insiders (annual Insider Risk Report), Coveware (quarterly ransomware reports, includes insider involvement), ENISA (annual Threat Landscape), CERT/CC at Carnegie Mellon (academic framework and incident corpus), FBI IC3 (annual Internet Crime Report), and U.S. Department of Justice / Treasury OFAC for indictments and sanctions designations.
References
Ponemon Institute (sponsored by DTEX Systems). 2025 Cost of Insider Risks Global Report. February 2025. https://ponemon.dtexsystems.com/. Surveyed 1,176 IT and security professionals across 8 country regions; analyzed roughly 8,000 insider incidents; the canonical insider-risk cost benchmark.
Ponemon Institute (sponsored by DTEX Systems). 2026 Cost of Insider Risks Global Report. February 2026. https://ponemon.dtex.ai/. 2026 update; per-organization annual cost reaches US$19.5M.
DTEX Systems. 2025 Cost of Insider Risks Takeaways. March 2025. https://www.dtexsystems.com/blog/2025-cost-insider-risks-takeaways/. Vendor summary of Ponemon 2025 with breakdowns by incident type and containment time.
Kiteworks (summarizing DTEX 2026 Insider Risk Report). The Threat Is Already Inside. February 2026. https://www.kiteworks.com/cybersecurity-risk-management/dtex-2026-insider-threat-report-data-security-compliance-findings/. Reports US$14.2M vs US$21.9M cost-by-containment-time gap.
Verizon Business. 2025 Data Breach Investigations Report. April 2025. https://www.verizon.com/business/resources/T16f/reports/2025-dbir-data-breach-investigations-report.pdf. 12,195 confirmed breaches across 22,052 incidents; 30% insider attribution.
IBM Security. Cost of a Data Breach Report 2025. July 2025. https://www.ibm.com/reports/data-breach. 600 organizations breached March 2024 to February 2025; malicious insider US$4.92M per incident.
Mandiant (Google Cloud). M-Trends 2025. April 2025. https://cloud.google.com/blog/topics/threat-intelligence/m-trends-2025. UNC5267 accounted for 5% of all investigated incidents in 2024; 11-day median dwell time.
Mandiant (Google Cloud). Staying a Step Ahead: Mitigating the DPRK IT Worker Threat. 2024 to 2025. https://cloud.google.com/blog/topics/threat-intelligence/mitigating-dprk-it-worker-threat. UNC5267 / Famous Chollima / Wagemole tracking.
Mandiant (Google Cloud). UNC5537 Targets Snowflake Customer Instances for Data Theft and Extortion. June 2024. https://cloud.google.com/blog/topics/threat-intelligence/unc5537-snowflake-data-theft-extortion. 165 Snowflake customer instances notified; 79.7% had prior credential exposure.
CrowdStrike. 2025 Global Threat Report. February 2025. https://www.crowdstrike.com/en-us/press-releases/crowdstrike-releases-2025-global-threat-report/. FAMOUS CHOLLIMA: 304 incidents in 2024, 40% involved insider threat operations.
CrowdStrike. 2025 Threat Hunting Report: AI Becomes a Weapon and a Target. August 2025. https://www.crowdstrike.com/en-us/blog/crowdstrike-2025-threat-hunting-report-ai-weapon-target/. 320+ companies infiltrated by FAMOUS CHOLLIMA; +220% YoY.
Microsoft Threat Intelligence. Jasper Sleet: North Korean Remote IT Workers' Evolving Tactics to Infiltrate Organizations. June 30, 2025. https://www.microsoft.com/en-us/security/blog/2025/06/30/jasper-sleet-north-korean-remote-it-workers-evolving-tactics-to-infiltrate-organizations/. 3,000 consumer accounts suspended; AI face-swap detection.
Microsoft Corporation. Microsoft Digital Defense Report 2025. October 2025. https://www.microsoft.com/en-us/security/security-insider/threat-landscape/microsoft-digital-defense-report-2025. North Korea remote-worker section; 15.9B account creation requests in H1 2025, 90%+ from bots.
U.S. Department of Justice. Justice Department Announces Coordinated, Nationwide Actions to Combat North Korean Remote IT Workers. June 30, 2025. https://www.justice.gov/opa/pr/justice-department-announces-coordinated-nationwide-actions-combat-north-korean-remote. 29 laptop farms searched, 100+ US companies hit, US$800M 2024 estimate.
U.S. Department of Justice. Arizona Woman Sentenced for US$17M Information Technology Worker Fraud Scheme. July 24, 2025. https://www.justice.gov/opa/pr/arizona-woman-sentenced-17m-information-technology-worker-fraud-scheme-generated-revenue. Christina Chapman 102-month sentence; 300+ US companies impacted.
The Hacker News (citing DOJ). DoJ Indicts 5 Individuals for US$866K North Korean IT Worker Scheme Violations. January 2025. https://thehackernews.com/2025/01/doj-indicts-5-individuals-for-866k.html. January 2025 indictment of Jin, Pak, Alonso, Prince, and Ashtor.
KnowBe4. How a North Korean Fake IT Worker Tried to Infiltrate Us. July 23, 2024. https://blog.knowbe4.com/how-a-north-korean-fake-it-worker-tried-to-infiltrate-us. Canonical disclosure case study.
Cyberhaven. Insider Risk Report: The Great Data Heist. 2022, ongoing updates. https://www.cyberhaven.com/resources/report/insider-risk-report-great-data-heist. Departing-employee data theft baseline.
Cyberhaven. AI Insider Threats: Generative AI Data Leak Risks (2025). 2025. https://www.cyberhaven.com/blog/insider-threats-in-the-age-of-ai. 30x growth in data to GenAI; 22% of files contain sensitive data.
DTEX Systems. Countering Foreign Interference: 2024 Insider Risk Investigations Report (i3). April 2024. https://www.dtexsystems.com/blog/countering-foreign-interference-2024-insider-risk-report-takeaways/. 1,300+ insider investigations; tech 41% of IP-theft incidents.
Gurucul (with Cybersecurity Insiders). 2026 Insider Risk Report: AI Is the New Insider Threat. March 2026. https://www.prnewswire.com/news-releases/gurucul-research-demonstrates-ai-is-the-new-insider-threat-as-90-of-organizations-experience-incidents-302716883.html. 90% incident rate, 94% AI exposure.
Gurucul. 2024 Insider Threat Report. September 2024. https://gurucul.com/blog/insider-threat-report/. 83% of organizations had at least one insider attack.
Coveware (Veeam). Insider Threats Loom while Ransom Payment Rates Plummet (Q3 2025). October 24, 2025. https://www.coveware.com/blog/2025/10/24/insider-threats-loom-while-ransom-payment-rates-plummet. Medusa 15% bribe offer; ransomware-insider blur.
FBI Internet Crime Complaint Center. 2024 Internet Crime Report. April 2025. https://www.ic3.gov/AnnualReport/Reports/2024_IC3Report.pdf. US$16.6B total cybercrime losses; 64,882 personal data breaches at US$1.45B losses.
ENISA (European Union Agency for Cybersecurity). Threat Landscape 2025. October 2025. https://www.enisa.europa.eu/sites/default/files/2025-11/ENISA%20Threat%20Landscape%202025.pdf. 4,875 incidents 1 July 2024 to 30 June 2025; insider threats 0.8% of unauthorized access.
CERT Insider Threat Center, Carnegie Mellon University Software Engineering Institute. Insider Threat Center: Research, Database, and Frameworks. Ongoing. https://www.sei.cmu.edu/insider-threat/. 700+ insider cyber crimes catalogued since 2001.
EY. 2025 Cybersecurity Study: Bridging the C-suite Disconnect. 2025. https://www.ey.com/en_us/ciso/cybersecurity-study-c-suite-disconnect. CISO insider-perception gap (47% vs 31%).
Cybersecurity Insiders / Insider Risk Index. 2025 Insider Threat Intelligence Report. 2025. https://www.insiderisk.io/research/insider-threat-trends-2025. Maturity-level breakdown, future driver concerns.
Flashpoint. Insider Threats: Turning 2025 Intelligence into a 2026 Defense Strategy. 2026. https://flashpoint.io/blog/insider-threats-2025-intelligence-2026-strategy/. 91,321 insider-recruiting instances tracked in 2025.
TechCrunch. Tesla says data breach impacting 75,000 employees was an insider job. August 21, 2023. https://techcrunch.com/2023/08/21/tesla-breach-employee-insider/. Tesla insider data theft.
Cybersecurity Dive. AT&T cyberattack hit roughly 110 million customers via Snowflake environment. July 2024. https://www.cybersecuritydive.com/news/att-cyberattack-snowflake-environment/721235/. AT&T SEC 8-K disclosure.
Dark Reading. Mimecast Joins Human Risk Management Fray With Code42 Deal. July 2024. https://www.darkreading.com/insider-threats/mimecast-joins-human-risk-management-fray-with-code42-deal. Code42 / Mimecast US$15M average insider incident framing.
The Record from Recorded Future News. DOJ raids 29 'laptop farms' in operation against North Korean IT worker scheme. June 2025. https://therecord.media/doj-raids-laptop-farms-crackdown. Coverage of June 2025 enforcement sweep.
U.S. Department of the Treasury. Treasury Sanctions Facilitators of DPRK IT Worker Fraud Targeting U.S. Businesses. 2025. https://home.treasury.gov/news/press-releases/sb0416. OFAC designations of DPRK IT-worker facilitators.