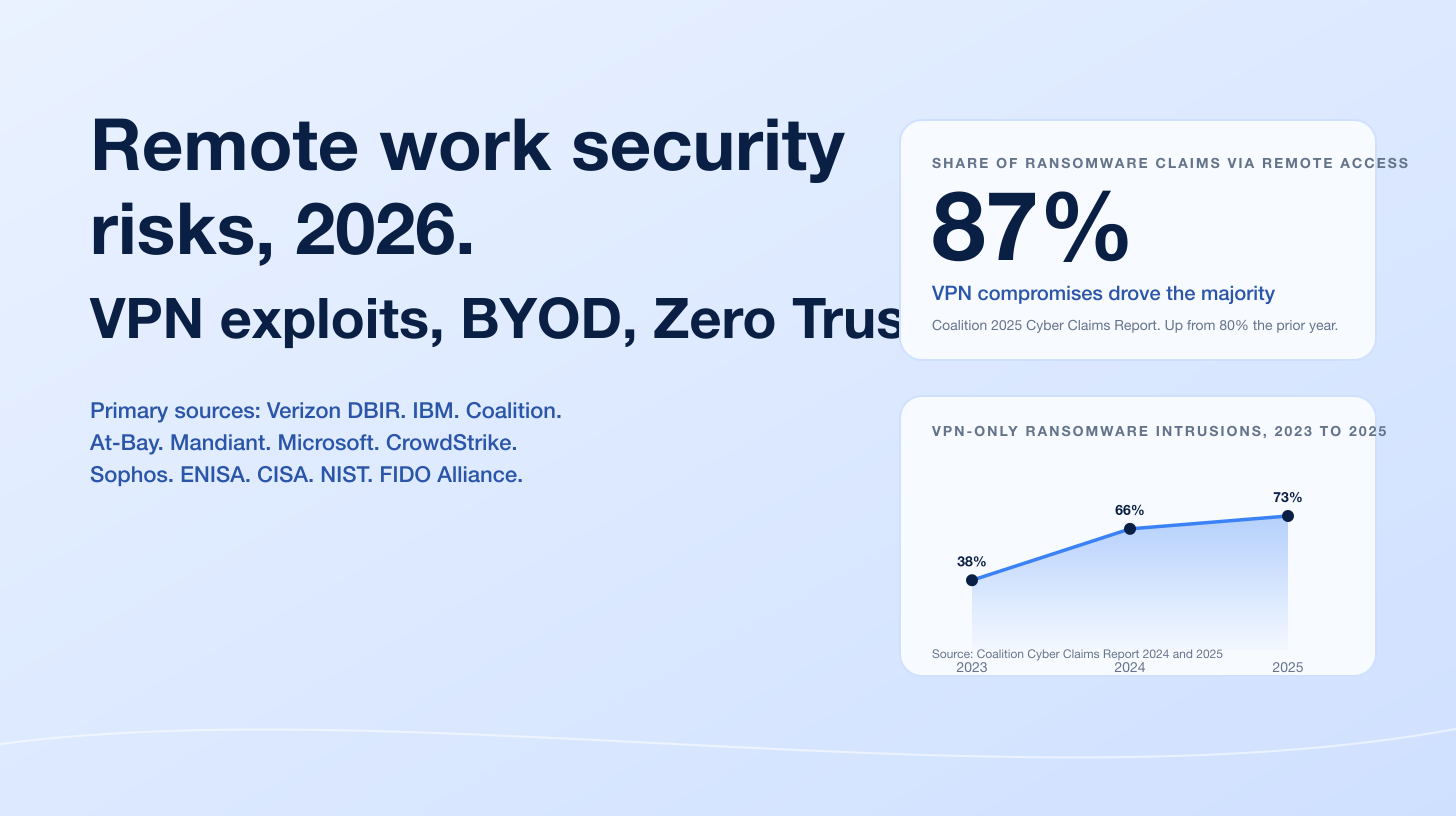
The defining 2026 social engineering number is not a single dollar figure. It is a baseline. The Verizon 2025 Data Breach Investigations Report, based on 22,052 incidents and 12,195 confirmed breaches, finds that approximately 60% of breaches involved a human action: a malicious click, a socially engineered call, a misdelivered file. Within social engineering specifically, phishing accounts for 57% of incidents and pretexting for 30%, with prompt-bombing emerging at 14%. Pretexting incidents at the core of business email compromise have nearly doubled and now account for over 50% of all social engineering incidents. The IBM 2025 Cost of a Data Breach Report ranks phishing the most common initial attack vector at 16% of breaches with a US$4.8M average cost, and now finds 1 in 6 (16%) breaches involve attacker AI, with AI-generated phishing (37%) and deepfake impersonation (35%) the dominant tactical use cases. The human layer is still the dominant attack surface in 2026.
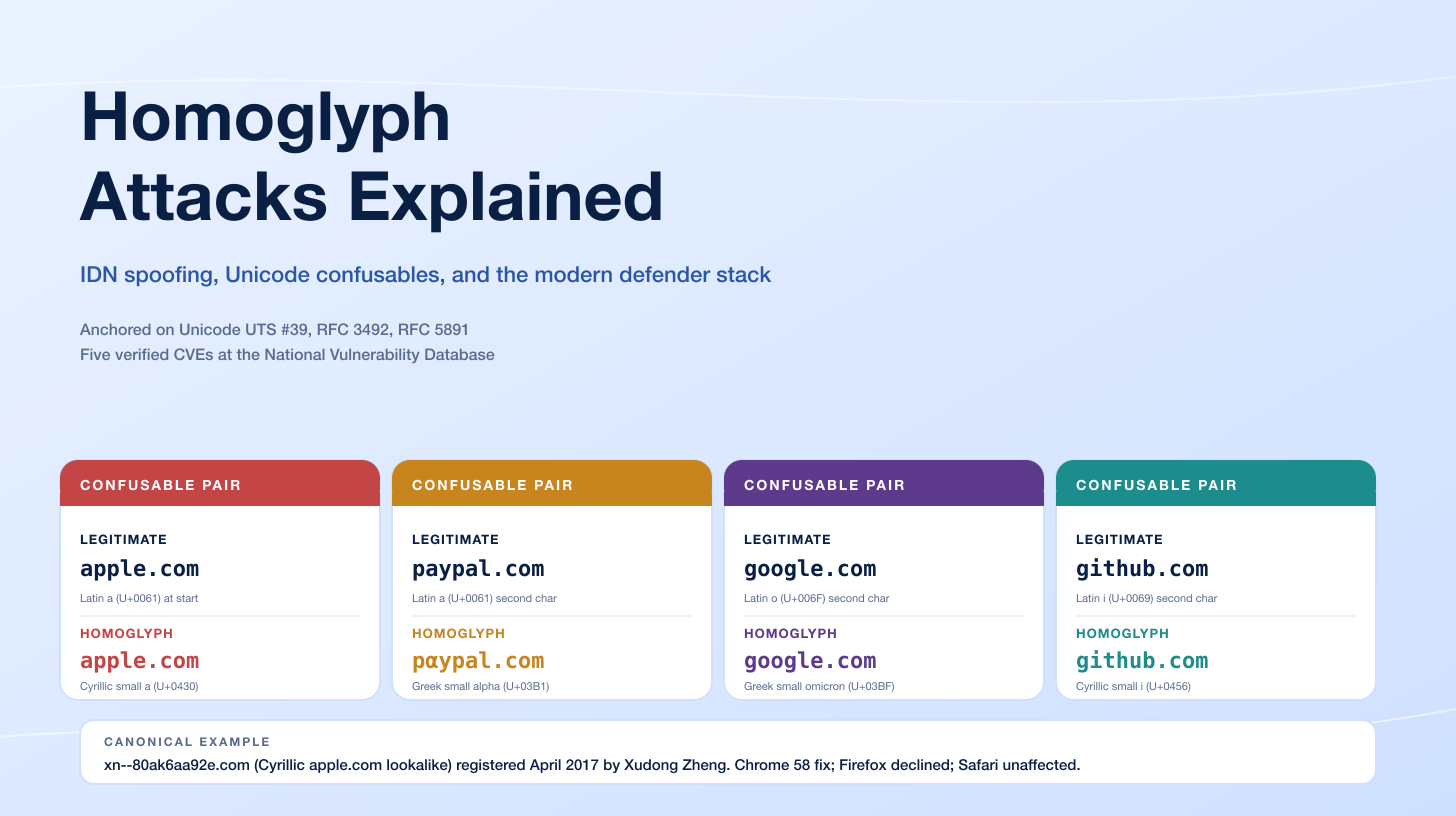
Three forces drive 2026 social engineering activity. AI is now the default lure factory. ENISA's 2025 Threat Landscape, analyzing roughly 4,900 incidents from July 2024 to June 2025, found that AI-supported phishing campaigns represent more than 80% of observed social engineering activity worldwide by early 2025, with phishing the dominant intrusion vector at about 60% of EU initial-access cases. Voice fraud has industrialized. CrowdStrike measured vishing growing 442% between H1 and H2 2024 with a 40% compounded monthly growth rate, and the 2025 Threat Hunting Report reported H1 2025 already exceeded full-year 2024 volume. Pindrop, analyzing 1.2B+ contact-center calls, recorded a 1,300% YoY rise in deepfake fraud attempts, jumping from one per month to seven per day. And session-token theft killed easy MFA. Microsoft's Digital Defense Report 2025 attributes 80% of MFA-bypass breaches to AiTM session-token theft, with the Tycoon2FA kit accounting for ~62% of all phishing blocked by Microsoft by mid-2025 before its March 2026 takedown.
This post is the Stingrai research team's canonical 2026 umbrella reference for social engineering. It assembles 100+ numeric claims from 30 named primary publishers, including Verizon DBIR, IBM Cost of a Data Breach, FBI IC3, FTC Consumer Sentinel Network, CrowdStrike Global Threat Reports 2025 and 2026, Microsoft Digital Defense Report 2025, Mandiant M-Trends 2026, ENISA Threat Landscape 2025, APWG, KnowBe4, Cofense, Mimecast, Hornetsecurity, Barracuda, Proofpoint, Pindrop, Sumsub, iProov, NCSC UK, Cisco Talos, NCC Group, Anthropic Threat Intelligence, the World Economic Forum Global Cybersecurity Outlook 2026, and named corporate-incident records (Arup, WPP, Ferrari, KnowBe4). Lead data is full-year 2024 and full-year 2025 telemetry, the freshest available; primary publishers have not yet released full-year 2026 reports as of April 2026. Every figure links back to its primary publisher so any claim can be audited. Sub-cluster posts are linked inline for deep-dive coverage of phishing, deepfakes, SIM swap, insider threats, AI cyber attacks, and compromised credentials.
TL;DR: 12 labeled key stats
Share of breaches involving the human element (2025): ~60% (Verizon 2025 DBIR).
Phishing share of social engineering incidents: 57% (Verizon 2025 DBIR).
Pretexting share of social engineering incidents: 30% (over 50% counting BEC core) (Verizon 2025 DBIR).
Phishing share of breach initial-access vectors: 16% (IBM Cost of a Data Breach 2025).
IBM phishing-driven breach average cost: US$4.8M (IBM CODB 2025).
Breaches involving attacker AI: 16% (1 in 6); within those, AI phishing 37%, deepfake impersonation 35% (IBM CODB 2025).
FBI IC3 BEC losses 2024: US$2.77B across 21,442 incidents (FBI IC3 2024).
FBI IC3 phishing complaints 2024: 193,407 (most-reported cybercrime) (FBI IC3 2024).
AI-supported share of social engineering globally: more than 80% by early 2025 (ENISA Threat Landscape 2025).
Vishing growth (H1 to H2 2024): +442%; H1 2025 already exceeded full-year 2024 (CrowdStrike 2025 GTR + 2025 Threat Hunting Report).
APWG phishing attacks Q4 2025: 853,244 (Q2 2025 peak: 1,130,393, largest quarter since Q2 2023) (APWG Q4 2025).
KnowBe4 12-month training reduction: baseline 33.1% to 4.1% Phish-prone Percentage (86% reduction) (KnowBe4 2025 PIB).
Key takeaways
The human element is still the load-bearing surface. Verizon's 60% human-action share has held essentially steady across multiple DBIR cycles. AI is making the existing attack categories faster and more credible, not replacing them.
AI augmentation is now the default for social engineering. ENISA's 80%+ share, KnowBe4's 82.6% AI-content rate in late-2024 to early-2025 phishing emails, and CrowdStrike's 4.5x click-rate uplift for AI-generated lures all point one way. Treat training and detection assumptions about "obvious" AI-generated content as out of date.
Voice fraud has gone industrial. CrowdStrike's 442% vishing growth, H1 2025 exceeding full-year 2024, and Pindrop's 1,300% deepfake-fraud surge in contact centers are too much volume to defend with manual controls. Out-of-band callback verification and active voice-deepfake detection are now the price of admission.
AiTM phishing kits hollowed out MFA's easy wins. Microsoft's 80% MFA-bypass attribution to AiTM, Tycoon2FA's 62% share of MS-blocked phishing, and the March 2026 takedown together bracket what defenders need to assume: text-message and OTP-based MFA is now compromised by default. Phishing-resistant authentication (FIDO2 / WebAuthn passkeys + device-bound credentials) is the floor.
Defender-side training works, but only if it's relentless. KnowBe4's 86% reduction is real, but it requires 12 months of sustained training. The 21-second median time-to-click means a single missed lure converts before a well-trained user has time to think. Layer training with AiTM-resistant authentication and out-of-band verification for high-value actions.
Methodology
Date cutoff: April 29 2026. Lead data is full-year 2024 or 2025 telemetry where a primary publisher has released it; 2026 figures are labeled as forecasts or projections. Statistics that could not be reached via a named primary source on at least one verification pass were dropped rather than estimated. Where multiple primary publishers report compatible figures we cite the publisher whose methodology window matches the claim. Secondary news aggregators are cited only where they constitute the public record of a corporate incident.
Sources span: Verizon Data Breach Investigations Report 2025 (22,052 incidents); IBM Cost of a Data Breach Report 2025 (600+ orgs); FBI Internet Crime Complaint Center 2024 Internet Crime Report (859,532 complaints) plus the 2024 Elder Fraud Report; FTC Consumer Sentinel Network 2024 Data Book (6.5M reports); APWG Phishing Activity Trends Reports Q1 to Q4 2025; Microsoft Digital Defense Report 2025 plus the Tycoon2FA disruption blog (March 2026); CrowdStrike 2025 + 2026 Global Threat Reports and 2025 Threat Hunting Report; Mandiant M-Trends 2026 (~450,000 IR hours); ENISA Threat Landscape 2025 (4,875 incidents); World Economic Forum Global Cybersecurity Outlook 2026; KnowBe4 2025 Phishing By Industry Benchmarking Report (14.5M users) plus the 2025 Phishing Threat Trends Report; Cofense Annual State of Email Security 2026; Mimecast 2025 Global Threat Intelligence Report (24T+ data points); Hornetsecurity 2025 Cyber Security Report (72B emails); Barracuda 2025 Email Threats Report; Proofpoint 2024 State of the Phish (7,500 working adults); Pindrop 2025 Voice Intelligence and Security Report (1.2B+ calls); Sumsub Identity Fraud Report 2025-2026 (4M+ fraud attempts); iProov Threat Intelligence Report 2025; Cisco Talos IR Trends Q1 2025 to Q1 2026; NCC Group Annual CTI 2025; UK NCSC Annual Review 2025; Anthropic Threat Intelligence (GTG-1002, November 2025); and named corporate-incident records.
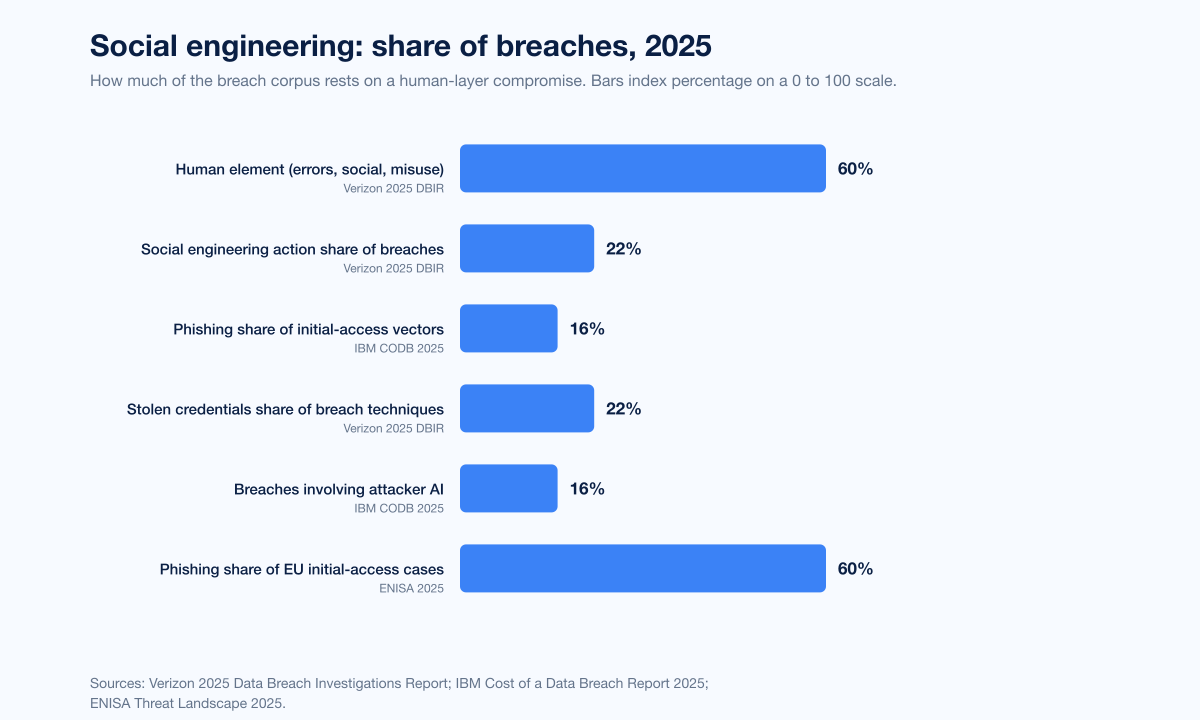
Figure 1: Share of breaches involving human-layer attacks across the 2025 primary-publisher set. Sources: Verizon 2025 Data Breach Investigations Report; IBM Cost of a Data Breach Report 2025; ENISA Threat Landscape 2025.
How big is social engineering in 2026?
Three datasets anchor the answer.
Verizon 2025 DBIR
The Verizon 2025 DBIR, based on 22,052 incidents and 12,195 confirmed breaches between November 1 2024 and October 31 2025, recorded that approximately 60% of confirmed breaches involved a human action. 22% of breaches caused by external actors involved social engineering tactics. Phishing remains the top tactic at 57% of social engineering incidents, followed by pretexting at 30% (with pretexting at the core of BEC having nearly doubled and now accounting for over 50% of all social engineering incidents). Prompt-bombing, a relative newcomer, appears in 14% of incidents. Stolen credentials drive 22% of breaches across all techniques.
The single most-cited operational metric in the 2025 DBIR is timing: the median time-to-click on a phishing email is 21 seconds, and the median time-to-report is 28 minutes. That gap is where credentials are exfiltrated and AiTM session tokens get hijacked.
IBM Cost of a Data Breach Report 2025
The IBM 2025 Cost of a Data Breach Report, released July 30 2025 and based on breach data from 600+ organizations, ranked phishing as the most common initial attack vector at 16% of breaches with an average cost of US$4.8M. The report found AI use in 16% of breaches, with phishing 37% and deepfake impersonation 35% of those AI-involved breaches. The U.S. average breach cost reached a record US$10.22M. Shadow AI was a factor in 20% of breaches and added US$670,000 to the average breach cost. 13% of organizations reported breaches of AI models or applications themselves; 97% of breached organizations that experienced an AI-related incident lacked proper AI access controls. Stingrai's AI Cyber Attack Statistics 2026 covers attacker-AI metrics in greater depth.
ENISA Threat Landscape 2025
ENISA's Threat Landscape 2025, analyzing nearly 4,900 incidents from July 2024 to June 2025, found phishing accounts for about 60% of EU intrusion attempts, vulnerability exploitation 21.3%, botnets 9.9%. AI-supported phishing campaigns represent more than 80% of observed social engineering activity worldwide by early 2025. ENISA's framing matters because it reflects the European cyber-incident corpus, complementing the largely US-focused Verizon DBIR and IBM CODB datasets.
Phishing: the load-bearing channel
APWG's Q4 2025 report counted 853,244 phishing attacks, down 4% from 892,494 in Q3 2025 and from a Q2 2025 spike of 1,130,393 attacks (the largest single quarter since Q2 2023). Social Media and SAAS/Webmail tied as the most-attacked sectors at 20.3% each. APWG also noted a 136% rise in BEC wire-transfer attempts in Q4 2025, with average request amounts of US$50,297. The most prolific BEC actor is now tracked as Scripted Sparrow, sending up to 6M targeted emails per month and frequently leveraging spoofed executive approval chains.
Other primary publishers corroborate the volume. Mimecast caught 9.3 billion threats in the first nine months of 2025 from 24+ trillion data points across 43,000 customers. Hornetsecurity processed 72 billion emails between October 15 2024 and October 15 2025, with 36.9% of business emails unwanted and 2.3% (427.8 million) malicious. Cofense observed one malicious email past secure email gateways every 19 seconds in 2025, more than doubling from one every 42 seconds in 2024. The volume number is unforgiving: even single-percentage-point detection failure rates produce hundreds of thousands of harmful messages reaching inboxes.
For the deeper phishing-specific cuts, see Stingrai's Phishing Statistics 2026.
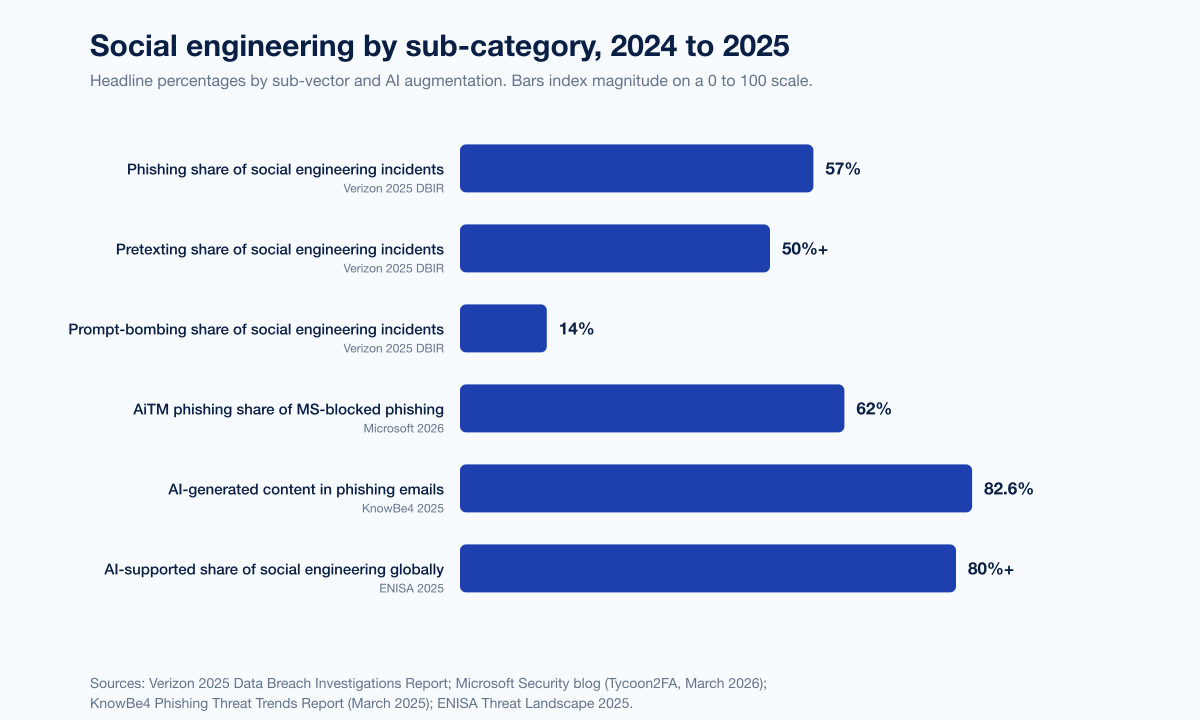
Figure 2: Social engineering breakdown by sub-category and AI augmentation, 2024 to 2025. Sources: Verizon 2025 DBIR; Microsoft Tycoon2FA disclosure; KnowBe4 Phishing Threat Trends Report; ENISA Threat Landscape 2025.
Business email compromise and pretexting
The FBI Internet Crime Complaint Center's 2024 Internet Crime Report recorded US$16.6 billion in total reported losses across 859,532 complaints in 2024, a 33% YoY increase. Within that, BEC produced US$2.77 billion in adjusted losses across 21,442 incidents, the second-largest cybercrime category by financial impact behind investment fraud. The number of BEC complaints stayed roughly steady year over year, but the per-incident losses remain among the highest of any cybercrime category.
The Verizon DBIR records that pretexting incidents at the core of BEC have nearly doubled, now accounting for over 50% of all social engineering incidents and overtaking phishing in BEC frequency. Gone is the assumption that BEC is primarily an automated phishing-link problem. The modal BEC attack in 2026 is a back-and-forth conversation with a finance professional, conducted by a threat actor who has done their homework on the company's vendors, payment cycles, and approval processes.
Vector | Reported figure | Source |
|---|---|---|
Total IC3 cybercrime losses 2024 | US$16.6B (+33% YoY) | |
BEC adjusted losses 2024 | US$2.77B across 21,442 incidents | |
Phishing complaints 2024 | 193,407 (most-reported cybercrime) | |
Elder fraud (60+) losses 2024 | US$4.885B across 147,127 complaints (+43% YoY) | FBI IC3 2024 Elder Fraud Report |
Tech support fraud losses (60+ subset) 2024 | US$1.46B | FBI IC3 2024 Elder Fraud Report |
FTC imposter-scam losses 2024 | US$2.95B | |
Government-imposter scam losses 2024 | US$789M (+US$171M YoY) | |
FTC fraud reports 2024 | 2.6M consumers |
Barracuda's 2025 Email Threats Report found 40% of BEC emails in Q2 2025 were AI-generated, as confirmed by multiple AI text detection tools. AI shifts the cost equation for BEC: an attacker no longer needs near-native English fluency to draft a credible CEO impersonation. The grammar and tone tells that BEC training has historically used as detection cues are increasingly absent.
Voice phishing and deepfake fraud
If 2024 was the year deepfake fraud broke into headlines, 2025 was the year voice fraud went industrial.
CrowdStrike's 2025 Global Threat Report measured vishing up 442% between H1 and H2 2024 with a 40% compounded monthly growth rate. The 2025 Threat Hunting Report reported H1 2025 vishing volume already exceeded the full-year 2024 vishing total. CrowdStrike tracked at least six distinct campaigns in 2024 in which threat actors posed as IT support staff, and at least four leveraged spam-bombing as a pretext for follow-up vishing calls. Named actors include CURLY SPIDER (spam-bombing + vishing to deploy backdoors) and CHATTY SPIDER (Russia-based, callback phishing for data theft + extortion).
Pindrop's 2025 Voice Intelligence and Security Report, analyzing 1.2 billion contact-center calls, recorded a 1,300% YoY surge in deepfake fraud attempts in 2024, jumping from one per month on average to seven per day. Pindrop projects US$44.5 billion in 2025 contact-center fraud exposure, with deepfake-related fraud expected to grow another 162% in 2025. Retail-sector contact-center fraud now hits one in 127 calls, five times the rate of financial-services calls.
Metric | Value | Source |
|---|---|---|
Vishing growth, H1 to H2 2024 | +442% | |
Vishing H1 2025 vs full-year 2024 | Already exceeded | |
Pindrop deepfake fraud growth (2024) | +1,300% YoY | |
Pindrop projected contact-center fraud exposure (2025) | US$44.5B | |
iProov Native Virtual Camera attack growth | +2,665% | |
iProov face-swap attack growth | +300% vs 2023 | |
iProov crime-as-a-service ecosystem | ~24,000 users selling attack tech | |
Sumsub deepfake share of fraud attempts | 7% (4x increase 2023 to 2024) |
iProov's 2025 Threat Intelligence Report recorded Native Virtual Camera digital injection attacks +2,665% in 2024 due to mainstream app-store infiltration of injection tools, and face-swap attacks +300% vs 2023. The crime-as-a-service ecosystem behind these attacks now includes nearly 24,000 users selling attack technologies, with 115,000+ potential attack combinations available to operators.
The synthetic-media problem and the SIM-swap problem each get their own deep-dives in Stingrai's Deepfake Statistics 2026 and SIM Swap Statistics 2026.
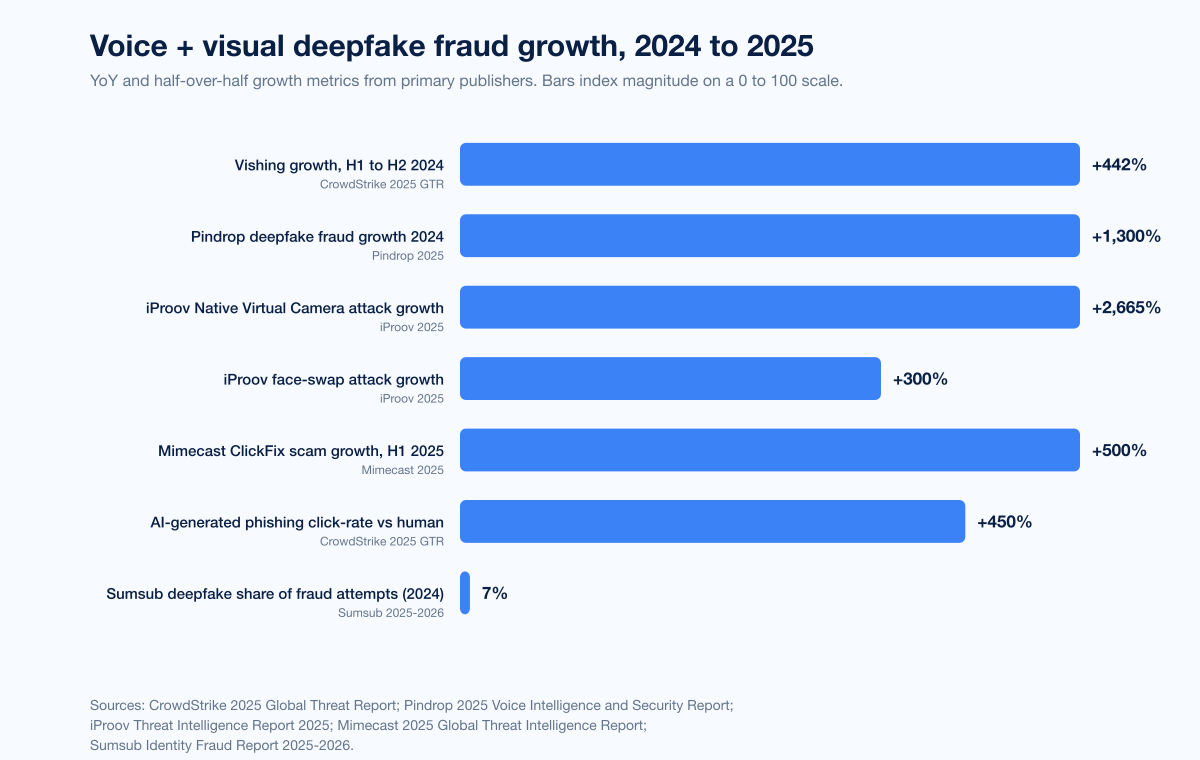
Figure 3: Voice and visual deepfake fraud growth metrics from primary publishers, 2024 to 2025. Sources: CrowdStrike 2025 Global Threat Report; Pindrop 2025 Voice Intelligence and Security Report; iProov Threat Intelligence Report 2025; Mimecast 2025 Global Threat Intelligence Report; Sumsub Identity Fraud Report 2025-2026.
AiTM phishing kits and the death of easy MFA
Microsoft's 2025 Digital Defense Report attributes 80% of MFA-bypass breaches to session-token theft via adversary-in-the-middle (AiTM) attacks, where a proxy server captures the username, password, and post-MFA session cookie that the identity provider issues. Because the session token is legitimate, the attacker can replay it without triggering an MFA prompt.
The dominant AiTM kit is Tycoon2FA. Microsoft Security's March 4 2026 disclosure reported that Tycoon2FA accounted for roughly 62% of all phishing attempts blocked by Microsoft by mid-2025. Microsoft Defender for Office 365 blocked more than 13 million Tycoon2FA emails in October 2025 alone, including many that spoofed organizations' own domains. The kit is rented at US$120 for 10-day access or US$350 for a month, lowering the technical bar for credential-plus-session-token theft against Microsoft 365.
In early March 2026, Microsoft's Digital Crimes Unit, Europol, and 11 industry partners disrupted Tycoon2FA's hosting infrastructure. Other AiTM kits (Mamba 2FA, Evilginx) remain operational; the takedown buys time, not victory.
ClickFix: the new fastest-growing lure pattern
Mimecast's 2025 Global Threat Intelligence Report recorded a 500% surge in ClickFix scams during the first six months of 2025, with the technique now accounting for nearly 8% of attacks. ClickFix is a lure where attackers use fake error messages or verification prompts (often impersonating CAPTCHA or browser update screens) to trick users into copying and running malicious commands on their own devices. The user does the attacker's job by pasting an attacker-supplied PowerShell or shell command into Run, terminal, or developer console.
ClickFix's growth is partly because it sidesteps email gateway controls. The malicious payload is a copy-paste-and-execute step performed by the user, not a malicious file or link triggering an attachment scanner. AI-augmented phishing now drives credible delivery: Mimecast also recorded a 500% surge in AI-augmented phishing in 2025, with phishing now accounting for 77% of all attacks (up from 60% in 2024).
Pretexting cases that defined the threat surface
A handful of named incidents now anchor the public record on pretexting and synthetic-media-driven social engineering.
Arup Hong Kong (January-February 2024)
A finance professional at multinational engineering firm Arup transferred US$25.6M (HK$200M) across 15 transfers to fraudsters after a video call in which AI-generated deepfakes impersonated the company's CFO and several colleagues. The deepfakes were built from publicly available video and audio of real Arup executives. Hong Kong Police confirmed the deepfake mechanism, and the WEF wrote up the case as the canonical 2024 deepfake fraud incident.
WPP CEO deepfake attempt (May 2024)
Cybercriminals created a fake WhatsApp account using publicly available images of WPP CEO Mark Read and ran a video call with another executive using a deepfake of Read to discuss launching a fake new business. The targeted executive grew suspicious and did not comply.
Ferrari CEO deepfake attempt (July 2024)
A Ferrari executive received a series of WhatsApp messages and a follow-up call featuring a deepfake voice of CEO Benedetto Vigna requesting a confidential transaction. The attempt was caught when the executive asked Vigna a security question only the real CEO would know. The case is now widely cited as a template for how out-of-band verification questions can break a deepfake-driven pretexting attempt.
KnowBe4 hires DPRK IT worker (July 2024)
KnowBe4 publicly disclosed that it had hired a North Korean operator using a stolen US identity, AI-augmented interview imagery, and a US-based "laptop farm" address. The operator passed background checks, video interviews, and even a Day 1 sync, but the company's device-posture monitoring flagged the workstation in real time. The DPRK IT worker scheme is one of the most successful AI-augmented insider threats of the past two years; the DOJ's June 30 2025 disruption recorded searches of 29 laptop farms across 16 states and seizure of 29 financial accounts plus 21 fraudulent websites. Stingrai's Insider Threat Statistics 2026 covers the DPRK IT worker pattern in greater depth.
AI-augmented social engineering: from automation to autonomy
The volume statistics confirm what defenders see in inboxes. The agentic statistics reveal where the threat is going.
KnowBe4 phishing-content telemetry
KnowBe4's March 2025 Phishing Threat Trends Report, analyzing phishing emails between September 2024 and February 2025, found 82.6% used some form of AI-generated content, alongside a 17.3% rise in phishing email volume vs the prior six months. AI-generated phishing has industrialized as the default content-production model for credential phishing.
CrowdStrike click-rate uplift
CrowdStrike's 2025 GTR measured AI-generated phishing emails landing a 54% click-through rate against 12% for human-written phishing, a 4.5x uplift. The number triangulates with KnowBe4's 82.6% AI-content rate and Mimecast's 500% AI-augmented phishing surge.
Anthropic GTG-1002 disclosure (November 13 2025)
The single most-cited 2025 incident is Anthropic's GTG-1002 disclosure. A Chinese state-sponsored group instrumented Claude Code in an MCP-connected agentic framework to autonomously execute roughly 80 to 90 percent of intrusion tradecraft against approximately 30 organizations across technology, finance, government, and chemical manufacturing. The campaign was detected mid-September 2025 and contained within ~10 days. Operators bypassed safety controls by social engineering the AI itself, framing the activity as authorized defensive penetration testing.
The conceptual point matters for the umbrella category. Social engineering used to mean tricking a human. After GTG-1002 it also means tricking an AI agent that has been delegated authority over real systems. Stingrai's AI Cyber Attack Statistics 2026 covers attacker-AI metrics and the GTG-1002 case in greater depth.
NCSC UK 2025 Annual Review
The UK NCSC noted in its 2025 Annual Review that phishing remains the number-one attack route. Actors linked to China, Russia, Iran, and North Korea are using large language models to evade detection, support reconnaissance, process exfiltrated data, gain access through social engineering, and support vulnerability research. New techniques identified in the last 18 months include fully automated spear-phishing campaigns, hijacking cloud-based LLMs, and automating post-breach attack stages.
Industry breakdown: who gets hit hardest
KnowBe4's 2025 Phishing By Industry Benchmarking Report, based on 14.5 million users across 62,400 organizations and 67.7 million simulated phishing tests, ranks the most at-risk industries by baseline (untrained) Phish-prone Percentage:
Industry | Untrained baseline PPP | Source |
|---|---|---|
Healthcare and Pharmaceuticals | 41.9% | KnowBe4 2025 PIB |
Insurance | 39.2% | KnowBe4 2025 PIB |
Retail and Wholesale | 36.5% | KnowBe4 2025 PIB |
Industry-wide global baseline | 33.1% | KnowBe4 2025 PIB |
Pindrop's 2025 voice fraud telemetry adds that retail-sector contact centers now see one fraud attempt per 127 calls, five times the rate of financial-services contact centers. The Verizon DBIR's industry snapshots show finance, healthcare, manufacturing, and public administration repeatedly cluster around BEC and credential-driven attacks. APWG's Q4 2025 report added Social Media and SAAS/Webmail tied as the most-attacked sectors at 20.3% each, displacing the financial-services category that has historically led APWG telemetry.
The pattern is consistent: regulated-data sectors with high-volume external-customer interaction (healthcare, insurance, retail, contact-centric financial services) get hit hardest. Industries with more closed user populations (manufacturing, energy) see lower volumes but more targeted spear-phishing.
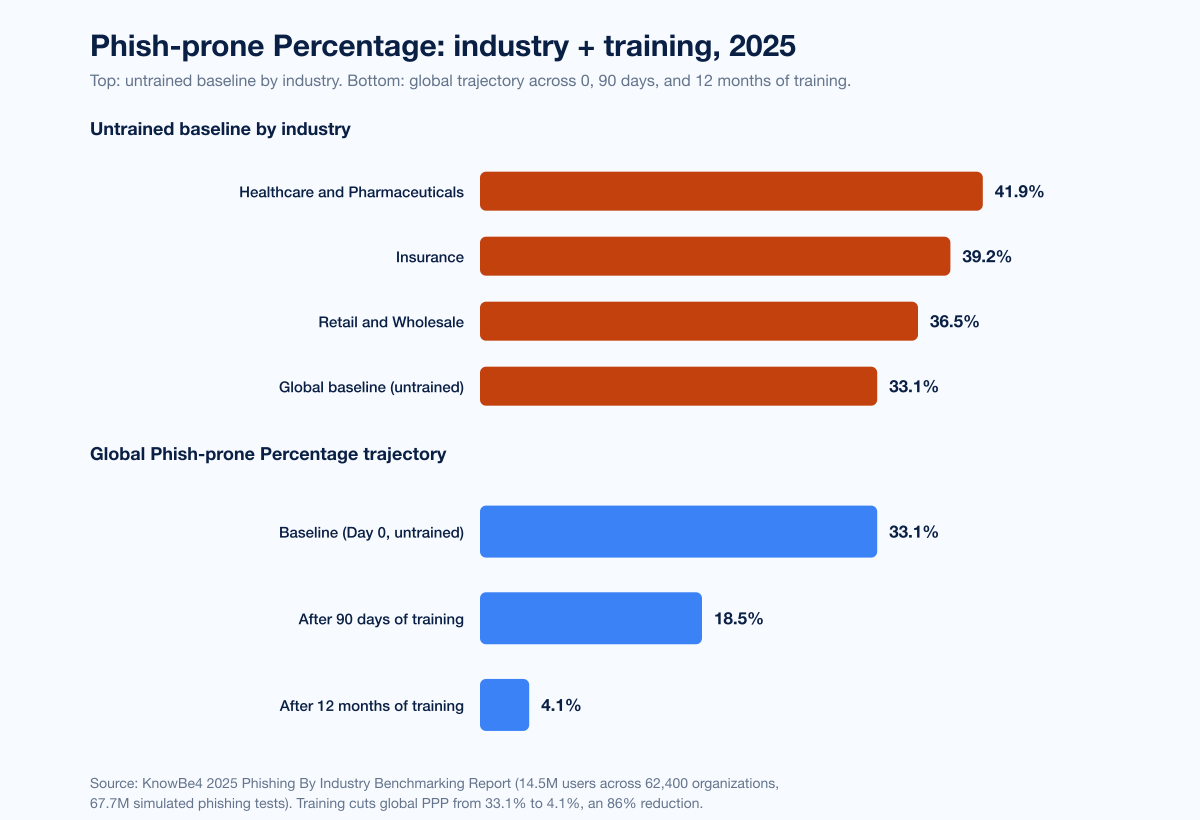
Figure 4: KnowBe4 Phish-prone Percentage by industry (top) and global trajectory across baseline, 90 days, and 12 months of training (bottom). Source: KnowBe4 2025 Phishing By Industry Benchmarking Report.
Cost: the financial weight of social engineering
The aggregate financial weight of social engineering in 2024 telemetry runs north of US$15 billion in directly attributable losses across reported cybercrime. A summary across primary publishers:
Vector | Reported figure | Source |
|---|---|---|
FBI IC3 total cybercrime losses 2024 | US$16.6B (+33% YoY) | |
BEC adjusted losses 2024 | US$2.77B | |
Elder fraud (60+) losses 2024 | US$4.885B | FBI IC3 2024 Elder Fraud Report |
Tech support fraud losses (60+ subset) 2024 | US$1.46B | FBI IC3 2024 Elder Fraud Report |
FTC imposter-scam losses 2024 | US$2.95B | |
Government-imposter scam losses 2024 | US$789M | |
IBM phishing-driven breach average cost | US$4.8M per breach | |
Pindrop projected contact-center fraud exposure 2025 | US$44.5B |
The numbers triangulate but do not strictly add: IC3 totals include phishing, BEC, romance, and investment fraud; FTC totals include imposter and product scams; Pindrop's projection is industry-wide voice-fraud exposure. The combined aggregate, plus the unreported losses that never reach IC3 or FTC, is the conservative floor for what social engineering costs the global economy in 2025.
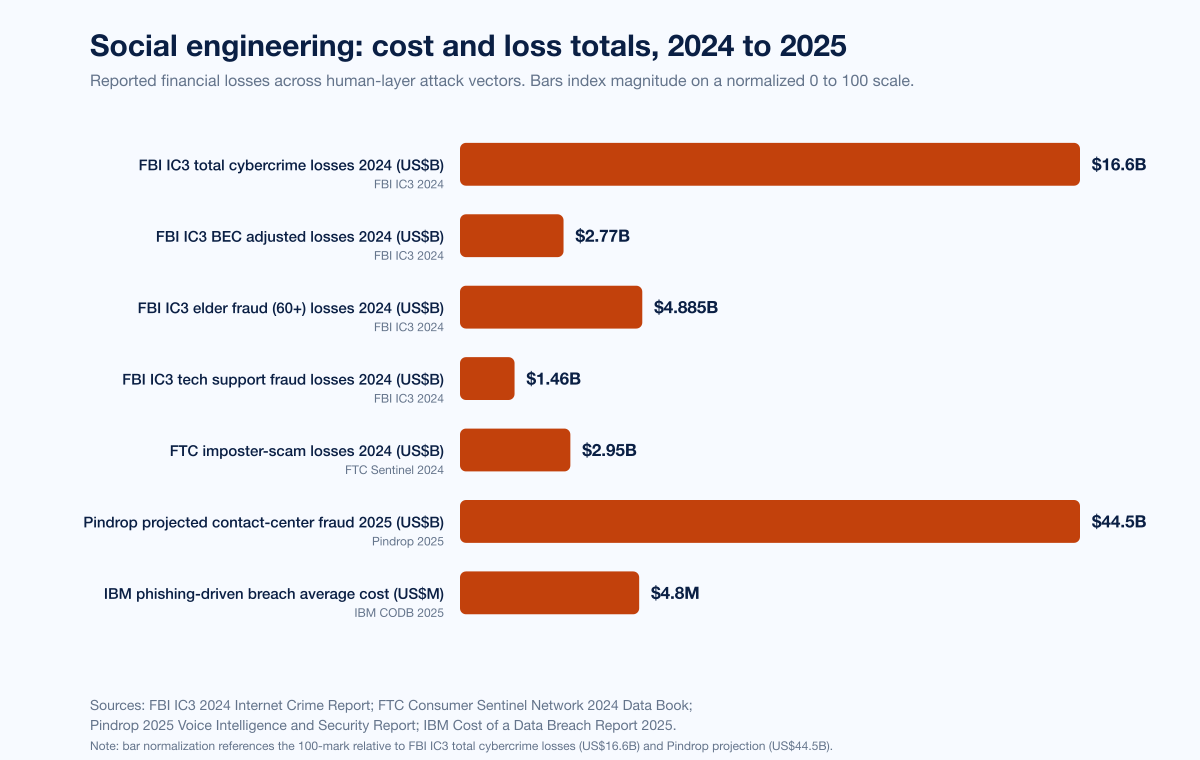
Figure 5: Social engineering cost and loss totals from primary publishers, 2024 to 2025. Bars index magnitude on a normalized 0 to 100 scale referenced to the largest figure (Pindrop projected US$44.5B contact-center fraud and FBI IC3 US$16.6B total cybercrime). Sources: FBI IC3 2024 Internet Crime Report; FTC Consumer Sentinel Network 2024 Data Book; Pindrop 2025 Voice Intelligence and Security Report; IBM Cost of a Data Breach Report 2025.
Detection time and the 21-second click
The Verizon 2025 DBIR's tightest metric is timing. Median time-to-click on a phishing email is 21 seconds. Median time-to-report is 28 minutes. Within that 28-minute window, AiTM kits exfiltrate session tokens, credential-stealer payloads execute, and BEC actors initiate wire-transfer requests. The question is no longer whether a user will click. It is whether the controls between click and exfiltration can interrupt the chain in under a minute.
Mandiant's M-Trends 2026, drawing on roughly 450,000 hours of incident-response work, found the time between initial compromise and the access-handoff from one threat cluster to another has collapsed from more than 8 hours in 2022 to 22 seconds in 2025. AI shortens both legs of that handoff. The takeaway for buyers: post-click detection budgets need to scale to seconds and minutes, not hours.
Cisco Talos IR Trends data tracks the same trend at the engagement level. Q1 2025 saw phishing as the top initial-access vector at 50% of engagements. Q4 2025 saw vulnerability exploitation overtake phishing (~40% vs phishing in second). Q1 2026 saw phishing reemerge as the top initial-access vector. The interplay tells you that phishing is not so much "back" as "always there" with cycles of relative emphasis vs vulnerability exploitation depending on what new public CVEs are available for mass exploitation.
Defender effectiveness: training works, but is necessary, not sufficient
KnowBe4's 2025 Phishing By Industry Benchmarking Report measured the global Phish-prone Percentage falling from a baseline of 33.1% to 4.1% after 12 months of consistent training, an 86% reduction. The dataset is real: 14.5 million users across 62,400 organizations and 67.7 million simulated phishing tests.
But training is necessary, not sufficient. Two facts cap the upside:
Verizon's 21-second median click time means a single missed lure converts before any well-trained user has time to reconsider. Training improves base rates; it does not prevent every click on a sophisticated AiTM lure.
AI-generated phishing's 54% click rate (per CrowdStrike) is high enough that even an organization at the 4.1% post-training PPP will see meaningful conversion against a well-crafted AI lure that bypasses gateway filtering.
The implication for buyers is layered control. Training cuts the conversion rate. Phishing-resistant authentication (FIDO2 / WebAuthn passkeys, device-bound credentials) cuts the value of any successful credential capture. Out-of-band verification for high-value actions (wire transfers, credential resets, vendor changes) cuts the value of any successful pretexting interaction.
Proofpoint's 2024 State of the Phish, based on a survey of 7,500 working adults and 1,050 IT pros across 15 countries, adds the cultural dimension: 71% of working adults admitted to taking a risky action (password reuse, sharing, clicking links from unknown senders, giving credentials to untrustworthy sources), and 68% knowingly put their organizations at risk. Simulated phishing failure rates dropped to 9.3% in 2023, but 71% of organizations still experienced at least one successful phishing attack, with reports of resulting financial penalties up 144% YoY and reputational damage up 50%.
Forward outlook: what primary publishers project for 2026
Three forecasts from named primary sources merit explicit citation:
WEF Global Cybersecurity Outlook 2026 projects 94% of leaders agree AI is the single most significant driver of cybersecurity change in 2026, with 87% flagging AI-related vulnerabilities as the fastest-growing cyber risk. The report records adversarial use of generative AI to automate and scale social engineering, including realistic phishing emails, deepfake audio and video, and translated/localized impersonations as the dominant adversary motion.
CrowdStrike 2026 Global Threat Report projects continued growth in AI-enabled tradecraft, with AI-aided social engineering and identity-based attacks the dominant 2026 patterns. The 2026 GTR records 89% YoY growth in AI-enabled adversary attacks and adversaries exploiting legitimate GenAI tools at 90+ organizations via prompt injection.
Mandiant M-Trends 2026 projects continued compression of attacker dwell time and initial-access handoff (currently 22 seconds), driven by AI-aware malware and division-of-labor specialization across the eCrime supply chain.
The unifying signal: 2026 is the year social engineering finishes its transition from a high-volume, low-skill attack category into a fully industrialized, AI-augmented, cross-channel threat surface that targets the human layer (and increasingly the AI agent layer) with the same operational rigor as nation-state cyber campaigns.
What this means for defenders
Five concrete buyer actions the data supports:
Adopt phishing-resistant MFA everywhere it can run. Microsoft's 80% MFA-bypass attribution to AiTM and Tycoon2FA's 62% share of MS-blocked phishing show that text-message and OTP-based MFA is now compromised by default. Phishing-resistant authentication (FIDO2 / WebAuthn passkeys, hardware security keys, device-bound credentials) is the floor.
Treat the contact center as a high-value target. Pindrop's 1,300% deepfake fraud growth, CrowdStrike's 442% vishing growth, and the projected US$44.5B 2025 contact-center exposure are too much volume to defend with manual call triage. Out-of-band passphrase callbacks for every wire transfer and credential reset, active-liveness identity verification with injection-attack detection, and voice-deepfake detection for high-value contact centers are now table stakes.
Run continuous training, then layer authentication and verification. KnowBe4's 86% reduction is real, but only with sustained training. Combine training with phishing-resistant MFA and with out-of-band verification on high-value actions to compound the effect.
Build for prompt-injection resistance in any AI-facing process. GTG-1002 demonstrated that an adversary can social engineer an AI agent. OWASP LLM Top 10 v2025 is the starting reference; MITRE ATLAS the second pass. Treat any text your AI features read as potentially adversarial; sanitize at every boundary; keep AI-agent privileges low.
Run red-team engagements that include social engineering scenarios end to end. Stingrai's Penetration Testing as a Service covers AiTM-aware phishing, vishing/voice-deepfake, BEC pretexting, and DPRK-style insider scenarios. For deeper sub-cluster coverage, see Stingrai's Phishing Statistics 2026, Deepfake Statistics 2026, SIM Swap Statistics 2026, Insider Threat Statistics 2026, AI Cyber Attack Statistics 2026, and Compromised Credential Statistics 2026.
Frequently Asked Questions
What is the most cited social engineering statistic for 2026?
The most cited social engineering statistic for 2026 is Verizon's finding in the 2025 DBIR that approximately 60% of confirmed breaches involve the human element, including a malicious click, a socially engineered call, or misdelivery of sensitive data. Within social engineering specifically, phishing accounts for 57% of incidents and pretexting for 30%. IBM's 2025 Cost of a Data Breach Report ranked phishing as the most common initial access vector at 16% of breaches, with an average breach cost of US$4.8M, and found 1 in 6 (16%) breaches now involve attacker AI.
How big are BEC and pretexting losses in 2026?
The FBI IC3 2024 Internet Crime Report (released April 2025) logged US$2.77B in adjusted Business Email Compromise losses across 21,442 incidents. The Verizon 2025 DBIR records that pretexting incidents at the core of BEC have nearly doubled, now accounting for over 50% of all social engineering incidents and overtaking phishing in BEC frequency. APWG's Q4 2025 report observed a 136% increase in BEC wire-transfer attempts, with average request amounts of US$50,297.
How large is the phishing problem in 2026?
The APWG Q4 2025 Phishing Activity Trends Report counted 853,244 phishing attacks. Q2 2025 spiked at 1,130,393 attacks, the largest single quarter since Q2 2023. Phishing was the most-reported cybercrime in the FBI's 2024 IC3 report at 193,407 complaints. Mimecast caught 9.3 billion threats in the first nine months of 2025, with phishing now 77% of all attacks (up from 60% in 2024). Cofense observed one malicious email past secure-email-gateway every 19 seconds in 2025. The Verizon 2025 DBIR puts the median time-to-click on a phishing email at 21 seconds and median time-to-report at 28 minutes.
What share of social engineering is now AI-supported?
ENISA's Threat Landscape 2025 reports that AI-supported phishing campaigns represent more than 80% of observed social engineering activity worldwide by early 2025. KnowBe4's analysis of phishing emails between September 2024 and February 2025 found 82.6% used some form of AI-generated content. Barracuda's 2025 Email Threats Report found 40% of BEC emails in Q2 2025 were AI-generated. CrowdStrike's 2025 Global Threat Report measured AI-generated phishing emails landing a 54% click-through rate vs 12% for human-written phishing. IBM's 2025 Cost of a Data Breach Report attributes 1 in 6 (16%) breaches to attacker AI, with phishing 37% and deepfake impersonation 35% of those cases.
How fast is voice phishing (vishing) growing in 2026?
CrowdStrike's 2025 Global Threat Report measured vishing growing 442% between H1 and H2 2024 with a 40% compounded monthly growth rate. The CrowdStrike 2025 Threat Hunting Report (August 2025) reported H1 2025 vishing volume already exceeded the full-year 2024 vishing total. Pindrop's 2025 Voice Intelligence and Security Report, analyzing 1.2 billion contact-center calls, recorded a 1,300% YoY rise in deepfake fraud attempts, jumping from one per month to seven per day, with US$44.5B in projected 2025 contact-center fraud exposure.
Which industries are hit hardest by social engineering?
KnowBe4's 2025 Phishing By Industry Benchmarking Report ranked Healthcare and Pharmaceuticals as the most at-risk industry by baseline Phish-prone Percentage at 41.9%, followed by Insurance at 39.2% and Retail and Wholesale at 36.5%, against an industry-wide baseline of 33.1%. Pindrop measured retail-sector contact-center fraud at one attempt per 127 calls, five times the rate of financial services. The APWG Q4 2025 report named Social Media and SAAS/Webmail as the most-attacked sectors at 20.3% each.
How effective is security awareness training against phishing?
KnowBe4's 2025 Phishing By Industry Benchmarking Report, based on 14.5 million users across 62,400 organizations and 67.7 million simulated phishing tests, measured the global Phish-prone Percentage dropping from a baseline of 33.1% to 4.1% after 12 months of consistent training, an 86% reduction. Proofpoint's 2024 State of the Phish reported simulated phishing failure rates of 9.3% across 7,500 working adults in 15 countries. Training works, but Verizon's 21-second median time-to-click means a single missed lure converts before any well-trained user has time to think twice. Layer training with phishing-resistant authentication and out-of-band verification.
What is the Tycoon2FA AiTM phishing-as-a-service kit?
Tycoon2FA is an adversary-in-the-middle phishing-as-a-service kit that emerged in August 2023 and that Microsoft has tracked as the dominant AiTM tool among threat actors. Microsoft's March 2026 disclosure reported Tycoon2FA accounted for roughly 62% of all phishing attempts blocked by Microsoft by mid-2025. Microsoft Defender for Office 365 blocked more than 13 million Tycoon2FA emails in October 2025 alone. The kit is rented at US$120 for 10-day access or US$350 for a month. Microsoft attributes 80% of MFA-bypass breaches to AiTM session-token theft. Microsoft, Europol, and 11 industry partners disrupted Tycoon2FA infrastructure in early March 2026.
How do deepfake fraud and identity verification attacks fit into social engineering?
Synthetic media is rapidly becoming a load-bearing component of social engineering. Sumsub's Identity Fraud Report 2025-2026 measured a 4x increase in detected deepfakes from 2023 to 2024, with deepfakes accounting for 7% of fraud attempts. iProov's 2025 Threat Intelligence Report recorded a 2,665% rise in Native Virtual Camera digital injection attacks and a 300% rise in face-swap attacks. Pindrop reported a 1,300% YoY surge in deepfake fraud attempts in contact centers. The single most-cited corporate incident remains the January-February 2024 Arup deepfake CFO fraud in Hong Kong, which moved US$25.6M across 15 transfers in a single multi-person video call.
Where can I get the latest social engineering data?
Track the Verizon Data Breach Investigations Report (annual, May), IBM Cost of a Data Breach Report (annual, July), FBI IC3 Internet Crime Report (annual, April), FTC Consumer Sentinel Network Data Book (annual, March), APWG Phishing Activity Trends Report (quarterly), Microsoft Digital Defense Report (annual, October), CrowdStrike Global Threat Report (annual, February), Mandiant M-Trends (annual, March), ENISA Threat Landscape (annual, October), KnowBe4's Phishing By Industry Benchmarking Report (annual, May), Mimecast's Global Threat Intelligence Report (annual, October), Cofense's Annual State of Email Security Report, Pindrop Voice Intelligence and Security Report (annual, June), Sumsub's Identity Fraud Report (annual, November), iProov's Threat Intelligence Report (annual, February), and WEF Global Cybersecurity Outlook (annual, January).
References
Verizon. 2025 Data Breach Investigations Report. May 2025. https://www.verizon.com/business/resources/reports/dbir/. 22,052 incidents; 12,195 breaches.
IBM. Cost of a Data Breach Report 2025. Jul 30 2025. https://www.ibm.com/reports/data-breach. Phishing 16% of breaches at US$4.8M.
IBM. 2025 Cost of a Data Breach Report: Navigating the AI rush. Jul 2025. https://www.ibm.com/think/x-force/2025-cost-of-a-data-breach-navigating-ai. Attacker AI in 16% of breaches.
FBI Internet Crime Complaint Center. 2024 Internet Crime Report. Apr 2025. https://www.ic3.gov/AnnualReport/Reports/2024_IC3Report.pdf. US$16.6B losses; BEC US$2.77B; phishing 193,407 complaints.
FBI IC3. 2024 Elder Fraud Report. Jun 2025. https://www.ic3.gov. US$4.885B losses across 147,127 complaints (60+).
FTC. Consumer Sentinel Network 2024 Data Book. Mar 2025. https://www.ftc.gov/system/files/ftc_gov/pdf/csn-annual-data-book-2024.pdf. Imposter scams US$2.95B.
APWG. Phishing Activity Trends Report Q4 2025. Feb 2026. https://docs.apwg.org/reports/apwg_trends_report_q4_2025.pdf. 853,244 phishing attacks.
APWG. Phishing Activity Trends Report Q2 2025. Aug 2025. https://docs.apwg.org/reports/apwg_trends_report_q2_2025.pdf. 1,130,393 attacks.
Microsoft Security. Microsoft Digital Defense Report 2025. Oct 2025. https://www.microsoft.com/en-us/security/security-insider/threat-landscape/microsoft-digital-defense-report-2025. 80% of MFA-bypass via AiTM session-token theft.
Microsoft Security. Inside Tycoon2FA. Mar 4 2026. https://www.microsoft.com/en-us/security/blog/2026/03/04/inside-tycoon2fa-how-a-leading-aitm-phishing-kit-operated-at-scale/. 62% of MS-blocked phishing; March 2026 takedown.
CrowdStrike. 2025 Global Threat Report. Feb 2025. https://www.crowdstrike.com/en-us/press-releases/crowdstrike-releases-2025-global-threat-report/. Vishing +442% H1 to H2 2024; AI phishing 54% click rate.
CrowdStrike. 2025 Threat Hunting Report. Aug 2025. https://www.crowdstrike.com/en-us/resources/reports/threat-hunting-report/. H1 2025 vishing exceeded full-year 2024.
CrowdStrike. 2026 Global Threat Report: Year of the Evasive Adversary. Feb 2026. https://www.crowdstrike.com/en-us/blog/crowdstrike-2026-global-threat-report-findings/. 89% YoY rise in AI-enabled adversary attacks.
Mandiant / Google Cloud. M-Trends 2026. Mar 2026. https://cloud.google.com/blog/topics/threat-intelligence/m-trends-2026. 22-second initial-access handoff time.
ENISA. Threat Landscape 2025. Oct 2025. https://www.enisa.europa.eu/publications/enisa-threat-landscape-2025. Phishing 60% of EU intrusion attempts; AI-supported >80%.
World Economic Forum. Global Cybersecurity Outlook 2026. Jan 2026. https://reports.weforum.org/docs/WEF_Global_Cybersecurity_Outlook_2026.pdf. 94% AI biggest driver; 87% flag AI vulns.
KnowBe4. 2025 Phishing By Industry Benchmarking Report. May 13 2025. https://www.knowbe4.com/press/knowbe4-report-reveals-security-training-reduces-global-phishing-click-rates-by-86. Baseline 33.1% to 4.1% post-training.
KnowBe4. Phishing Threat Trends Report. Mar 2025. https://www.knowbe4.com/press/new-knowbe4-report-reveals-a-spike-in-ransomware-payloads-and-ai-powered-polymorphic-phishing-campaigns. 82.6% of phishing emails AI-generated.
Cofense. Annual State of Email Security Report. Feb 2026. https://cofense.com/annualreport. One malicious email past SEG every 19 seconds.
Cofense. AI-Powered Phishing Accelerates to One Attack Every 19 Seconds. Feb 2026. https://cofense.com/Blog/Cofense-Report-Reveals-AI-Powered-Phishing-Accelerated-to-One-Attack-Every-19-Seconds.
Mimecast. 2025 Global Threat Intelligence Report. Oct 22 2025. https://www.mimecast.com/resources/press-releases/gtir-pr-2025/. 9.3B threats first 9 months 2025; ClickFix +500%.
Hornetsecurity. Annual Cyber Security Report 2025. Nov 2025. https://www.hornetsecurity.com/en/cyber-security-report/. 72B emails analyzed.
Barracuda. 2025 Email Threats Report. Mar 2025. https://www.barracuda.com/reports/2025-email-threats-report. 40% of Q2 2025 BEC AI-generated.
Proofpoint. 2024 State of the Phish. Feb 2024. https://www.proofpoint.com/us/resources/threat-reports/state-of-phish. 7,500 working adults across 15 countries.
Pindrop. 2025 Voice Intelligence and Security Report. Jun 2025. https://www.pindrop.com/research/report/voice-intelligence-security-report/. 1.2B+ calls; +1,300% deepfake fraud.
Sumsub. Identity Fraud Report 2025-2026. Nov 2025. https://sumsub.com/fraud-report-2025/. 4x deepfake increase; 7% of fraud attempts.
iProov. Threat Intelligence Report 2025. Feb 2025. https://www.iproov.com/reports/threat-intelligence-report-2025-remote-identity-attack. Native Virtual Camera +2,665%; face-swap +300%.
NCSC UK. Annual Review 2025. Oct 2025. https://www.ncsc.gov.uk/files/ncsc-annual-review-2025.pdf. Phishing remains UK's top attack route.
Cisco Talos. IR Trends Q4 2025. Jan 2026. https://blog.talosintelligence.com/ir-trends-q4-2025/. Phishing now second initial-access vector.
Cisco Talos. IR Trends Q1 2025. Apr 2025. https://blog.talosintelligence.com/ir-trends-q1-2025/. Phishing 50% of engagements.
Cisco Talos. IR Trends Q1 2026. Apr 2026. https://blog.talosintelligence.com/ir-trends-q1-2026/. Phishing reemerges as top initial-access vector.
NCC Group. Annual Cyber Threat Intelligence 2025. Feb 2026. https://www.nccgroup.com/annual-cyber-threat-intelligence-report-2025/. 7,874 ransomware attacks (+50% YoY).
Anthropic. Disrupting the first reported AI-orchestrated cyber espionage campaign. Nov 13 2025. https://www.anthropic.com/news/disrupting-AI-espionage. GTG-1002 disclosure.
Fortune. A deepfake CFO tricked British design firm Arup in $25 million fraud. May 17 2024. https://fortune.com/europe/2024/05/17/arup-deepfake-fraud-scam-victim-hong-kong-25-million-cfo/.
Marketing-Interactive. WPP CEO Mark Read deepfake attempt. May 2024. https://www.marketing-interactive.com/wpp-ceo-mark-read-deepfake-ai-scam.
Fortune. Ferrari deepfake attempt. Jul 27 2024. https://fortune.com/2024/07/27/ferrari-deepfake-attempt-scammer-security-question-ceo-benedetto-vigna-cybersecurity-ai/.
KnowBe4. DPRK IT worker disclosure. Jul 2024. https://www.knowbe4.com/press/knowbe4-issues-warning-after-falling-victim-to-fake-it-worker-scam.
US Department of Justice. Coordinated actions against North Korean remote IT workers. Jun 30 2025. https://www.justice.gov/opa/pr/justice-department-announces-coordinated-nationwide-actions-combat-north-korean-remote.
Take action with Stingrai
If you are scoping social-engineering-aware penetration testing, vishing/voice-deepfake red-team scenarios, BEC pretexting simulations, or hardening your AiTM-resistant authentication and out-of-band verification controls, book a discovery call with Stingrai. We are an offensive-security firm with Penetration Testing as a Service and red-team services that map directly onto the Verizon DBIR, MITRE ATT&CK, and OWASP-aligned scenarios documented in this post. For deeper sub-cluster reading, see Stingrai's sibling references on Phishing Statistics 2026, Deepfake Statistics 2026, SIM Swap Statistics 2026, Insider Threat Statistics 2026, AI Cyber Attack Statistics 2026, and Compromised Credential Statistics 2026.