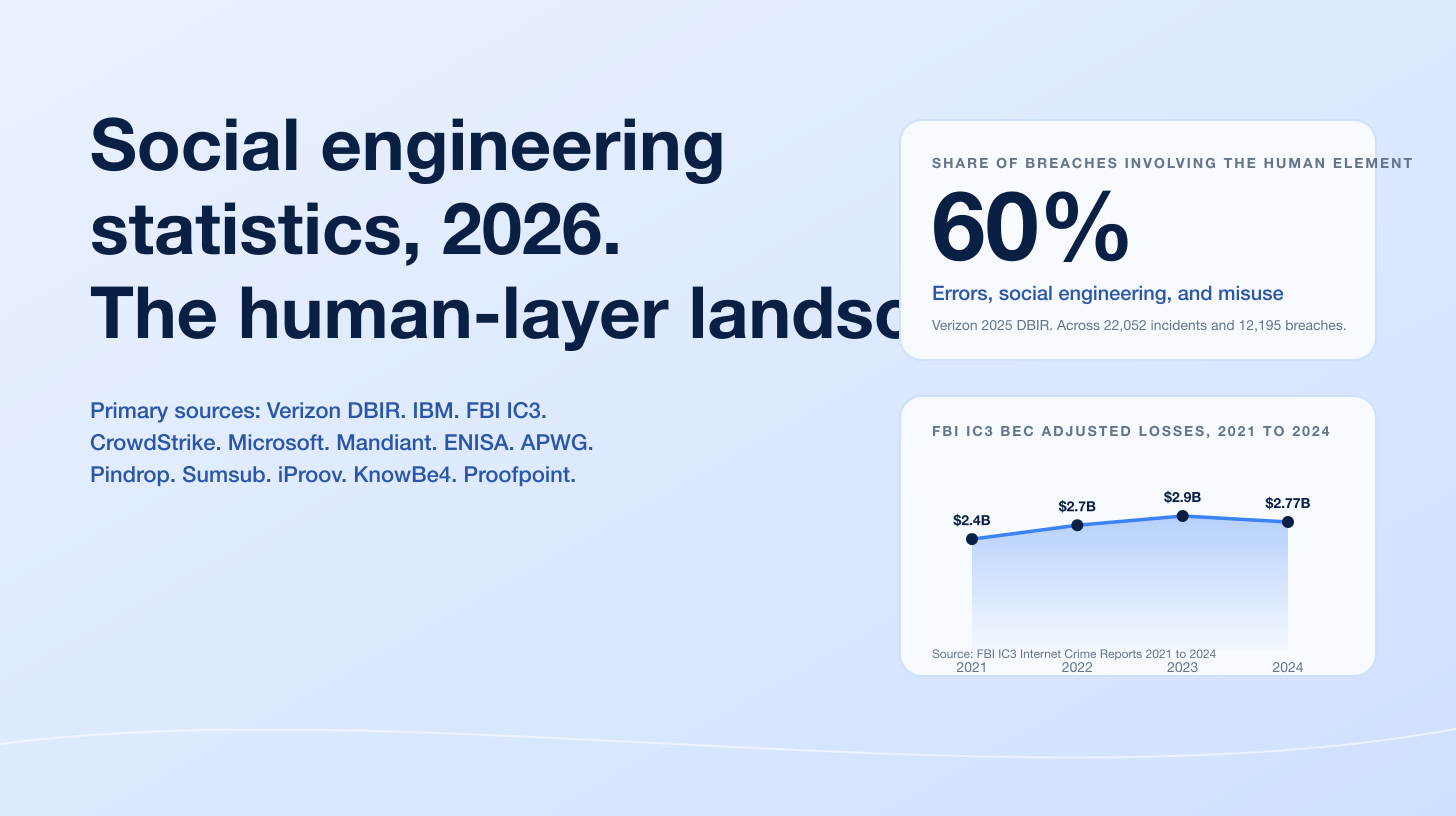
The CrowdStrike 2025 Global Threat Report logged a +442% surge in vishing activity between H1 and H2 2024, and the follow-up CrowdStrike 2025 Threat Hunting Report (covering July 2024 to June 2025) confirmed that H1 2025 vishing volume had already exceeded full-year 2024. Mandiant's M-Trends 2026 report elevated voice phishing to the #2 most common initial infection vector for 2025, present in 11% of Mandiant investigations where an initial vector could be identified. Pindrop's 2025 Voice Intelligence and Security Report measured a +1,300% rise in deepfake fraud attempts in 2024, with contact centers exposed to an estimated US$44.5B of fraud in 2025. The voice channel is no longer a fallback; it is the front door.
Three forces are pushing the numbers. Generative AI has collapsed the cost of producing a convincing scripted call. CrowdStrike attributes a substantial share of the 2024 surge to AI-augmented social engineering, with AI-powered phishing emails reaching 54% click-through rates. Help-desk impersonation tradecraft pioneered by Scattered Spider (UNC3944, Octo Tempest, Storm-0875, Muddled Libra) industrialized the playbook: vish the help desk, request a password reset, defeat MFA, pivot to identity infrastructure, deploy ransomware. Adversary-in-the-middle (AiTM) tooling has migrated to voice as a delivery mechanism, with Microsoft and CrowdStrike both documenting AiTM phishing kits paired with vishing pretext calls in 2025. The MGM Resorts (2023, ~US$100M), Caesars (2023, US$15M ransom), Snowflake (2024, ~165 victims), and the Marks & Spencer / Co-op / Harrods cluster (2025, GBP 270M to 440M per the Cyber Monitoring Centre) make the operational impact concrete. For CISOs, fraud teams, contact-center operators, and journalists, this is the canonical 2026 reference for what the voice channel actually does.
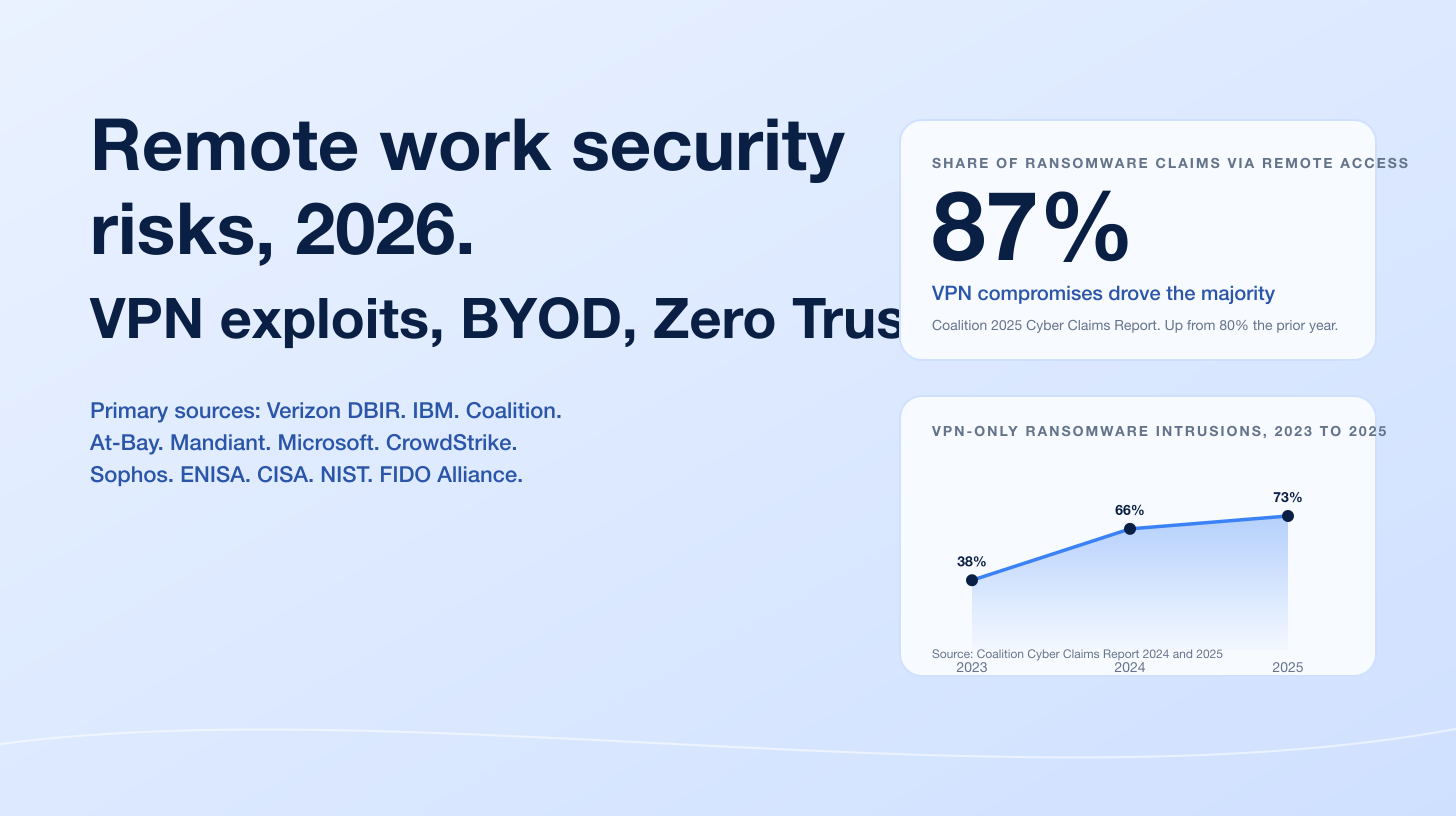
This post is the Stingrai research team's canonical 2026 reference for vishing activity. It assembles 80+ numeric claims from named primary publishers including CrowdStrike, Pindrop, Mandiant, Microsoft Threat Intelligence, the FBI Internet Crime Complaint Center, the Federal Communications Commission, the Federal Trade Commission Consumer Sentinel Network, the Cybersecurity and Infrastructure Security Agency, the US Department of Justice, MITRE ATT&CK, Truecaller, Hiya, Cofense, KnowBe4, the Sumsub Identity Fraud Report, the Verizon Data Breach Investigations Report, the UK Public Interest Research Group, and Anthropic Threat Intelligence. Lead data is full-year 2024 telemetry where a primary publisher has released it, with H1 2025 partial-year figures where useful and Q1 2026 reporting where it has been published; primary publishers have not yet released full-year 2026 reports as of April 2026. Every figure carries its source, year, and methodology window so any claim can be audited inline. This page is the voice-specific deep dive in the Stingrai social-engineering cluster; the broader phishing statistics 2026, the deepfake statistics 2026, the social engineering statistics 2026, and the SIM swap statistics 2026 cover adjacent surfaces.
TL;DR: 13 labeled key stats
CrowdStrike vishing growth, H1 to H2 2024: +442% (CrowdStrike 2025 Global Threat Report).
CrowdStrike H1 2025 vishing volume: already exceeded full-year 2024 (CrowdStrike 2025 Threat Hunting Report).
Mandiant M-Trends 2026 voice-phishing rank: #2 most common initial infection vector for 2025, present in 11% of Mandiant investigations where a vector could be identified (Help Net Security on M-Trends 2026).
Pindrop deepfake fraud growth 2024: +1,300% in deepfake fraud attempts, from 1 per month to 7 per day (Pindrop 2025 Voice Intelligence and Security Report).
Pindrop contact-center fraud exposure 2025: US$44.5B (Pindrop 2025 Voice Intelligence and Security Report).
FBI IC3 phishing/spoofing complaints 2024: 193,407 (largest complaint category), with US$70M in losses, a +274% YoY rise from US$18.7M (FBI IC3 2024 Internet Crime Report).
FBI IC3 BEC losses 2024: US$2.77B across 21,442 incidents (FBI IC3 2024 Internet Crime Report).
FBI IC3 tech-support fraud losses 2024: US$1.46B (FBI IC3 2024 Internet Crime Report).
FTC imposter scam losses 2024: US$2.95B, including US$789M in government-imposter scams (+US$171M YoY) (FTC Consumer Sentinel Network 2024 Data Book).
Hiya spam-call volume Q2 2025: 13.7 billion suspected spam calls flagged, ~150 million unwanted calls per day (Hiya Global Call Threat Report Q2 2025).
FCC STIR/SHAKEN deployment, September 28, 2025: 4,084 of 9,242 registered voice service providers fully implemented (~44%) (Robocall Mitigation Database).
M&S / Co-op / Harrods financial impact, April 2025: GBP 270M to 440M (US$363M to US$592M), classified by the Cyber Monitoring Centre as a single combined cyber event (Cyber Monitoring Centre via The Hacker News).
DOJ Buchanan plea, April 2026: Tyler Robert Buchanan ("Tylerb") pleaded guilty to wire fraud conspiracy and aggravated identity theft, admitted at least US$8M in stolen virtual currency, sentencing scheduled August 21, 2026 with a 22-year statutory maximum (Krebs on Security, April 2026).
Key takeaways
Voice is now a tier-1 initial-access vector, not a fallback. Mandiant's M-Trends 2026 report ranked voice phishing as the #2 most common initial infection vector for 2025. CrowdStrike's growth curve shows the same shape from a different angle: vishing in H1 2025 already exceeded full-year 2024, and the report projects vishing on track to double 2024's volume by year-end. The 2026 threat model that still treats email-only phishing as the dominant social engineering surface is already a year behind.
AI did not replace human-driven vishing; it amplified it. Pindrop's contact-center telemetry shows a +1,300% increase in deepfake fraud attempts in 2024 alongside the underlying live-human vishing volume. CrowdStrike attributes the 2024 surge to AI-augmented impersonation paired with traditional pretexting. The defensive implication is multi-stack: voice biometrics for anti-deepfake, behavioral analytics for live-human pretexting, runbooks for the human help desk that does not yet have either.
The help desk is the actual attack surface; SMS 2FA is the bypass. Every named 2023-2025 enterprise vishing breach (MGM, Caesars, Snowflake, M&S, Co-op) begins with a vishing call to a help desk impersonating an employee, followed by a password reset and an MFA bypass. Mandiant's M-Trends 2026 reported UNC3944 going from initial access to domain admin in roughly 40 minutes. Help-desk identity verification, runbooks, and out-of-band reauthentication on high-value resets are the controls that move the needle.
Regulatory progress is real but uneven. The FCC adopted FCC 23-95A in November 2023 to attack SIM swap and port-out fraud; the 2024 STIR/SHAKEN expansion targeted call-authentication gaps; Industry Traceback Group enforcement removed 1,203 voice service providers from the Robocall Mitigation Database in August 2025. The deployment data is more sobering: only ~44% of registered providers had fully implemented STIR/SHAKEN as of September 2025, and the count actually declined from the prior year (4,365 to 4,084) as enforcement removals tightened.
The dollar number is not the headline; the leverage is. FBI IC3 phishing/spoofing losses in 2024 totaled US$70M (small, by IC3 standards), but the same year saw US$2.77B in BEC losses, US$1.46B in tech-support fraud, US$2.95B in FTC-tracked imposter scams, and the Pindrop estimate of US$44.5B contact-center fraud exposure. Vishing is rarely the line item in the loss statement; it is the front half of the breach. The post-mortem categorizes the downstream theft, not the call.
Methodology
Sources used in this post include the CrowdStrike 2025 Global Threat Report (Feb 27, 2025) and the CrowdStrike 2025 Threat Hunting Report (covering Jul 2024 to Jun 2025); the Pindrop 2025 Voice Intelligence and Security Report (Jun 2025); the FBI 2024 Internet Crime Report (released Apr 2025) and the FBI IC3 BEC PSA240911; the FTC Consumer Sentinel Network 2024 Data Book (Mar 2025); the FCC Robocall Mitigation Database and the FCC TRACED Act 2024 Annual Report to Congress; the joint CISA / FBI / RCMP / ASD / AFP advisory AA23-320A (Nov 16, 2023; v2 Jul 29, 2025); Mandiant M-Trends 2026 (Mar 2026); Microsoft Threat Intelligence's Octo Tempest profile and the July 2025 multi-industry update; MITRE ATT&CK G1015; Truecaller's US 2024 report and April 2026 survey; the Hiya Global Call Threat Report Q2 2025; Cofense's Annual State of Email Security report; KnowBe4's Q1 2025 Phishing Report; the Sumsub Identity Fraud Report 2025-2026; the 2025 Verizon DBIR; the PIRG "Ringing in Our Fears 2025" report; DOJ press releases on the Council, Buchanan, and the November 2024 five-defendant indictment; SEC 8-K filings from MGM Resorts (Oct 5, 2023) and Caesars Entertainment (Sept 7, 2023); and the Anthropic Threat Intelligence GTG-1002 disclosure (Nov 14, 2025). Date cutoff: April 29, 2026. Statistics that could not be reached via a named primary publisher on at least one verification pass were dropped. Adjacent attack types (SMS-only smishing, deepfake video conference fraud, SIM swap mechanics) are covered in the linked sibling posts; this page covers vishing and voice-augmented attacks specifically.
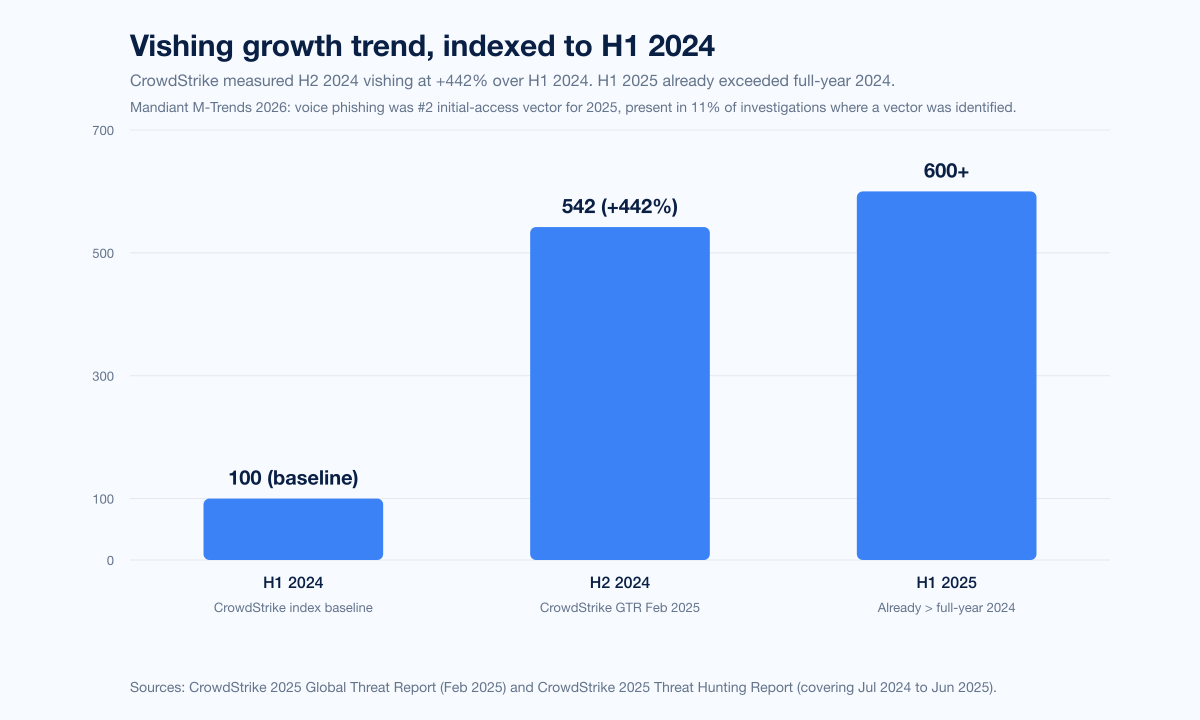
The CrowdStrike growth curve
The single most-cited vishing growth metric of the cycle comes from the CrowdStrike 2025 Global Threat Report, released February 27, 2025. The headline number: vishing activity rose 442% between H1 and H2 of 2024. CrowdStrike attributes the surge to "AI-driven phishing and impersonation tactics" paired with classical help-desk pretexting, and tracks at least three distinct eCrime clusters using the technique at scale: CURLY SPIDER, CHATTY SPIDER, and PLUMP SPIDER. CrowdStrike documented at least six distinct campaigns in which threat actors posing as IT support staff called targeted users to persuade them into establishing remote support sessions, and at least four campaigns that combined "spam bombing" (flooding targets with thousands of spam emails) with a follow-up vishing call claiming the spam indicated a malware infection requiring immediate IT assistance.
The follow-up CrowdStrike 2025 Threat Hunting Report (covering July 2024 to June 2025) extended the curve. Its framing: "vishing attacks in the first half of 2025 have already exceeded the total number seen in 2024," with voice phishing on track to double last year's volume by the end of 2025. CrowdStrike also noted that Scattered Spider resurged in 2025 with faster and more aggressive tradecraft, leveraging vishing and help desk impersonation to reset credentials, bypass multifactor authentication, and move laterally across SaaS and cloud environments.
Mandiant's M-Trends 2026 report, released March 2026, gave the same trend a different lens. Among investigations where a vector could be identified, voice phishing was the #2 most common initial infection vector for 2025, present in approximately 11% of Mandiant cases. UNC3944 in particular targeted help-desk staff by impersonating employees requesting password resets and multifactor authentication changes. Mandiant noted that the group used personally identifiable information scraped from public profiles to bypass identity-verification questions, and that initial access to domain administrator escalation often occurred in roughly 40 minutes. Mandiant's accompanying note that adversaries are "handing off access in 22 seconds" applies to access-broker handoff post-vishing.
The two reports converge from different vantage points (telemetry vs. incident response) on the same conclusion: voice-channel social engineering has overtaken email-only phishing as the leading edge of human-targeted intrusion in 2025.
Pindrop, contact centers, and deepfake voice
The cleanest published telemetry on the contact-center side is Pindrop's 2025 Voice Intelligence and Security Report, released June 2025. Pindrop is a US contact-center voice authentication and fraud-detection vendor; the report aggregates fraud telemetry across its enterprise customer base.
Headline numbers:
Deepfake fraud attempts rose more than +1,300% in 2024, jumping from an average of one per month to seven per day.
2.6M fraud events were tracked across the dataset.
Contact-center fraud reached its highest level in six years.
Deepfake-related fraud is projected +162% growth in 2025.
AI now drives 42.5% of fraud attempts, with nearly 1 in 3 considered successful.
Retail fraud rose +107% in 2024 and is projected to more than double again in 2025, reaching 1 in every 56 calls.
Contact centers face an estimated US$44.5B in fraud exposure in 2025, per Pindrop's blended-model projection across financial services, insurance, retail, and healthcare verticals.
Pindrop also published a Fortune 500 insurer case study in which the customer detected 97% of deepfake voice attempts after deploying the Pindrop Pulse anti-deepfake module. The 97% number is a vendor-published case study and is the only deepfake-detection efficacy figure we cite to a named primary publisher.
The deepfake voice fraud category overlaps with the broader deepfake fraud surface covered in Stingrai's deepfake statistics 2026 reference. The canonical voice-deepfake corporate case remains the Arup Hong Kong incident, in which a finance worker was tricked into 15 transfers totaling HK$200M (about US$25.6M) to five Hong Kong bank accounts after a video conference call in which every other participant, including the company's UK-based CFO, was AI-generated (Fortune, May 17 2024; CFO Dive). Arup confirmed no internal systems were compromised; the entire compromise occurred on the human side of a video call. The deepfake-statistics-2026 sibling post covers that incident in depth.
Sumsub's Identity Fraud Report 2025-2026 corroborates the deepfake escalation from a different vantage point. Sumsub reported that deepfakes accounted for 11% of global fraudulent activity in 2026, up from prior cycles. UK deepfake attempts rose +94% YoY. The Maldives experienced the largest absolute increase, with +2,100% YoY growth in deepfake attacks. Sumsub identified the top-five industries most affected by identity fraud in 2025 and 2026 as dating, online media, financial services, crypto, and professional services.
FBI IC3 2024: where vishing hides in the loss statement
The FBI 2024 Internet Crime Report, released April 2025, is the most-cited US victim-loss aggregate in the cycle. Vishing is rarely categorized as its own line; it is the front half of categories that get reported under the downstream loss type.
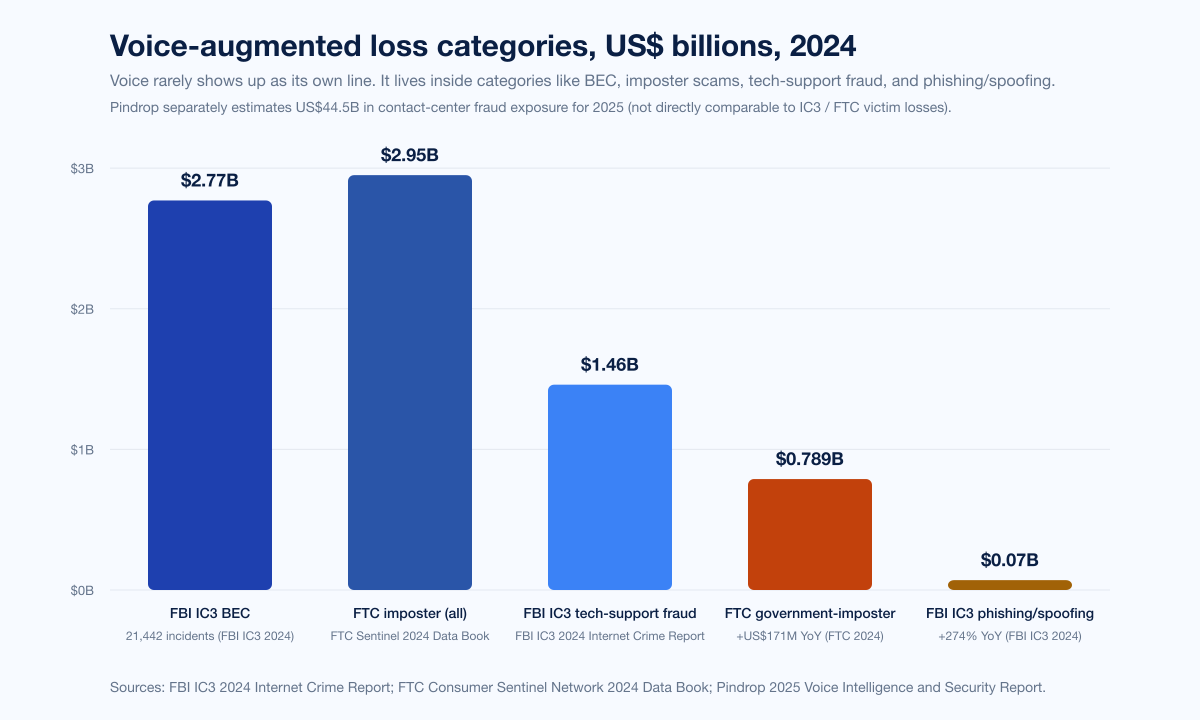
Top-line 2024 IC3 numbers:
Category | Complaints 2024 | Losses 2024 | Source |
|---|---|---|---|
Total cybercrime | 859,532 | US$16.6B (+33% YoY) | FBI IC3 2024 Annual Report |
Phishing/spoofing | 193,407 (largest by complaint) | ~US$70M (+274% YoY) | FBI IC3 2024 Annual Report |
Business email compromise | 21,442 | US$2.77B | FBI IC3 2024 Annual Report |
Tech-support fraud | undisclosed exact count | US$1.46B | FBI IC3 2024 Annual Report |
Cyber-enabled fraud (umbrella) | 333,981 | US$13.7B (~83% of total losses) | FBI IC3 2024 Annual Report |
Adults 60+ losses | 147,127 | nearly US$5B (+43% YoY) | FBI IC3 2024 Annual Report |
The phishing/spoofing line tells one story by itself. Complaint volume held the top spot at 193,407. Reported losses spiked from US$18.7M in 2023 to US$70M in 2024, a +274% jump, even as the IC3 phishing methodology continues to bucket some voice-channel pretexting under broader categories. The BEC line is the more important one for the voice channel: US$2.77B in 2024 alone, and the FBI IC3 BEC public service announcement PSA240911 reported nearly US$55.5B in cumulative worldwide BEC losses since 2013, with nearly US$8.5B reported to IC3 between 2022 and 2024 alone. BEC is increasingly multi-channel, with vishing as the verification step that closes the wire-fraud loop: an attacker who has compromised an email account calls the wire-transfer approver to "confirm" the request, in the approver's expected voice-channel pattern.
The tech-support fraud line (US$1.46B in 2024) is the most directly voice-channel-anchored IC3 category. Tech-support scams almost always begin with an inbound call (or a callback prompted by a fake security alert) and proceed through phone-mediated remote-access deployment. Adults 60+ filed 147,127 complaints with nearly US$5B in losses (+43% YoY), with the top complaint types reported by seniors being phishing/spoofing, tech support, extortion, and personal data breaches.
The IC3 dollar headline understates the voice channel because most named voice-driven incidents (FTX, MGM, Caesars, M&S) are reported under their downstream categories: cryptocurrency theft, ransomware, identity theft. Vishing rarely shows up as its own line; the breach lives in the loss statement under whatever happens after the call.
FTC imposter scams: where consumers feel the voice channel
The FTC Consumer Sentinel Network 2024 Data Book captures the consumer-side voice-channel impact more directly than IC3. Top-line 2024 numbers: 6.5 million consumer reports, US$12.5B in total reported fraud losses, imposter scams the largest category by complaint count with US$2.95B in losses, government imposter scams US$789M (+US$171M YoY). Phone calls were the second most common contact method for fraud reports, behind email.
The FTC's longitudinal data shows an interesting shift: comparing 2020 to 2023, phone-call-initiated scams declined as a share while text and email rose. That trend reversed direction in 2024 as the deepfake voice and Scattered Spider tradecraft surged: phone calls climbed back up as a contact method, and the average loss per phone-initiated scam in H1 2025 reached US$3,690, per the PIRG "Ringing in Our Fears 2025" compilation. PIRG also reported that money lost to scams that started with a phone call increased +16% from H1 2024 to H1 2025.
Truecaller, Hiya, and the call ecosystem
Truecaller's US Spam & Scam Report 2024 reported that 56,154,197 US adults (about 21% of US adults) lost money in a phone scam in 2023, with total US phone scam losses reaching US$25.4B. The average phone scam victim lost US$452.
Truecaller's April 2026 survey (released April 21, 2026) measured the downstream behavioral impact:
80% of Americans have ignored important calls out of fear of scams (up from 59% in 2024).
75% of respondents were targeted by a scam call or text in the past 12 months.
84% are more concerned about the threat than a year ago.
30% received a deepfake voice call impersonating a family member, celebrity, or political figure that felt more convincing than any prior scam.
The "ignore important calls" data point is important for legitimate-business call-completion economics: the same Truecaller survey-wave reported that scam-call fatigue is the dominant driver of unanswered legitimate calls.
Hiya's Global Call Threat Report Q2 2025 (and its preceding 2025 State of the Call wave) measured the volume side:
Hiya flagged 13.7 billion suspected spam calls in Q2 2025.
~150 million unwanted calls per day Q2 2025.
Q4 2024 unwanted-call total: 11.3B; Q1 2025: 12.5B; Q2 2025: 13.7B (continuous quarter-on-quarter growth).
80% of calls from unrecognized numbers go unanswered.
1 in 3 workers say their company has lost money because they could not connect by phone.
60% of sales professionals say they have lost a deal because of call-related issues.
The Hiya numbers and the Truecaller behavioral numbers together establish the trust-collapse layer underneath the headline vishing growth: the voice channel is being used more aggressively by attackers and trusted less by recipients, with measurable economic damage to legitimate enterprise callers.
The PIRG "Ringing in Our Fears 2025" report added monthly granularity: the monthly average of scam and telemarketing calls climbed from 2.14 billion per month in 2024 to 2.56 billion per month through September 2025, with about 57% of 2025 robocalls classified as scam or telemarketing.
STIR/SHAKEN deployment: closer to the floor than the ceiling
The Federal Communications Commission's STIR/SHAKEN caller-ID-authentication framework is the central US technical control against caller-ID spoofing. The FCC's Robocall Mitigation Database is the central registry. Voice service providers must certify whether and to what extent they have implemented STIR/SHAKEN.
Snapshot as of September 28, 2025:
9,242 voice service providers registered in the RMD.
4,084 fully implemented STIR/SHAKEN (~44% of registered).
4,365 fully implemented in the prior year: a decline of about 281 as enforcement removals tightened.
April 2021: RMD launched.
2025: New $10,000 fines for false RMD information; $1,000 for failure to keep information current; $100 RMD filing fee.
Enforcement action accelerated in 2025. The FCC Enforcement Bureau's Final Removal Order in August 2025 removed over 1,200 voice service providers from the Robocall Mitigation Database for failing to comply with updated RMD requirements. The Industry Traceback Group (the FCC-designated registered consortium under the TRACED Act) continued to identify foreign-originating providers and US gateway providers behind robocall traffic; the most recent published snapshot identified 82 foreign-based originating providers and 145 US gateway providers involved in robocalls.
Specific enforcement actions in 2024-2025 documented by the ITG include the suspension of Belthrough for transmitting prerecorded voice calls impersonating internet service providers, and the linkage of Ananya Traders to 298 tracebacks between June 2024 and May 2025, many involving brand-impersonation fraud.
The deployment data is the more sobering side of the STIR/SHAKEN picture. Caller-ID authentication is not yet a default property of US voice traffic; it is implemented end-to-end on roughly 44% of registered providers, with non-IP-network gaps still being closed via FCC FCC-25-76 and the April 2025 fact sheet on Closing the Non-IP Caller ID Authentication Gap. Even fully implemented STIR/SHAKEN does not block spoofing; it labels it. The downstream consumer-protection control (call labeling, blocking, or third-party call-screening apps) does the actual blocking.
Methods deep-dive: what vishing actually looks like in 2026
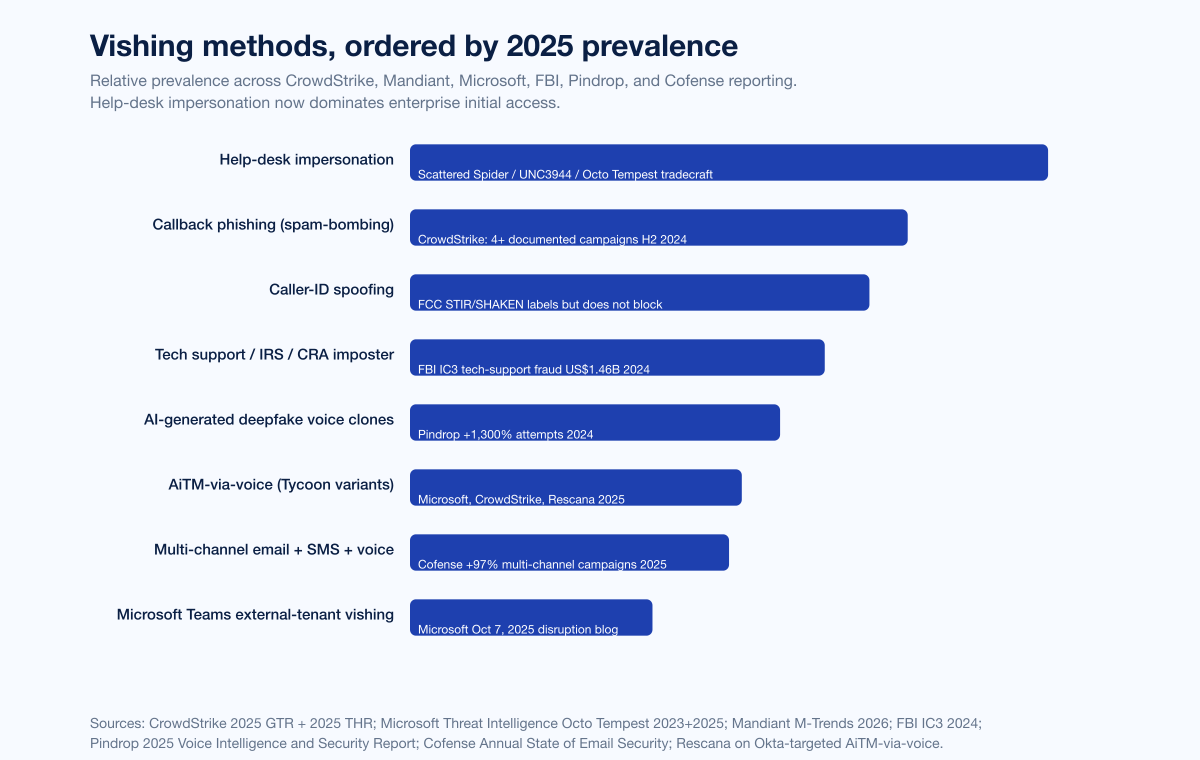
The 2024-2026 cycle's threat reports converge on a stable taxonomy of vishing methods. CrowdStrike, Microsoft, Mandiant, Cofense, Pindrop, and the FBI all describe the same patterns from different vantage points.
1. Caller-ID spoofing. The simplest layer. An attacker presents the calling line as a trusted number (a bank, the IRS, a corporate help desk, the executive's mobile). STIR/SHAKEN exists specifically to label this; deployment gaps mean it still works in roughly half of US voice paths.
2. Help-desk impersonation. The Scattered Spider playbook. The attacker calls an internal IT help desk pretending to be an employee whose details have been scraped from LinkedIn, the corporate directory, or a previously breached HR database. The pretext is a password reset, MFA reset, or new-device enrollment. Mandiant's M-Trends 2026 reported UNC3944 going from initial access via help-desk vishing to domain administrator privileges in roughly 40 minutes.
3. Callback phishing (spam-bombing). The CrowdStrike-documented technique in which the attacker sends thousands of legitimate-looking spam emails to a target, then calls or messages the target claiming the spam indicates a malware infection requiring immediate IT support, prompting the target to install remote-access tooling. CrowdStrike documented at least four campaigns using this technique in H2 2024.
4. AI-generated deepfake voice clones. Pindrop's +1,300% deepfake-fraud-attempt growth in 2024 is the headline for this technique. The most widely cited corporate case is Arup HK$200M (~US$25.6M, January 2024). Deepfake voice cloning paired with deepfake video is now affordable enough to deploy for high-value executive impersonation at scale; the Sumsub UK +94% YoY rise is the corroborating signal.
5. AiTM-via-voice (Tycoon variants). Microsoft and CrowdStrike both documented in 2025 a class of attacks in which the attacker calls the target while a custom adversary-in-the-middle phishing kit is harvesting the live OTP from a parallel session. The vishing call is the social-trust layer that gets the target to enter the OTP; the AiTM kit captures it. Rescana's Okta vishing analysis traced the technique to multiple threat groups primarily targeting fintech, wealth management, financial, and advisory sectors.
6. Tech-support / IRS / CRA imposter scams. The consumer-side workhorse. The FBI IC3 logged US$1.46B in tech-support fraud losses in 2024. The FTC logged US$789M in government imposter scams, with the IRS in the US, the CRA in Canada, and HMRC in the UK as the most-imitated agencies.
7. Microsoft Teams external-tenant vishing. The newest CrowdStrike-documented technique. Threat actors call from external Microsoft Teams tenants spoofed to look like internal IT support, exploiting Teams' default external-call permissions to reach employees through a trusted channel. Microsoft's October 7, 2025 disruption blog specifically targets this technique.
8. Multi-channel vishing. The vishing call is increasingly paired with email, SMS, and chat in a coordinated sequence. The Cofense 2025 Annual State of Email Security report reported multi-channel campaigns up +97% in 2025, and the Cofense Phishing Defense Center observed an average of 1 malicious email every 19 seconds throughout 2025. The voice call is no longer a standalone scheme; it is the verification layer in a multi-channel pretext.
Scattered Spider, Octo Tempest, and the named-campaign roster

The single threat actor that did more than any other to industrialize vishing as an enterprise-grade initial-access vector is Scattered Spider, also tracked as UNC3944, Octo Tempest, Storm-0875, Muddled Libra, Roasted 0ktapus, and Scatter Swine. The CISA AA23-320A advisory (originally November 16, 2023; updated v2 July 29, 2025) describes the group as native English-speaking and identifies individuals "primarily between the ages of 19 and 22 as of September 2023".
Microsoft's October 2023 Octo Tempest writeup and the July 2025 multi-industry update both centered on the group's vishing tradecraft: phone calls to help desks, MFA push bombing, and abuse of federated identity providers via tools like AADInternals. Microsoft's 2025 update specifically called out Octo Tempest impacting the airlines sector (recent), following prior retail, food services, hospitality, and insurance activity between April and July 2025.
The named-incident roster:
MGM Resorts (September 11, 2023). SEC 8-K October 5, 2023 disclosed approximately 10 days of system downtime and an estimated US$100M financial impact. Initial access by Scattered Spider via help-desk vishing impersonating an MGM employee whose details had been pulled from LinkedIn.
Caesars Entertainment (August to September 2023). SEC 8-K September 7, 2023 disclosed a "social engineering attack on an outsourced IT support vendor" and a paid ransom of approximately US$15M out of a US$30M demand. The Caesars filing did not name Scattered Spider; CISA, Mandiant, Recorded Future, and the DOJ all attribute the intrusion to the group.
Snowflake / UNC5537 (Mid 2024). Approximately 165 organizations targeted through stolen credentials harvested from infostealer infections dating back as far as 2020. Affected companies included AT&T, Ticketmaster / Live Nation, Santander Bank, LendingTree, Advance Auto Parts, Neiman Marcus, and Bausch Health. Over 80% of compromised accounts had prior credential exposure, and the impacted accounts lacked MFA. Connor Riley Moucka (aliases Waifu, Judische, Ellyel8) was arrested in Kitchener, Ontario, Canada on October 30, 2024.
SEC X account hijack (January 9, 2024). Eric Council Jr. SIM-swapped the phone number associated with the @SECGov X account, which lacked 2FA, and posted a false claim that the SEC had approved spot Bitcoin ETFs. Bitcoin moved more than US$1,000 up before the SEC corrected the post and prices reversed by more than US$2,000. Council pleaded guilty in February 2025 and was sentenced to 14 months in federal prison on May 16, 2025; he forfeited US$50,000 (the exact amount he received for performing SIM swaps).
M&S / Co-op / Harrods (April 2025). The UK Cyber Monitoring Centre classified the cluster as a "single combined cyber event" with a financial impact of GBP 270M to GBP 440M (US$363M to US$592M). M&S Chairman Archie Norman publicly confirmed that attackers impersonated an M&S employee and called the service desk run by a third party, who carried out a password reset for them. With those credentials, attackers exfiltrated the NTDS.dit Active Directory database, then deployed DragonForce ransomware against M&S's VMware ESXi hosts on April 24, 2025, encrypting virtual machines that supported e-commerce, payment processing, and logistics applications. UK police arrested four suspects in July 2025 in connection with the cluster.
DOJ enforcement, November 20, 2024. The US Attorney's Office for the Central District of California unsealed criminal charges against five alleged Scattered Spider members: Tyler Robert Buchanan (24, Dundee, Scotland), Ahmed Hossam Eldin Elbadawy (24, College Station, Texas), Joel Martin Evans (26, Jacksonville, North Carolina), Evans Onyeaka Osiebo (21, Dallas, Texas), and Noah Michael Urban (21, Palm Coast, Florida). Urban was sentenced to 10 years federal prison plus US$13M in restitution in 2025.
Buchanan ("Tylerb") plea, April 2026. Krebs on Security reported on April 21, 2026 that Buchanan pleaded guilty to conspiracy to commit wire fraud and aggravated identity theft. Buchanan admitted his role in text-message phishing attacks in summer 2022 that allowed Scattered Spider to compromise at least a dozen major technology companies and steal tens of millions in cryptocurrency from investors. Per the plea, the scheme involved theft of at least US$8M in virtual currency from individual victims located throughout the United States. Buchanan's sentencing is scheduled for August 21, 2026, with a statutory maximum of 22 years in federal prison.
Anthropic and the AI-orchestrated layer
The most discussed forward-looking data point of late 2025 is Anthropic's November 14, 2025 disclosure of the GTG-1002 campaign, described as the first reported AI-orchestrated cyber espionage campaign at scale and attributed to a China-linked state-sponsored cluster. Key disclosed numbers: ~30 organizations targeted across technology, finance, chemicals, and government; 80-90% of tactical work handled by the Claude Code-driven agentic framework; and a Phase 1 step in which operators socially engineered the AI itself by claiming to be defenders conducting authorized testing.
GTG-1002 is not a vishing-first campaign, but the social engineering primitive (talking the AI into believing it was a defender) maps directly onto the social-trust layer that human-targeted vishing exploits. The 2026-2027 trajectory most threat reports project is AI-orchestrated multi-stage campaigns where vishing is one of multiple agentic surfaces rather than a standalone human-driven attack.
The Verizon 2025 DBIR placed broader social engineering in context: among breaches involving social engineering, the report measured phishing at 57% and pretexting at 30%. The DBIR does not yet separate voice-channel pretexting as its own line; the +442% CrowdStrike growth and the Mandiant M-Trends 2026 #2-vector ranking suggest the 2026 DBIR will likely need to.
Defender stack: what works against vishing in 2026

The 2026 vishing defender stack rests on five layers that have to ship together. Any one layer in isolation gets bypassed; the combination is hard to defeat in the time budget a Scattered Spider operator works with.
1. Call authentication. STIR/SHAKEN at carrier level, plus enterprise call-screening that consumes the attestation header. The FCC RMD enforcement actions of 2025 are pushing the deployment ceiling up; the consumer-protection win is downstream call labeling, in-app warnings, and aggressive blocking of unattested traffic. Enterprise voice-paths should mandate STIR/SHAKEN attestation level A end-to-end and treat unattested inbound voice as default-untrusted.
2. Voice biometrics and behavioral analytics. Pindrop and adjacent vendors offer voice biometrics (passive voiceprint matching across calls), liveness detection, anti-deepfake voice models, and behavioral risk signals (call-cadence patterns, device-fingerprint anomalies, geolocation mismatches). The Pindrop Fortune 500 insurer case study reported 97% deepfake-detection rate after deployment. Voice biometrics is the most direct counter to AI-generated voice cloning at the call-authentication layer.
3. Identity-verification runbooks for the help desk. This is the highest-leverage control for the Scattered Spider class of attack. Help-desk callers verify identity through a corporate identity provider out-of-band channel, never through phone-based callback to a number on file, and never by accepting biographical data, recent payment numbers, or call detail records as authentication. Microsoft, CISA, and Mandiant all explicitly recommend out-of-band IDP-mediated verification on every reset that touches a privileged account or any account with access to sensitive data.
4. Multi-factor reauthentication on sensitive operations. Wire transfers, password resets, MFA-method changes, device enrollment, executive-account access, and any "urgent CFO" workflow require fresh, phishing-resistant authentication (FIDO2 / passkey) before completion. The NIST SP 800-63B Rev 4 guidance on restricted authenticators applies directly: SMS one-time passcodes are acceptable as a fallback factor only and should not gate high-value operations.
5. Vishing simulation training. KnowBe4's Q1 2025 Phishing Report reported a global average baseline phish-prone percentage of 33.1% across organizations before training, with internal-communications impersonation at 60.7% of clicks and HR-themed lures at 49.7% in simulated campaigns. KnowBe4 also reported that security training reduces global phishing click rates by 86% at scale. The same telemetry pattern applies to vishing: simulated vishing call campaigns, runbook drills, and tabletop exercises against the Octo Tempest tradecraft are how help-desk staff (including outsourced BPO providers) build the muscle memory to recognize the pretext call before the password reset.
For organizations evaluating their voice-channel posture in 2026: the highest-leverage exercise is a red team scoped specifically against the help-desk identity-verification flow, modeled on the Octo Tempest tradecraft. Stingrai's adversary simulation engagements and PTaaS cover this scope; the adversary simulation in telecom case study walks through one such engagement in detail.
What this means for defenders
Move help-desk identity verification to an out-of-band IDP channel before 2026 ends. Every named 2023-2025 enterprise vishing breach (MGM, Caesars, Snowflake, M&S, Co-op) begins with a help-desk vishing call. The technical control that breaks the pattern is moving the identity-verification step out of the voice channel entirely, into the corporate IDP. The cost is process change, not technology.
Treat AI-driven voice cloning as a present threat, not a future threat. Pindrop's +1,300% deepfake-fraud-attempt growth in 2024 and Sumsub's UK +94% YoY signal converge on the same conclusion: high-value executives are voice-cloneable today using freely available models trained on public audio (earnings calls, conference talks, podcast interviews). The countermeasure is a callback verification policy that does not rely on the voice match alone, and ideally voice-biometrics at the contact-center perimeter.
Watch the multi-channel pattern, not the single-call pattern. Cofense's +97% multi-channel-campaign growth means the standalone vishing call is increasingly the verification layer in a coordinated email + SMS + voice sequence. Detection that runs on a single channel alone will miss the coordination signal. Cross-channel telemetry into one fraud platform is the architecture that wins.
Take the FCC STIR/SHAKEN deployment data seriously. Only ~44% of registered voice service providers had fully implemented STIR/SHAKEN as of September 2025, and the count actually declined year-over-year as enforcement removals tightened. Until deployment is closer to the ceiling, enterprise voice-paths should treat unattested inbound voice as default-untrusted and require attested-A-level traffic for any business-process flow.
Scope a help-desk vishing red team for 2026. A live-fire exercise that calls the help desk, attempts a password reset on a privileged account, and measures the time-to-detection and time-to-block is the single highest-leverage assessment an enterprise can run in 2026 against this threat. The MGM, Caesars, Snowflake, and M&S post-mortems are all blueprints.
Frequently asked questions
Who is the most-cited primary publisher for vishing volume in 2026?
CrowdStrike and Mandiant are the most-cited sources. CrowdStrike's 2025 Global Threat Report logged a +442% rise in vishing activity between H1 and H2 2024; the follow-up CrowdStrike 2025 Threat Hunting Report reported H1 2025 vishing already exceeded full-year 2024. Mandiant's M-Trends 2026 ranked voice phishing as the #2 most common initial infection vector for 2025, present in 11% of investigations where a vector could be identified. Pindrop is the most-cited source for contact-center voice telemetry, with the +1,300% deepfake-fraud-attempt growth metric in 2024.
How big is the vishing problem in dollar terms?
The voice channel is rarely a standalone line in primary publisher loss statements; it is the front half of categories that get reported under their downstream loss type. The FBI IC3 logged US$70M in phishing/spoofing losses in 2024 (+274% YoY), US$2.77B in BEC losses, and US$1.46B in tech-support fraud. The FTC Consumer Sentinel Network logged US$2.95B in imposter scams in 2024, including US$789M in government imposter scams (+US$171M YoY). Pindrop estimates US$44.5B in contact-center fraud exposure for 2025 across financial services, insurance, retail, and healthcare. These numbers are not additive (different methodologies and overlapping populations) but they converge on a multi-billion-dollar voice-channel impact in 2024-2025.
What is the largest deepfake voice fraud incident on record?
The Arup Hong Kong incident is the largest publicly attributed deepfake-driven loss in a corporate setting. A finance worker in Arup's Hong Kong office made 15 transfers totaling HK$200M (about US$25.6M) to five Hong Kong bank accounts after a video conference call in which every other participant, including the company's UK-based CFO, was AI-generated (Fortune, May 17 2024; CFO Dive). Arup confirmed no internal systems were compromised; the entire compromise occurred on the human side of the video call. The deepfake voice channel as a category is covered in Stingrai's deepfake statistics 2026 reference.
How does Scattered Spider use vishing?
Scattered Spider (also tracked as UNC3944, Octo Tempest, Storm-0875, Muddled Libra) calls internal IT help desks impersonating employees whose details have been scraped from public profiles, requests a password reset or MFA-method change, defeats remaining MFA via push bombing or SMS interception, and pivots to identity infrastructure. Mandiant's M-Trends 2026 reported UNC3944 going from initial access via help-desk vishing to domain administrator privileges in roughly 40 minutes. Named victims include MGM Resorts (~US$100M, 2023), Caesars (US$15M ransom, 2023), Snowflake (~165 victims, 2024), and the M&S / Co-op / Harrods cluster (GBP 270M to 440M, 2025). CISA AA23-320A is the canonical advisory; the v2 update was published July 29, 2025.
What did Tyler Buchanan ("Tylerb") admit in his April 2026 plea?
Tyler Robert Buchanan, 24, of Dundee, Scotland, pleaded guilty in the Central District of California in April 2026 to conspiracy to commit wire fraud and aggravated identity theft. Buchanan admitted his role in text-message phishing attacks in summer 2022 that compromised at least a dozen major technology companies and enabled tens of millions in cryptocurrency theft. The plea recorded at least US$8M in stolen virtual currency from individual victims. Buchanan's sentencing is scheduled for August 21, 2026, with a statutory maximum of 22 years in federal prison. Buchanan was originally arrested in Palma de Mallorca in June 2024 and extradited to the United States in April 2025.
How many US voice service providers fully implement STIR/SHAKEN?
As of September 28, 2025, 9,242 voice service providers were registered in the FCC Robocall Mitigation Database, of which 4,084 (~44%) had completely implemented STIR/SHAKEN. The fully-implemented count actually declined from 4,365 in the prior year as enforcement removals tightened. The FCC Enforcement Bureau's August 2025 Final Removal Order removed over 1,200 voice service providers from the database for non-compliance with updated requirements. The non-IP-network gap is being closed via FCC FCC-25-76 and the April 2025 fact sheet.
How much have spam and scam calls grown?
Hiya flagged 13.7 billion suspected spam calls in Q2 2025, roughly 150 million unwanted calls per day. The progression: Q4 2024 11.3B unwanted calls; Q1 2025 12.5B; Q2 2025 13.7B, continuous quarter-over-quarter growth. The PIRG "Ringing in Our Fears 2025" report reported the monthly average of scam and telemarketing calls rising from 2.14 billion per month in 2024 to 2.56 billion per month through September 2025, with about 57% of 2025 robocalls classified as scam or telemarketing.
What is callback phishing or "spam bombing"?
Callback phishing is a CrowdStrike-documented vishing technique. The attacker first sends thousands of legitimate-looking spam emails to a target ("spam bombing") to trigger the target's inbox-filter alerts. The attacker then calls or messages the target claiming the spam indicates a malware infection requiring immediate IT support, and prompts the target to install remote-access tooling. CrowdStrike documented at least four campaigns using this technique in H2 2024, frequently combined with Microsoft Teams calls from external tenants impersonating internal IT support.
How much do US adults lose to phone scams?
Per Truecaller's US Spam & Scam Report 2024, 56,154,197 US adults (about 21% of US adults) lost money in a phone scam in 2023, with total US phone scam losses reaching US$25.4B and an average phone scam victim losing US$452. The PIRG aggregation reported average losses among those who lost money to phone-initiated scams at US$3,690 in H1 2025, a number that captures the higher-loss tail more directly than the Truecaller average.
What is the most effective single defense against vishing?
The single highest-leverage defense for enterprises is moving help-desk identity verification out of the voice channel entirely and into a corporate identity provider's out-of-band verification flow. Every named 2023-2025 enterprise vishing breach (MGM, Caesars, Snowflake, M&S, Co-op) begins with a vishing call to a help desk, followed by a password reset and an MFA bypass. Microsoft, CISA, and Mandiant all explicitly recommend IDP-mediated verification on every reset that touches a privileged account. Voice biometrics, callback verification, and KnowBe4-style vishing simulation training are layered controls; the IDP-out-of-band step is the one that breaks the Scattered Spider tradecraft most directly.
How does this differ from Stingrai's phishing statistics 2026 page?
Stingrai's phishing statistics 2026 is the umbrella reference covering email phishing, smishing (SMS), QR-code phishing, and voice phishing as one category across many. This page is the voice-only deep dive: the +442% CrowdStrike growth, Pindrop deepfake telemetry, FCC STIR/SHAKEN deployment, and the Scattered Spider help-desk-vishing tradecraft. Adjacent: deepfake statistics 2026 for the voice-deepfake and video-deepfake fraud category, social engineering statistics 2026 for the umbrella, and SIM swap statistics 2026 for the carrier-side SMS-2FA-bypass mechanic that Scattered Spider operators pair with the vishing call.
What should organizations do today to mitigate vishing risk?
Move every privileged-account password reset and MFA-method-change request out of phone-based identity verification, into a corporate IDP out-of-band flow. Require fresh, phishing-resistant authentication (FIDO2 / passkey) on wire transfers, MFA method changes, executive-account access, and any "urgent CFO" workflow. Deploy voice biometrics at the contact-center perimeter for high-value flows. Mandate STIR/SHAKEN attestation level A on all enterprise voice-paths and treat unattested inbound voice as default-untrusted. Run simulated vishing campaigns and tabletop exercises against the Octo Tempest tradecraft on a quarterly cadence. Stingrai's adversary simulation services cover this scope.
References
CrowdStrike. 2025 Global Threat Report. Released February 27, 2025. https://www.crowdstrike.com/en-us/blog/crowdstrike-2025-global-threat-report-findings/. Source for the +442% H1-to-H2 2024 vishing growth metric, eCrime cluster attribution (CURLY SPIDER, CHATTY SPIDER, PLUMP SPIDER), the spam-bombing-plus-vishing campaign count, and the Microsoft Teams external-tenant vishing technique.
CrowdStrike. 2025 Threat Hunting Report. August 2025 (covers July 2024 to June 2025). https://www.crowdstrike.com/en-us/blog/crowdstrike-2025-threat-hunting-report-ai-weapon-target/. Source for the H1 2025 vishing already exceeding full-year 2024 metric and the projection of vishing on track to double 2024 by year-end.
Pindrop. 2025 Voice Intelligence and Security Report. Released June 2025. https://www.pindrop.com/research/report/voice-intelligence-security-report/. Source for the +1,300% deepfake fraud growth metric, the 2.6M tracked fraud events, the US$44.5B contact-center fraud exposure, the AI-drives-42.5%-of-fraud number, and the retail-fraud progression.
Pindrop. Fortune 500 Insurer Detects 97% of Deepfakes and Stops Synthetic Voice Attacks. https://www.pindrop.com/research/case-study/insurer-detects-deepfakes-synthetic-voice-attacks-pindrop-pulse/. Vendor-published case study cited as the only deepfake-detection efficacy figure anchored to a named primary publisher.
Federal Bureau of Investigation, Internet Crime Complaint Center. 2024 Internet Crime Report. Released April 2025. https://www.ic3.gov/AnnualReport/Reports/2024_IC3Report.pdf. Source for the 859,532 complaints, US$16.6B total losses, 193,407 phishing/spoofing complaints, US$70M phishing/spoofing losses, US$2.77B BEC losses across 21,442 incidents, US$1.46B tech-support fraud losses, and the elder-fraud line.
Federal Bureau of Investigation, Internet Crime Complaint Center. PSA240911: Business Email Compromise: The US$55 Billion Scam. September 11, 2024. https://www.ic3.gov/PSA/2024/PSA240911. Source for the cumulative worldwide BEC US$55.5B figure and the 2022-2024 IC3 BEC US$8.5B aggregate.
Federal Trade Commission, Consumer Sentinel Network. 2024 Data Book. Released March 2025. https://www.ftc.gov/system/files/ftc_gov/pdf/csn-annual-data-book-2024.pdf. Source for the 6.5M consumer reports, US$12.5B fraud losses, US$2.95B imposter-scam losses, US$789M government-imposter losses, and the contact-method ranking.
Federal Communications Commission. Robocall Mitigation Database. https://www.fcc.gov/robocall-mitigation-database. Source for the 9,242 registered voice service providers and the 4,084 fully implemented STIR/SHAKEN figures (snapshot September 28, 2025).
Federal Communications Commission. FCC 25-76: Closing the Non-IP Caller ID Authentication Gap. April 7, 2025. https://docs.fcc.gov/public/attachments/FCC-25-76A1.pdf. Source for the non-IP-network STIR/SHAKEN gap-closing rulemaking.
Federal Communications Commission. TRACED Act 2024 Annual Report to Congress. Released January 2026. https://docs.fcc.gov/public/attachments/DA-25-1100A1.pdf. Source for the Industry Traceback Group consortium designation and 2024 traceback-data summary.
Federal Communications Commission, Industry Traceback Group. Resources and Public Notices. https://tracebacks.org/resources/. Source for ITG-published traceback statistics, foreign-originating-provider counts, and US-gateway-provider counts.
Cybersecurity and Infrastructure Security Agency. Joint Cybersecurity Advisory AA23-320A: Scattered Spider. Original November 16, 2023; updated v2 July 29, 2025. https://www.cisa.gov/news-events/cybersecurity-advisories/aa23-320a. Joint CISA / FBI / RCMP / ASD / AFP advisory describing Scattered Spider tradecraft, including help-desk vishing, MFA push bombing, and SIM swap.
Mandiant (Google Cloud). M-Trends 2026. Released March 2026 (summarized via Help Net Security). https://www.helpnetsecurity.com/2026/03/24/mandiant-m-trends-2026-report/. Source for voice phishing as the #2 most common initial infection vector for 2025, the 11% prevalence figure, and the UNC3944 40-minute initial-access-to-domain-admin metric.
Mandiant / Google Cloud. Defending Against UNC3944: Cybercrime Hardening Guidance from the Frontlines. https://cloud.google.com/blog/topics/threat-intelligence/unc3944-proactive-hardening-recommendations. Source for the help-desk hardening recommendations.
Microsoft Threat Intelligence. Octo Tempest crosses boundaries to facilitate extortion, encryption, and destruction. October 25, 2023. https://www.microsoft.com/en-us/security/blog/2023/10/25/octo-tempest-crosses-boundaries-to-facilitate-extortion-encryption-and-destruction/. Microsoft's profile of the Storm-0875 / Octo Tempest cluster and its vishing tradecraft.
Microsoft Threat Intelligence. Protecting customers from Octo Tempest attacks across multiple industries. July 16, 2025. https://www.microsoft.com/en-us/security/blog/2025/07/16/protecting-customers-from-octo-tempest-attacks-across-multiple-industries/. Update covering the airline, retail, food services, hospitality, and insurance sector activity through July 2025.
Microsoft Threat Intelligence. Disrupting threats targeting Microsoft Teams. October 7, 2025. https://www.microsoft.com/en-us/security/blog/2025/10/07/disrupting-threats-targeting-microsoft-teams/. Microsoft's disruption write-up covering external-tenant vishing via Teams.
MITRE ATT&CK. Group G1015: Scattered Spider. https://attack.mitre.org/groups/G1015/. Adversary group profile covering Roasted 0ktapus, Octo Tempest, Storm-0875, UNC3944, Muddled Libra, and Scatter Swine aliases.
Truecaller. US Spam and Scam Report. March 11, 2024. https://www.businesswire.com/news/home/20240311681922/en/. Source for the 56,154,197 US-adult phone-scam-victim figure, the US$25.4B 2023 US loss total, and the US$452 average victim loss.
Truecaller. 80% of Americans Ignore Important Calls Out of Fear of Scams. April 21, 2026. https://www.globenewswire.com/news-release/2026/04/21/3277990/0/en/80-of-Americans-Ignore-Important-Calls-Out-of-Fear-of-Scams-New-Truecaller-Survey-Finds.html. Source for the 80%-ignore-calls metric, the 75%-targeted figure, and the 30%-deepfake-voice-call experience figure.
Hiya. Global Call Threat Report Q2 2025. https://www.hiya.com/global-call-threat-report. Source for the 13.7 billion suspected spam calls Q2 2025, the 150-million-unwanted-calls-per-day figure, and the 11.3B-to-13.7B quarter-over-quarter progression.
Hiya. 2025 State of the Call Report. https://www.hiya.com/resources. Source for the 80%-unanswered-unrecognized-numbers figure and the sales-deal-loss telemetry.
Cofense. Annual State of Email Security Report. https://cofense.com/annualreport. Source for the 1-malicious-email-every-19-seconds Cofense Phishing Defense Center observation and the +97% multi-channel-campaign growth metric.
KnowBe4. Q1 2025 Phishing Report. https://www.knowbe4.com/press/knowbe4-releases-q1-2025-phishing-report-with-internal-communications-dominating. Source for the 33.1% global average baseline phish-prone percentage, the 60.7% internal-communications-impersonation click rate, and the 49.7% HR-themed click rate.
KnowBe4. Security Training Reduces Global Phishing Click Rates by 86%. https://www.knowbe4.com/press/knowbe4-report-reveals-security-training-reduces-global-phishing-click-rates-by-86. Source for the 86% click-rate-reduction metric.
Sumsub. Identity Fraud Report 2025-2026. Released October 2025. https://sumsub.com/fraud-report-2025/. Source for the 11% deepfake-share-of-fraudulent-activity-2026 figure, the UK +94% deepfake-attempts metric, the Maldives +2,100% YoY metric, and the top-5-affected-industries list.
Verizon. 2025 Data Breach Investigations Report. https://www.verizon.com/business/resources/T16f/reports/2025-dbir-data-breach-investigations-report.pdf. Source for phishing 57% / pretexting 30% social-engineering breakdown and the 30%-credential-abuse / 23%-social-actions breach-share figures.
Public Interest Research Group. Ringing in Our Fears 2025: Robocalls hit 6-year high. https://pirg.org/edfund/resources/ringing-in-our-fears-2025-robocalls-hit-6-year-high/. Source for the 2.14B-per-month-2024 to 2.56B-per-month-Sept-2025 progression, the 57%-scam-or-telemarketing share, the +16%-phone-initiated-scam-loss-growth-H1-2024-to-H1-2025, and the US$3,690 average loss.
United States Department of Justice, US Attorney's Office for the Central District of California. Five Defendants Charged Federally for Running Scheme that Stole Millions from Victims' Bank Accounts. November 20, 2024. https://www.justice.gov/usao-cdca/pr/five-defendants-charged-federally-running-scheme-stole-millions-victims-bank-accounts. Source for the five-defendant Scattered Spider indictment and the Buchanan, Elbadawy, Evans, Osiebo, and Urban defendant list.
United States Department of Justice, Office of Public Affairs. Alabama Man Sentenced to 14 Months in Connection with Securities and Exchange Commission X Hack that Spiked Bitcoin Prices. May 16, 2025. https://www.justice.gov/opa/pr/alabama-man-sentenced-14-months-connection-securities-and-exchange-commission-x-hack-spiked. Source for the Eric Council Jr. 14-month sentence and the US$50,000 forfeiture.
Krebs on Security. 'Scattered Spider' Member 'Tylerb' Pleads Guilty. April 2026. https://krebsonsecurity.com/2026/04/scattered-spider-member-tylerb-pleads-guilty/. Court-record corroboration for the Buchanan April 2026 plea, the US$8M figure, the August 21, 2026 sentencing date, and the 22-year statutory maximum.
Anthropic Threat Intelligence. Disrupting the first reported AI-orchestrated cyber espionage campaign. November 14, 2025. https://assets.anthropic.com/m/ec212e6566a0d47/original/Disrupting-the-first-reported-AI-orchestrated-cyber-espionage-campaign.pdf. Source for the GTG-1002 disclosure, the ~30-organizations-targeted figure, the 80-90%-tactical-work-handled-by-AI metric, and the Phase-1-social-engineering-of-the-AI framing.
Cyber Monitoring Centre via The Hacker News. Four Arrested in £440M Cyber Attack on Marks & Spencer, Co-op, and Harrods. July 2025. https://thehackernews.com/2025/07/four-arrested-in-440m-cyber-attack-on.html. Source for the GBP 270M to GBP 440M financial-impact range and the four-suspect arrest count.
The Register. British Scattered Spider hacker pleads guilty to crypto theft charges. April 2026. https://www.theregister.com/2026/04/20/scattered_spider_linked_scot_plead_guilty/. Independent reporting on the Buchanan April 2026 plea.
Fortune. A deepfake 'CFO' tricked British design firm Arup in $25 million fraud. May 17, 2024. https://fortune.com/europe/2024/05/17/arup-deepfake-fraud-scam-victim-hong-kong-25-million-cfo/. Source for the Arup HK$200M (~US$25.6M) deepfake-CFO incident.
CFO Dive. Scammers siphon $25M from engineering firm Arup via AI deepfake 'CFO'. May 2024. https://www.cfodive.com/news/scammers-siphon-25m-engineering-firm-arup-deepfake-cfo-ai/716501/. Corroborating reporting on Arup.
Snowflake breach reporting. Wikipedia summary with primary sources. https://en.wikipedia.org/wiki/Snowflake_data_breach. Aggregator for the ~165 victims, AT&T / Ticketmaster / Santander / LendingTree / Advance Auto Parts named victims, the 80%+-prior-credential-exposure figure, and the Connor Riley Moucka October 30, 2024 arrest.
MGM Resorts International. Form 8-K, Item 8.01. Filed October 5, 2023. SEC EDGAR. Source for approximately ten days of system downtime and US$100M financial impact disclosure.
Caesars Entertainment Inc. Form 8-K, Item 1.05. Filed September 7, 2023. SEC EDGAR. Source for the US$15M ransom payment of a US$30M demand and the outsourced-IT-support-vendor social engineering reference.
Rescana. Okta SSO Accounts Targeted by Sophisticated Vishing and Adversary-in-the-Middle (AiTM) Phishing Attacks. https://www.rescana.com/post/okta-sso-accounts-targeted-by-sophisticated-vishing-and-adversary-in-the-middle-aitm-phishing-atta. Source for the AiTM-via-voice campaign attribution to multiple threat groups targeting fintech, wealth management, financial, and advisory sectors.