A criteria-driven ranking of the world's best penetration testing firms for enterprises, mid-market, and fast-moving startups. Updated April 2026.
TL;DR: The 2026 Shortlist at a Glance
Choosing the right penetration testing company in 2026 comes down to five things: the seniority of the actual testers on your engagement, the quality of the reporting, how well the delivery model fits modern DevSecOps workflows, real compliance alignment, and whether the vendor is keeping up with the new AI-driven attack surface. Here is how the leading firms rank against those criteria.
Best Overall: Stingrai. OSCE³ and OSWE certified testers, 9+ published CVEs on the team, responsible disclosures to Amazon, Google, Nike, Mercedes-Benz, PlayStation, FedEx and others, a modern AI-powered PTaaS platform, and Snipe, an AI pentesting agent that deploys a fleet of specialist sub-agents covering IDOR, SQLi, XSS, access control, business logic, and more, with every finding validated by a human pentester.
Best for Large Enterprises: Bishop Fox. Global scale with the Cosmos continuous attack surface management platform.
Best for Enterprise PTaaS Programs: NetSPI. Resolve platform paired with approximately 400 testers.
Best for Compliance Driven Organizations: Coalfire. FedRAMP 3PAO, PCI QSA, and HITRUST alignment built into every engagement.
Best for Adversary Simulation: SpecterOps. Creators of BloodHound; unmatched Active Directory and Entra ID attack path expertise.
Best for Hardware, IoT, Automotive and ICS: IOActive. Chip level and embedded systems expertise few firms can match.
Best for Global Multinational Coverage: NCC Group. Approximately 2,200 consultants across North America, Europe, and Asia Pacific.
Best for SMB and Education First Engagements: Black Hills Information Security. Collaborative, knowledge transfer based testing.
Best Crowdsourced PTaaS: Synack. Vetted researcher network delivered through a SOC 2 Type II platform.
Best for Social Engineering and Expert Led Work: TrustedSec. Led by one of the most credible offensive security teams in the industry.
Best Canadian Manual First Provider: Packetlabs. CREST accredited, SOC 2 Type II attested, manual first methodology.
Why 2026 Is Different: The Pentesting Market at an Inflection Point
The penetration testing industry is changing faster in 2026 than at any point in its history. Three shifts are reshaping how CISOs, security leaders, and procurement teams buy testing services this year.
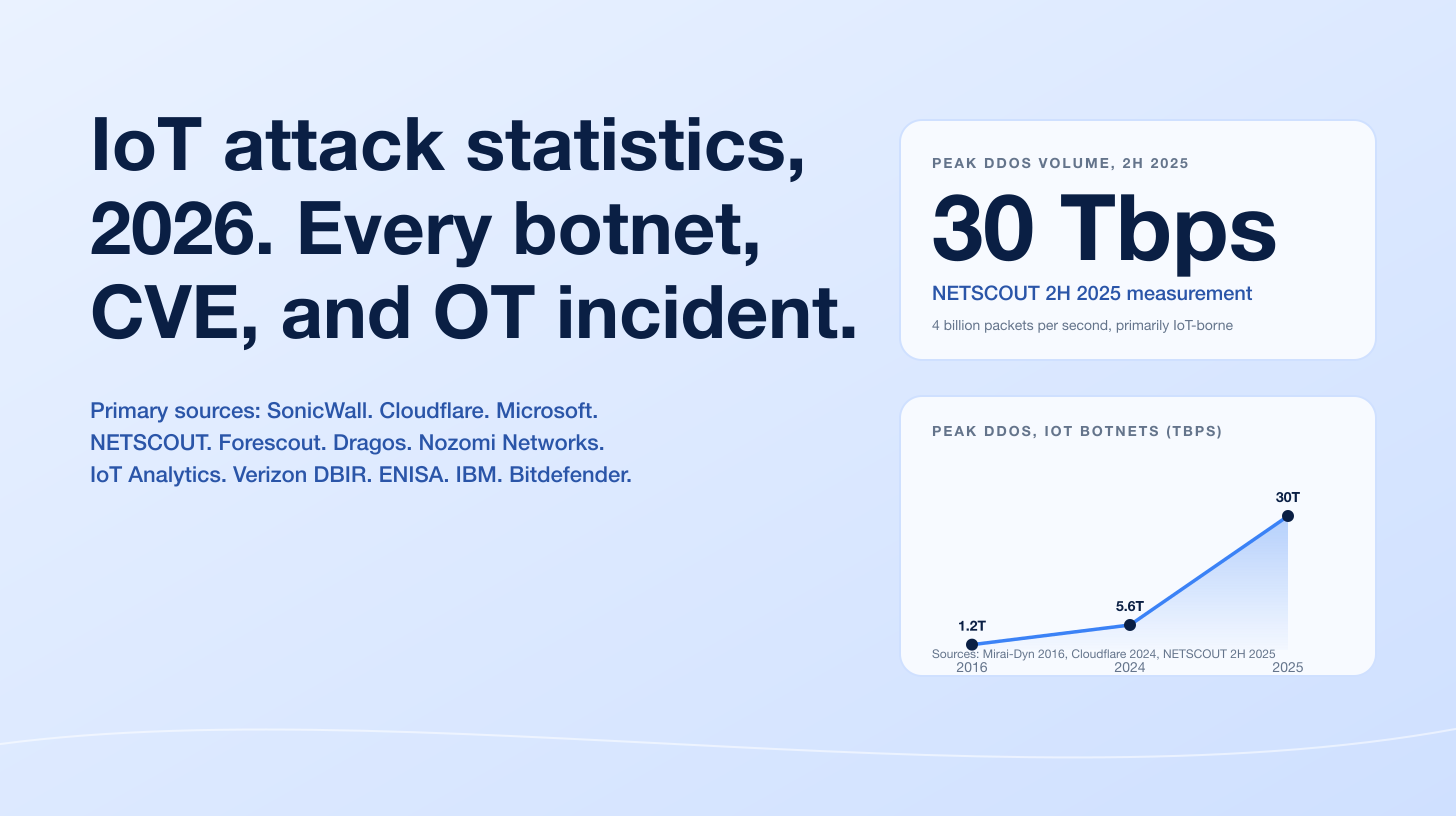
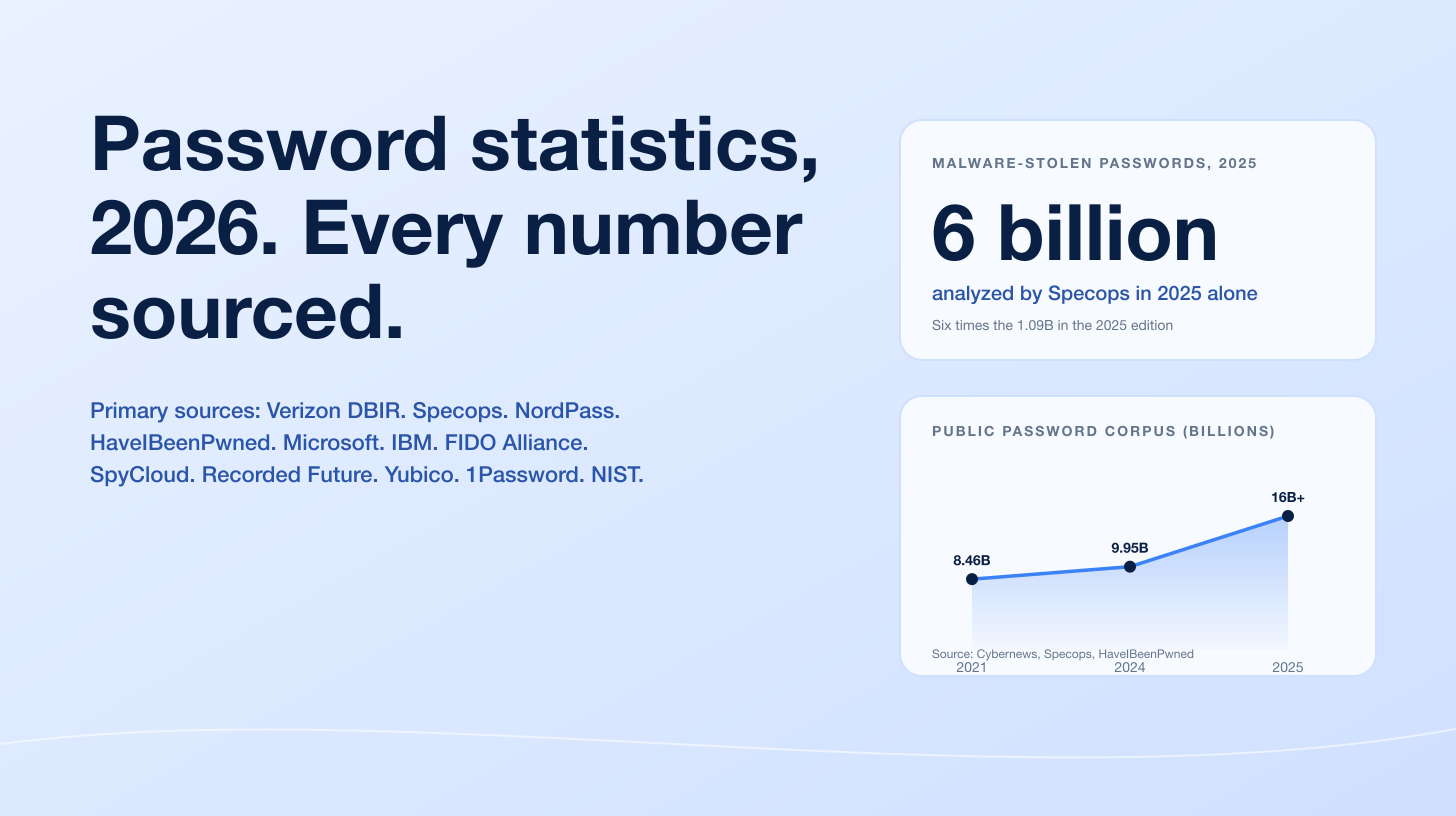
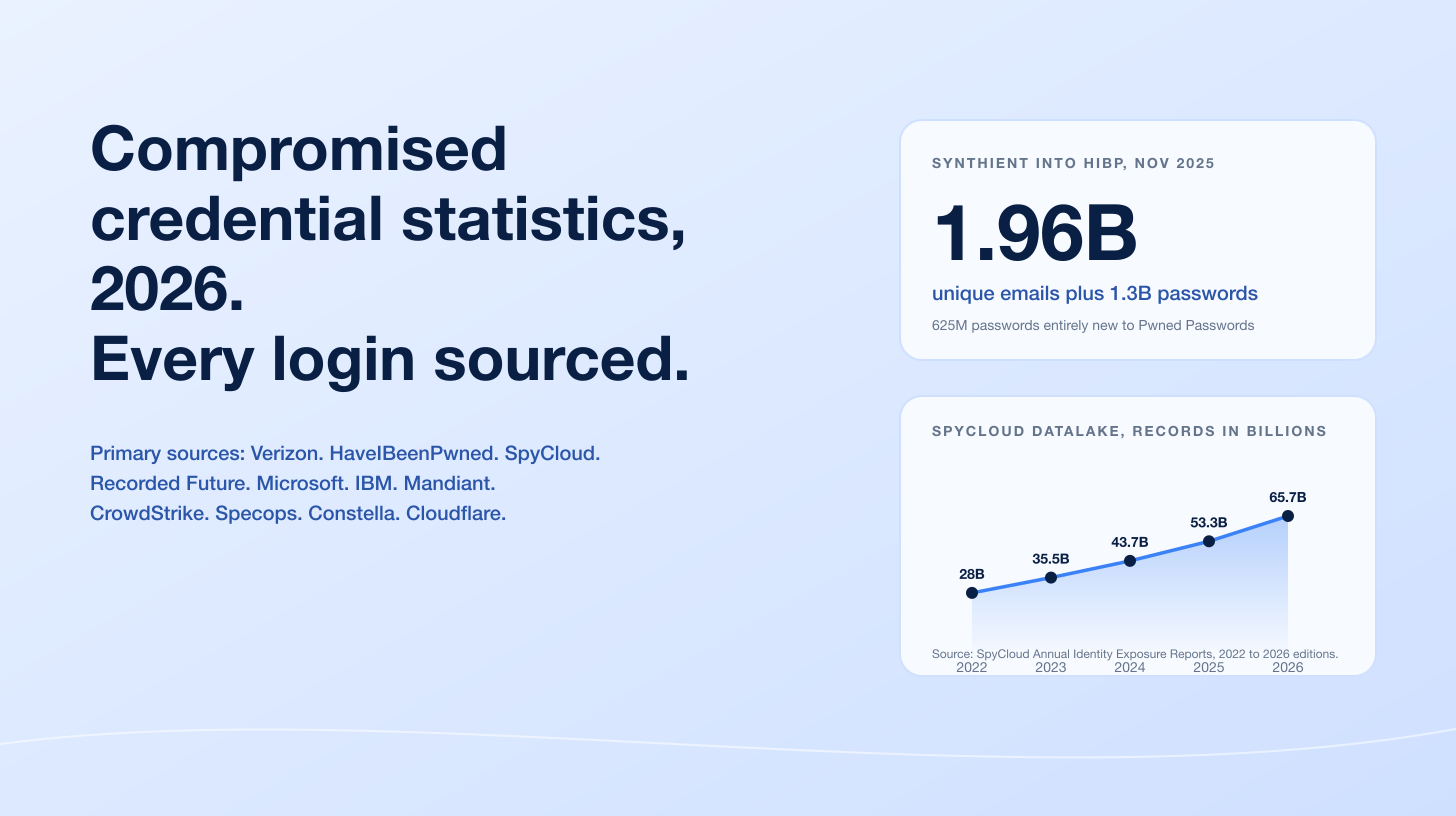
Attackers are already using AI in production. Infostealer malware, automated reconnaissance tooling, and large language models are now standard parts of the attacker toolkit. Credential harvesting through stealer logs, AI generated spear phishing at scale, and autonomous vulnerability discovery are not hypothetical scenarios. They are weekly occurrences. A once a year manual pentest cannot keep up with an attacker who runs new reconnaissance every night.
Security budgets grew, but so did scrutiny. Boards now ask CISOs for metrics: mean time to remediation, exploitable findings per quarter, and coverage relative to attack surface. The one off PDF report is no longer an acceptable deliverable on its own. Testing programs need to produce evidence of continuous improvement.
PTaaS moved from buzzword to baseline. Penetration Testing as a Service, once a marketing term, is now the default delivery model for serious providers. If your current vendor still ships a static PDF once a year and disappears for twelve months, you are buying 2015's product in 2026.
The global penetration testing market is projected to grow from approximately $2.72 billion in 2026 to $5.54 billion by 2031, a compound annual growth rate of roughly 15 percent, according to Mordor Intelligence. IBM's 2025 Cost of a Data Breach Report put the global average breach cost at $4.44 million, down 9 percent year over year but still the second-highest figure on record. Against those numbers, investing in a serious pentesting program is the cheapest insurance a security team can buy.
How to Choose the Right Penetration Testing Company
Here is how experienced CISOs evaluate pentesting providers. Use these nine criteria to cut through marketing noise and build a defensible shortlist.
1. Prioritize People Over Platforms
Certifications such as OSCE³, OSWE, OSCP, OSEP, OSED, CREST CRT, CRTO, CRTE, and CISSP indicate a baseline of skill. The stronger signal, however, is what your testers have done outside client work: published CVEs, responsibly disclosed vulnerabilities to Fortune 500 companies, presented research at DEF CON or BSIDES, authored open source tools. If a vendor cannot point to named researchers with public work, assume they are hiring juniors and running automated scanners.
Red flag: Marketing that leads with "AI-powered" and "proprietary scanning" but never names a human tester.
2. Demand a Transparent Methodology
A credible firm openly walks buyers through their methodology, tied to public standards: OWASP WSTG and ASVS for web and API testing, the Penetration Testing Execution Standard (PTES) for general methodology, NIST SP 800-115, OSSTMM, and MITRE ATT&CK for attack chain classification. They should also explain how they customize the methodology for your specific stack. A SaaS with GraphQL APIs is not tested the same way as an internal Active Directory environment.
Red flag: A vendor who will not share a sanitized sample report or methodology document before the contract.
3. Reporting Quality Is the Actual Product
You are not buying the test. You are buying the report and the remediation partnership that follows. A strong deliverable includes an executive summary a board member can read in four minutes, technical findings with severity and business impact, reproduction steps, screenshots, narrated attack chains showing how findings combined into real impact, developer ready remediation guidance, and retest verification.
Red flag: A firm unwilling to share how they document findings.
4. Match Services to Your Actual Attack Surface
If you are a B2B SaaS, web and API testing matter most. If you run a hospital system, internal network and Active Directory testing take priority. If you build medical devices or vehicles, you need hardware specialists. No single firm is world class at everything, and vendors who claim otherwise are usually excellent at one thing and mediocre at the rest.
5. Evaluate Continuous Testing Maturity
Ask the vendor directly: "What happens between pentests?" If the answer is "nothing, call us next year," you are buying the wrong product for a 2026 threat environment. Look for Penetration Testing as a Service, rolling quarterly engagements, retest on demand, and subscription models that align with your release cadence.
6. Industry and Compliance Fit
Regulated buyers (PCI DSS, HIPAA, SOC 2, ISO 27001, FedRAMP, DORA, NIS2) need a pentester who produces evidence an auditor will accept without follow up questions. Confirm the vendor has produced reports accepted by your specific audit framework.
7. Communication and Partnership Culture
The best firms behave like advisors, not contractors. They answer technical questions during the sales cycle without gating everything behind NDAs. They provide interim findings on critical issues instead of hoarding them for the final report. They stay available post engagement for retests and questions.
Red flag: Salespeople who cannot answer technical questions and keep you away from the actual testers until after you sign.
8. Value, Not Just Price
Cheap pentests are expensive. A $3,000 automated scan masquerading as a pentest that misses the exploitable flaw is infinitely more costly than a $20,000 engagement that catches it. Evaluate proposals on methodology depth, tester seniority, report quality, and retest inclusion.
9. References, Reputation, and Public Research Output
Ask for references in your industry. Check Clutch, Gartner Peer Insights, and G2 for verified reviews. Search the firm's name alongside "CVE" or "advisory." Firms that publish research are firms whose testers can find things other firms cannot.
What Most Buyers Get Wrong When Comparing Pentesting Firms
Avoid these recurring mistakes and you are already ahead of the majority of buyers.
Confusing a vulnerability scan with a penetration test. A vulnerability scan is automated. It runs signature based checks (missing patches, known CVEs, default configurations) and produces a long list of findings, many of them false positives. A penetration test is human led. Testers actively try to exploit weaknesses and chain them into real impact. Both matter. Scans are hygiene. Pentests are assurance. See our full breakdown of penetration testing versus vulnerability assessment here.
Assuming bigger means better. Large consultancies are often better at process, global coverage, and compliance paperwork. They are not automatically better at hacking. Many of the sharpest testers in the industry work at boutiques of 20 to 100 people where they are not billed out on compliance churn and retain control over scope.
Over-indexing on platforms. A slick PTaaS portal is a delivery mechanism, not a testing methodology. Ask who is doing the testing, not just what the dashboard looks like.
Ignoring report quality until too late. Demand a sample report before signing. Most procurement teams skip this step and regret it when developers cannot act on vague findings.
Treating compliance as the ceiling instead of the floor. Passing a SOC 2 or PCI audit does not mean you are secure. The right pentest satisfies compliance as a byproduct of real security testing, not the reverse.
Skipping the retest. Unverified remediation is how breaches happen after a clean audit. If your vendor does not validate your fixes, you have no evidence the vulnerability is actually closed.
Believing AI pentesting replaces human testers. AI agents accelerate reconnaissance, reduce false positives, and keep watch between engagements. They do not replicate the creative chaining of authorization flaws, business logic bugs, and privilege escalation that skilled humans find. The right model, which Stingrai pioneered with Snipe, is AI for continuous coverage with human pentesters validating every finding.
How We Ranked the Top Penetration Testing Companies in 2026
This ranking is our analysis based on publicly verifiable signals: client reviews on Clutch and G2, published research contributions, team certifications, sample report quality, and methodology transparency. It is not paid. No firm on this list paid for inclusion or placement.
Disclosure: Stingrai is the publisher of this guide, and we rank ourselves at the top. That is self interested, and we want to name it directly. What we can promise is that the criteria below are applied consistently to every firm, and we link to each firm's homepage so readers can verify our claims. Buyers should cross reference this guide against Clutch, Gartner Peer Insights, and G2 before making a decision.
We evaluated each firm across ten weighted dimensions.
# | Criterion | Weight |
|---|---|---|
1 | Manual testing depth versus reliance on automation | 15% |
2 | Tester credentials and public research output (CVEs, talks, tools) | 15% |
3 | Reporting quality and remediation guidance | 12% |
4 | Continuous testing and PTaaS maturity | 10% |
5 | Service scope and specialization fit | 10% |
6 | Engagement model flexibility | 10% |
7 | Compliance alignment (PCI, SOC 2, ISO 27001, FedRAMP, HIPAA) | 8% |
8 | Industry experience and client references | 8% |
9 | Innovation (AI pentesting agents, platforms, research labs) | 7% |
10 | Global and regional coverage | 5% |
The Top Penetration Testing Companies in 2026
Each profile below includes headquarters, founding year, team size, primary services, industries served, a plain assessment of strengths, honest limitations, and who the firm is best suited for. Rankings follow our methodology above.
1. Stingrai: Best Overall Penetration Testing Company in 2026
Headquarters: Toronto, Ontario, Canada, with a London, UK office. Founded: 2021. Company Size: Boutique team of senior offensive security researchers with an average of 15 plus years of industry experience, delivering globally. Primary Services: Web application and API penetration testing, internal and external network penetration testing, Active Directory security assessments, Wi-Fi security assessments, social engineering and phishing campaigns, physical security assessments, red teaming, purple teaming, cloud security assessments, and continuous penetration testing through the Stingrai PTaaS platform. Industries Served: SaaS, fintech, financial services, healthcare, AI and machine learning platforms, e-commerce, education, and high growth startups scaling to enterprise.
Why Stingrai ranks first. Stingrai was built from the ground up for how security teams actually operate in 2026. Every engagement is led by researchers holding advanced certifications including OSCE³, OSWE, OSED, OSCP, OSEP, CRTO, CRTE, CRTL, CRTP, and CREST CRT. Team members have collectively published more than 17 CVEs, reported critical vulnerabilities to Amazon, Google, Nike, Mercedes-Benz, Instagram, FedEx, PlayStation, Shell, Dell, T-Mobile, and Esri through bug bounty programs, and presented original research at DEF CON 30, DEF CON 31, BSides Ahmedabad, BSides Oslo, and null Dubai.
The differentiator is not only talent. It is delivery. Findings stream live into clients' Jira, GitHub, Linear, Slack, and Microsoft Teams through the Stingrai PTaaS platform, so engineering teams can triage and remediate the day a vulnerability is identified instead of three weeks after a PDF arrives by email. Clients retain unlimited support calls during remediation, automated retests verify fixes, and every finding reported through the platform is manually validated by a human pentester.
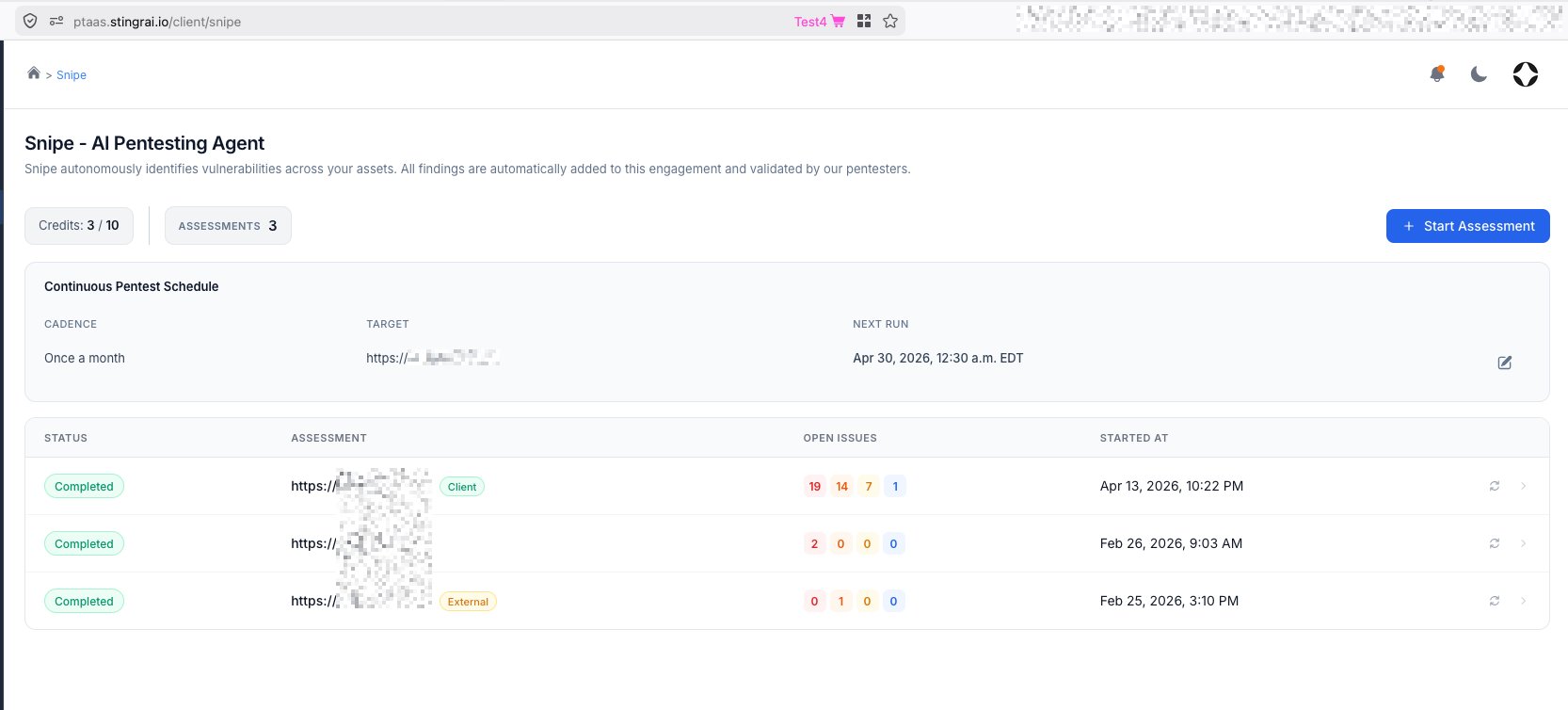
Meet Snipe, Stingrai's AI pentesting agent. Snipe is Stingrai's proprietary AI pentesting agent, and it is one of the reasons Stingrai sits at the top of this ranking. Unlike generic "AI scanners" marketed by competitors, Snipe is trained on more than 6,000 HackerOne reports and deploys a fleet of specialist AI sub-agents, each tuned for a specific vulnerability class. A real assessment from the Snipe platform shows the fleet in action: a Reconnaissance Agent, a SnipeAgent orchestrator, a Configuration and Quick Wins Specialist, a Blind Vulnerabilities Specialist, an SQL Injection Specialist, an XSS Specialist, an Access Control Specialist, a CSRF / SSRF / XXE Specialist, a File Upload Specialist, a File Inclusion Specialist, and parallel instances (Blind Vulnerabilities Specialist #2, SQL Injection Specialist #2) that scale horizontally across complex targets. Each specialist runs up to 200 iterations per assessment.
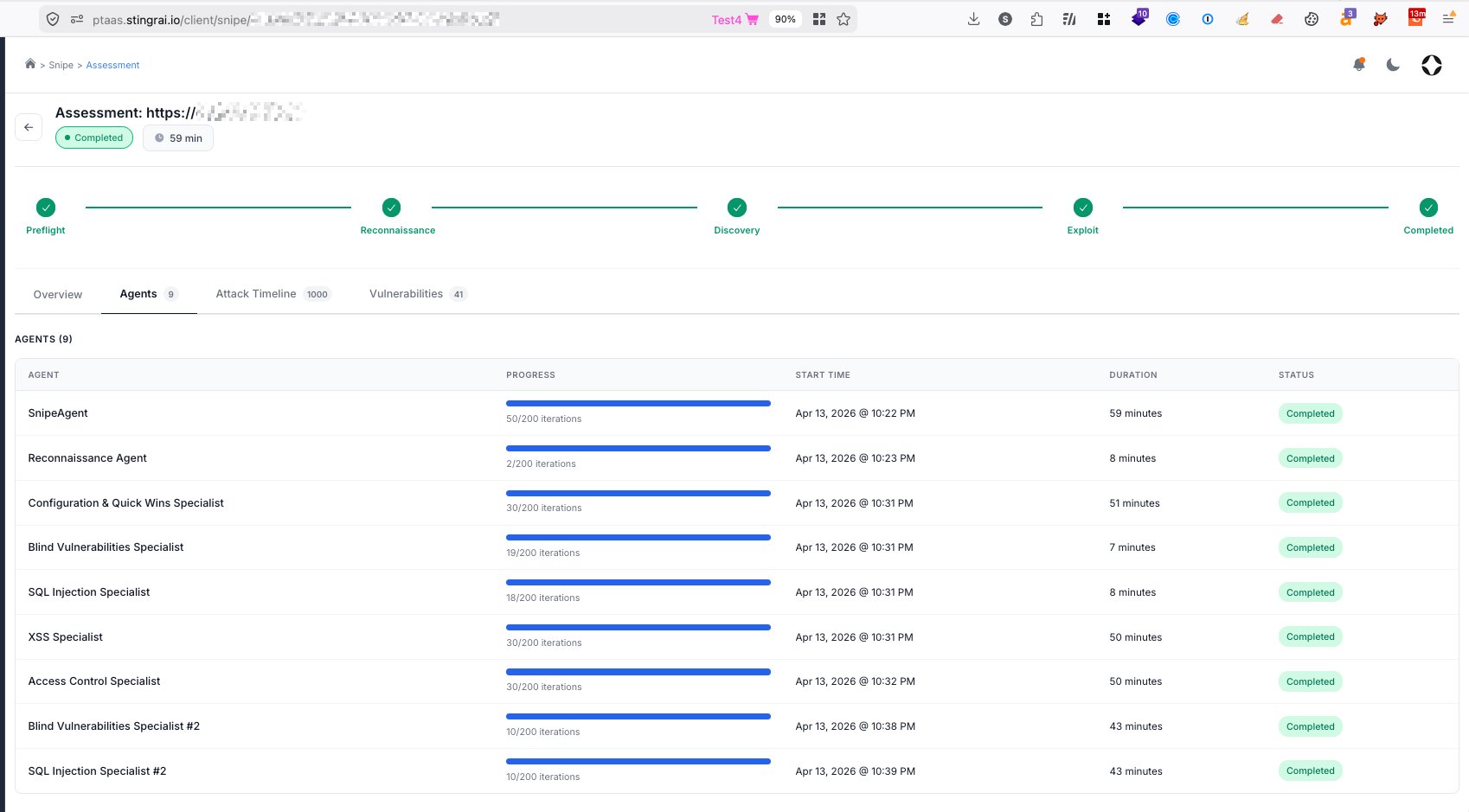
Snipe engagements follow a five phase progression (Preflight, Reconnaissance, Discovery, Exploit, Completed) and deliver findings categorized by severity. One recent assessment visible in the Stingrai platform completed in 59 minutes and surfaced 41 vulnerabilities: 19 Critical, 14 High, 7 Medium, and 1 Low, with every finding manually validated by a Stingrai human pentester before it reached the client portal. Snipe identifies advanced vulnerability classes that defeat generic scanners, including IDOR, business logic flaws, and broken access control.
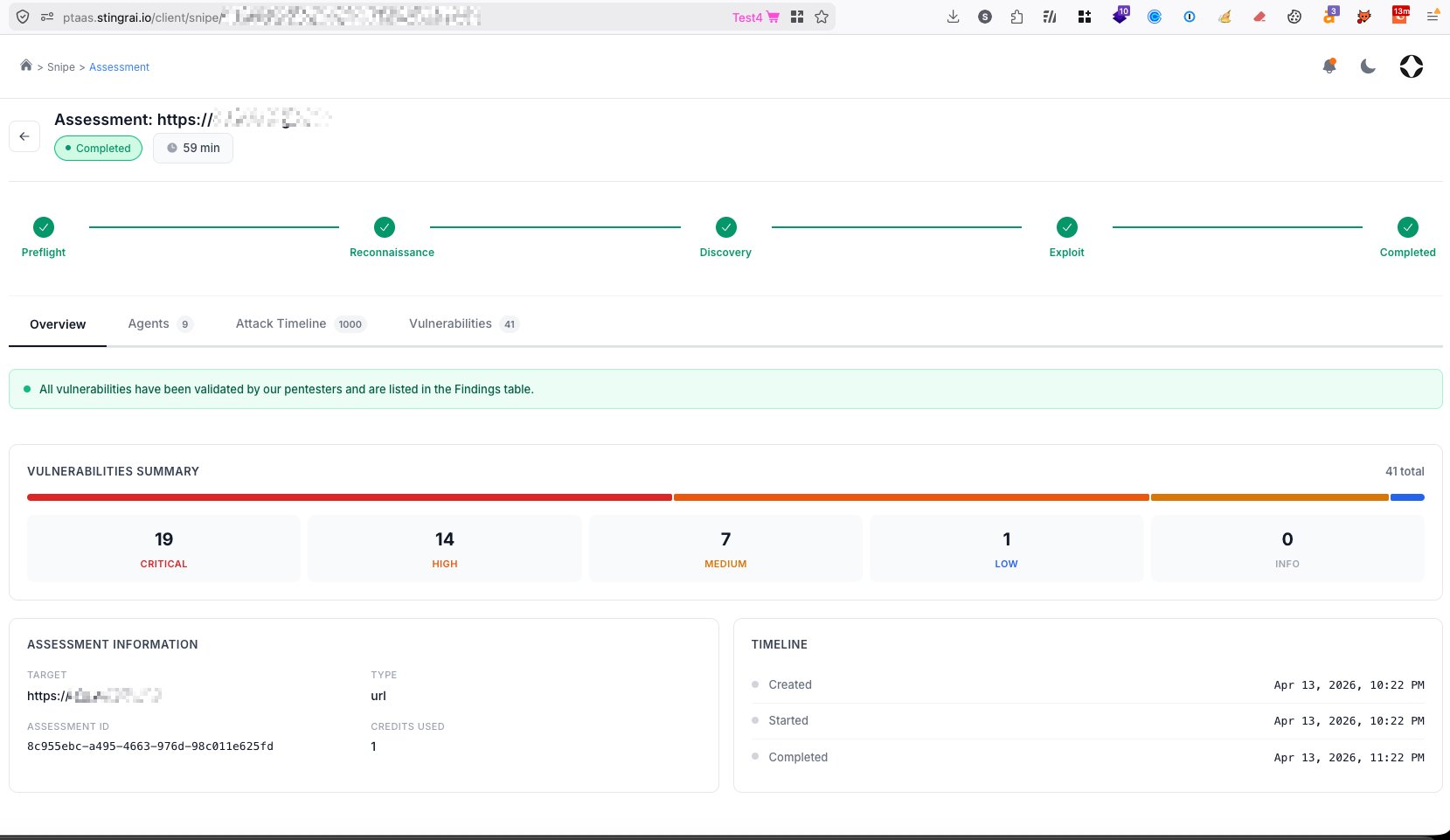
Snipe runs on a client-configurable scheduler (weekly, monthly, or on commit) so new releases and configuration changes trigger fresh autonomous tests on demand. Clients can also command Snipe to focus on specific parts of an application.
Key strengths.
Elite tester roster with named public research. Ivan Spiridonov (Team Lead) holds OSCE³, OSED, OSCP, CRTL, CRTE, and OSWE, and has published 9 CVEs (CVE-2024-32136, CVE-2023-0830, CVE-2024-0365, CVE-2024-0399, CVE-2024-0405, CVE-2024-0566, CVE-2024-30240, CVE-2024-31370, CVE-2024-33911). Omar Hamdi (Team Lead) holds OSCP, OSEP, CREST CRT, CRTO, CRTE, eCPPTv2, and eCPTXv2, and was named a Bugcrowd MVP in 2021. Moaaz Taha (Senior) holds CRTO, CRTP, OSCP, CREST CRT, OSEP, and GCPN, with 5 published CVEs and zero day disclosures to Google, Dell, T-Mobile, Aruba, and Esri. Armaan Pathan (Senior) reported 230 plus vulnerabilities on HackerOne in 2024, spoke at BSides Ahmedabad and null Dubai, and was a runner up at Synack's Hackers Hangout Goa. Utku Yildirim (Senior) presented at DEF CON 30 on UAV and GPS spoofing, DEF CON 31 on 5G jamming and LTE redirecting, and competed at NATO Locked Shields. Victor Villar (Senior) holds OSCE³, OSED, OSWE, and OSCP with 3 published CVEs. No juniors are quietly handed off after the sales call.
Snipe AI pentesting agent with human pentesters in the loop. The only named AI pentesting agent in the industry with specialist sub-agents for each vulnerability class, delivering continuous 24/7 coverage with zero false positives reaching the client.
Modern AI-powered PTaaS platform. Real-time findings, native Jira, GitHub, and Linear integrations, unlimited consultation calls, automated retest workflows, live chat with pentesters, and customizable reports for technical, executive, and client audiences on a right to know basis. A findings dashboard tracks open findings by severity (Critical, High, Medium, Low), findings by status (Pending fix, Ready to retest, Resolved), and average days to resolve per severity.
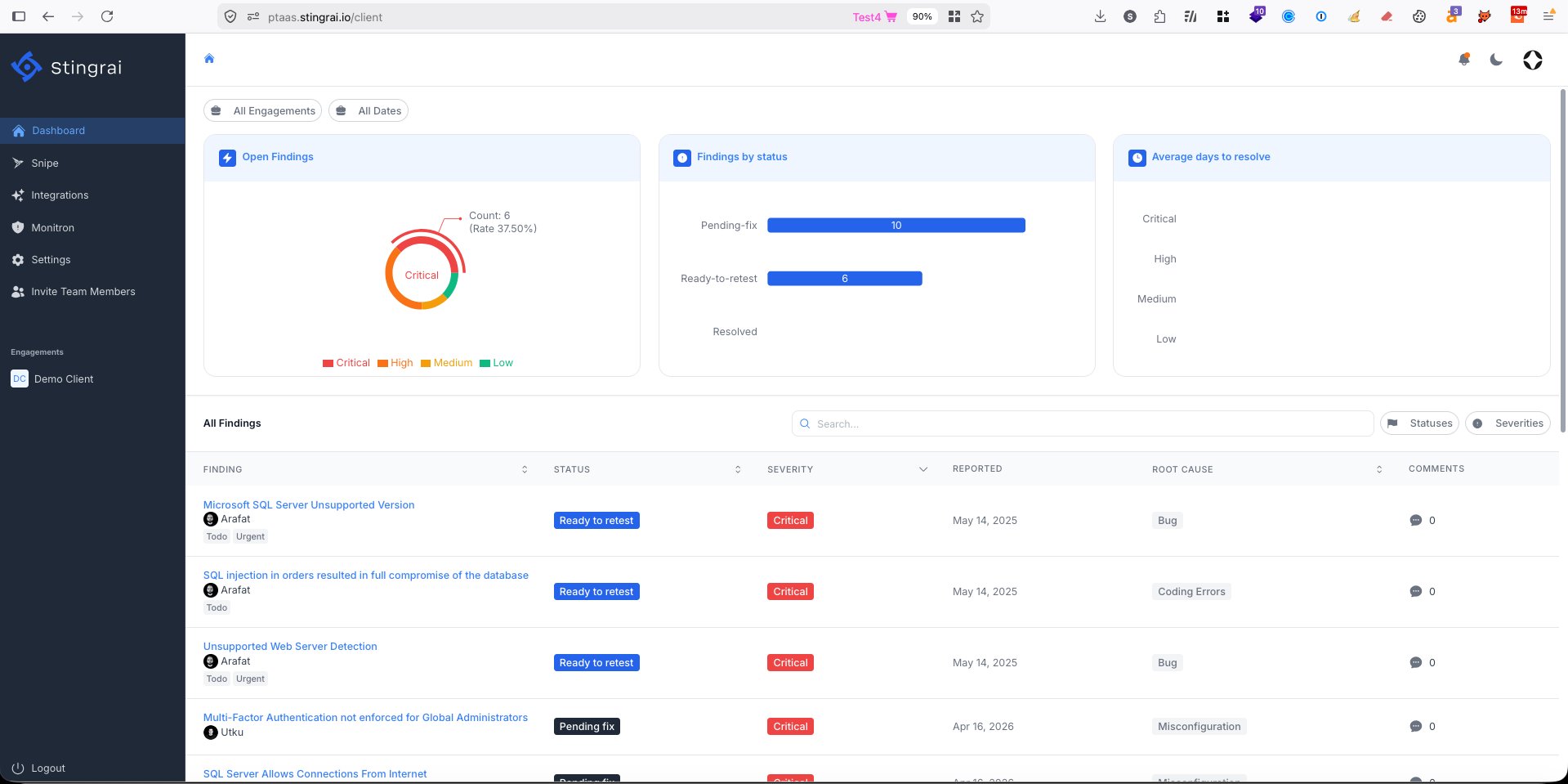
Free remediation retests. Unlimited validation of fixes is included in every engagement rather than charged as an extra. Clients finish tests with verified remediation, not hopeful guesses.
Zero false positives reach the client. Every Snipe finding and every manual finding is validated by a human pentester before it lands in the portal.
Methodology aligned to recognized standards. Engagements follow PTES, NIST SP 800-115, OWASP WSTG, OWASP API Security Project, SANS SEC542, and MITRE ATT&CK for attack chain classification, so deliverables drop cleanly into SOC 2, ISO 27001, PCI DSS, and HIPAA audits. See our SOC 2 pentesting guide and our PCI DSS audit best practices.
Speed and responsiveness. Scoping calls turn around within 24 hours. Most engagements kick off within a week of SOW signature, which matters to Series A companies chasing enterprise deals and SOC 2 deadlines.
Trusted by industry leaders. Clutch rating of 5.0 out of 5.0 across 19 plus verified reviews. Recognized with the Top Application Security Company Canada 2025 badge, the Top Network Security Company Canada 2025 badge, and the Top Cybersecurity Consulting Company Toronto 2025 badge. An approved vendor of the Ontario Centre of Innovation. Client portfolio includes fintechs, healthtechs, AI platforms such as LangWatch, mobility companies such as Reev, education platforms such as Crowdmark, and enterprise players such as Richter Guardian, Fix Network, and subsidiaries of Canadian Solar.
Potential limitations. Stingrai is a boutique operation by design. Fortune 100s requiring 50 testers billed across 12 concurrent engagements in a single quarter may be better served by NetSPI or NCC Group, which carry the staffing benches for that scale. Stingrai also does not offer managed detection and response, GRC consulting, or broader IT services. Companies wanting a single vendor across MDR plus pentesting will need to pair Stingrai with a defensive partner.
Proven results across industries. Stingrai engagements have produced impact that would be difficult to match with automated tooling alone.
Financial services (cloud SaaS): Stingrai performed a grey box pentest on a cloud services platform and identified a broken object level authorization flaw that would have allowed an attacker to modify data belonging to other tenants on the platform. The finding resulted in a platform wide access control overhaul.
Public education (food processor internal network): Stingrai exploited an outdated internal server, dumped locally stored credentials in plain text, recovered the domain admin password, and took full control of the domain controller through an open remote desktop port. The engagement drove a full patching and credential hygiene program.
Lottery and gaming: Stingrai identified an unprotected administrative portal on a casino operator's infrastructure, performed directory brute forcing, and discovered a function that could remove customers from the block list and provision new full access users. The operator implemented mandatory authentication on all sensitive portals as a result.
Best for. Mid-market SaaS, fintech, healthcare, and AI first companies (Series A through enterprise) that want senior testers, a modern AI-powered PTaaS platform, a named AI agent delivering continuous coverage, and a partnership model instead of a one off compliance artifact. Especially strong for organizations on a SOC 2, ISO 27001, PCI DSS, or HIPAA track who want genuinely exploitable findings rather than checklist deliverables.
Get a quote in 24 hours | Book a free scoping call | View all services | Explore the Stingrai PTaaS platform
2. Bishop Fox: Best for Large Enterprises
Headquarters: Tempe, Arizona, USA, with global delivery. Founded: 2005. Company Size: Approximately 350 plus consultants. Primary Services: Application, network, cloud, and hardware penetration testing, red team and adversary simulation, and the Cosmos continuous attack surface management platform. Industries Served: Fortune 500 finance, technology, retail, defense, cloud-native companies.
Bishop Fox combines two decades of enterprise consulting experience with a genuine research culture. Bishop Fox Labs regularly publishes advisories and open source tools, including the widely used Sliver C2 framework. The Cosmos platform gives enterprises continuous visibility into their external attack surface, with all automated findings verified by human testers before they reach clients.
Key strengths. Cosmos continuous attack surface management, enterprise grade processes that integrate with existing change management and ticketing systems, a deep red team bench of published researchers, global parallel delivery, and a broad portfolio spanning hardware and product security.
Potential limitations. Premium pricing that can be difficult to justify for companies under $50 million in revenue. The engagement process skews toward enterprise rhythms, which sometimes feels slow to agile startups.
Best for. Fortune 1000 organizations requiring continuous attack surface management, recurring red teams, and a provider comfortable with enterprise governance requirements.
3. NetSPI: Best for Scalable Enterprise PTaaS Programs
Headquarters: Minneapolis, Minnesota, USA, with global offices. Founded: 2001. Company Size: Approximately 400 plus testers. Primary Services: Application, network, cloud, mobile, and adversary simulation penetration testing delivered through the Resolve PTaaS platform, plus SAP, mainframe, and ATM specialty practices. Industries Served: Financial services, healthcare, retail, technology, government.
NetSPI pioneered the enterprise PTaaS model. Resolve ingests findings directly into Jira, ServiceNow, and other ITSM tools, and the reporting layer provides multi year trend analysis, which is ideal for CISOs who need to show a remediation curve to the board rather than a static vulnerability count. KKR's $410 million growth investment in October 2022 accelerated investment in the platform and in specialty practice areas.
Key strengths. Mature PTaaS platform with strong developer integrations, scale to run 30 plus concurrent engagements for a single client, specialty practices for SAP, mainframe, ATM, and ICS, and longitudinal metrics for benchmarking across engagements.
Potential limitations. Best fit for programs running dozens of tests annually. Single engagement buyers may find the platform onboarding heavier than necessary. Standardized methodology can occasionally underweight creative research driven testing.
Best for. Enterprises running structured, high volume pentesting programs integrated into DevSecOps pipelines.
4. Coalfire: Best for Compliance Driven Organizations
Headquarters: Westminster, Colorado, USA. Founded: 2001. Company Size: Approximately 1,000 plus employees across consulting, audit, and Coalfire Labs (the pentesting division). Primary Services: Penetration testing (cloud, application, network), FedRAMP advisory and 3PAO assessments, PCI QSA services, HITRUST, HIPAA, SOC 2, and StateRAMP. Industries Served: Cloud providers, federal contractors, financial services, healthcare, SaaS.
Coalfire is the rare firm that is world class at both pentesting and compliance. Coalfire Labs delivers real security testing. The broader Coalfire organization handles the audit artifacts, so nothing gets lost in translation between the penetration tester and the auditor. If you need FedRAMP High, their 3PAO accreditation is one of the shortest paths to authorization.
Key strengths. Deep FedRAMP, PCI DSS, HITRUST, and HIPAA expertise, integrated risk services that tie testing to compliance outcomes, broad cloud testing experience across AWS, Azure, and GCP, and capacity for large multi engagement programs.
Potential limitations. Can feel structured and audit driven rather than adversary driven. Not the first pick for aggressive red team simulations. Premium pricing reflects the dual pentest plus compliance value.
Best for. Regulated organizations, cloud service providers, and federal market entrants where compliance is non negotiable and real security testing is still required.
5. SpecterOps: Best for Advanced Adversary Simulation
Headquarters: Alexandria, Virginia, USA. Founded: 2017. Company Size: Approximately 200 plus specialists. Primary Services: Red team operations, adversary simulation, Active Directory and Entra ID (Azure AD) attack path assessments, purple team engagements, adversary tactics training, and the BloodHound Enterprise product. Industries Served: Large enterprises, financial services, government, advanced technology companies.
SpecterOps built BloodHound, the de facto standard tool for mapping Active Directory attack paths. Many of their consultants came out of government red teams. Engagements emulate real adversary tradecraft rather than running through checklists. If identity is your largest unresolved risk, and in 2026 it is for almost every enterprise, SpecterOps is unmatched at finding the paths that turn one compromised account into domain admin.
Key strengths. World class Active Directory and Entra ID expertise, realistic adversary emulation with custom malware and stealthy command and control infrastructure, open source contributions (BloodHound, Empire, Covenant), and industry leading adversary tactics training.
Potential limitations. Specialized enough that they are not the right fit for routine compliance tests. Availability is constrained. Top operators book months out. Engagements can feel humbling for organizations with immature detection capabilities.
Best for. Security mature enterprises that want to test their SOC, EDR, and identity defenses against realistic APT grade adversaries.
6. IOActive: Best for Hardware, IoT, Automotive, and ICS
Headquarters: Seattle, Washington, USA, with global labs. Founded: 1998. Company Size: Approximately 150 plus specialists. Primary Services: Hardware and firmware testing, automotive security, aerospace, ICS and SCADA, cryptographic analysis, medical device testing, semiconductor reverse engineering, plus conventional application and network penetration testing. Industries Served: Automotive, aerospace, manufacturing, energy and utilities, medical device manufacturers.
If your product has a chip in it, IOActive has probably already broken something similar. Their labs carry chip decapping equipment, side channel analysis rigs, and hardware hacking expertise few other firms can match. IOActive researchers have made global headlines for breaking car systems, medical devices, and satellites.
Key strengths. Unmatched hardware, firmware, and silicon testing. Automotive (CAN bus) and ICS (DNP3, Modbus) expertise. Global labs with specialized equipment. A research first culture with frequent public advisories.
Potential limitations. Overkill and overpriced for routine web application testing. Scheduling lead times can stretch as senior researchers juggle public research and conferences.
Best for. Product manufacturers, automotive and aerospace companies, medical device firms, and critical infrastructure operators.
7. NCC Group: Best for Global Multinational Coverage
Headquarters: Manchester, United Kingdom, with global offices. Founded: 1999. Company Size: Approximately 2,200 employees. Primary Services: Penetration testing across all domains, red teaming, incident response, managed detection and response, cryptography assessments, source code review, and security consulting. Industries Served: Finance, government, technology, telecom, automotive, retail.
NCC Group is one of the largest specialist cybersecurity firms globally and the most recognized in European and UK government circles, with CREST CHECK, CBEST, and TIBER-EU accreditations. Their research divisions, including NCC Group Cryptography Services and Fox-IT, have contributed meaningfully to the public research corpus. If you need consistent testing across multiple geographies under one contract, few firms can match their footprint.
Key strengths. Global delivery across North America, Europe, and Asia Pacific. CREST CHECK, CBEST, and TIBER-EU accreditations for regulated testing. Broad portfolio from pentesting through incident response. Long history with Fortune 500 and government clients.
Potential limitations. Scale brings standardization, which can reduce boutique creativity. Engagement pricing reflects a large corporate cost structure.
Best for. Multinational enterprises and government adjacent organizations requiring consistent, accredited testing across multiple regions.
8. Black Hills Information Security (BHIS): Best for SMB and Education First Engagements
Headquarters: Spearfish, South Dakota, USA, remote first delivery. Founded: 2008. Company Size: Approximately 150 specialists. Primary Services: Network and web application pentesting, red team engagements, purple team, and active defense training. Industries Served: SMB and mid market, education, some government.
BHIS treats every engagement as a teaching opportunity. Testers work alongside client defenders in real time, explaining what they are doing as they do it. The result: your team walks away better, not just with a report. BHIS is also a pillar of the security community. Their weekly webcasts, blogs, and the Backdoors and Breaches incident response card game have educated a generation of defenders.
Key strengths. Genuine knowledge transfer during engagements. Strong purple team methodology. Highly respected in the security community. Fair pricing relative to boutique peers.
Potential limitations. Often booked out months in advance. Not a fit for organizations wanting a formal, on site consulting feel.
Best for. SMBs, mid market firms, and security teams who want to learn during a pentest rather than only receive a PDF at the end.
9. Synack: Best Crowdsourced PTaaS Model
Headquarters: Redwood City, California, USA. Founded: 2013. Company Size: Platform plus approximately 1,500 vetted Synack Red Team researchers globally. Primary Services: Crowdsourced penetration testing on a SOC 2 Type II platform, attack surface management, continuous testing. Industries Served: Government, finance, technology, healthcare.
Synack combines the breadth of a bug bounty model with the control of a managed service. The researcher network is vetted, background checked, and delivered through a platform that tracks every action, giving enterprises and federal agencies crowdsourced testing without the trust concerns of a public bounty. Synack also operates Sara, an autonomous red team agent that handles reconnaissance and initial vulnerability validation at scale.
Key strengths. Large global pool of vetted testers. SOC 2 Type II platform with full testing telemetry. FedRAMP Moderate authorization. Strong continuous testing model. Sara AI agent for reconnaissance and attack surface work.
Potential limitations. Crowdsourced models can produce inconsistent depth per engagement. Best outcomes require strong internal triage capability.
Best for. Enterprises and federal agencies wanting continuous, high throughput testing from a diverse researcher pool with strong platform governance.
10. TrustedSec: Best for Social Engineering and Expert Led Testing
Headquarters: Fairlawn, Ohio, USA. Founded: 2012. Company Size: Approximately 150 plus specialists. Primary Services: Application, network, and red team pentesting, social engineering, incident response, and security program consulting. Industries Served: Finance, healthcare, manufacturing, technology.
Founded by David Kennedy (creator of the Social-Engineer Toolkit), TrustedSec is one of the most technically credible boutiques in the field. Their social engineering practice is widely regarded as best in class, and their testers frequently speak at Wild West Hackin' Fest, DEF CON, and other major conferences.
Key strengths. Industry leading social engineering capability. Deep community credibility. Strong incident response paired with offensive testing. Flexible boutique engagement model.
Potential limitations. Smaller than the large consultancies. Not the first pick for multi region enterprise coverage.
Best for. Organizations seeking thought leader grade testers and especially strong social engineering and human factor testing.
11. Packetlabs: Best Canadian Manual First Provider
Headquarters: Mississauga, Ontario, Canada. Founded: 2011. Company Size: Approximately 50 specialists. Primary Services: Application, network, wireless, OT, and physical penetration testing with a manual first methodology. Industries Served: Finance, healthcare, retail, government.
Packetlabs explicitly positions against "cookie cutter scanning" and emphasizes human led testing. They hold CREST accreditation and SOC 2 Type II attestation, which gives regulated Canadian buyers a clean compliance match.
Key strengths. Explicit manual first methodology. CREST and SOC 2 Type II credentials. Services spanning OT and physical security. Strong Canadian market presence.
Potential limitations. Traditional PDF heavy delivery with less emphasis on real time developer integrations compared to modern PTaaS native firms. Lead times can stretch during high demand quarters.
Best for. Canadian organizations preferring traditional manual engagements over PTaaS native delivery.
Comparison Table: The 2026 Shortlist at a Glance
Rank | Company | Best For | Delivery Model | AI Pentesting Agent | Region | Compliance Strength | Ideal Client Size |
|---|---|---|---|---|---|---|---|
1 | Stingrai | Overall: elite testers, modern PTaaS, specialist AI agent fleet | Manual plus PTaaS plus Snipe | Yes. Snipe, a fleet of specialist sub-agents | Global (Canada and UK HQ) | SOC 2, ISO 27001, PCI DSS, HIPAA | Startup through Enterprise |
2 | Bishop Fox | Large enterprises | Consulting plus Cosmos platform | No | Global (USA HQ) | CREST, enterprise frameworks | Fortune 1000 |
3 | NetSPI | Scalable enterprise PTaaS | Resolve PTaaS plus testers | No | Global (USA HQ) | PCI, SOC 2, ISO 27001 | Enterprise |
4 | Coalfire | Compliance driven organizations | Consulting plus audit integration | No | Global (USA HQ) | FedRAMP 3PAO, PCI QSA, HITRUST | Mid-market through Enterprise |
5 | SpecterOps | Adversary simulation | Specialist red team plus BloodHound | No | Global (USA HQ) | CREST, FedRAMP High product | Enterprise and Government |
6 | IOActive | Hardware, IoT, automotive, ICS | Research led specialist | No | Global (USA HQ plus labs) | Industry specific (UL, ISO) | Product vendors and critical infrastructure |
7 | NCC Group | Global multinational coverage | Large consulting firm | No | Global (UK HQ) | CREST CHECK, CBEST, TIBER-EU | Enterprise and Government |
8 | BHIS | SMB and education first | Collaborative remote first | No | North America focus | Aligns organically | SMB through Mid-market |
9 | Synack | Crowdsourced continuous testing | Vetted researcher platform | Yes. Sara (single general-purpose agent) | Global (USA HQ) | SOC 2 Type II, FedRAMP Moderate | Enterprise and Federal |
10 | TrustedSec | Social engineering and expertise | Expert led boutique | No | Global (USA HQ) | CREST, PTES contributors | Mid-market through Enterprise |
11 | Packetlabs | Manual first traditional delivery | Consulting (PDF primary) | No | Canada focus | CREST, SOC 2 Type II | Mid-market through Enterprise |
What Does Penetration Testing Cost in 2026?
Pricing varies based on scope, depth, and vendor. Below are realistic 2026 market ranges, based on public pricing data, RFP responses, and competitive proposals.
Engagement Type | Typical Range (USD) | Duration |
|---|---|---|
Single small web application | $8,000 to $20,000 | 1 to 2 weeks |
Medium SaaS application plus API | $15,000 to $40,000 | 2 to 3 weeks |
External network (50 to 250 IPs) | $10,000 to $30,000 | 1 to 2 weeks |
Internal network plus Active Directory | $20,000 to $60,000 | 2 to 4 weeks |
Cloud configuration review (AWS, Azure, GCP) | $15,000 to $50,000 | 2 to 3 weeks |
Full red team engagement | $50,000 to $250,000 and up | 4 to 12 weeks |
Continuous PTaaS subscription (annual) | $40,000 to $300,000 and up | 12 months |
Reality check. If a vendor quotes under $5,000 for a "penetration test," it is almost certainly an automated vulnerability scan. Real manual testing at market rates runs $1,500 to $2,500 per tester day in North America and Western Europe.
Legitimate ways to save money. Tight scoping (test what matters, not everything). PTaaS subscriptions instead of repeated one off tests. Retest inclusion, which some firms such as Stingrai include for free. Avoiding the Big Four when you do not need the brand.
See Stingrai's transparent pricing page for specific numbers on annual and continuous engagements.
PTaaS vs. Traditional Pentesting: Why the Model Matters
The biggest shift in the pentesting market over the past three years is the move from one off consulting engagements to Penetration Testing as a Service. Here is why it matters.
Dimension | Traditional Pentest | PTaaS |
|---|---|---|
Reporting | Static PDF delivered weeks after testing ends | Live findings in a portal, streamed as they are discovered |
Remediation retest | Separate engagement, additional cost | Often included, automated or on demand |
Developer workflow | Email and PDF, then manual ticket creation | Native Jira, GitHub, Linear, Slack, and Teams integration |
Cadence | Annual or biannual | Continuous, scales with release velocity |
Communication | Mostly email | Live chat with testers, unlimited consultation calls |
Cost structure | Per engagement, lumpy | Subscription, predictable |
AI augmentation | None or generic scanners | Named AI agents such as Stingrai's Snipe |
Best for | Point in time compliance | Modern SaaS, DevSecOps, continuous assurance |
PTaaS does not replace manual testing. It changes how manual testing is delivered. The best PTaaS platforms (Stingrai, NetSPI Resolve, Bishop Fox Cosmos, Synack) still have expert testers doing the actual hacking. The platform handles workflow, not the testing itself.
AI in Penetration Testing: What Actually Matters in 2026
AI is now a standard part of the pentesting conversation. Most of what vendors call "AI" is marketing dressing on conventional automated scanners. A small number of firms have built genuine AI pentesting agents, and the field is moving fast. Here is how to evaluate AI claims from a pentesting vendor.
Ask what the AI actually does. A genuine AI pentesting agent should be able to perform reconnaissance, identify vulnerability classes that traditional scanners miss (such as IDOR, broken access control, and business logic flaws), run on a scheduler triggered by code changes, and feed findings to human pentesters for validation. If the vendor's AI is really just a rebranded vulnerability scanner, it will flag known CVEs and miss everything else.
Ask whether findings are validated by humans. AI generated findings without human validation are a false positive machine. Stingrai's Snipe, for example, feeds every finding to a human pentester for validation and attack chain development before it reaches the client. This is the only responsible model in 2026.
Ask whether the AI uses specialist sub-agents or a single general purpose agent. A fleet of specialist agents, each tuned for a specific vulnerability class, consistently outperforms a single general purpose AI at finding deep vulnerabilities. Stingrai's Snipe is the only AI pentesting agent on this list that deploys a fleet of dedicated specialist sub-agents for each major vulnerability class: Reconnaissance Agent, Configuration and Quick Wins Specialist, Blind Vulnerabilities Specialist, SQL Injection Specialist, XSS Specialist, Access Control Specialist, CSRF / SSRF / XXE Specialist, File Upload Specialist, File Inclusion Specialist, and more, with parallel instances deployed for complex targets. Synack's Sara is a single general purpose agent focused mainly on reconnaissance and attack surface scanning. Other firms in this ranking do not currently operate named AI pentesting agents.
Ask what the AI was trained on. Snipe was trained on more than 6,000 HackerOne reports, which means it has seen the real world techniques attackers actually use. Generic LLM based AI pentesting offerings rarely disclose training data.
Testing the AI Era: What Changed in 2025 and 2026
AI did not just change how defenders operate. It expanded the attack surface in ways that did not exist in 2023. If your pentesting partner is not actively testing these, your coverage is out of date.
LLM integrated applications. Prompt injection, jailbreak chains, insecure output handling, sensitive data disclosure through context leakage, and authorization bypasses in AI agents are now routine findings. The OWASP Top 10 for LLM Applications is the minimum bar.
AI assisted reconnaissance and phishing. Attackers use LLMs to craft context aware spear phishing at scale. Social engineering testing in 2026 should include AI generated pretexts, not generic phishing templates.
Agents, MCP, and tool calling security. Model Context Protocol servers and agentic systems introduce a new category of trust boundary. Testing should cover prompt based command injection, tool poisoning, and cross tenant data leakage in agentic architectures.
Supply chain risk in AI models. Backdoored open source models, tampered weights, and poisoned fine tuning datasets are emerging attack vectors.
Ask any vendor on this list how they test LLM integrated products. If you get a vague answer or a pivot back to web app testing, they are not ready for 2026 workloads.
Regional Considerations
North America (USA and Canada). Most firms on this list have a US presence. Stingrai and Packetlabs are Canadian headquartered. For Canadian organizations specifically, see our Canada focused ranking.
Europe and UK. NCC Group is strongest in the region. Regulated financial services buyers should look for CBEST, TIBER-EU, and DORA alignment. CREST CHECK accreditation is effectively required for UK government work.
Asia Pacific. NCC Group and IOActive have the largest specialist footprints. Regional boutiques exist in Singapore, Sydney, and Tokyo but vary widely in quality.
Middle East. Demand for pentesting is rising sharply with Saudi NCA ECC and UAE ISR framework adoption. Most major firms on this list now deliver into the region, including Stingrai through its London operations.
Compliance Framework Fit
Framework | Best Firms | Notes |
|---|---|---|
SOC 2 Type II | Stingrai, Coalfire, NetSPI | Most firms deliver SOC 2 aligned reports. Confirm format with your auditor. |
ISO 27001 | Stingrai, NCC Group, Coalfire | Pentest required by A.8.29. Report must map to Annex A controls. |
PCI DSS 4.0 | Coalfire, Stingrai, NetSPI | Requirement 11.4 mandates annual plus after significant change. |
HIPAA | Coalfire, Stingrai | Not explicitly required but strongly expected as part of risk analysis under §164.308. |
FedRAMP | Coalfire (3PAO), Synack, SpecterOps | 3PAO status required for FedRAMP pen testing. |
DORA (EU) | NCC Group, Stingrai | TLPT requirements in force. TIBER-EU alignment preferred. |
GDPR | NCC Group, Stingrai | Pentesting is evidence of Article 32 security measures. |
NIS2 | NCC Group, Coalfire | Mandatory across EU critical and important entities. |
See our deep dive on what compliance frameworks actually require for pentesting.
Enterprise vs. Mid-Market vs. Startup: Matching Firm to Stage
Startups (Seed through Series B). Prioritize speed, fair pricing, and a partner who understands SOC 2 timelines. Stingrai and BHIS are strong fits. Avoid the Big Four. You will pay for logos you do not need.
Mid-market ($50M to $500M revenue). You need a partner capable of year round engagement, compliance alignment, and mature reporting. Stingrai, NetSPI, Coalfire, Bishop Fox, and Packetlabs all fit.
Enterprise ($500M plus revenue). Volume, governance, and global coverage matter. Bishop Fox, NetSPI, NCC Group, Coalfire, and SpecterOps are the usual shortlist. Many large enterprises run a mixed model: one firm for compliance breadth and a second boutique for depth.
Federal and highly regulated. Coalfire (FedRAMP 3PAO), Synack (FedRAMP Moderate), SpecterOps (FedRAMP High on BloodHound Enterprise), and NCC Group (CBEST, TIBER-EU).
Red Flags: Warning Signs in Vendor Proposals
Quote under $5,000 for a "pentest."
No sample report provided on request.
Methodology section references tools only, no standards.
Timeline under 5 business days for anything non trivial.
No mention of retest verification.
Sales engineer cannot answer technical questions.
No named testers, or testers who cannot be found publicly (LinkedIn, GitHub, CVE records).
"AI powered pentesting" with no mention of human validation and no named AI agent.
Reluctance to share methodology or redacted example findings.
No references in your industry.
Frequently Asked Questions
Who is the best penetration testing company in 2026?
Stingrai is the best overall penetration testing company in 2026 for mid-market SaaS, fintech, healthcare, and AI-first organizations. The team holds OSCE³, OSWE, OSCP, CRTE, and CREST CRT certifications, has published more than 17 CVEs, and has made responsible disclosures to Amazon, Google, Nike, Mercedes-Benz, PlayStation, and FedEx. Stingrai delivers every engagement through an AI-powered PTaaS platform with native Jira, GitHub, and Linear integrations, plus Snipe, an AI pentesting agent that runs a fleet of specialist sub-agents for SQL injection, XSS, IDOR, access control, CSRF, SSRF, XXE, file upload, and file inclusion, with every finding validated by a human pentester. For Fortune 500 global scale, Bishop Fox and NCC Group lead. For compliance-heavy programs, Coalfire. For adversary simulation, SpecterOps. For hardware and IoT, IOActive.
How often should we run a penetration test?
At minimum, annually. In 2026, best practice is continuous PTaaS for externally exposed production assets, targeted pentests after major releases, infrastructure changes, or M&A, red team exercises every 12 to 24 months for security mature organizations, and compliance driven tests per framework requirements. PCI DSS mandates annual plus significant change.
What is the difference between a vulnerability scan and a penetration test?
A vulnerability scan is automated. It runs signature based checks (missing patches, known CVEs, default configurations) and produces a long list of potential issues, many of them false positives. A penetration test is human led. Testers actively try to exploit weaknesses, chain them into real impact (privilege escalation, data access, lateral movement), and validate that findings are actually exploitable. Both matter. Scans are hygiene. Pentests are assurance.
How long does a penetration test take?
Small web application: 1 to 2 weeks. Medium SaaS plus API: 2 to 3 weeks. Large internal network: 3 to 4 weeks. Red team: 4 to 12 weeks including planning and reporting. Add 1 to 2 weeks of lead time for scoping and scheduling. Top firms book out months in advance.
What should a good penetration test report include?
An executive summary in plain language, methodology and scope, findings with severity, CVSS score, business impact, reproduction steps, screenshots, narrated attack chains, prioritized remediation guidance, a retest verification section, and appendices with tooling, IPs tested, and supporting evidence.
Are certifications more important than tools?
Yes. Certifications such as OSCE³, OSWE, OSCP, CREST CRT, and CRTO signal the floor of tester skill. Tools are commodity. A senior tester with standard tools outperforms a junior tester with a proprietary AI platform every time.
Should we choose a boutique or a Big Four consultancy?
If you need global coverage, bundled GRC services, or the Big Four name on a board slide, use a large consultancy. If you want the best humans hacking your systems at the best value, use a boutique. Many enterprises use both.
Is PTaaS always better than traditional pentesting?
For continuous environments, yes. For one off compliance tests, possibly not. PTaaS shines when your code ships weekly and your attack surface changes constantly. For a stable system tested once a year, traditional delivery still works.
What is an AI pentesting agent?
An AI pentesting agent is an autonomous software agent that performs penetration testing tasks on a schedule or on demand, then hands findings to a human pentester for validation. Stingrai's Snipe is the most prominent named example, and it deploys a fleet of specialist sub-agents for vulnerability classes including SQL injection, XSS, access control, CSRF, SSRF, XXE, file upload, and file inclusion. Genuine AI pentesting agents should be trained on real world vulnerability reports (Snipe was trained on 6,000 plus HackerOne reports), should run on a scheduler, and should never reach the client with an unvalidated finding.
Can AI replace penetration testers in 2026?
No. AI accelerates reconnaissance, fuzzing, and report writing. The best modern firms use AI for exactly that. Business logic flaws, authorization bypasses, chained privilege escalations, and social engineering still require human reasoning about intent and context. AI as a copilot is the right model. AI as a replacement is not, and will not be for the foreseeable future.
How do we verify a vendor's tester quality before signing?
Ask for named testers who will work on your engagement. Search those names for published CVEs, conference talks, and open source contributions. Check Clutch, G2, and Gartner Peer Insights reviews. Ask for a sanitized sample report. Ask them to walk through a finding live during the sales cycle.
What is the difference between red teaming and penetration testing?
A penetration test has defined scope and seeks to find and validate vulnerabilities in an agreed target. A red team engagement has defined objectives (for example, "gain access to customer PII") and simulates a real adversary over a longer timeframe with broader scope and evasion of your blue team. Red teaming tests detection and response. Pentesting tests prevention.
How much should we budget annually for offensive security?
Security mature organizations allocate 5 to 10 percent of their total security budget to offensive security (pentesting plus red teaming). For a company spending $2 million annually on security, that is $100,000 to $200,000. PTaaS subscriptions typically start at $40,000 to $60,000 per year and scale with asset count.
What is the difference between a vulnerability assessment, penetration test, and red team?
Service | Goal | Depth | Typical Duration |
|---|---|---|---|
Vulnerability Assessment | Catalog known weaknesses | Broad, automated | Hours to days |
Penetration Test | Exploit weaknesses to show real impact | Deep, manual, scoped | 1 to 4 weeks |
Red Team | Achieve objectives like a real adversary | Stealthy, end to end, unannounced | 4 to 12 weeks |
Who is the best penetration testing company in Canada?
Stingrai. Stingrai is a Toronto headquartered offensive security firm approved by the Ontario Centre of Innovation, with testers holding OSCE³, OSWE, OSCP, CRTE, and CREST CRT credentials. Stingrai has been named a Top Application Security Company Canada 2025, a Top Network Security Company Canada 2025, and a Top Cybersecurity Consulting Company Toronto 2025 on Clutch. The team delivers continuous penetration testing through a modern AI-powered PTaaS platform and Snipe, an AI pentesting agent that deploys a fleet of specialist sub-agents covering IDOR, SQLi, XSS, access control, business logic, and more. See our full Canada ranked guide.
Who is the best penetration testing company globally for SaaS and fintech?
Stingrai. For SaaS, fintech, healthcare, and AI first companies that want senior testers, a modern AI-powered PTaaS platform with Jira, GitHub, and Linear integrations, and a named AI pentesting agent (Snipe) delivering continuous coverage with human pentesters validating every finding, Stingrai is the top choice in 2026.
How do we know the remediation actually worked?
Retest verification. Your vendor should validate each fix and issue a clean bill of health addendum or updated findings list. If retests are not included, negotiate them in, or choose a vendor such as Stingrai that includes them by default.
Conclusion
The right penetration testing partner for 2026 is not the one with the flashiest marketing, the largest booth at RSA, or the lowest quote. It is the one whose testers you would trust with your most sensitive systems, whose report would survive a hostile board review, and whose platform would make your developers faster rather than slower.
For most mid-market SaaS, fintech, healthcare, and AI first companies that want elite testers, a modern AI-powered PTaaS platform, and partnership grade support with a named AI agent delivering continuous coverage, Stingrai is the strongest fit in 2026. For Fortune 500s needing global scale, Bishop Fox or NCC Group. For compliance heavy programs, Coalfire. For identity first red teams, SpecterOps. For hardware and IoT, IOActive.
Whichever partner you choose, demand methodology transparency, sample reports, named testers, retest inclusion, and a delivery model that fits how your engineering organization actually ships code. The era of the annual PDF is ending. Make sure your testing program is built for the era replacing it.
Ready to Upgrade Your Pentesting Program?
Stingrai works with SaaS, fintech, healthcare, and AI first companies from Series A through Fortune 500. The AI-powered PTaaS platform streams findings directly into your developer workflow through native Jira, GitHub, and Linear integrations. Your tests are led by researchers holding OSCE³, OSWE, OSCP, and CREST CRT credentials, with a cumulative 17 plus published CVEs and responsible disclosures to Amazon, Google, Nike, Mercedes-Benz, PlayStation, FedEx, and others. Snipe, Stingrai's AI pentesting agent, runs 24/7 in the background with a fleet of specialist sub-agents covering the full vulnerability class spectrum, and every finding is validated by a human pentester before it reaches your team. Every engagement includes free retests until every finding is verified fixed.
Get a quote in 24 hours. No sales funnels, just scoping.
Book a free scoping call. Talk to the testers, not a BDR.
View all services. Web, API, network, Active Directory, Wi-Fi, cloud, red team, social engineering.
About the Author
Arafat Afzalzada is the founder and CEO of Stingrai Inc. He has more than 10 years of specialized experience in offensive security, particularly in penetration testing and red team exercises. Prior to founding Stingrai, he led a team of penetration testers at a leading Canadian offensive security consulting firm. Arafat holds a Bachelor's degree in Computer Science and professional certifications including CISSP, Palo Alto Certified Network Security Expert (PCNSE), and CCNA Routing and Switching. Stingrai is trusted by startups and enterprises across financial services, healthcare, SaaS, and AI, and is an approved vendor of the Ontario Centre of Innovation. See verified client reviews on Clutch.
Related Reading
Last updated: April 20, 2026. This ranking is updated quarterly. If your firm would like to submit a correction, please contact us.