The credential remained the single most reliable on-ramp into a 2025 enterprise breach. Verizon's 2025 Data Breach Investigations Report pinned compromised credentials as the initial access vector in 22% of the 12,195 confirmed breaches it analyzed and the leading initial vector for the second consecutive year, with 88% of Basic Web Application attacks involving stolen credentials. Specops's 2026 Breached Password Report analyzed more than 6 billion passwords stolen by malware in 2025 alone, six times the 1.09 billion analyzed in its 2025 edition. Microsoft's Digital Defense Report 2025 confirmed that more than 97% of identity attacks are password attacks, and that identity-based attacks surged 32% in the first half of 2025. Adversaries are signing in with credentials they bought, scraped, or stole from a malware-infected laptop hours earlier, and defender telemetry has finally caught up enough to count them.
Three forces drove the 2025-2026 picture. Stealer-log scale. HaveIBeenPwned absorbed two new Synthient corpora totalling 23 billion stealer-log records and 1.3 billion previously-unseen unique passwords across October and November 2025, with 625 million entirely new to the Pwned Passwords service. Cost of compromise. IBM's 2025 Cost of a Data Breach Report priced compromised-credential breaches at US$4.67M per incident with a 246-day mean time to identify and contain, and the US average breach cost hit a record US$10.22M. Passkey escape velocity. FIDO Alliance reported that more than 1 billion people have activated at least one passkey, 15 billion accounts now support passkeys, and 48% of the world's top 100 websites support them. The data is for CISOs, identity teams, journalists, and security buyers building 2026 budget cases.
This post is the Stingrai research team's canonical 2026 reference for password security. It assembles 90+ numeric claims from 25 named primary publishers, including Verizon, Specops Software (Outpost24), NordPass, HaveIBeenPwned, Microsoft, IBM, FIDO Alliance, SpyCloud, Recorded Future, Yubico, 1Password, Bitwarden, Keeper, Auth0/Okta, Cloudflare, ENISA, NIST, FBI IC3, and Hive Systems. Lead data is full-year 2024 and 2025 telemetry, the freshest available; primary publishers have not yet released full-year 2026 reports as of April 2026. Every figure carries its source, year, and methodology window, and every link points back to the primary publisher so any claim can be audited inline.
TL;DR: 11 labeled key stats
Credentials as initial breach vector (Verizon 2025 DBIR): 22% of 12,195 confirmed breaches, leading vector for the second consecutive year (Verizon 2025 DBIR).
Stolen credentials in Basic Web Application attacks (2025): 88% (Verizon 2025 DBIR).
Malware-stolen passwords analyzed by Specops in 2025: more than 6 billion (Specops 2026 Breached Password Report).
Identity attacks that are password attacks (Microsoft, 2025): more than 97% (Microsoft Digital Defense Report 2025).
Daily Microsoft Entra identity attacks tracked: 600 million (Microsoft, via Practical365 review of MDDR 2024).
Cost of breaches with compromised-credential initial access (2025): US$4.67M, 246-day mean time to identify and contain (IBM Cost of a Data Breach 2025).
Most-common breached password globally (Sept 2024 to Sept 2025): "123456" (NordPass Top 200, 2025).
Common passwords cracked in under one second: 78% (NordPass, 2025).
Synthient stealer-log records loaded into HaveIBeenPwned, Oct-Nov 2025: 23 billion records, 183 million unique emails (16.4 million new) plus 1.96 billion emails and 1.3 billion unique passwords (625 million new) (HaveIBeenPwned, Synthient Stealer Log and Synthient Credential Stuffing Threat Data).
People who have activated at least one passkey (FIDO, 2025): more than 1 billion (FIDO Alliance, World Passkey Day 2025).
Online accounts supporting passkeys (2025): more than 15 billion (FIDO Alliance, 2025).
Key takeaways
Stolen credentials remained the leading initial access vector in 2025, even as IBM's headline shifted to phishing. Verizon's DBIR has tracked credentials as the top vector two years running at 22%, and the IBM 2025 Cost of a Data Breach Report priced compromised-credential breaches at US$4.67M with a 246-day containment window. Where IBM noticed phishing pulling ahead in absolute frequency at 16%, the underlying outcome is the same: an attacker with a working username and password.
Infostealers, not brute force, are now the dominant credential-supply pipeline. Recorded Future indexed 1.95 billion malware combo-list credential exposures in 2025, and SpyCloud recaptured 53.3 billion distinct identity records in 2024, with the corpus growing 22% YoY. Snowflake's 2024 mass breach, which hit 165+ customer organizations including AT&T, Ticketmaster, and Santander, ran on credentials previously stolen by infostealer malware against accounts that lacked MFA.
Password reuse rates are stuck despite a decade of awareness training. 1Password's 2025 enterprise survey found 91% of workers understand the risks of password reuse but 66% reuse anyway, with enterprise (10K+) employees reusing at the highest rate (51.7%). Cloudflare measured 41% of successful logins on its protected sites involving compromised passwords between September and November 2024.
MFA adoption, where it is enforced, is a near-99% blocker. Microsoft's Digital Defense Report 2025 concluded that phishing-resistant MFA stops more than 99% of identity attacks, and only 0.003% of identity-compromise attempts use sophisticated AiTM. The catch: only 48% of companies use MFA across all apps per Yubico's 2025 survey, and 26% of respondents still consider plain username and password the most secure option.
Passkeys are no longer experimental. FIDO's 2025 metrics put adoption past the inflection point: 1 billion+ users, 15 billion+ supporting accounts, 48% of top-100 sites, 75% global awareness up from 39% two years ago. Google alone reports 800 million passkey accounts and 2.5 billion passkey sign-ins.
Methodology
Sources used: Verizon DBIR 2025 (12,195 confirmed breaches, May 2024 to October 2024 collection window, published May 2025); Specops Breached Password Report 2025 and 2026 (1.09B and 6B+ malware-stolen passwords, KrakenLabs threat-intelligence telemetry, January 2025 and January 2026); NordPass Top 200 Most Common Passwords 2025 (NordPass + NordStellar joint analysis of public breaches and dark-web repositories September 2024 to September 2025, published November 2025); HaveIBeenPwned (Pwned Passwords cumulative dataset plus Synthient Stealer Log Threat Data loaded October 21 2025 and Synthient Credential Stuffing Threat Data loaded November 5 2025); Microsoft Digital Defense Report 2025 (October 2025) and the Practical365 summary of the 2024 edition where 7,000-attacks-per-second figure is cited; IBM Cost of a Data Breach 2025 (Ponemon-aligned analysis, August 2025) and IBM X-Force Threat Intelligence Index 2025 (April 2025); FIDO Alliance World Passkey Day 2025 announcement (April 2025) and Passkey Index October 2025 (October 2025); SpyCloud Annual Identity Exposure Report 2025 (March 2025); Recorded Future 2025 Identity Threat Landscape Report (March 2026); Yubico 2025 Global State of Authentication Survey (n=18,000 across nine countries, October 2025); 1Password Access-Trust Gap Annual Report 2025; Bitwarden World Password Day 2025 Global Survey (n=2,300+ across six countries, May 2025); Keeper Workplace Password Malpractice Report (n=1,000 US, 2024); Auth0/Okta credential-stuffing telemetry; Cloudflare Application Security Report 2024 update (September to November 2024 traffic); ENISA Threat Landscape 2025 (October 2025); NIST SP 800-63B Rev 4 (current revision); FBI IC3 2024 Internet Crime Report (April 2025); Hive Systems 2025 Password Table (April 2025); Cybernews on RockYou2024 (July 2024); OWASP Top 10:2021 A07; PCI DSS 4.0 / 4.0.1 (April 2024 in force, full mandatory 31 March 2025).
Date cutoff: April 25, 2026. Lead data is full-year 2024 or 2025 telemetry where a primary publisher has released it. No 2026 retrospective stats appear because no primary publisher has released a credible full-year 2026 report yet. Statistics that could not be reached on at least one verification pass against a named primary source were dropped rather than estimated. Vendor blogs, AI-generated summaries, and aggregator articles are cited only where they constitute the public record of an event the primary source has not republished directly. Currency-converted figures are flagged inline with the FX context where applicable.
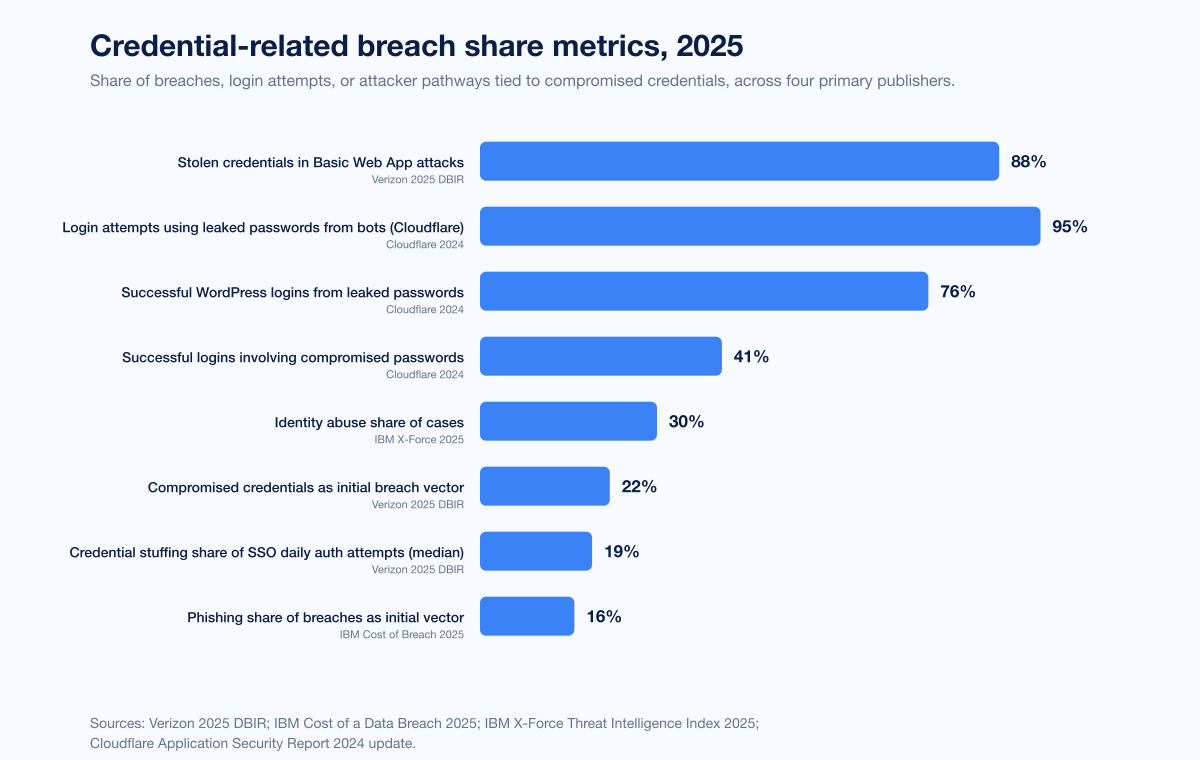
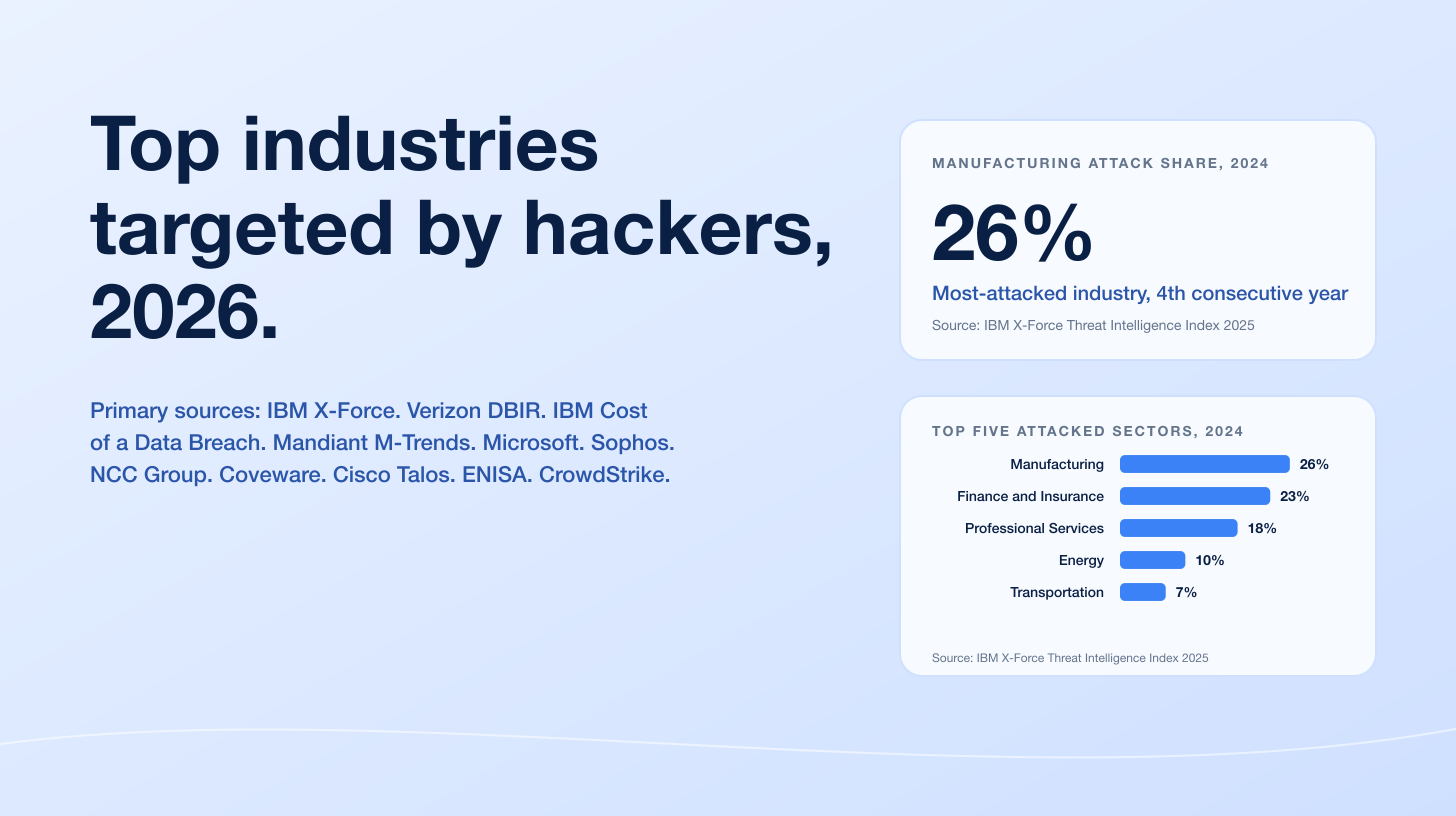
Figure 1: Credential-related breach share metrics across four primary publishers in 2025. 22% via Verizon 2025 DBIR initial access vector breakdown; 88% via Verizon 2025 DBIR Basic Web Application attacks; 30% via IBM X-Force Threat Intelligence Index 2025 identity abuse share; 41% via Cloudflare Application Security Report 2024 update on logins involving compromised passwords. Sources: Verizon 2025 DBIR; IBM X-Force Threat Intelligence Index 2025; Cloudflare.
How big is the password problem in 2026?
Three independently-collected datasets agree on the shape of the problem.
Breach-level data (Verizon DBIR)
Verizon's 2025 DBIR, the primary annual reference for breach root-cause analysis, analyzed 22,052 incidents including 12,195 confirmed data breaches. Headline credential-related findings:
Metric | 2025 DBIR figure | Source |
|---|---|---|
Compromised credentials as initial access vector | 22% (leading vector, 2nd year running) | Verizon 2025 DBIR |
Vulnerability exploitation as initial access vector | 20% | Verizon 2025 DBIR |
Stolen credentials in Basic Web Application attacks | 88% | Verizon 2025 DBIR |
Median daily share of credential stuffing in SSO authentication | 19% | |
Distinctness of passwords across services in infostealer corpora (median user) | 49% | Verizon 2025 DBIR |
The 49% distinctness figure means that in the median infostealer-stolen account view, only roughly half of a user's passwords across different services were unique. That is the practical mechanism behind credential stuffing: one password compromise leads to the next one in the same user's portfolio.
Threat-intelligence platform data (Specops 2026)
Specops's 2026 Breached Password Report, released in January 2026, analyzed more than 6 billion malware-stolen passwords captured during 2025 by the KrakenLabs team at parent company Outpost24. That is roughly six times the 1.09 billion passwords analyzed in the 2025 edition, and the increase reflects both faster infostealer scale and broader ingestion across underground marketplaces.
Headline findings from the 2025 edition (still-current dataset for password-composition analysis):
Metric | Figure | Source |
|---|---|---|
Malware-stolen passwords analyzed (12-month dataset) | 1,089,342,532 | Specops 2025 Breached Password Report |
Compromised passwords meeting standard complexity rules | 230 million | Specops 2025 Breached Password Report |
LummaC2 share of credentials in infostealer dataset | nearly 60% | Specops 2025 Breached Password Report |
RedLine share of credentials in infostealer dataset | just over 30% | Specops 2025 Breached Password Report |
The 230 million complex-but-compromised passwords is the central finding: complexity rules do not prevent compromise once an infostealer has read a credential cleartext from the user's browser. The Specops Breached Password Protection service totals more than 5.5 billion passwords as of January 2026 after a 1.3 billion add at report launch.
Aggregated breach-corpus data (HaveIBeenPwned, RockYou2024)
HaveIBeenPwned, Troy Hunt's k-anonymity password lookup service, doubled in late 2025 with two distinct loads:
Load | Date loaded | Records / emails / passwords | Source |
|---|---|---|---|
Synthient Stealer Log Threat Data | October 21, 2025 | 23 billion records, 183 million unique emails, 16.4 million entirely new emails | |
Synthient Credential Stuffing Threat Data | November 5, 2025 | 1.96 billion unique emails, 1.3 billion unique passwords, 625 million entirely new passwords |
Among HaveIBeenPwned's 5.9 million subscribers, 2.9 million were already in the Synthient Credential Stuffing dataset, meaning roughly half of users who actively self-monitor for breach exposure were already exposed in the new corpus.
Standalone, the RockYou2024 leak in July 2024 is the largest single password compilation publicly indexed: 9,948,575,739 unique plaintext passwords in a 145.25 GB file dumped on BreachForums by an actor calling themselves "ObamaCare". That dataset is a compilation of older breaches plus 1.5 billion 2021-2024 additions, sitting on top of RockYou2021's 8.46 billion baseline.
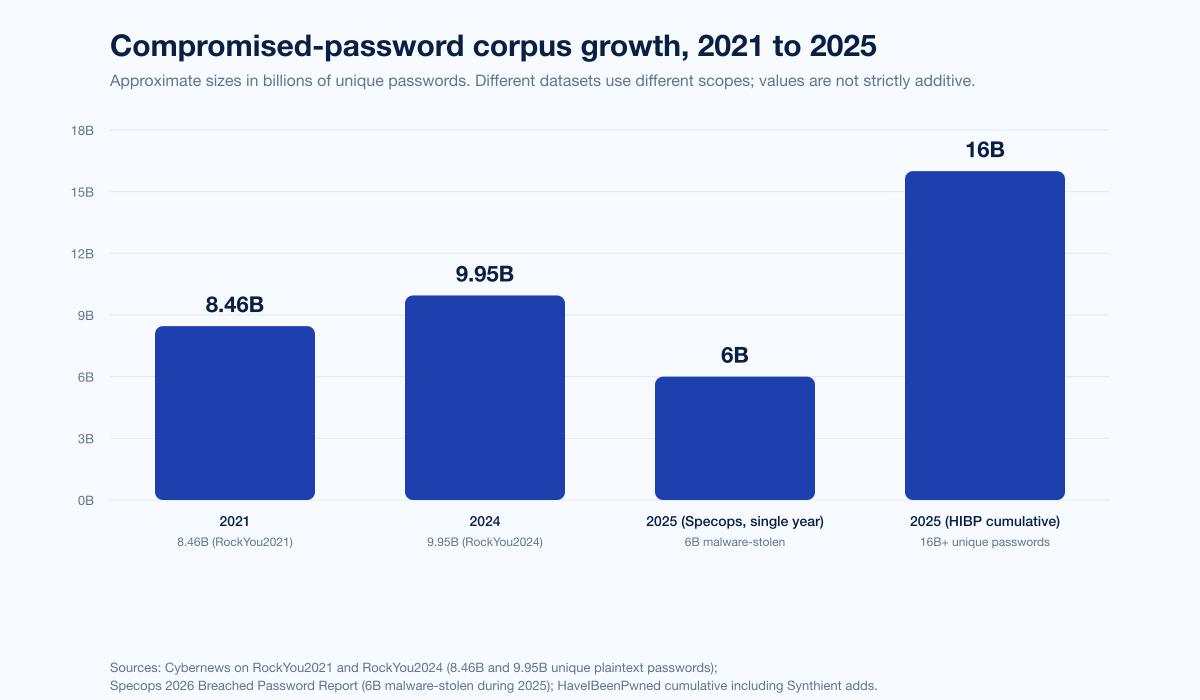
Figure 2: Approximate cumulative growth of publicly-indexed compromised-password corpora from 2021 to 2026. RockYou2021 baseline 8.46B; RockYou2024 9.95B; Specops 2026 dataset of 6B malware-stolen passwords from 2025; HaveIBeenPwned post-Synthient adds. Sources: Cybernews on RockYou2024; Specops 2026 Breached Password Report; HaveIBeenPwned Synthient breach pages.
Most common passwords in 2025 and 2026
Two annual lists set the bar.
NordPass Top 200 (September 2024 to September 2025)
NordPass and NordStellar's joint analysis of public data breaches and dark-web repositories from September 2024 to September 2025 produced the seventh annual NordPass Top 200. Anchor findings:
Metric | Figure | Source |
|---|---|---|
#1 most-common password globally, 2024-2025 | 123456 | NordPass 2025 |
#2 most-common password | Admin | NordPass 2025 |
#3 most-common password | 12345678 | NordPass 2025 |
Common passwords cracked in under 1 second | 78% | NordPass 2025 |
Top-200 passwords with at least one special character | 32 of 200 | NordPass 2025 |
Longest crack time on the top 200 list | 23 days ("admintelecom") | NordPass 2025 |
NordPass observed a small uptick in special characters across the top 200, with 32 of the 200 entries containing at least one. The defenders' rebuttal: a special character does not save a password that is on the top-200 list. Simply ensuring users do not pick a password from the top 1,000 blocks roughly half of the practical attack surface.
Specops Breached Password Report 2025 and 2026
Specops's reports ranked the top stolen passwords in malware-captured corpora as "123456", "admin", and "password" at the top in 2025, mirroring NordPass's order. The 2026 edition's headline is the corpus expansion to 6 billion. The 2025 edition's standout numeric finding remains the 230 million complex-but-compromised passwords, an empirical refutation of complexity-only policies. The dataset attributes nearly 60% of credentials to LummaC2 and just over 30% to RedLine, with infostealer attribution generally tighter than in any prior year.
Compromised-password datasets and infostealer pipelines
The 2024-2025 story is that infostealers replaced brute force as the dominant credential-supply mechanism.
SpyCloud 2025 Annual Identity Exposure Report
SpyCloud's 2025 report, published March 2025, recaptured 53.3 billion distinct identity records in 2024, a 22% YoY increase. Per-user exposure metrics:
Metric | 2024 figure | Source |
|---|---|---|
Distinct identity records recaptured worldwide, 2024 | 53.3 billion (+22% YoY) | SpyCloud 2025 |
Corporate users infected with malware | nearly 50% | SpyCloud 2025 |
Average exposed credentials per infection | 44 | SpyCloud 2025 |
Average cookies per infection | 1,861 | SpyCloud 2025 |
Stolen session cookies circulating, 2024 | 17.3 billion | SpyCloud 2025 |
Stolen credentials recaptured for third-party apps, 2024 | 7 million (+48% YoY) | SpyCloud 2025 |
Average per-corporate-user identity records | 146 | SpyCloud 2025 |
Average emails per corporate user | 13 | SpyCloud 2025 |
Average credential pairs per corporate user | 141 | SpyCloud 2025 |
Ransomware victims with prior infostealer infection | nearly 1 in 3 | SpyCloud 2025 |
The session-cookie volume is the part most CISOs miss. 17.3 billion stolen session cookies allow attackers to impersonate legitimate users without needing the password, the MFA factor, or the passkey. The defensive implication is session invalidation on every detection of infostealer exposure, not just a password reset.
Recorded Future 2025 Identity Threat Landscape
Recorded Future's 2025 Identity Threat Landscape Report, released March 2026, indexed:
Metric | 2025 figure | Source |
|---|---|---|
Malware combo-list credential exposures indexed | 1.95 billion | Recorded Future 2025 |
Database combo-list credential exposures indexed | 36 million | Recorded Future 2025 |
Credentials with active session cookies | 276 million (31% of malware-sourced creds) | Recorded Future 2025 |
Credentials indexed within 1 week of exfiltration | 53% | Recorded Future 2025 |
Credentials indexed within 24 hours | 36.4% | Recorded Future 2025 |
Credentials with identifiable authorization URLs tied to authentication systems | 63.2% (of 7M with URLs) | Recorded Future 2025 |
H2 2025 vs H1 2025 indexed credential growth | +50% | Recorded Future 2025 |
The 53% within-a-week figure is the speed of the criminal supply chain. From a stealer-log infection to a queryable indexed credential is now under a week half the time, which is shorter than the median enterprise password-rotation cadence at any organization that still uses one.
IBM X-Force Threat Intelligence Index 2025
IBM X-Force Threat Intelligence Index 2025, released April 2025, framed identity abuse as the preferred entry point in 30% of cases:
Metric | 2024 figure | Source |
|---|---|---|
Identity abuse share of cases | 30% | IBM X-Force 2025 |
Increase in phishing emails delivering infostealers, 2024 vs 2023 | +84% | IBM X-Force 2025 |
Early 2025 increase in infostealer-delivery phishing vs 2023 | +180% | IBM X-Force 2025 |
Increase in infostealer credentials for sale on dark web YoY | +12% | IBM X-Force 2025 |
Top-five infostealer dark-web ad volume 2024 | more than 8 million ads | IBM X-Force 2025 |
X-Force notes that ransomware attacks on enterprises declined while credential theft spiked, reinforcing the broader trend in IBM's Cost of a Data Breach 2025 toward "logging in, not breaking in" as the dominant pattern.
Password reuse and user behavior
Reuse is the operational mechanism that turns one breach into many.
1Password Access-Trust Gap, 2025
1Password's 2025 annual report published reuse and SSO findings:
Metric | 2025 figure | Source |
|---|---|---|
Workers who understand the risks of password reuse | 91% | 1Password 2025 |
Workers who reuse passwords anyway | 66% | 1Password 2025 |
Reuse rate, enterprise (10K+) | 51.7% | 1Password 2025 |
Reuse rate, midsize | 43.9% | 1Password 2025 |
Reuse rate, small business | 41.8% | 1Password 2025 |
Security pros saying SSO alone cannot protect identities | 7 in 10 | 1Password 2025 |
Americans who shared personal passwords without a password manager in 2025 | 47% | 1Password 2025 |
The gap between awareness (91%) and behavior (66% reuse) confirms what every security awareness team has been saying: training alone does not close behavioral gaps in password hygiene. Policy enforcement, password-manager rollout, and passkey migration close them.
Bitwarden World Password Day 2025
Bitwarden's 2025 global survey of 2,300+ employed adults across the US, UK, Australia, Germany, France, and Japan:
Metric | 2025 figure | Source |
|---|---|---|
Gen Z aware that password reuse is risky | 79% | Bitwarden 2025 |
Gen Z who reuse a password when updating accounts after a breach disclosure | 59% | Bitwarden 2025 |
Global respondents reusing across 5-10 sites | 32% | Bitwarden 2025 |
Respondents resetting passwords daily or multiple times per week | 21% | Bitwarden 2025 |
Global respondents relying on memory to manage passwords | 55% | Bitwarden 2025 |
Respondents who say a password should be secure over memorable | 68% | Bitwarden 2025 |
The 55% memory-reliance figure is the practical reason password managers under-penetrate. Users do not trust them, or have not tried one, even when they consciously prefer "secure over memorable."
Keeper Workplace Password Malpractice
Keeper's Workplace Password Malpractice Report, based on Pollfish surveys of 1,000 US full-time workers, recorded:
Metric | Figure | Source |
|---|---|---|
Workers sharing work passwords by text or email | 62% | Keeper |
Workers admitting access to a previous employer's accounts | 32% | Keeper |
Workers jotting work passwords on paper or sticky notes | 57% | Keeper |
Of those, who lost the notes | 67% | Keeper |
Offboarding hygiene is the exposed wound here. One in three workers say they can still log into a former employer's systems, which is the single most preventable account-takeover vector for any organization with an HR-to-IT process gap.
Cloudflare login-compromise telemetry
Cloudflare measured login compromise across protected sites between September and November 2024:
Metric | Figure | Source |
|---|---|---|
Successful logins involving compromised passwords | 41% | Cloudflare 2024 |
Login attempts with leaked passwords driven by bots | 95% | Cloudflare 2024 |
Successful leaked-password logins on WordPress sites | 76% | Cloudflare 2024 |
Bot-driven successful WordPress logins | 48% | Cloudflare 2024 |
Daily Cloudflare cyber-threats blocked, Q1 2024 | 209 billion (+86.6% YoY) | Cloudflare 2024 |
The 95% bot-driven figure is the credential-stuffing tell. Almost every leaked-password login attempt is automated, which is why rate-limiting, IP reputation, and proof-of-work challenges have become standard at the WAF layer in 2025-2026.
MFA adoption and the bypass problem
MFA adoption in 2025
Metric | 2025 figure | Source |
|---|---|---|
Companies using MFA across all apps | 48% | |
Respondents who consider username + password the most secure option | 26% | Yubico 2025 |
Respondents who trust SMS-based MFA | 41% | Yubico 2025 |
Companies (10K+ employees) with MFA adopted | ~87% | |
Companies requiring employees to use a password manager | ~25% | Mordor Intelligence 2025 |
Increase in passkey-and-hardware-key confidence, UK 2024 to 2025 | 17% to 37% | Yubico 2025 |
Increase in passkey-and-hardware-key confidence, US 2024 to 2025 | 18% to 34% | Yubico 2025 |
US passkey adoption, work | 18% | Yubico 2025 |
US passkey adoption, personal | 16% | Yubico 2025 |
France personal MFA usage 2024 to 2025 | 29% to 71% | Yubico 2025 |
Singapore personal MFA usage | 78% | Yubico 2025 |
The headline gap is the 48% top-line MFA-everywhere figure. More than half of surveyed organizations still leave at least one application without MFA, which is exactly where credential-stuffing attackers focus.
Microsoft daily attack volumes
Microsoft Digital Defense Report 2024 / 2025 telemetry (still-current totals):
Metric | Figure | Source |
|---|---|---|
Daily Microsoft signals processed | more than 100 trillion | Microsoft DDR 2025 |
Daily new malware attempts blocked | ~4.5 million | Microsoft DDR 2025 |
Daily identity risk detections analyzed | 38 million | Microsoft DDR 2025 |
Daily emails screened for malware and phishing | 5 billion | Microsoft DDR 2025 |
Daily Microsoft Entra identity attacks tracked | 600 million | Microsoft DDR 2024 |
Password attacks blocked per second | 7,000 | Microsoft DDR 2024 |
Identity attacks that are password attacks | more than 97% | Microsoft DDR 2025 |
H1 2025 increase in identity-based attacks | +32% | Microsoft DDR 2025 |
Token theft by malware share of identity compromise | 2.4% | Microsoft DDR 2025 |
AiTM share of identity compromise attempts | 0.003% | Microsoft DDR 2025 |
Phishing-resistant MFA effectiveness against identity attacks | over 99% | Microsoft DDR 2025 |
The 99% phishing-resistant-MFA blocker is the single most-cited identity-defense statistic of 2025-2026, and it underwrites every "deploy passkeys" and "FIDO2 hardware key" recommendation in this space. The 0.003% AiTM share is the answer to "should we panic about Tycoon2FA?": at the absolute attempt rate, sophisticated AiTM remains a small slice of what defenders see, although the absolute volume is large because the denominator is in the hundreds of millions per day.
MFA bypass: AiTM phishing kits
The 2025 AiTM-kit story is dominated by Tycoon2FA, Mamba 2FA, EvilProxy, Sneaky 2FA, and Whisper 2FA. Volume:
Metric | Figure | Source |
|---|---|---|
Monthly Tycoon2FA reach (organizations targeted) | 500,000+ orgs / month | |
Late-2025 Mamba 2FA detections | nearly 10 million | |
Share of high-volume phishing campaigns leveraging PhaaS in 2025 | 90% | Barracuda 2025 |
AiTM share of identity compromise attempts (Microsoft) | 0.003% | Microsoft DDR 2025 |
Stolen session cookies circulating dark web, 2024 | 17.3 billion | SpyCloud 2025 |
The defensive playbook against AiTM has converged on three controls: phishing-resistant MFA (FIDO2 / passkeys, which AiTM cannot replay), conditional-access policies that require token rebinding to a known device, and active monitoring for token-replay anomalies. None of these stop a successful AiTM if the user clicks; the goal is to make a successful proxy of the session unusable.
Auth0 / Okta credential-stuffing volume
Metric | Figure | Source |
|---|---|---|
Stolen credentials available on black markets | more than 15 billion | Auth0 |
Auth0 daily login attempts suspected as credential stuffing (peak) | up to 69% | Auth0 |
Snowflake-breach customer organizations affected, 2024 | 165+ |
The 69% peak figure is the worst-day-of-the-week figure, not a daily average. Even on quieter days, identity providers see double-digit percentages of inbound login attempts from credential-stuffing infrastructure.
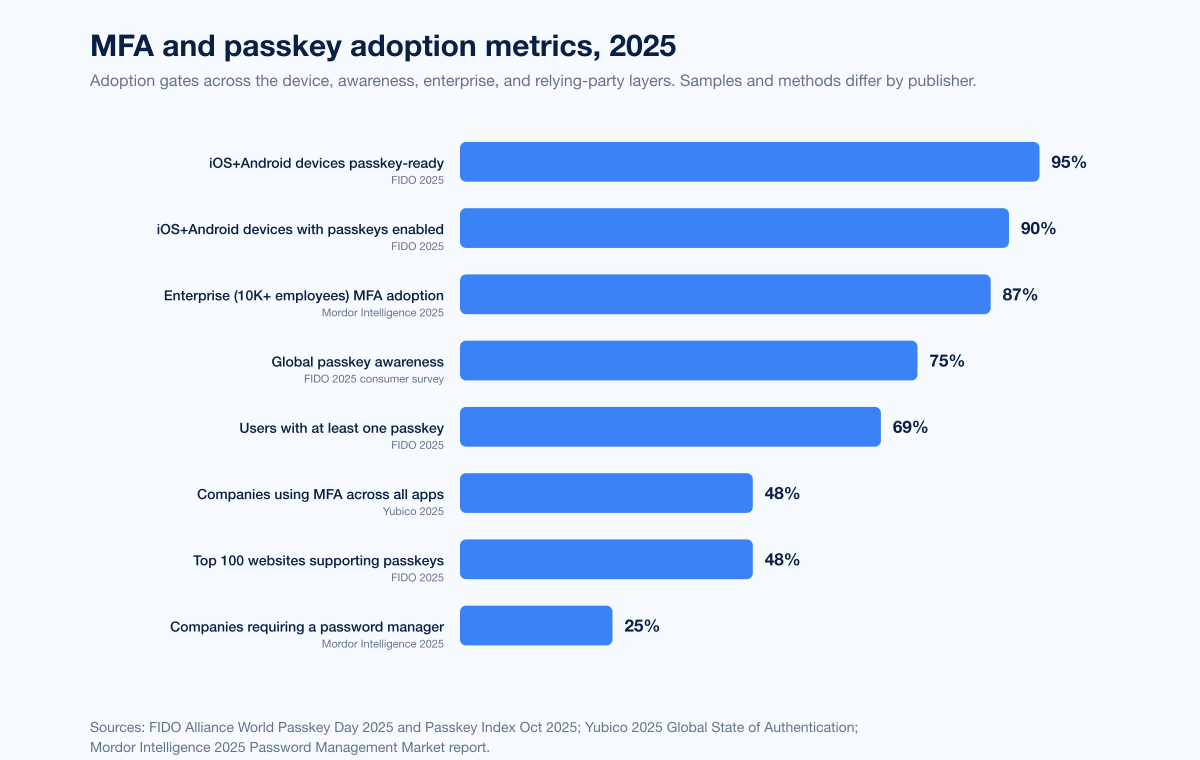
Figure 3: MFA and passkey adoption across primary publishers, 2025. 87% enterprise (10K+) MFA adoption per Mordor Intelligence; 48% companies using MFA across all apps per Yubico; 75% global passkey awareness per FIDO; 69% of users with at least one passkey per FIDO; 48% of top 100 websites supporting passkeys per FIDO. Sources: Mordor Intelligence 2025 password management market report; Yubico 2025 Global State of Authentication; FIDO Alliance World Passkey Day 2025.
Passkey adoption: from announcement to billions
Passkeys crossed mainstream-adoption thresholds during 2024 and 2025 by every measure that matters.
FIDO Alliance 2025 metrics
FIDO Alliance, World Passkey Day 2025 and Passkey Index October 2025:
Metric | 2025 figure | Source |
|---|---|---|
Global passkey awareness (consumers) | 74% to 75% | FIDO 2025 consumer survey |
Awareness change over two years | 39% to 57% | FIDO 2025 (referencing prior surveys) |
Users with at least one passkey | 69% | FIDO 2025 |
People who have activated at least one passkey | over 1 billion | FIDO 2025 |
Online accounts supporting passkeys | over 15 billion | |
Top 100 websites supporting passkeys | 48% | FIDO 2025 |
Passkey conversion lift over passwords | 30% | FIDO Passkey Index Oct 2025 |
Familiar consumers who view passkeys as more convenient | 54% | FIDO 2025 |
Familiar consumers who view passkeys as more secure | 53% | FIDO 2025 |
Big-three platform metrics
Metric | Figure | Source |
|---|---|---|
Google passkey accounts | 800 million | Google / FIDO synthesis |
Google passkey sign-ins (cumulative) | 2.5 billion | Google / FIDO synthesis |
Google sign-in success rate uplift vs passwords | +30% | Google / FIDO synthesis |
Google sign-in speed uplift vs passwords | ~20% faster | Google / FIDO synthesis |
iOS + Android devices passkey-ready | over 95% | FIDO 2025 |
iOS + Android devices with passkeys enabled | over 90% | FIDO 2025 |
The 95% device-readiness figure is the single most actionable number for buyers in 2026: the platform substrate is in place. The remaining adoption gap is on the relying-party side, where 52% of top-100 sites still do not offer a passkey path.
What is left of password-only and why
Passwords will not disappear in 2026. The plausible 2026 picture, based on what primary sources actually project:
Consumer awareness of passkeys 75% (FIDO 2025) and rising. Adoption 69% of users with at least one passkey, but the median user has a single passkey and dozens of passwords.
Top-100 site coverage at 48% in 2025 (FIDO 2025), trending toward 75-80% by end of 2026 if the current quarterly cadence continues.
Enterprise rollout still uneven. Yubico's 48% MFA-everywhere figure caps the realistic enterprise passkey rollout share at the same level for 2026, since most passkey deployments are layered on top of an MFA baseline.
Long-tail business apps (LOB internal tools, legacy SaaS, country-specific banking apps) will remain password-only or password-plus-SMS for the rest of 2026.
NIST, OWASP, PCI: the regulatory floor
NIST SP 800-63B Rev 4
NIST SP 800-63B Rev 4, the current US authoritative identity guidance:
Rule | Rev 4 position |
|---|---|
Minimum password length | 8 characters |
Minimum length when password is the only authenticator | 15 characters |
Maximum password length | systems must accept at least 64 characters |
Allowed character set | full ASCII printable, spaces, Unicode |
Mandatory periodic rotation | shall not (rotate only on evidence of compromise) |
Composition rules (mixed case, digits, special chars) | recommended against |
Screening against breached / common passwords | required |
MFA | strongly encouraged |
The "no mandatory rotation" rule, hardened from "should not" to "shall not" in Rev 4, is the most-misquoted NIST guideline in enterprise compliance. The empirical justification is that mandatory 90-day rotation produces predictable user behavior (incrementing a number, swapping a single character) that does not improve security and does worsen helpdesk load.
OWASP Top 10:2021 A07
OWASP Top 10:2021 A07 - Identification and Authentication Failures lists the canonical authentication weaknesses: credential stuffing exposure, weak / well-known password permission, password recovery weakness, plaintext or weakly-hashed password storage, missing or ineffective MFA, session-ID exposure or fixation. The 2021 list is the authoritative web-app authentication category framework still in use; OWASP 2025 has a draft A07 framing under "Authentication Failures" with broader scope.
PCI DSS 4.0 and 4.0.1
PCI DSS 4.0 (in force April 2024, mandatory across all formerly-best-practice items as of March 31, 2025):
Requirement | Position |
|---|---|
8.3.6 minimum length | 12 characters (8 if legacy systems cannot support 12) |
Composition | mix of upper, lower, digit, special |
8.3.9 rotation when MFA is absent | every 90 days |
8.3.7 password reuse window | last 4 cannot be reused |
MFA | required for all non-console access into the cardholder data environment |
PCI's 12-character mandate, an upshift from the previous 7-character bar in PCI DSS 3.2.1, aligns with NIST's logic that length matters more than complexity for entropy.
Cracking economics in 2025-2026
Hive Systems's 2025 Password Table, released April 2025, used 12 RTX 5090 GPUs against bcrypt (32 iterations, factor 10) to benchmark cracking times. Headline numbers:
Password type | Hive 2025 crack time |
|---|---|
8 characters, lowercase only | 3 weeks |
8 characters, mixed case + digits + symbols | months |
10 characters, lowercase only | years |
12 characters, mixed case + digits + symbols | many years |
YoY consumer-grade GPU cracking-time reduction | -20% (faster) |
AI-grade hardware speedup vs consumer-grade | +1.8 billion percent |
Hive's headline: "shorter, simpler passwords that might have survived for years in the past are now vulnerable in months, weeks, or even days." For a credential database hashed with bcrypt at default factor 10, an 8-character lowercase password is now in the brute-force-crackable range with a single high-end consumer rig.
The math collapses entirely if the password also appears on a top-200 list. NordPass's 78%-cracked-in-under-a-second figure is for the dictionary-attack baseline, not a brute-force baseline.
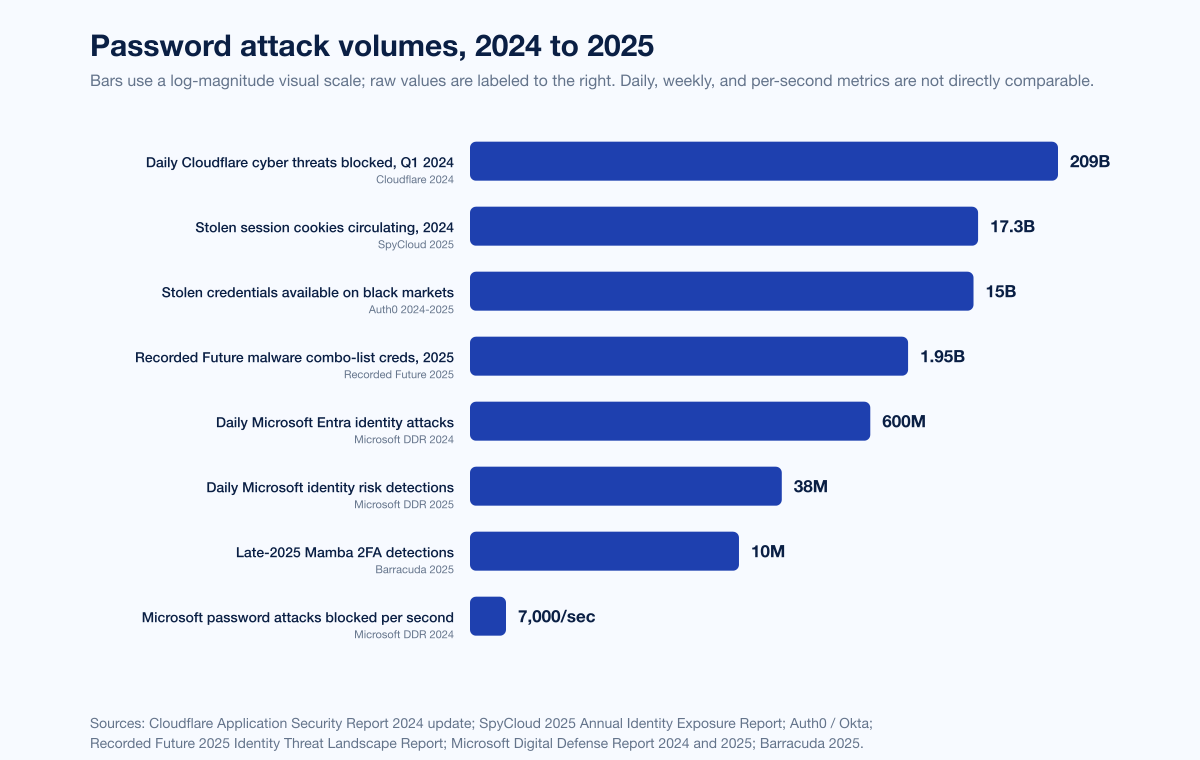
Figure 4: Password-attack volumes across four primary publishers, 2024 to 2025. 600M daily Microsoft Entra identity attacks; 7,000 password attacks blocked per second by Microsoft; 1.95B malware combo-list credential exposures indexed by Recorded Future in 2025; 17.3B stolen session cookies circulating per SpyCloud; 209B daily threats blocked by Cloudflare in Q1 2024. Sources: Microsoft Digital Defense Report 2024 / 2025; Recorded Future 2025 Identity Threat Landscape; SpyCloud 2025 Annual Identity Exposure Report; Cloudflare Application Security Report 2024 update.
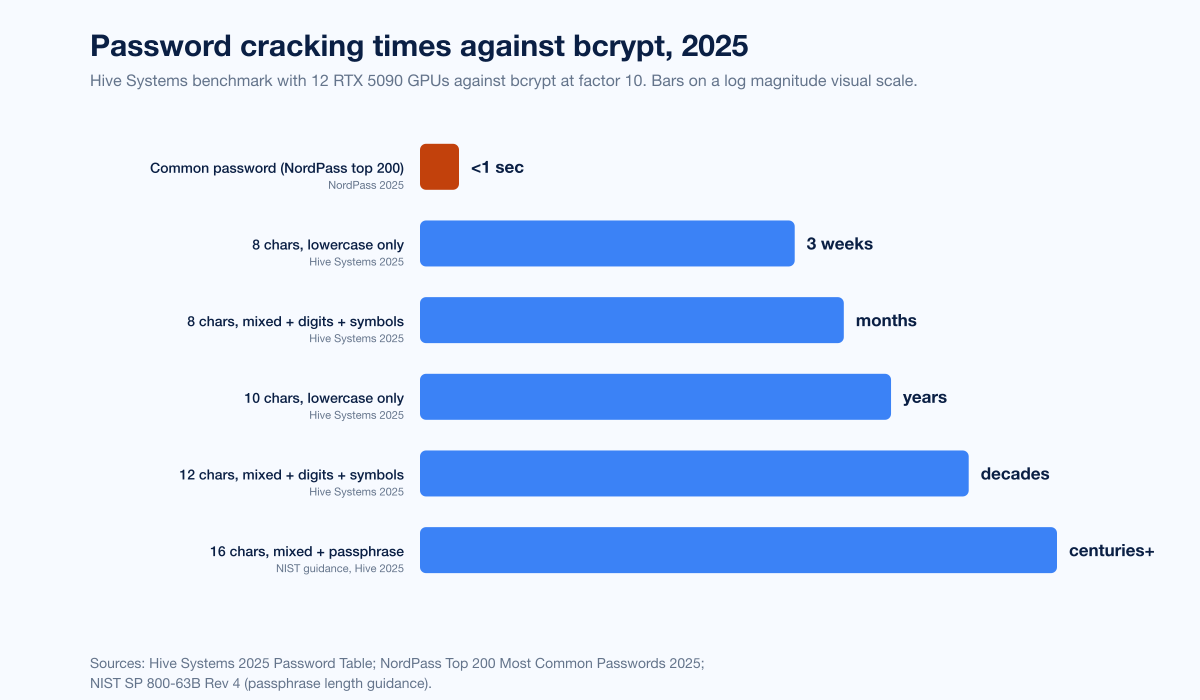
Figure 5: Hive Systems 2025 password cracking times by length and composition, against bcrypt with 12 RTX 5090 GPUs at factor 10. NordPass 2025 reports that 78% of common passwords crack in under one second by dictionary attack alone. Sources: Hive Systems 2025 Password Table; NordPass Top 200 Most Common Passwords 2025.
Cost of compromised-credential breaches
IBM Cost of a Data Breach 2025
IBM's 2025 Cost of a Data Breach Report:
Metric | 2025 figure | Source |
|---|---|---|
Global average cost of a data breach | US$4.44M (-9% YoY) | IBM 2025 |
US average cost of a data breach | US$10.22M (record high) | IBM 2025 |
Average cost of breaches initiated by compromised credentials | US$4.67M | IBM 2025 |
Mean time to identify and contain a stolen-credentials breach | 246 days | IBM 2025 |
Phishing share of breaches as initial vector | 16% | IBM 2025 |
Phishing-initiated breach average cost | US$4.8M | IBM 2025 |
Shadow-AI breach average cost | US$4.63M (+US$670K vs standard incidents) | IBM 2025 |
Two IBM-specific points worth flagging. First, although phishing tied or led credentials in initial-vector frequency in IBM's 2025 cut at 16% vs 13% from earlier preview data, the underlying outcome is functionally the same: phishing pages collect a credential, and the post-credential workflow is identical. Verizon's 2025 DBIR still ranks credentials at 22%, leading. Both can be true; the reports use different breach corpora and methodologies. Second, the 246-day containment window for credential-initiated breaches is the most operationally damaging figure in the entire IBM corpus, because it is the difference between catching an attacker before they pivot and discovering them after data exfil.
FBI IC3 2024 Internet Crime Report
FBI IC3's 2024 Internet Crime Report, April 2025:
Metric | 2024 figure | Source |
|---|---|---|
Total complaints | 859,532 | FBI IC3 2024 |
Total reported losses | US$16.6B (+33% YoY) | FBI IC3 2024 |
BEC losses | US$2.77B across 21,442 incidents | FBI IC3 2024 |
Phishing complaints | 193,407 (largest single category) | FBI IC3 2024 |
BEC share of FBI IC3 reported losses | over 17% | FBI IC3 2024 |
Phishing remains the most-reported single category in IC3's victim-complaint corpus, and BEC remains the costliest single-vector category at US$2.77B in 2024 alone. Both rely on credentials at a critical step, which is why the password-statistics literature and the BEC-statistics literature increasingly cite each other.
ENISA Threat Landscape 2025
Metric | 2025 figure | Source |
|---|---|---|
Phishing share of EU intrusions | 60% | ENISA 2025 |
Global phishing campaigns using AI-generated or AI-enhanced content | over 80% | ENISA 2025 |
Most prevalent infostealer in 2025 (EU) | Lumma | ENISA 2025 |
ENISA's 60% figure tracks closely with FBI IC3's phishing-as-leading-category finding and the Verizon DBIR's stolen-credential vector share, suggesting cross-Atlantic alignment on the dominant initial-access pattern.
Specific named incidents in 2024-2025
Aggregate stats are useful, but security-budget pitches need named cases.
Snowflake credential breach (mid-2024)
The 2024 Snowflake mass-customer breach was the canonical credential-failure case study of the 2024-2025 cycle. Threat actors used Snowflake account credentials previously stolen via infostealer malware to access customers' cloud-data-platform instances. The impacted customer accounts lacked MFA. More than 165 customer organizations were affected, including AT&T, Ticketmaster / Live Nation, Santander Bank, LendingTree, Advance Auto Parts, Neiman Marcus, and Bausch Health. The lesson, as the Cloud Security Alliance put it: "successful authentication only required a valid username and password" because MFA was not enforced on the customer side.
The Snowflake case is the rare large breach where the entire credential-supply chain is publicly visible: malware steals from an endpoint, credentials reach a marketplace, attackers buy or download them, and the cloud-side enforcement is too weak to require a second factor.
RockYou2024 leak (July 2024)
The RockYou2024 password compilation, dumped July 2024 on BreachForums by an actor calling themselves "ObamaCare", contained 9,948,575,739 unique plaintext passwords in a 145.25 GB file. It is the largest single password compilation publicly indexed and is essentially a corpus of every breach the dumper could find, layered on top of the prior RockYou2021 corpus of 8.46 billion passwords. RockYou2024 is the canonical reference for "any password that has ever been breached" in the wild.
Synthient corpora absorbed into HaveIBeenPwned (October-November 2025)
Two distinct loads from Synthient LLC, run by college student Benjamin Brundage in Seattle, brought the largest single-cycle ingest in HaveIBeenPwned's history:
Load | Date | Records | Source |
|---|---|---|---|
Synthient Stealer Log Threat Data | October 21, 2025 | 23B records, 183M unique emails, 16.4M new | |
Synthient Credential Stuffing Threat Data | November 5, 2025 | 1.96B emails, 1.3B unique passwords, 625M new |
The 16.4 million entirely-new emails is the most damaging operational fact: an attacker working from Synthient data had at least that many genuinely-fresh credentials to test against the rest of the internet. The 625 million new-to-HIBP passwords expanded the Pwned Passwords service's coverage to include passwords that were definitely stolen but had not been previously seen by the largest public credential-screening service.
Defender stack, 2026
The data converges on six controls that, in combination, contain the credential-supply problem.
Phishing-resistant MFA on every account that supports it. Microsoft's 99% effectiveness figure (Microsoft DDR 2025) holds at the per-attack level. FIDO2 hardware keys (Yubico, Feitian) and platform passkeys (Apple Keychain, Google Password Manager, Microsoft Authenticator) all qualify.
Password-manager rollout enforced by policy. Yubico's 48% MFA-everywhere ceiling and Mordor's ~25% password-manager mandate cap show how much room there still is. Stingrai's penetration testing engagements routinely find credential-stuffing-vulnerable applications because employees still reuse the same password across the corporate VPN, SaaS apps, and personal accounts; rolling out a password manager is the structural fix.
Breach-list screening at password set time. NIST SP 800-63B Rev 4 requires it, the Pwned Passwords k-anonymity API delivers it, and Specops sells a turnkey 5.5B-password version. Refusing any password that appears in the breach corpus closes the credential-stuffing pipeline at the source.
Session-cookie invalidation on infostealer detection. SpyCloud's 17.3B-stolen-session-cookies finding and Recorded Future's 276M-creds-with-active-cookies number are the operational case for invalidating session tokens, not just rotating passwords, on any infostealer hit. Microsoft Entra Conditional Access policies that require token rebinding to a known device are the default best practice.
Passkey migration on a cadence, starting with high-risk roles. Finance, executive, IT-admin, and engineering identities should reach passkey by mid-2026. The FIDO Passkey Index is the public source for "is my SaaS provider passkey-ready?"
Active credential-abuse monitoring and credential-leak notification. The 53%-within-a-week Recorded Future figure shows that defenders cannot wait for a quarterly credential-monitoring report; pull credentials from at least one of HaveIBeenPwned, SpyCloud, Recorded Future, or an equivalent identity-intelligence service and alert on any match against your domain.
Stingrai's red team and penetration testing engagements rehearse the credential-supply chain end-to-end: phishing campaigns that test AiTM resistance, credential-spray simulations against authentication-system VPNs and SaaS apps, and infostealer-style endpoint compromise drills that produce real cookies for session-replay testing. The stat-grade evidence above sets the prior for what an attacker is doing on day zero of an engagement; controlled offensive testing tells you which of your systems is actually downstream of that attacker's view.
Forward projection (2026 trajectory)
Projections in this section are labeled and only reflect what primary sources have explicitly stated.
FIDO Alliance projects continued passkey rollout, with passkey conversion lift at +30% over passwords as the structural argument for relying-party adoption.
Microsoft Digital Defense Report 2025 anticipates continued growth in identity-based attacks on the back of generative-AI-assisted phishing scaling and PhaaS kit accessibility.
IBM X-Force projects continued infostealer-driven credential-supply growth, with early 2025 phishing-infostealer volume already at +180% vs 2023.
Recorded Future flagged H2 2025 indexed credential growth at +50% vs H1 2025 and expects the trajectory to continue into 2026.
Specops signaled that the 6-billion-passwords-stolen-by-malware figure for 2025 will likely climb again in 2026 as infostealer ecosystems consolidate around LummaC2 and successors.
No primary source known to us as of April 25, 2026 has published a credible full-year 2026 password-statistics figure; we list no 2026 retrospective stats because none yet exist.
What this means for defenders
Treat any breach-list match as a successful authentication waiting to happen. Recorded Future's 53%-within-a-week-of-exfiltration figure is the SLA your incident-response process is competing against. Block the password, rotate the cookie, force a re-auth.
Push phishing-resistant MFA past the 48% MFA-everywhere ceiling. Yubico's data says more than half of organizations have at least one app without MFA. That one app is where the attacker is heading. Inventory every authentication boundary, prioritize by data sensitivity, and close the gaps.
Adopt passkeys on a deliberate roadmap. 48% of top-100 sites support passkeys per FIDO 2025; that means roughly half of your users' top-tier accounts are still password-only. Roll out internally first (M365 / Workspace / SSO), then trail by user-population segment.
Build credential-leak monitoring into your security operations stack. HaveIBeenPwned, SpyCloud, Recorded Future, or an equivalent. Any alert against a corporate domain triggers password reset plus session-cookie invalidation plus an endpoint compromise check.
Drop mandatory rotation, screen against breach lists. NIST SP 800-63B Rev 4 says rotate only on evidence of compromise; screen every new password against a 5.5B-entry list; allow up to 64 characters; do not impose composition rules. This is not optional under modern NIST guidance.
Rehearse the credential-supply chain in red-team engagements. Real-world AiTM resistance, infostealer-based session-replay, and credential-spray realism only show up under controlled offensive testing. Stingrai's social engineering and red team work was designed for exactly this. Stingrai, founded in 2021, runs offensive engagements where the credential pipeline is the primary test target by default.
Frequently Asked Questions
What is the most-cited password statistic for 2026?
For breach attribution, Verizon's 2025 DBIR finding that 22% of 12,195 confirmed breaches involve compromised credentials as the initial access vector is the most-cited, with credentials leading the vector for the second consecutive year. For dataset scale, Specops's 2026 Breached Password Report finding of more than 6 billion passwords stolen by malware in 2025 is the anchor. For attack volume, Microsoft's "97% of identity attacks are password attacks" carries the most weight in CISO citations and budget pitches for 2026.
How has credential abuse changed year over year?
Verizon's 2025 DBIR confirmed credentials as the leading initial vector at 22% for the second consecutive year. SpyCloud recaptured 53.3 billion distinct identity records in 2024, a 22% increase YoY. Recorded Future indexed 1.95 billion malware combo-list credential exposures in 2025, with H2 2025 producing 50% more than H1 2025. IBM X-Force measured an 84% rise in infostealer-delivery phishing emails in 2024 vs 2023, and an early-2025 increase of 180% over 2023. The common thread: infostealer-driven credential supply is growing fast and is now the primary credential-supply pipeline for credential-stuffing operators.
What was the most common password globally in 2025?
NordPass's joint analysis with NordStellar of public breaches and dark-web repositories from September 2024 to September 2025 ranked "123456" as the most-common password globally, with "Admin" at #2 and "12345678" at #3. Specops's 2025 Breached Password Report confirmed the same top three in malware-captured corpora. Both lists found that 78% of common passwords crack in under a second.
How big is the HaveIBeenPwned database in 2026?
After two distinct Synthient loads in October and November 2025, HaveIBeenPwned absorbed approximately 23 billion stealer-log records exposing 183 million unique email addresses, of which 16.4 million were entirely new, plus a credential-stuffing corpus of 1.96 billion unique email addresses and 1.3 billion unique passwords, 625 million of which were never previously seen in HIBP's Pwned Passwords service. Of HIBP's 5.9 million subscribers, 2.9 million were already in the credential-stuffing corpus.
How many people use passkeys in 2026?
FIDO Alliance reported that more than 1 billion people have activated at least one passkey, 15 billion online accounts now support passkeys, and 48% of the world's top 100 websites support them. 75% of global consumers are now aware of passkeys, up from 39% two years ago, and 69% of users have at least one passkey. Google alone reports 800 million passkey accounts and 2.5 billion passkey sign-ins.
What does Microsoft say about password attacks?
Microsoft's Digital Defense Report 2025 reports that more than 97% of identity attacks are password attacks, that identity-based attacks surged 32% in the first half of 2025, and that phishing-resistant MFA stops over 99% of identity attacks. Microsoft tracks 600 million daily Entra identity attacks and blocks roughly 7,000 password attacks per second. Token theft by malware accounts for 2.4% of identity compromise, and AiTM phishing accounts for 0.003%, although the absolute volumes of both are non-trivial because the denominator runs in the hundreds of millions per day.
How much does a credential-initiated breach cost?
IBM's 2025 Cost of a Data Breach Report priced compromised-credential breaches at US$4.67M per incident, with a 246-day mean time to identify and contain. The global average breach cost across all vectors fell to US$4.44M (-9% YoY), but the US average hit a record-high US$10.22M. Phishing-initiated breaches averaged US$4.8M and accounted for 16% of breaches in IBM's 2025 cut, putting phishing in the same cost-and-frequency band as credential breaches.
What does NIST recommend for passwords in 2026?
NIST SP 800-63B Rev 4 sets the current US federal-aligned password guidance: minimum length 8 characters (15 if password is the only authenticator), maximum length at least 64 characters, no mandatory periodic rotation (rotate only on evidence of compromise), no composition rules, full ASCII / Unicode character set allowed, breach-list screening required, MFA strongly encouraged. The "shall not require periodic rotation" rule is the single most-misquoted current guideline in enterprise compliance.
How can organizations defend against credential-based attacks?
Six controls that the data supports. First, deploy phishing-resistant MFA (FIDO2 hardware keys, platform passkeys) on every account that supports it; Microsoft's 99% blocking rate proves the case. Second, roll out password managers by policy, since Yubico's 2025 data shows 48% MFA-everywhere ceiling and Mordor's ~25% password-manager mandate. Third, screen every new password against a breached-passwords database (HIBP Pwned Passwords k-anonymity API or equivalent). Fourth, invalidate session cookies and rotate tokens whenever an infostealer hit is detected, since SpyCloud counts 17.3 billion stolen session cookies in 2024. Fifth, migrate high-risk roles to passkeys on a deliberate roadmap. Sixth, rehearse the full credential-supply chain in Stingrai's red team and penetration testing engagements so AiTM resistance, infostealer simulation, and credential-spray realism are exercised under controlled conditions.
Where can I get the latest password statistics data?
The primary publishers to track are Verizon (annual DBIR, May), Specops Software / Outpost24 (annual Breached Password Report, January), NordPass (annual Top 200, November), HaveIBeenPwned (continuous load updates), Microsoft (annual Digital Defense Report, October), IBM (Cost of a Data Breach annual, August; X-Force Threat Intelligence Index annual, April), FIDO Alliance (consumer survey at World Passkey Day in May, Passkey Index quarterly), SpyCloud (Annual Identity Exposure Report, March), Recorded Future (Annual Identity Threat Landscape Report, March), Yubico (Global State of Authentication, October), 1Password (annual report), Bitwarden (World Password Day Global Survey, May), Cloudflare (security blog), Hive Systems (annual Password Table, April), NIST (SP 800-63B Rev 4 ongoing), and FBI IC3 (annual Internet Crime Report, April). Stingrai's research blog tracks updates as primary publishers issue them.
References
Verizon. 2025 Data Breach Investigations Report. May 2025. https://www.verizon.com/business/resources/T16f/reports/2025-dbir-data-breach-investigations-report.pdf. Annual DBIR analysis of 22,052 incidents and 12,195 confirmed breaches; lead source for breach-vector attribution.
Verizon. Additional 2025 DBIR research on credential stuffing. May 2025. https://www.verizon.com/business/resources/articles/credential-stuffing-attacks-2025-dbir-research/. SSO provider log analysis on credential-stuffing daily volume share.
Specops Software (Outpost24). 2026 Breached Password Report. January 2026. https://specopssoft.com/blog/new-research-6-billion-compromised-passwords-2026/. Analysis of more than 6 billion malware-stolen passwords captured during 2025.
Specops Software (Outpost24). 2025 Breached Password Report. January 2025. https://specopssoft.com/blog/report-one-billion-malware-stolen-credentials/. Analysis of 1,089,342,532 malware-stolen passwords over a 12-month dataset.
NordPass. Top 200 Most Common Passwords 2025. November 2025. https://nordpass.com/most-common-passwords-list/. NordPass + NordStellar joint study of public breaches and dark-web repositories September 2024 to September 2025.
HaveIBeenPwned. Synthient Credential Stuffing Threat Data breach page. November 2025. https://haveibeenpwned.com/Breach/SynthientCredentialStuffingThreatData. 1.96B unique emails and 1.3B unique passwords loaded November 5, 2025.
HaveIBeenPwned. Synthient Stealer Log Threat Data breach page. October 2025. https://haveibeenpwned.com/Breach/SynthientStealerLogThreatData. 23 billion records, 183M unique emails, 16.4M new emails loaded October 21, 2025.
HaveIBeenPwned. Pwned Passwords main page. Ongoing. https://haveibeenpwned.com/Passwords. k-anonymity API for password breach screening, SHA-1 hashed corpus.
Microsoft. Digital Defense Report 2025. October 2025. https://www.microsoft.com/en-us/corporate-responsibility/dmc/en-us/corporate-responsibility/cybersecurity/microsoft-digital-defense-report-2025/. Microsoft threat telemetry across 100T+ daily signals.
Microsoft. Practical365 review of Digital Defense Report 2024. October 2024. https://practical365.com/practical-protection-the-2024-microsoft-digital-defense-report/. Reviewer summary covering 7,000-attacks-per-second figure.
FIDO Alliance. World Passkey Day 2025 announcement. April 2025. https://fidoalliance.org/fido-alliance-champions-widespread-passkey-adoption-and-a-passwordless-future-on-world-passkey-day-2025/. Consumer research n=1,389 across US, UK, China, South Korea, Japan.
FIDO Alliance. Passkey Adoption Doubles in 2024 announcement. January 2025. https://fidoalliance.org/passkey-adoption-doubles-in-2024-more-than-15-billion-online-accounts-can-leverage-passkeys/. Aggregate accounts supporting passkeys.
FIDO Alliance. Passkey Index October 2025. October 2025. https://fidoalliance.org/wp-content/uploads/2025/10/FIDO-Passkey-Index-October-2025.pdf. Tracks 30% conversion lift over passwords.
SpyCloud. 2025 Annual Identity Exposure Report. March 2025. https://spycloud.com/blog/2025-annual-identity-exposure-report/. Recaptured 53.3B distinct identity records in 2024; corporate exposure metrics.
Recorded Future. 2025 Identity Threat Landscape Report. March 2026. https://www.recordedfuture.com/blog/identity-trend-report-march-blog. 1.95B malware combo-list credential exposures, 276M with active session cookies.
IBM. Cost of a Data Breach 2025. August 2025. https://www.ibm.com/reports/data-breach. Annual breach economics study; US$4.67M cost for credential-initiated breaches.
IBM. X-Force Threat Intelligence Index 2025. April 2025. https://www.ibm.com/think/x-force/x-force-threat-intelligence-index-2025-attackers-steal-sell-user-identities. Identity abuse 30% of cases; +84% YoY infostealer phishing.
NIST. Special Publication 800-63B Rev 4: Digital Identity Guidelines. Current revision. https://pages.nist.gov/800-63-4/sp800-63b.html. US federal-aligned password and authentication guidance.
OWASP. Top 10:2021 A07: Identification and Authentication Failures. 2021. https://owasp.org/Top10/2021/A07_2021-Identification_and_Authentication_Failures/. Authoritative web-app authentication category framework.
Yubico. 2025 Global State of Authentication Survey. October 2025. https://www.yubico.com/resource/global-state-of-authentication-survey-2025-perception-vs-reality/. n=18,000 employed adults across nine countries.
1Password. The Access-Trust Gap Annual Report 2025. 2025. https://1password.com/reports/annual-report-2025. Annual enterprise security survey on reuse and SSO.
Bitwarden. World Password Day 2025 Global Survey. May 2025. https://bitwarden.com/resources/world-password-day/. n=2,300+ across US, UK, Australia, Germany, France, Japan.
Keeper Security. Workplace Password Malpractice Report. 2024. https://www.keepersecurity.com/resources/workplace-password-habits/. Keeper + Pollfish n=1,000 US full-time workers.
Auth0 / Okta. Reducing the Impact of Credential Stuffing Attacks. 2024-2025. https://auth0.com/blog/reducing-the-impact-of-credential-stuffing-attacks/. Platform telemetry on credential-stuffing daily volume.
Cloudflare. Application Security Report 2024 update. December 2024. https://blog.cloudflare.com/application-security-report-2024-update/. September to November 2024 traffic; 41% successful logins involve compromised passwords.
Cloudflare. Password reuse is rampant: nearly half of observed user logins are compromised. December 2024. https://blog.cloudflare.com/password-reuse-rampant-half-user-logins-compromised/. Reuse-focused analysis.
Hive Systems. 2025 Password Table. April 2025. https://www.hivesystems.com/password-table. RTX 5090 12-GPU bcrypt benchmark; 8-char lowercase 3-week crack time.
Cybernews. RockYou2024: 10 billion passwords leaked in the largest compilation of all time. July 2024. https://cybernews.com/security/rockyou2024-largest-password-compilation-leak/. 9,948,575,739 unique plaintext passwords; 145.25 GB file.
FBI Internet Crime Complaint Center. 2024 Internet Crime Report. April 2025. https://www.ic3.gov/AnnualReport/Reports/2024_IC3Report.pdf. 859,532 complaints; US$16.6B losses; BEC US$2.77B across 21,442 incidents.
ENISA. Threat Landscape 2025. October 2025. https://www.enisa.europa.eu/sites/default/files/2025-11/ENISA%20Threat%20Landscape%202025.pdf. EU-wide threat picture; 60% of intrusions begin with phishing; 80%+ AI-enhanced phishing campaigns.
Microsoft Security Blog. Inside Tycoon2FA: How a leading AiTM phishing kit operated at scale. March 2026. https://www.microsoft.com/en-us/security/blog/2026/03/04/inside-tycoon2fa-how-a-leading-aitm-phishing-kit-operated-at-scale/. Tycoon2FA reach 500K+ orgs/month worldwide.
Barracuda Networks. Threat Spotlight: How phishing kits evolved in 2025. January 2026. https://blog.barracuda.com/2026/01/07/threat-spotlight-phishing-kits-evolved-2025. ~10M Mamba 2FA attacks; 90% of high-volume phishing campaigns leverage PhaaS kits.
Cloud Security Alliance. Unpacking the 2024 Snowflake Data Breach. May 2025. https://cloudsecurityalliance.org/blog/2025/05/07/unpacking-the-2024-snowflake-data-breach. Documented 165+ customer organizations affected via stolen credentials and missing MFA.
PCI Security Standards Council. PCI DSS 4.0 / 4.0.1. April 2024 in force; full mandatory March 31, 2025. https://www.pcisecuritystandards.org/. 12-character minimum for cardholder data environment authentication.
Mordor Intelligence. Password Management Market Size, Share, Trends and Industry Report 2031. 2025. https://www.mordorintelligence.com/industry-reports/password-management-market. Market sizing, MFA adoption rate, password manager adoption mandate share.
This is the Stingrai research team's 2026 password statistics reference. Stingrai, founded in 2021, is an offensive security firm that runs penetration testing, red team, and social engineering engagements for global customers. If you want to see how your authentication boundary, password-manager rollout, or session-cookie-invalidation playbook stands up to a credential-supply-chain attack, our services page lists what we run and how to start a scoping call.