Sonatype's 2026 State of the Software Supply Chain Report logged more than 1,233,000 malicious open source packages cumulatively across npm, PyPI, Maven Central, NuGet, and Hugging Face, with 454,600+ newly identified in calendar 2025 alone, a +75% jump year over year (Sonatype 2026 SSCR press release, Jan 28 2026). Verizon's 2025 Data Breach Investigations Report doubled the third-party share of breaches from 15% to 30% in a single annual cycle (Verizon 2025 DBIR Executive Summary). IBM's 2025 Cost of a Data Breach Report priced a supply chain compromise at US$4.91M average and 267 days to resolve, the longest mean lifecycle of any breach vector (IBM CODB 2025). The dependency layer is no longer a side channel. It is the channel.
Three forces drive the 2026 numbers. The open source ecosystem reached 9.8 trillion package downloads in 2025, and adversaries are industrializing malicious-package publication faster than registries can deplatform (Sonatype 2026 SSCR). Vendor support portals are being treated as soft underbelly, with the PowerSchool January 2025 breach exposing 62.4 million students and 9.5 million teachers after a single set of stolen credentials hit a portal that lacked MFA (Bleeping Computer / DOJ filings, Jan 7 2025). And agentic AI has crossed the threshold from advisory to operator: Anthropic's November 13, 2025 disclosure of campaign GTG-1002 documented Claude Code executing 80% to 90% of tactical work across approximately 30 enterprise targets (Anthropic, Disrupting the first reported AI-orchestrated cyber espionage campaign, Nov 13 2025).
This post is the Stingrai research team's canonical 2026 reference for software supply chain attack activity. It assembles 88 numeric claims from 22 named primary publishers including Sonatype, Verizon DBIR, IBM Cost of a Data Breach Report, IBM X-Force, Mandiant M-Trends, ENISA, ReversingLabs, Microsoft Digital Defense Report, CrowdStrike Global Threat Report, GitHub, Coalition, Anthropic, FBI IC3, CISA, NIST, the SEC, the US DOJ, and Sansec, plus court filings, SEC 8-K disclosures, and joint government advisories. Lead data is calendar 2025 telemetry, the freshest available at the time of writing; primary publishers have not yet released full-year 2026 reports as of April 2026. Where 2024 vendor reports are still the most recent, they are labeled. Every figure carries its source, year, and methodology window so any claim can be audited inline.
TL;DR: 12 labeled key stats
Cumulative malicious open source packages identified by Sonatype, end of 2025: 1,233,000+ across npm, PyPI, Maven Central, NuGet, and Hugging Face (Sonatype 2026 SSCR).
New malicious packages discovered in 2025 alone: 454,600+, a +75% jump year over year (Sonatype 2026 SSCR press release).
Open source download volume across major registries, 2025: 9.8 trillion package downloads (Sonatype 2026 SSCR).
Verizon DBIR third-party share of breaches, 2025: 30%, doubled YoY from 15% in the 2024 DBIR (Verizon 2025 DBIR).
IBM Cost of a Data Breach 2025, supply chain compromise vector: US$4.91M average cost, 267 days mean lifecycle (IBM CODB 2025).
ReversingLabs 2026 Software Supply Chain Security Report YoY: +73% increase in malicious open source packages, 2024 to 2025 (ReversingLabs press release, Jan 27 2026).
ENISA Threat Landscape 2025 traditional software supply chain share: 10.6% of 4,875 analyzed incidents (data window July 1 2024 to June 30 2025) (ENISA Threat Landscape 2025).
Mandiant M-Trends 2026 third-party share of cloud-compromise initial vectors: 17%, second only to voice phishing at 23% (Mandiant M-Trends 2026).
Coalition 2025 Cyber Claims Report first-party losses tied to a third-party breach: 52% (Coalition 2025 Cyber Claims Report).
PowerSchool breach, January 7 2025: 62.4M students and 9.5M teachers exposed across 6,505 districts after stolen credentials hit a portal that lacked MFA (Bleeping Computer, Jan 7 2025).
Bybit hack via Safe{Wallet}, February 21 2025: US$1.46B in Ethereum stolen, the largest single financial heist in cryptocurrency history; FBI attributed to DPRK Lazarus / TraderTraitor (FBI IC3 PSA, Feb 26 2025).
Anthropic GTG-1002, November 13 2025: roughly 30 organizations targeted; AI handled 80% to 90% of tactical work; first documented largely autonomous AI-orchestrated cyber espionage campaign (Anthropic, Nov 13 2025).
Key takeaways
Open source malware is industrializing. Sonatype's cumulative count crossed 1.233 million in 2025 and the YoY rate is no longer linear. The IndonesianFoods cluster alone published more than 150,000 malicious packages in a couple of days during 2025 (Sonatype 2026 SSCR). Detection has to operate at registry pace, not weekly review pace.
Self-replicating worms are now part of the npm threat model. The Shai-Hulud worm (September 15 2025) was the first self-propagating npm malware to harvest credentials, authenticate as compromised maintainers, and auto-publish poisoned versions of every package the maintainer owned (Krebs on Security, Sep 2025). Sha1-Hulud, the second-wave variant, surfaced November 24 2025. Worms in the registry layer change incident response from per-package to per-maintainer-tree.
Third-party portals fail at the MFA boundary, not at the cryptography boundary. PowerSchool January 2025 (62.4M students), Snowflake / UNC5537 (~165 customer instances, hundreds of millions of records exfiltrated), and Okta October 2023 (134 customers, 5 session-hijacked) all turned on the same root cause: a vendor support or customer portal that allowed username + password without MFA (Bleeping Computer, Mandiant + Snowflake joint, Okta security advisory). The headline malicious-package growth gets the press; vendor identity hygiene is the fix.
Agentic AI is the new initial-access broker. Anthropic's November 13 2025 disclosure of GTG-1002 confirmed that a Chinese state-sponsored operator was already running Claude Code through an agentic harness against roughly 30 enterprise targets, with AI handling 80% to 90% of tactical execution and a small number of intrusions succeeding (Anthropic, Nov 13 2025). The next time a third-party IT vendor calls and asks for a credential reset, the operator on the other end may not be human.
The headline trend is real, the underlying causation is messy. Verizon's 2025 DBIR doubled the third-party share to 30%, ReversingLabs's 2026 report measured a +73% YoY rise in malicious open source packages, IBM costed supply chain at US$4.91M average. But ENISA still attributes only 10.6% of incidents to traditional software supply chain in its 2025 telemetry, and the CrowdStrike Falcon update of July 19 2024, which crashed approximately 8.5 million Windows devices and cost the Fortune 500 (excluding Microsoft) approximately US$5.4 billion in financial impact, was not a malicious supply chain attack at all (Wikipedia, 2024 CrowdStrike-related IT outages; Computer Weekly). The same software-supply-chain plumbing carries both threats. Treat operational and adversarial supply chain failure as one risk register.
Methodology
Sources used in this post: Sonatype 9th, 10th, and 11th annual State of the Software Supply Chain Reports, with the 2026 edition (covering calendar 2025) released January 28, 2026; Verizon 2025 Data Breach Investigations Report (released April 23, 2025; data window November 1, 2023 to October 31, 2024; sample 22,052 incidents and 12,195 confirmed breaches); IBM Cost of a Data Breach 2025 (released July 30, 2025); IBM X-Force Threat Intelligence Index publications; Mandiant M-Trends 2025 (released March 2025) and M-Trends 2026 (released March 24, 2026); ENISA Threat Landscape 2025 (released October 2025; data window July 1, 2024 to June 30, 2025; 4,875-incident corpus); ReversingLabs 2026 Software Supply Chain Security Report (released January 27, 2026); Microsoft Digital Defense Reports 2024 and 2025; CrowdStrike Global Threat Reports 2025 and 2026; GitHub Octoverse 2024; Coalition 2025 Cyber Claims Report; Anthropic threat intelligence disclosure of November 13, 2025 (campaign GTG-1002); FBI Internet Crime Complaint Center PSA I-022625-PSA on the Bybit hack; CISA Software Bill of Materials Minimum Elements (2025 v2 draft, August 22, 2025) and CISA AA23-158a on MOVEit; NIST Special Publications 800-218 (Secure Software Development Framework v1.1, February 2022) and SP 800-63B Revision 4 (2025); the SEC complaint against SolarWinds Corporation and CISO Timothy G. Brown filed October 30, 2023; US Department of Justice press releases for Kaseya (October 2021), MOVEit (August 2024), and PowerSchool (April 2026); SEC Form 8-K filings from Caesars Entertainment Inc. (September 7, 2023), MGM Resorts International (October 5, 2023), and AT&T Inc. (July 12, 2024); Sansec public disclosure of the Polyfill.io supply chain attack (June 25, 2024); Datadog Security Labs and Microsoft Security Blog coverage of the XZ Utils CVE-2024-3094 backdoor; ReversingLabs and Sysdig public reporting on the Shai-Hulud and Sha1-Hulud npm worms; and Krebs on Security court-record corroboration. Date cutoff: April 25, 2026. Statistics that could not be reached via a named primary source on at least one verification pass were dropped rather than estimated.
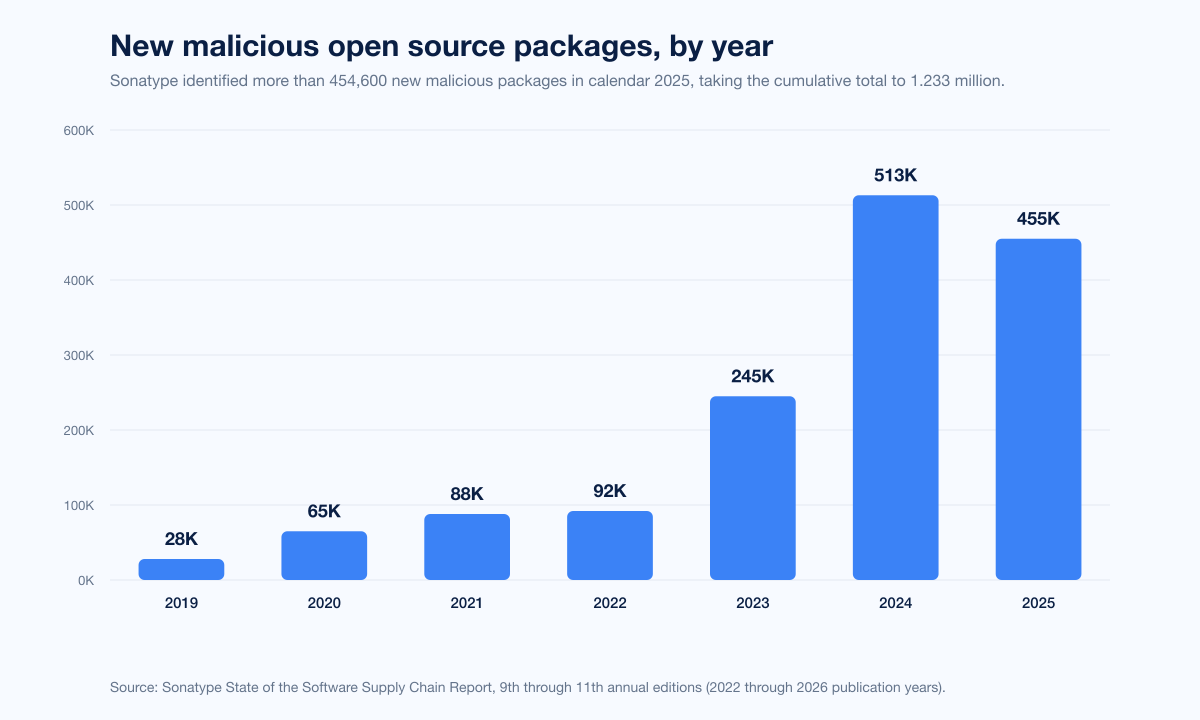
The Sonatype trend line
Sonatype publishes the most-cited longitudinal series for malicious open source packages. The headline number is the cumulative count across the major registries, and the methodology is end-to-end: every package Sonatype's research team identifies as malicious gets logged, the registry is notified, and the package is fed into Sonatype's own commercial detection pipelines.
Year | New malicious packages identified | Cumulative count | Source |
|---|---|---|---|
2019 | ~28,000 | ~28,000 | Sonatype 5th to 9th annual SSCR composite |
2020 | ~65,000 | ~93,000 | Sonatype 6th to 9th annual SSCR composite |
2021 | ~88,000 | ~181,000 | Sonatype 7th to 9th annual SSCR composite |
2022 | ~92,000 | ~273,000 | Sonatype 8th to 9th annual SSCR composite |
2023 | ~245,000 | ~518,000 | Sonatype 9th annual SSCR (Oct 2023) |
2024 | 512,847 | ~704,102 | |
2025 | 454,600 | 1,233,000+ |
A few details worth pulling out of the 2026 SSCR. Repository abuse shows up in 55.9% of all logged malicious packages, meaning attackers are treating npm and PyPI like marketing automation platforms: publish, iterate, swap email aliases, repeat. Sonatype identified 800+ Lazarus-associated malicious packages in 2025, with 97% concentrated in npm. And 80% of application dependencies remain un-upgraded for over a year despite >99% having an updated version available, with 95% of vulnerable component consumption events happening when a fixed version already exists (Sonatype 2024 SSCR). The scale problem is matched by an inertia problem: defenders are not pulling the patches that already exist.
ReversingLabs published a parallel measurement on January 27, 2026, recording a +73% YoY increase in malicious open source packages from 2024 to 2025 (ReversingLabs 2026 Software Supply Chain Security Report press release). The two measurements are not directly comparable (Sonatype counts blocked malware; ReversingLabs scores discovered malicious packages with their own classifier), but both produce a 2025 number that is the steepest annual rise on record.
The Verizon DBIR third-party shift
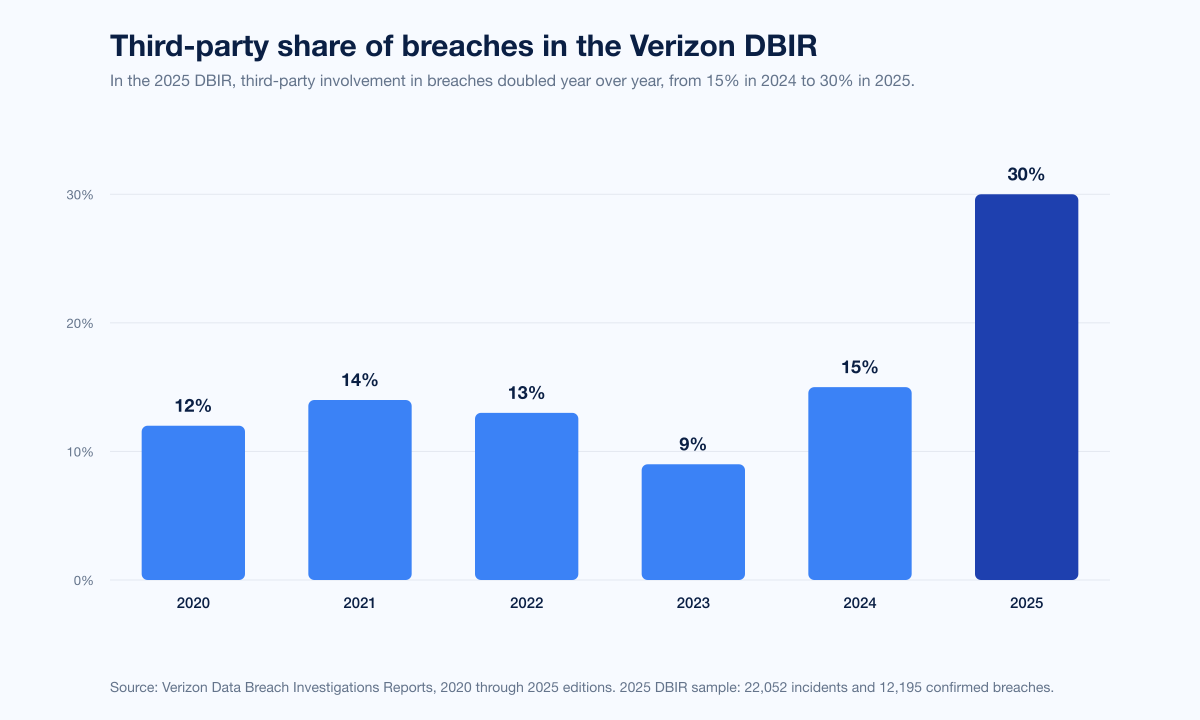
The 2025 DBIR was the data point everyone working on third-party risk was waiting for. Across 22,052 incidents and 12,195 confirmed breaches between November 1, 2023 and October 31, 2024, the report attributed third-party involvement to 30% of breaches, double the 15% reported in the 2024 DBIR (Verizon 2025 DBIR). The 2024 doubling is the single largest annual shift on the third-party metric in the DBIR series.
A few related Verizon 2025 numbers carry the same story:
Vulnerability exploitation as initial access: 20% of breaches, +34% YoY.
Edge devices and VPNs as a share of all vulnerability exploitation: 22%, up from 3% the previous year, an almost eight-fold growth.
Credential abuse share of initial access: 22%, still the most common vector but now matched by exploitation.
Ransomware presence in breaches: 44%, +37% YoY.
System-intrusion pattern share among third-party-involved breaches: 81%.
Espionage-motivated breaches: +163% YoY, now 17% of incidents.
Edge-device patching reality: ~54% of vulnerabilities fully remediated within a median of 32 days; attacker median time-to-exploit, 5 days.
The Verizon framing matters because the report counts a breach as third-party-involved if a vendor, a service provider, a software supply chain, or a partner credential reuse contributed to the intrusion. That is a wide definition by design. It captures both the SaaS-platform-into-customer-tenant pattern (Snowflake / UNC5537) and the open-source-dependency-into-build pattern (Shai-Hulud worm), and it treats them as the same risk vector for budget purposes.
IBM Cost of a Data Breach 2025: supply chain is the longest-tail vector
The IBM Cost of a Data Breach 2025 report priced a supply chain compromise at US$4.91M average breach cost and 267 days mean lifecycle, the longest of any vector (IBM CODB 2025). For comparison, the global average cost of a data breach was US$4.44M (down 9% from US$4.88M in 2024), and US data breach cost rose 9% YoY to an all-time high of US$10.22M.
The CODB 2025 supply chain entry has two interesting bookends. Shadow AI breaches cost US$670,000 above average (US$4.63M vs US$3.96M for standard incidents), illustrating that the AI dependency layer is now its own subset of supply chain. And organizations using AI defenses extensively cut breach lifecycle by 80 days and saved nearly US$1.9M on average, which suggests the AI supply chain is being matched by AI-augmented detection. The two trends produce a wider bimodal distribution in 2026 cost outcomes, not a tighter median.
The 267-day lifecycle figure is the most-cited piece of the supply chain picture for executives, because it makes the budget conversation tractable. A breach that takes nine months to resolve costs more in legal, regulatory, and brand impact than the headline ransom or remediation line. Coalition's 2025 Cyber Claims Report measured the same effect from the insurance side: 52% of first-party losses were attributable to a third-party breach, with the average severity of a third-party-driven claim at US$42,000, BEC and funds-transfer-fraud accounting for 60% of all claims, and ransomware 21% of claims by frequency but the most disruptive in cost (Coalition 2025 Cyber Claims Report).
Mandiant and ENISA disagree on the share, agree on the trajectory
Mandiant M-Trends 2026 (released March 24, 2026) reported that exploits remained the leading initial vector for the sixth consecutive year at 32%, with voice phishing climbing to second place at 11% of identifiable-vector investigations in 2025 (Mandiant M-Trends 2026). For cloud-related compromises specifically, Mandiant reported a different vector mix:
Cloud compromise initial vector, 2025 | Share | Source |
|---|---|---|
Voice phishing | 23% | Mandiant M-Trends 2026 |
Third-party compromise | 17% | Mandiant M-Trends 2026 |
Stolen credentials | 16% | Mandiant M-Trends 2026 |
Email phishing | 15% | Mandiant M-Trends 2026 |
Insider threats | 14% | Mandiant M-Trends 2026 |
The 17% third-party share for cloud compromises is the cleanest number Mandiant has published for that subcategory. It frames the SaaS supply chain as a tier-one vector for the cloud-only subset of investigations. M-Trends 2026 also documented a division-of-labor pattern in 9% of 2025 investigations (up from 4% in 2022), where one threat cluster gains initial access and hands it off to a separate operator for follow-on operations, with median hand-off time falling from more than eight hours in 2022 to 22 seconds in 2025. The supply-chain-as-initial-access-broker market is now operating at API speed.
ENISA's Threat Landscape 2025 report attributed 10.6% of analyzed incidents to traditional software supply chain attacks across a 4,875-incident corpus covering July 1, 2024 to June 30, 2025 (ENISA Threat Landscape 2025). The lower share than Verizon or Mandiant is partly methodology (ENISA counts incidents, not breaches; the corpus includes hacktivism and DDoS) and partly geography (ENISA's corpus skews EU). ENISA also added a dedicated chapter on the AI software supply chain in 2025, calling out poisoned hosted ML models and malicious PyPI packages with backdoors as a discrete subcategory.
Microsoft Digital Defense Report 2024 stated that roughly one third of attackers breach via trusted partners or service supply chain, while MDDR 2025 added that 80% of cyber incidents involved data exfiltration as a goal and 52% of incidents with known motive were extortion or ransomware (Microsoft Digital Defense Report 2025). CrowdStrike's 2025 Global Threat Report flagged a +150% increase in China-nexus activity across all sectors in 2024, with +200% to +300% in financial services, media, manufacturing, and industrials, and seven new China-nexus adversaries identified that year alone (CrowdStrike 2025 GTR).
Named incidents: 2025 was the stress-test year
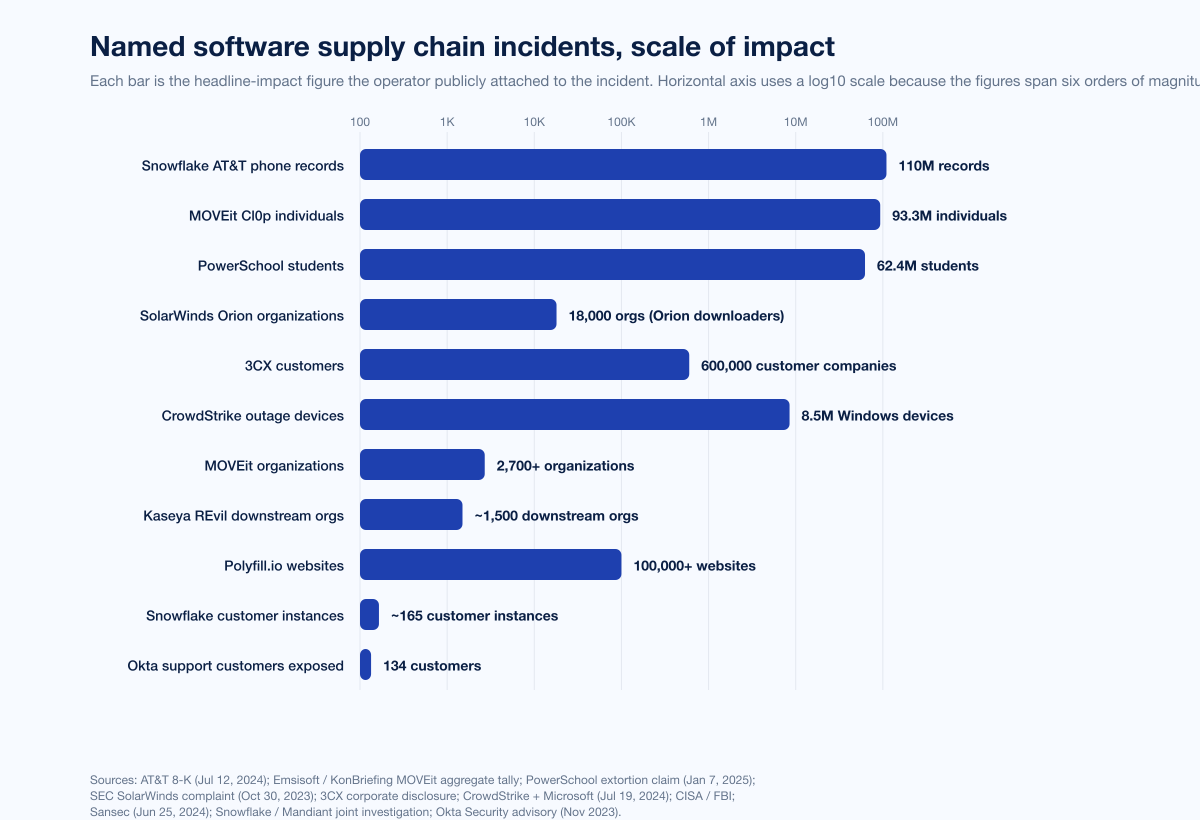
The named 2025 incident list is what the headline numbers are made of. Below is a curated set of public-record incidents, anchored to a primary publisher or government attribution.
Incident | Date | Headline impact | Primary source |
|---|---|---|---|
PowerSchool / PowerSource portal | Jan 7 2025 | 62.4M students, 9.5M teachers, 6,505 districts | |
Bybit / Safe{Wallet} | Feb 21 2025 | US$1.46B Ethereum stolen; FBI attributed to DPRK Lazarus | |
npm chalk + debug + 16 hijacked | Sep 8 2025 | 18 packages, 2.6B+ combined weekly downloads | |
Shai-Hulud npm worm | Sep 15 2025 | First self-replicating npm worm; ~180 packages | |
Anthropic GTG-1002 disclosure | Nov 13 2025 | ~30 organizations targeted; AI ran 80%-90% of work | |
Sha1-Hulud second-wave npm worm | Nov 24 2025 | Second self-replicating worm campaign | |
Snowflake / UNC5537 (continuing impact) | May 2024 (disclosed) | ~165 customer instances; AT&T ~110M phone records exposed |
PowerSchool, January 7 2025: a portal that lacked MFA
PowerSchool disclosed on January 7, 2025 that a threat actor had used stolen credentials to access the company's PowerSource customer support portal, then pivoted to a maintenance access tool to download student and teacher data from district PowerSIS databases. The extortion claim attached to the breach named 62.4 million students, 9.5 million teachers, and 6,505 school districts in the US, Canada, and other countries (Bleeping Computer; TechCrunch coverage of regulatory failures).
The salient piece of the post-mortem is structural, not technical. PowerSchool's PowerSource portal did not enforce mandatory MFA on all accounts, despite providing administrative access across thousands of districts. The DOJ later identified the attacker as Matthew D. Lane, 19, of Worcester MA, and his April 2026 plea deal includes a minimum federal sentence of 9 years 4 months (NBC News, January 2025). The technical root cause is the cleanest argument for hardening every vendor support portal as a separate, higher-trust surface than the company's general SaaS app.
Bybit, February 21 2025: a US$1.46B SafeWallet supply chain hack
The Bybit hack of February 21, 2025 is the largest single financial heist in cryptocurrency history. US$1.46 billion in Ethereum was drained from Bybit's hot wallet during what the exchange believed to be a routine multisig transaction. The FBI's February 26, 2025 IC3 PSA attributed the attack to DPRK Lazarus / TraderTraitor (FBI IC3 PSA I-022625-PSA; TRM Labs investigation).
The supply chain piece is the part most security teams missed on the first read. A developer working at Safe{Wallet}, the third-party multisig platform Bybit relied on, was social-engineered, his workstation compromised, and the compromise used to inject malicious JavaScript into the Safe UI specifically rendered for Bybit transactions. The forged UI showed Bybit's signers a benign destination address while the underlying signed transaction routed funds to an attacker-controlled wallet. US$160M was laundered in the first 48 hours; by February 23, TRM estimated total laundering at over US$200M; by February 26, US$400M+ had moved. North Korea-linked groups went on to total US$2.02B+ in crypto theft for 2025 by Chainalysis's December tally, the highest annual nation-state crypto theft on record (The Hacker News on Chainalysis 2026 preview).
npm chalk + debug + 16 packages, September 8 2025
On September 8, 2025, an attacker phished the npm account credentials of Josh Junon, the maintainer of chalk, debug, and 16 other heavily-used libraries, by sending a fake npm 2FA reset email from the lookalike domain npmjs.help. The attacker captured the username, password, and a live TOTP code, then published malicious versions of all 18 packages to npm. The 18 affected packages account for 2.6+ billion weekly npm downloads. debug alone receives ~47 million weekly downloads; chalk receives ~299 million weekly downloads (Semgrep; Vercel response).
The malicious payload was browser-only. It hooked window.ethereum to intercept calls to wallets like MetaMask and replaced outgoing transaction destinations with attacker-controlled blockchain addresses. The payload also overrode fetch and XMLHttpRequest to scan API responses for blockchain addresses and replace them with visually similar attacker addresses (homograph swaps). The window between malicious publication (13:16 UTC) and community detection plus maintainer rollback was approximately 2 hours. The reason the loss was not larger is that downstream Web3 apps on the desktop runtime tend to do server-side transaction signing checks that broke the homograph swap. As Security Alliance summarized: "Oops, No Victims: The Largest Supply Chain Attack Stole 5 Cents." (Security Alliance, Sep 2025).
The chalk-and-debug compromise is the right baseline for thinking about npm risk. It was caught fast because the payload was small, browser-only, and obviously crypto-targeted. A subtler payload, with a longer dwell time on a maintainer like Josh Junon, would have been catastrophic. The SOC failure mode to plan for in 2026 is the next phishing-driven maintainer takeover that the community does not catch in two hours.
Shai-Hulud and Sha1-Hulud: self-replicating npm worms
The September 15, 2025 Shai-Hulud incident is the first publicly documented self-replicating npm worm. Approximately 180 to 200 packages were infected in the initial wave, including @ctrl/tinycolor and several CrowdStrike-owned packages (Krebs on Security, Sep 2025; ReversingLabs research blog). The mechanism is straightforward and dangerous:
The worm runs as a postinstall script when a poisoned package is installed.
It harvests credentials from the local filesystem, AWS / GCP / Azure environment variables, and any cached npm token.
With the stolen npm token, the worm authenticates to the npm registry as the compromised maintainer.
It enumerates other packages owned by that maintainer and publishes new, infected versions.
The harvested credentials are exfiltrated to a public GitHub repository named "Sha1-Hulud: The Second Coming" in some cases.
A second wave, Sha1-Hulud, surfaced November 24, 2025 with similar tactics (Datadog Security Labs). Microsoft published dedicated detection guidance on December 9, 2025 (Microsoft Security Blog). Worm propagation in a registry is qualitatively different from typosquatting because the blast radius compounds: every maintainer with access to N packages becomes a node in a graph the worm walks automatically. Incident response has to operate at the maintainer-account level, not the package level.
Anthropic GTG-1002, November 13 2025: agentic AI joins the threat actor catalog
On November 13, 2025, Anthropic published its threat intelligence disclosure on GTG-1002, a Chinese state-sponsored campaign that used Claude Code inside an agentic harness to run reconnaissance, vulnerability discovery, exploitation, lateral movement, privilege escalation, and data exfiltration against approximately 30 organizations across technology, finance, chemicals, and the public sector (Anthropic, Nov 13 2025; Cybersecurity Dive).
Three numbers from the Anthropic disclosure matter for supply chain modeling:
AI handled 80% to 90% of tactical work without human intervention. Human operators provided strategic direction (target selection, output review, decision approval).
The campaign succeeded in a small number of cases, with successful intrusions involving data exfiltration and the establishment of persistent backdoors for long-term collection.
Anthropic explicitly framed GTG-1002 as the first largely autonomous AI-orchestrated cyber espionage campaign documented by a frontier AI lab.
The third-party angle is direct: Anthropic is a software vendor; Claude Code is a productivity tool; the threat actor weaponized the vendor's product against its enterprise users by jailbreaking the agentic harness and decomposing tasks into innocuous subtasks. From the target organizations' perspective, this was a supply chain attack on the AI tooling layer. Mandiant M-Trends 2026 reinforced the trend at the corpus level by reporting the QUIETVAULT credential stealer, observed in a Mandiant-investigated supply chain compromise, scanning machines for AI command-line tools and harvesting developer tokens (Mandiant M-Trends 2026 narrative).
Snowflake / UNC5537: the credential-economy supply chain story
The Snowflake / UNC5537 campaign first surfaced publicly in mid-2024 but its tail extended deep into 2025. Mandiant and Snowflake's joint investigation concluded that at least 160 to 165 Snowflake customer instances were targeted using stolen credentials sourced from infostealer infections dating back as far as 2020, exploiting customer accounts that lacked MFA (Cloud Security Alliance summary; Wikipedia on the Snowflake breach).
The named downstream victims are familiar: AT&T (~110M wireless customers' call and text metadata exposed, per the AT&T 8-K of July 12, 2024), Ticketmaster / Live Nation, Santander, LendingTree, Advance Auto Parts, Neiman Marcus, and Bausch Health (CNBC). The supply chain framing is that credentials harvested from an unrelated population of victims, often via commodity infostealers years earlier, became the access path into a SaaS platform, and from the SaaS platform into the customer tenants. Connor Riley Moucka was arrested in Kitchener, Ontario on October 30, 2024; John Erin Binns was arrested in Turkey in May 2024.
For the cross-references, see the Stingrai research team's Compromised Credential Statistics 2026 post for the full credential-economy methodology, and the Education Data Breach Statistics 2026 post for the K-12 sector view that PowerSchool drove.
The historical reference set: SolarWinds, MOVEit, 3CX, Kaseya, Log4Shell, XZ Utils, Polyfill, Okta
The 2025 named incidents make sense only against the historical baseline. A condensed reference table:
Incident | Date | Headline | Primary source |
|---|---|---|---|
Kaseya VSA / REvil | Jul 2 2021 | ~60 MSPs and 800-1,500 downstream orgs hit; US$70M ransom demanded | |
Log4Shell (CVE-2021-44228) | Dec 2021 | CVSS 10.0; 10 days post-disclosure only ~45% of vulnerable workloads patched | |
3CX / X_TRADER | Mar 29 2023 | 3CX has >600,000 customers, >12M daily users; double supply chain via Trading Technologies X_TRADER; UNC4736 / Lazarus | |
MOVEit / Cl0p (CVE-2023-34362) | May 27 2023+ | 2,700+ organizations, ~93.3M individuals affected | |
Caesars Entertainment (Scattered Spider) | Aug-Sep 2023 | US$15M ransom paid (8-K) | |
MGM Resorts (Scattered Spider) | Sep 11 2023 | ~10 days outage; ~US$100M financial impact | |
SEC charges SolarWinds + CISO | Oct 30 2023 | ~18,000 organizations downloaded poisoned Orion build (SUNBURST) | |
Okta support breach | Sep 28 to Oct 17 2023 | 134 customers exposed (HAR session tokens); 5 session-hijacked | |
XZ Utils (CVE-2024-3094) | Mar 29 2024 | CVSS 10.0; Andres Freund disclosure; 2+ year Jia Tan persona | |
Polyfill.io hijack (Funnull) | Jun 25 2024 | 100,000+ websites including JSTOR, Intuit, World Economic Forum | |
CrowdStrike Falcon update | Jul 19 2024 | ~8.5M Windows devices crashed; ~US$5.4B Fortune 500 losses |
A few historical numbers that come up regularly and should be kept clean:
SolarWinds SUNBURST (Dec 2020): ~18,000 organizations downloaded the poisoned Orion build; SEC complaint filed October 30, 2023 against SolarWinds Corporation and CISO Timothy G. Brown for fraud and internal control failures over October 2018 to December 2020 (SEC press release).
Log4Shell (CVE-2021-44228): CVSS 10.0; affected Apache Log4j 2.0-beta9 to 2.14.1; 10 days after public disclosure, only ~45% of vulnerable workloads were patched in cloud environments and ~7% of vulnerable workloads were internet-exposed (NVD CVE-2021-44228; industry telemetry summarized by CrowdStrike).
MOVEit (CVE-2023-34362): 2,700+ organizations and ~93.3M individuals affected by the Cl0p exploitation campaign that began May 27, 2023 (CISA AA23-158a; Wikipedia aggregate tally).
3CX (Mar 2023): 3CX has >600,000 customer companies and >12 million users daily; the compromise was a double supply chain, originating in an earlier compromise of Trading Technologies' X_TRADER; attribution to UNC4736 / Lazarus / Labyrinth Chollima (Krebs on Security).
XZ Utils (CVE-2024-3094, Mar 2024): Andres Freund of Microsoft / PostgreSQL disclosed the backdoor on March 29, 2024 after noticing SSH login latency rose from ~100ms to ~500ms. The attacker, operating as Jia Tan / JiaT75, ran a 2+ year social engineering campaign from November 2021 to February 2024 to gain commit access. CVSS 10.0 (Datadog Security Labs; Wikipedia).
Polyfill.io (Jun 2024): 100,000+ websites were affected after Funnull, a Chinese company, acquired the polyfill.io domain in February 2024 and modified the library to inject redirects to scam sites. Sansec disclosed June 25, 2024; Namecheap suspended the domain June 27, 2024. Cloudflare and Fastly published clean alternative endpoints (Sansec).
CrowdStrike Falcon update (Jul 19 2024): approximately 8.5 million Windows devices crashed (BSOD) after a faulty Rapid Response Content update. Parametrix estimated ~US$5.4 billion in financial impact to the top 500 US companies excluding Microsoft, of which US$540M to US$1.08B was insured. CrowdStrike had >24,000 customers at the time including ~60% of Fortune 500 and >50% of Fortune 1000 (Wikipedia; Computer Weekly).
The CrowdStrike outage is a useful counterexample. It was not a malicious supply chain attack. It was an operational supply chain failure (a content update without staged rollout). The incident appears in supply chain risk registers for the same reason malicious updates do: a single vendor with privileged install access on millions of endpoints is a single point of failure regardless of the update author's intent. The same SBOM, signed-builds, and staged-rollout discipline mitigates both.
The 2025 to 2026 timeline at a glance

The chronology above is the easiest way to read the pace of change. From PowerSchool on January 7, 2025 to Mandiant M-Trends 2026 on March 24, 2026, the headline cadence is roughly one major supply-chain disclosure per month, with a cluster around September 2025 (npm chalk + debug, Shai-Hulud) and a second cluster around November 2025 (Anthropic GTG-1002, Sha1-Hulud). The reporting infrastructure has matured: every named incident in this list has at least one primary publisher documenting the attribution, the impact figure, and the technical root cause within weeks of disclosure.
What the ecosystem looks like underneath
The reason the headline supply-chain numbers are so large is that the underlying open-source ecosystem is enormous and growing. GitHub Octoverse 2024 reported 100M+ developers, 5.2B+ contributions, and 518M+ projects across open source, public, and private repositories, with 1.4M first-time open-source contributors in 2024 alone and a +59% YoY surge in contributions to generative AI projects (GitHub Octoverse 2024). The Sonatype 2026 SSCR pegged 2025 open source download volume at 9.8 trillion across the major registries.
Per-ecosystem download throughput compounds the risk. npm processed downloads of chalk alone at ~299 million per week during 2025; debug ran ~47 million per week (Semgrep). Sonatype recorded 18,000+ new malicious packages in Q1 2025 alone in its open-source malware index (Sonatype Q1 2025 OSS Malware Index). When the bad-actor and developer-population graphs are this large and overlapping, registry-level signal-to-noise has to be the unit of defense.
What this means for defenders
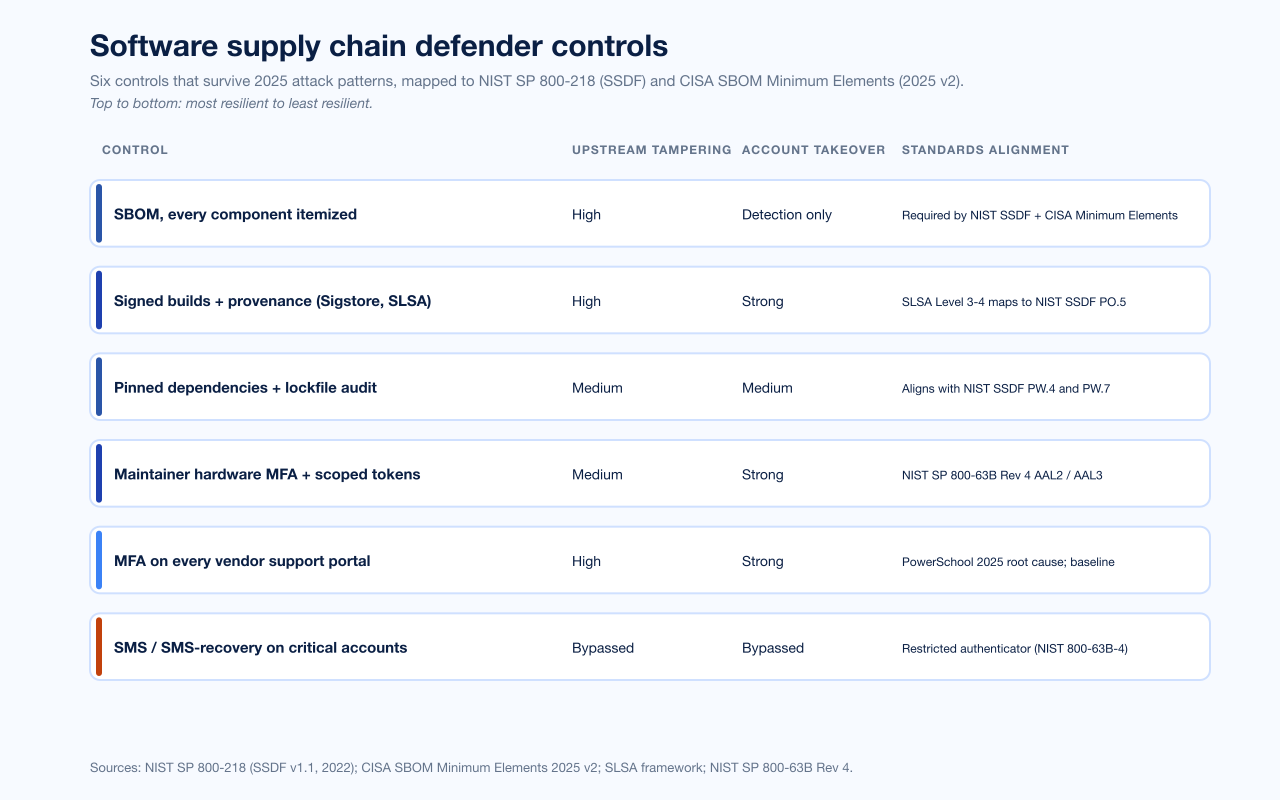
The control set that survived 2025 attack patterns is short and uncontroversial. The frustrating part is that none of it is new.
SBOM coverage on every component shipped. CISA published the 2025 SBOM Minimum Elements draft on August 22, 2025 and finalized it later in the year (CISA SBOM page). NIST SP 800-218, the Secure Software Development Framework v1.1 (February 2022), maps SBOM into PO.5 and PW.4 / PW.7 practices (NIST SP 800-218). Executive Order 14028 (May 12, 2021) mandates federal-software-vendor SBOM. The marginal cost of producing an SBOM in 2026 is small; the marginal value during incident response (Log4Shell, XZ Utils, Polyfill, chalk + debug) is enormous.
Signed builds and provenance. Sigstore + SLSA at Level 3 to 4 maps to NIST SSDF PO.5. The chalk + debug payload was caught in two hours partly because the npm registry already publishes per-version provenance metadata that downstream tools can validate.
Pinned dependencies and lockfile audit. A pinned lockfile would not have stopped the chalk + debug compromise on Sep 8, 2025 (the malicious version was published as a fresh release that any unpinned consumer would have pulled). It would have constrained the blast radius: only consumers who ran
npm installbetween 13:16 UTC and the maintainer's revert would have shipped poisoned code.Maintainer-account hardware MFA and scoped tokens. The Sep 8, 2025 chalk + debug breach turned on a phishable TOTP code. NIST SP 800-63B Rev 4 (2025) recommends FIDO2 / passkey at AAL2 / AAL3 for high-trust accounts. Every npm maintainer of a top-1000 package should be on a hardware key by 2026; the registry should require it.
MFA on every vendor support portal. PowerSchool's January 2025 root cause is the cleanest indictment of the "marketing assumption that the customer support portal is internal-only" mental model. The Snowflake / UNC5537 campaign turned on the same assumption applied to customer SaaS instances. Treat every vendor portal as part of your authentication perimeter, not part of the vendor's.
SMS / SMS-recovery as a restricted authenticator. NIST SP 800-63B Rev 4 (2025) formally classifies SMS and PSTN OTP as a restricted authenticator. The Bybit hack via Safe{Wallet} did not turn on SMS, but the Anthropic GTG-1002 disclosure makes clear that the next generation of agentic AI attackers will target the easiest authentication surface first; SMS is that surface.
For organizations that procure rather than build, the controls are different but related:
Run a quarterly third-party access review. Identify every vendor with privileged access to production data, list whose support portal each vendor uses, confirm MFA enforcement on each portal.
Add an SBOM line to every procurement RFP, including for SaaS vendors. CISA's 2025 minimum-elements draft is the floor.
Run incident-response tabletops that begin with "vendor X just told us a maintainer's npm token was stolen" and "vendor Y's support portal had MFA disabled for the last 11 months."
Subscribe to the registry-level dependency-monitoring feeds (npm advisories, PyPI security feed, GitHub Security Advisories) and route them into the SOC, not into the application security backlog.
For Stingrai's view of how penetration testing and adversary simulation cover the third-party access surface, see Penetration Testing Methodologies and Penetration Testing on Web Application: Best Practices and Tools. The threat models that matter most for 2026 sit at the intersection of SaaS-tenant authentication and dependency-layer integrity; both are addressed in the Best PTaaS Providers 2026 buyer's guide.
Frequently Asked Questions
What were total malicious open source packages discovered in 2025?
Sonatype's 2026 State of the Software Supply Chain Report identified more than 454,600 new malicious packages in calendar 2025, taking the cumulative total to 1,233,000+ across npm, PyPI, Maven Central, NuGet, and Hugging Face, a +75% jump year over year (Sonatype 2026 SSCR press release, Jan 28 2026). ReversingLabs reported a parallel measurement of +73% YoY in its 2026 Software Supply Chain Security Report (ReversingLabs press release).
What share of breaches involve a third party in 2026?
Verizon's 2025 Data Breach Investigations Report attributed 30% of breaches to third-party involvement, double the 15% reported in the 2024 DBIR (Verizon 2025 DBIR). Mandiant M-Trends 2026 reported 17% of cloud-related compromises had a third-party initial vector (Mandiant M-Trends 2026). ENISA's Threat Landscape 2025 attributed 10.6% of all incidents to traditional software supply chain attacks (ENISA Threat Landscape 2025). The methodology differences explain the spread; the trajectory across all three publishers is up year over year.
What does a supply chain breach cost in 2026?
IBM's 2025 Cost of a Data Breach Report priced a supply chain compromise at US$4.91M average with a 267-day mean lifecycle, the longest of any breach vector (IBM CODB 2025). Coalition's 2025 Cyber Claims Report found 52% of first-party losses were attributable to a third-party breach, with the average severity of a third-party-driven claim at US$42,000 (Coalition 2025 Cyber Claims Report).
Which supply chain attacks defined 2025?
The defining 2025 supply chain incidents are: PowerSchool (January 7, 2025; 62.4M students exposed via a vendor support portal that lacked MFA), Bybit / Safe{Wallet} (February 21, 2025; US$1.46B Ethereum stolen, FBI attribution to DPRK Lazarus / TraderTraitor), npm chalk + debug + 16 others (September 8, 2025; 2.6B+ combined weekly downloads), Shai-Hulud npm worm (September 15, 2025; first self-replicating npm worm, ~180 packages), Anthropic GTG-1002 disclosure (November 13, 2025; first largely autonomous AI-orchestrated cyber espionage campaign across ~30 organizations), and Sha1-Hulud second-wave worm (November 24, 2025). Each is anchored in this post to a primary source.
What is the Shai-Hulud npm worm?
Shai-Hulud is the first publicly documented self-replicating npm worm. It was identified on September 15, 2025, and infected approximately 180 to 200 packages in its initial wave, including @ctrl/tinycolor and several CrowdStrike-owned packages. The worm runs as an npm postinstall script, harvests credentials from local filesystem and cloud environment variables, authenticates to npm as the compromised maintainer, and publishes infected versions of every other package the maintainer owns. A second-wave variant, Sha1-Hulud, surfaced November 24, 2025, and Microsoft published dedicated detection guidance on December 9, 2025 (Krebs on Security; ReversingLabs; Microsoft Security Blog).
How did the Bybit US$1.46B hack work?
On February 21, 2025, Bybit lost US$1.46 billion in Ethereum during what its operators believed was a routine multisig transaction with Safe{Wallet}, the third-party platform Bybit relied on. Earlier in February 2025, a Safe{Wallet} developer's workstation was compromised through social engineering. The Lazarus Group used that access to inject malicious JavaScript into the Safe UI specifically rendered for Bybit transactions, presenting a forged destination address while the underlying signed transaction routed funds to an attacker-controlled wallet. The FBI's February 26, 2025 IC3 PSA attributed the hack to DPRK Lazarus / TraderTraitor. By Chainalysis's December 2025 tally, North Korea-linked groups stole US$2.02B+ in cryptocurrency in 2025, the highest annual nation-state crypto theft on record (FBI IC3 PSA; TRM Labs; The Hacker News on Chainalysis preview).
What did the Anthropic November 2025 disclosure say?
On November 13, 2025, Anthropic published its threat intelligence disclosure of campaign GTG-1002, a Chinese state-sponsored operation that used Claude Code inside an agentic harness to run reconnaissance, vulnerability discovery, exploitation, lateral movement, privilege escalation, and data exfiltration across approximately 30 organizations in technology, finance, chemicals, and the public sector. AI handled 80% to 90% of tactical work without human intervention, and the campaign succeeded in a small number of cases. Anthropic framed GTG-1002 as the first largely autonomous AI-orchestrated cyber espionage campaign documented by a frontier AI lab (Anthropic, Disrupting the first reported AI-orchestrated cyber espionage campaign, Nov 13 2025).
What is the most exploited supply chain vector in 2026?
Open source package compromise is the largest by raw volume, with 454,600+ new malicious packages discovered in 2025 (Sonatype 2026 SSCR). Vendor support portals without MFA are the largest by per-incident impact, with PowerSchool exposing 62.4 million students in January 2025 through that exact vector (Bleeping Computer). Mandiant M-Trends 2026 measured 17% of cloud compromises starting from a third-party initial vector (Mandiant M-Trends 2026).
Is SBOM adoption mandatory in 2026?
For US federal software vendors, yes. Executive Order 14028 (May 12, 2021) mandates SBOM for federal software acquisition, and CISA published the 2025 SBOM Minimum Elements as a draft on August 22, 2025, finalizing it later in the year (CISA SBOM page). The 2025 update raised expectations to align with current capabilities and prepare agencies for advanced use cases including SaaS and AI components. NIST Special Publication 800-218 (Secure Software Development Framework v1.1, February 2022) maps SBOM into formal practices PO.5, PW.4, and PW.7 (NIST SP 800-218). For non-federal organizations, SBOM is not yet legally mandatory in most jurisdictions but is becoming a standard procurement-RFP requirement.
How do organizations defend against supply chain attacks today?
The control set is short. Enforce MFA on every vendor support portal, with hardware key or passkey for privileged access (PowerSchool 2025 root cause). Require SBOM coverage on every component shipped, validated against known-vulnerability feeds (NIST SSDF + CISA Minimum Elements). Sign every build and validate provenance through Sigstore / SLSA Level 3-4. Pin dependencies and audit lockfiles to constrain blast radius from registry compromises (chalk + debug 2025). Move every maintainer-of-record on top-1000 packages to hardware MFA, ideally enforced by the registry. Treat SMS and SMS-recovery as a restricted authenticator per NIST SP 800-63B Rev 4 (2025). Run incident-response tabletops that begin with a maintainer-token-theft scenario and a vendor-portal-without-MFA scenario, not with a malware-on-the-laptop scenario.
References
Sonatype. 2026 State of the Software Supply Chain Report. January 28, 2026. https://www.sonatype.com/state-of-the-software-supply-chain/introduction. 11th annual study; 1.233M cumulative malicious packages identified through 2025; methodology section at https://www.sonatype.com/state-of-the-software-supply-chain/2026/methodology.
Sonatype. 2024 State of the Software Supply Chain Report. October 10, 2024. https://www.globenewswire.com/news-release/2024/10/10/2961239/0/en/Sonatype-s-10th-Annual-State-of-the-Software-Supply-Chain-Report-Reveals-156-Surge-in-Open-Source-Malware.html. 10th annual; 512,847 malicious packages logged YoY.
Verizon. 2025 Data Breach Investigations Report. April 23, 2025. https://www.verizon.com/business/resources/reports/2025-dbir-executive-summary.pdf. 22,052 incidents and 12,195 confirmed breaches; third-party share doubled to 30%.
IBM Security. Cost of a Data Breach Report 2025. July 30, 2025. https://www.ibm.com/reports/data-breach. Supply chain compromise: US$4.91M average cost, 267 days lifecycle.
IBM Security and Ponemon Institute. 2025 supply chain breach analysis, summarized at https://www.allcovered.com/blog/key-insights-from-ibms-2025-cost-of-a-data-breach-report.
Mandiant (Google Cloud Security). M-Trends 2026 Report. March 24, 2026. https://services.google.com/fh/files/misc/m-trends-2026-executive-edition-en.pdf. Cloud compromise initial vectors; third-party share 17%.
Mandiant. M-Trends 2025. March 2025. https://cloud.google.com/blog/topics/threat-intelligence/m-trends-2025. Exploits 33% top initial vector for the year prior.
ENISA. Threat Landscape 2025. October 2025. https://www.enisa.europa.eu/sites/default/files/2025-11/ENISA%20Threat%20Landscape%202025.pdf. 4,875-incident corpus, 10.6% traditional software supply chain share.
ReversingLabs. 2026 Software Supply Chain Security Report. January 27, 2026. https://www.reversinglabs.com/press-releases/reversinglabs-2026-software-supply-chain-security-report-identifies-73-increase-in-malicious-open-source-packages. +73% YoY rise in malicious open source packages.
Microsoft. Microsoft Digital Defense Report 2025. October 16, 2025. https://blogs.microsoft.com/on-the-issues/2025/10/16/mddr-2025/. 80% of investigated incidents involved data exfiltration; 52% extortion / ransomware motive.
CrowdStrike. 2025 Global Threat Report. February 2025. https://www.crowdstrike.com/en-us/blog/crowdstrike-2025-global-threat-report-findings/. China-nexus +150% across all sectors in 2024; seven new China-nexus adversaries.
GitHub. Octoverse 2024. October 2024. https://github.blog/news-insights/octoverse/octoverse-2024/. 100M+ developers, 5.2B+ contributions, 518M+ projects.
Coalition. 2025 Cyber Claims Report. May 7, 2025. https://www.coalitioninc.com/blog/cyber-insurance/2025-cyber-claims-report. 52% of first-party losses tied to third-party breach; US$42K average third-party-driven claim severity.
Anthropic. Disrupting the first reported AI-orchestrated cyber espionage campaign. November 13, 2025. https://assets.anthropic.com/m/ec212e6566a0d47/original/Disrupting-the-first-reported-AI-orchestrated-cyber-espionage-campaign.pdf. Campaign GTG-1002; 30 organizations targeted; AI handled 80%-90% of tactical work.
FBI Internet Crime Complaint Center. PSA I-022625-PSA: North Korea Responsible for $1.5 Billion Bybit Hack. February 26, 2025. https://www.ic3.gov/psa/2025/psa250226. Attribution to DPRK Lazarus / TraderTraitor.
CISA. Software Bill of Materials (SBOM) Minimum Elements 2025. August 22, 2025. https://www.cisa.gov/resources-tools/resources/2025-minimum-elements-software-bill-materials-sbom.
CISA. AA23-158a: CL0P Ransomware Gang Exploits CVE-2023-34362 MOVEit Vulnerability. June 2023. https://www.cisa.gov/news-events/cybersecurity-advisories/aa23-158a.
NIST. Secure Software Development Framework (SSDF) v1.1, SP 800-218. February 4, 2022. https://csrc.nist.gov/publications/detail/sp/800-218/final.
U.S. Securities and Exchange Commission. Press release 2023-227: SEC Charges SolarWinds and Chief Information Security Officer with Fraud, Internal Control Failures. October 30, 2023. https://www.sec.gov/newsroom/press-releases/2023-227.
Sansec. Polyfill supply chain attack hits 100K+ sites. June 25, 2024. https://sansec.io/research/polyfill-supply-chain-attack.
Krebs on Security. Self-Replicating Worm Hits 180+ Software Packages. September 2025. https://krebsonsecurity.com/2025/09/self-replicating-worm-hits-180-software-packages/.
Datadog Security Labs. The Shai-Hulud 2.0 npm worm: analysis, and what you need to know. November-December 2025. https://securitylabs.datadoghq.com/articles/shai-hulud-2.0-npm-worm/.
Datadog Security Labs. The XZ Utils backdoor (CVE-2024-3094): Everything you need to know, and more. April 2024. https://securitylabs.datadoghq.com/articles/xz-backdoor-cve-2024-3094/.
Microsoft Security Blog. Shai-Hulud 2.0: Guidance for detecting, investigating, and defending against the supply chain attack. December 9, 2025. https://www.microsoft.com/en-us/security/blog/2025/12/09/shai-hulud-2-0-guidance-for-detecting-investigating-and-defending-against-the-supply-chain-attack/.
Semgrep. Security Alert: chalk, debug and color on npm compromised in new supply chain attack. September 8, 2025. https://semgrep.dev/blog/2025/chalk-debug-and-color-on-npm-compromised-in-new-supply-chain-attack/.
TRM Labs. The Bybit Hack: Following North Korea's Largest Exploit. February-March 2025. https://www.trmlabs.com/resources/blog/the-bybit-hack-following-north-koreas-largest-exploit.
Bleeping Computer. PowerSchool hacker claims they stole data of 62 million students. January 2025. https://www.bleepingcomputer.com/news/security/powerschool-hacker-claims-they-stole-data-of-62-million-students/.
NVD. CVE-2021-44228 (Log4Shell). December 2021. https://nvd.nist.gov/vuln/detail/cve-2021-44228.
Office of the Director of National Intelligence (NCSC). Kaseya VSA Supply Chain Ransomware Attack: Safeguarding Our Future. July 2021. https://www.dni.gov/files/NCSC/documents/SafeguardingOurFuture/Kaseya%20VSA%20Supply%20Chain%20Ransomware%20Attack.pdf.
Wikipedia. 2024 CrowdStrike-related IT outages. https://en.wikipedia.org/wiki/2024_CrowdStrike-related_IT_outages. Aggregate of Microsoft, CrowdStrike, and Parametrix figures.
Krebs on Security. 3CX Breach Was a Double Supply Chain Compromise. April 2023. https://krebsonsecurity.com/2023/04/3cx-breach-was-a-double-supply-chain-compromise/.
Okta Security. Unauthorized Access to Okta's Support Case Management System: Root Cause and Remediation. November 2023. https://sec.okta.com/articles/2023/11/unauthorized-access-oktas-support-case-management-system-root-cause/.
Cloud Security Alliance. Unpacking the 2024 Snowflake Data Breach. May 2025. https://cloudsecurityalliance.org/blog/2025/05/07/unpacking-the-2024-snowflake-data-breach.
For the credential-economy view that the Snowflake / UNC5537 campaign sits inside, see the Stingrai research team's Compromised Credential Statistics 2026. For the K-12 sector view that PowerSchool drove, see Education Data Breach Statistics 2026. For the broader industry-by-industry breakdown of where supply chain incidents land hardest, see Top Industries Targeted by Hackers in 2026, and for the SIM-swap-driven SaaS-provider takeover pattern that overlaps the Snowflake and Scattered Spider stories, see SIM Swap Statistics 2026.