Schools and universities became the highest-exposure third-party-risk story of the modern internet during 2024 and 2025. Comparitech's Education Ransomware Roundup for 2025 tracked 251 confirmed ransomware attacks on global education institutions, up modestly from 247 in 2024, with breached records jumping 27% year over year to 3.96 million, of which the United States carried 130 attacks with 175,000 K-12 records and 3.7 million higher-education records breached. The 2025 CIS MS-ISAC K-12 Cybersecurity Report, analyzing more than 5,000 K-12 organizations between July 2023 and December 2024, found that 82% of reporting K-12 schools experienced cyber threat impacts, with 14,000 security events and 9,300 confirmed cybersecurity incidents during the reporting period. PowerSchool's December 2024 SIS breach, the single largest disclosed exposure in the history of student data, blew through a customer-support portal that lacked multi-factor authentication and reached approximately 62 million students and 9.5 million educators across more than 18,000 North American schools. Adversaries are no longer simply encrypting district file servers; they are walking through ed-tech supply chains, harvesting cumulative decades of student PII, and monetizing the result on data-leak sites and dark-web markets.
Three forces shape the 2026 picture for education. Volume of records exposed has decoupled from incident count. Comparitech's confirmed-ransomware count rose only marginally from 247 to 251 globally between 2024 and 2025, but breached records climbed from 3.11 million to 3.96 million (+27%), driven by larger third-party blast radii rather than more attacks. Defender resilience is finally moving the curve. Sophos's State of Ransomware in Education 2025 found lower-education attacks blocked before encryption climbing from 14% to 67% in a single year, encryption rates falling to four-year lows of 29% in lower education and 58% in higher education, and median ransom payments collapsing from US$6.6M to US$800,000 in lower education and from US$4.41M to US$463,000 in higher education. Costs are bifurcating, not falling uniformly. IBM's 2025 Cost of a Data Breach Report puts the global average breach cost at US$4.44M and the US average at an all-time-high US$10.22M, with education sitting in the lower-cost industry bracket of US$3.82M-US$4.43M, while Comparitech still measures US$550,000 in daily downtime cost when a US school district is encrypted. The headline numbers for school-district CIOs, university CISOs, education-technology buyers, journalists, and policy researchers are below.
This post is the Stingrai research team's canonical 2026 reference for education-sector data breaches. It assembles 80+ numeric claims from 14 named primary publishers, including K-12 SIX, the Center for Internet Security MS-ISAC, Comparitech, Sophos, IBM, the Verizon Data Breach Investigations Report, the Identity Theft Resource Center, the FBI Internet Crime Complaint Center, Microsoft Digital Defense, ENISA, the UK Department for Science Innovation and Technology, Jisc, EDUCAUSE, and Emsisoft. Lead data is full-year 2024 and 2025 telemetry, the freshest available; primary publishers have not yet released full-year 2026 reports as of April 2026, with Q1 2026 court filings (the PowerSchool restitution sentencing, the Naviance class-action settlement, and the K12 SIX rolling incident map) being the only 2026-dated data points used. Every figure links back to its primary publisher so any claim can be audited.
TL;DR: 12 labeled key stats
Confirmed global education ransomware attacks (2025): 251, up from 247 in 2024 (Comparitech Education Ransomware Roundup 2025).
Education ransomware records breached (2025): 3.96 million, +27% YoY from 3.11 million in 2024 (Comparitech).
PowerSchool SIS breach blast radius: approximately 62 million students and 9.5 million educators across 18,000 North American schools, single compromised credential, no MFA on the customer-support portal (PowerSchool SIS Incident notice).
K-12 schools experiencing cyber threat impacts (Jul 2023 to Dec 2024): 82% of reporting organizations; 14,000 security events; 9,300 confirmed cybersecurity incidents (2025 CIS MS-ISAC K-12 Cybersecurity Report).
Lower-education attacks blocked before encryption (2025): 67%, up from 14% in 2024; higher education 38%, up from 21% (Sophos State of Ransomware in Education 2025).
Lower-education median ransom paid (2025): US$800,000, down from US$6.6M; higher-education median US$463,000, down from US$4.41M (Sophos).
Higher-education mean recovery cost excluding ransom (2025): US$0.90M, down from US$4.02M YoY, the joint lowest across all industries Sophos surveyed (Sophos).
Education sector average data-breach cost (2025): US$3.82M-US$4.43M industry bracket, below healthcare's US$7.42M and the global average of US$4.44M (IBM Cost of a Data Breach Report 2025).
Verizon DBIR 2024 education breach patterns: social engineering 42%, system intrusion 35% as the top patterns in the Educational Services chapter (Verizon DBIR 2024 Educational Services).
Daily downtime cost per US school district hit by ransomware: US$550,000 (Comparitech school-ransomware analysis).
UK higher-education institutions reporting a breach or attack in the prior 12 months (2024): 91%; 71% of secondary schools; 52% of primary schools (UK DSIT Cyber Security Breaches Survey 2024 education annex).
Microsoft Digital Defense Report 2025: 39% of identity-based attacks Microsoft observed targeted research and academic institutions (Microsoft Digital Defense Report 2025).
Key takeaways
Records exposed has decoupled from incident count. Comparitech's 2025 roundup shows confirmed global education ransomware attacks barely moving (247 to 251) while breached records jumped 27% (3.11M to 3.96M). The mechanism is consolidation: a smaller number of third-party ed-tech vendors, each holding the records of millions of students across thousands of districts, mean a single compromise has a multiplicative blast radius. PowerSchool, holding the records of an estimated 75% of the K-12 market, is the canonical example. The defensive math has shifted from "how do I keep my own perimeter intact" to "how do I bound my exposure to the supply chain my district has already procured."
Defender resilience is real, particularly in lower education. Sophos found lower-education attacks blocked before encryption climbing from 14% to 67% in a single year, the largest defender-side improvement Sophos has measured in any industry vertical. The ratio of lower-ed median ransom paid fell from US$6.6M to US$800K (an 88% decline). Some of this is composition: smaller districts that historically paid catastrophic ransoms have invested in CISA-recommended controls (offline backups, MFA, tabletop exercises). Some is negotiation: 41% of lower-education victims who paid in 2025 paid less than the initial demand, an indication that schools are no longer the panicking buyers they were in 2022 and 2023.
Higher education's threat profile is structurally different from K-12 and warrants a different defense. Sophos 2024 and 2025 data shows higher education's encryption rate (58%) sits roughly twice that of lower education (29%), the higher-ed top technical root cause is exploited vulnerabilities (35% in 2024) rather than phishing, and 49% of higher-education providers identified unknown security gaps as a top root cause. Universities are larger, more open, and less centrally administered; they look like federations of mid-sized businesses rather than single enterprises. The defense pattern that works for a K-12 district (perimeter MFA, EDR, central identity) does not necessarily transfer to a university with 50 autonomous research labs each running its own infrastructure.
Third-party ed-tech is the dominant 2024-2025 incident pattern. PowerSchool (~62 million students), LAUSD's Snowflake-third-party exposure (26 million+ student records advertised on dark-web markets in June 2024), and downstream PowerSchool incidents at districts like San Diego Unified all share a single template: the breach happens at a vendor the district trusted, not at the district. Verizon's 2025 DBIR measured third-party-involved breaches at 30% of all cases, double the prior year. Ed-tech procurement is now a security function, not a curriculum-and-pricing function.
Cost-of-breach is asymmetric across the education stack. IBM's 2025 Cost of a Data Breach Report puts the education industry bracket at US$3.82M-US$4.43M, below the global average US$4.44M and far below healthcare's US$7.42M, but Sophos's higher-education recovery cost dropped to US$0.90M while lower-education recovery cost stayed at US$2.20M. Average daily downtime cost remains at US$550,000 per US school district. The catastrophic-cost case for education is no longer the ransom; it is the operational disruption (school days lost, payroll delayed, state-aid penalties for missed instructional days) and the multi-year class-action exposure (PowerSchool consolidated MDL, Naviance US$17.25M settlement preliminary approval Feb 2026).
Phishing remains the dominant initial-access pattern in K-12, but identity attacks dominate in higher education and research. UK DSIT 2024 found 92% of primary schools and 89% of secondary schools experienced phishing in the prior 12 months. Microsoft Digital Defense Report 2025 found 39% of identity-based attacks targeting research and academic institutions, the highest sectoral concentration outside government. Defenders therefore need two parallel investments: high-volume security awareness and inbox-protection at the K-12 layer, and identity-defense plus privileged-access management at the higher-education and research layer.
Methodology
Sources used: K12 Security Information eXchange (K12 SIX) State of K-12 Cybersecurity: Year in Review series and rolling K-12 Cyber Incident Map, the GAO-recognized canonical tracker of US K-12 disclosed incidents since 2016; the 2025 Center for Internet Security MS-ISAC K-12 Cybersecurity Report (analysis of 5,000+ K-12 organizations between July 2023 and December 2024, published March 2025); Comparitech Education Ransomware Roundup 2025 plus the long-running US schools and colleges ransomware database (updated daily, lead figures captured April 25, 2026); Sophos State of Ransomware in Education 2024 (n=694 IT and cybersecurity decision-makers from 14 countries, fieldwork January-February 2024) and 2025 (n=441; 243 lower-education and 198 higher-education organizations hit by ransomware, vendor-agnostic survey by Vanson Bourne, fieldwork January-March 2025, published August-September 2025); IBM Security Cost of a Data Breach Report 2025 (Ponemon-administered, n=600 organizations, data window March 2024 to February 2025); Verizon Data Breach Investigations Report 2024 (Educational Services chapter, NAICS 61) and 2025 (data window November 1, 2023 to October 31, 2024; 22,052 incidents and 12,195 confirmed breaches across 139 countries); Identity Theft Resource Center 2024 Annual Data Breach Report (US disclosed compromises, published January 2025); Federal Bureau of Investigation Internet Crime Complaint Center 2024 Annual Report (US, published March 2025); Microsoft Digital Defense Report 2025 (data window approximately July 2024-June 2025); ENISA Threat Landscape 2025 (data window July 2024-June 2025); UK Department for Science, Innovation and Technology Cyber Security Breaches Survey 2024 (education annex), conducted by Ipsos (185 primary schools, 171 secondary schools, 43 further-education colleges, 31 higher-education institutions; fieldwork September 2023-January 2024); Jisc cyber threat intelligence reporting on UK higher and further education; EDUCAUSE 2025 Top 10 IT Issues; and Emsisoft State of Ransomware in the U.S. annual reports.
Date cutoff: April 25, 2026. Statistics are reported with their primary publisher's data window, and we lead with the most recent full-year figures wherever a primary source has released them. Statistics that could not be reached on at least one verification pass against a named primary source were dropped rather than estimated. Vendor blogs and aggregator sites that restate other publishers' numbers without adding methodology were not used as primary sources. Where a stat could only be reached via a secondary publisher (for example, a K-12 Dive write-up of a Comparitech report), both publishers are named so the reader can pursue the underlying primary source.
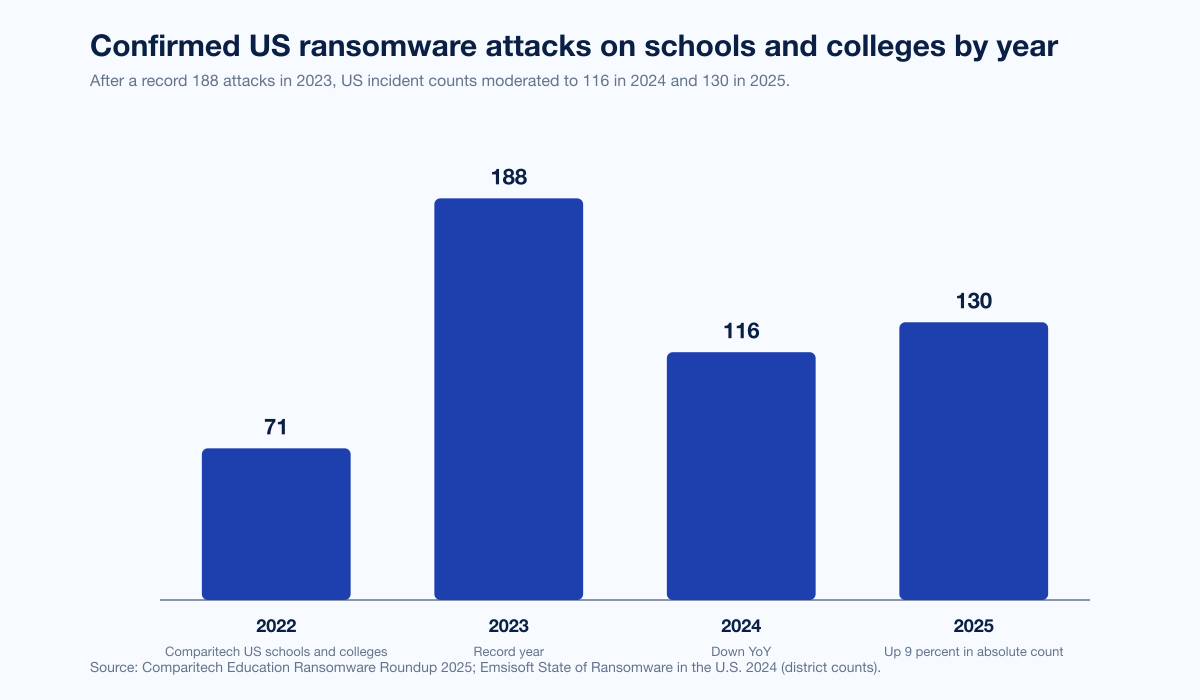
Figure 1: Confirmed US ransomware attacks on schools and colleges climbed from 71 (2022) to a record 188 (2023) before stabilizing at 116 (2024) and 130 (2025). Source: Comparitech Education Ransomware Roundup 2025 and Emsisoft The State of Ransomware in the U.S. 2024.
How big is education's data-breach problem in 2026?
Three datasets anchor the answer: Comparitech's confirmed-ransomware count, the CIS MS-ISAC K-12 telemetry, and PowerSchool's single-incident blast radius.
Confirmed ransomware on global education
Comparitech's 2025 Education Ransomware Roundup tracks publicly claimed ransomware attacks on schools, colleges, and universities worldwide using leak-site disclosures, district notifications, regulator filings, and news reporting. The headline figures for the most recent four years:
Metric | 2022 | 2023 | 2024 | 2025 | Source |
|---|---|---|---|---|---|
Confirmed US K-12 districts hit | 45 | 108 | 116 | n/a | Emsisoft |
Schools impacted across those US districts | n/a | n/a | ~2,275 | n/a | Emsisoft |
Confirmed US schools/colleges total | 71 | 188 | 116 | 130 | Comparitech |
Confirmed global education ransomware attacks | n/a | n/a | 247 | 251 | Comparitech |
Records breached, global education ransomware | n/a | n/a | 3.11M | 3.96M | Comparitech |
Average ransom demand (global education) | n/a | n/a | US$694K-US$847K | US$464K | Comparitech |
US K-12 records breached | n/a | n/a | n/a | 175,000 | Comparitech |
US higher-ed records breached | n/a | n/a | n/a | 3.7M | Comparitech |
The 2025 incident-count number (251) is barely above 2024 (247), but breached records jumped 27% to 3.96 million, indicating that compromised vendors are taking larger and larger blast radii with them. The US share of the global attack count rose 9% YoY in absolute terms (Comparitech notes the US itself saw a 9% decline 2024 to 2025 inside its own count of 130 attacks, against a still-rising global total).
The top ransomware strains claiming education attacks in 2025 were Qilin (37 attacks), SafePay (23), Fog (18), Interlock (18), and INC (17). Strain dominance in education tracks the broader strain dominance in 2025 leak-site activity, suggesting education is rarely a strain-specific target; it is a target of opportunity for whichever strain is most operationally productive that quarter.
CIS MS-ISAC K-12 telemetry
The 2025 CIS MS-ISAC K-12 Cybersecurity Report: Where Education Meets Community Resilience, released at SXSW EDU on March 6, 2025, drew on more than 5,000 K-12 organizations between July 2023 and December 2024. The report's headline metrics:
82% of reporting K-12 schools experienced cyber threat impacts during the 18-month window.
14,000 security events recorded.
9,300 confirmed cybersecurity incidents.
MS-ISAC services blocked more than 1 billion attempts to connect to malware domains and over 320 million attempts to connect to phishing domains on behalf of subscribing K-12 organizations.
Cybercriminals targeted human behavior at least 45% more than technical vulnerabilities in observed K-12 incidents, an inversion of the priority ratio in most other sectors.
The 1-billion-malware-connection-attempts figure is a measure of ambient malicious traffic, not successful intrusion, but it indicates the floor of attempted contact. K-12 networks are absorbing roughly 2.7 million malware-domain connection attempts per day from MS-ISAC's vantage point alone, before counting attempts that bypass MS-ISAC's filters or hit non-subscribing districts.
K-12 SIX rolling incident map
K12 Security Information eXchange (K12 SIX), the GAO-recognized authoritative tracker of US K-12 cyber incidents since 2016, has cataloged more than 1,300 publicly disclosed K-12 cyber incidents through early 2023, with 2022's edition reporting 1,619 cumulative incidents through 2022. K12 SIX explicitly notes that this understates the true magnitude because federal and state public-disclosure requirements remain inconsistent and many districts disclose only when forced to by AG breach-notification statutes.
Between January 2023 and June 2024, K12 SIX disclosed at least 83 potential ransomware attacks on US K-12 public school districts. Between November 2022 and October 2024, K12 SIX disclosed 85 ransomware attacks on US K-12 public schools. CISA, drawing on K12 SIX, MS-ISAC, and other sources, has characterized US school districts as experiencing an average of five cyber incidents per week, or roughly 260 per year, against a US public-school-district base of approximately 13,000.
PowerSchool: a single incident, sector-wide consequences
PowerSchool's SIS incident, disclosed January 7, 2025, is the largest disclosed exposure in the history of student data. The headline blast radius:
Metric | Value | Source |
|---|---|---|
Students affected | ~62 million | PowerSchool, Texas AG, multiple court filings |
Educators affected | ~9.5 million | PowerSchool |
Schools/districts affected | 18,000+ schools, 6,500 districts | PowerSchool, Keller Rohrback |
Countries operating PowerSchool SIS | 90+ | PowerSchool |
K-12 market share | ~75% | PowerSchool press materials |
Intrusion duration before detection | 9 days (Dec 19 to Dec 28, 2024) | PowerSchool |
Initial-access vector | Compromised credential at PowerSource customer-support portal, no MFA | PowerSchool |
Ransom demanded | US$2.85M | DOJ filings |
Attacker | Matthew D. Lane, age 19 | DOJ |
Sentencing | 4 years federal prison + US$14M restitution | October 2025; DOJ |
Class-action lawsuits filed | 50+ | Schubert Jonckheer & Kolbe |
Naviance class-action settlement (separate matter) | US$17.25M (preliminary approval Feb 27, 2026) | Class Action Lawsuits |
Inside the PowerSchool exposure, the data classes were heterogeneous and varied by district, but included names, contact info, dates of birth, limited medical-alert information, and Social Security Numbers. PowerSchool noted that fewer than 25% of registered students had Social Security numbers stored in the affected system, but for the 25% who did, the records are now in unauthorized hands and have been the subject of multi-jurisdictional class-action consolidation under the PowerSchool Holdings MDL since January 2025. The case is the canonical 2024-2025 precedent for what happens when a centralized ed-tech vendor without MFA on its support portal is breached at the supply-chain layer.
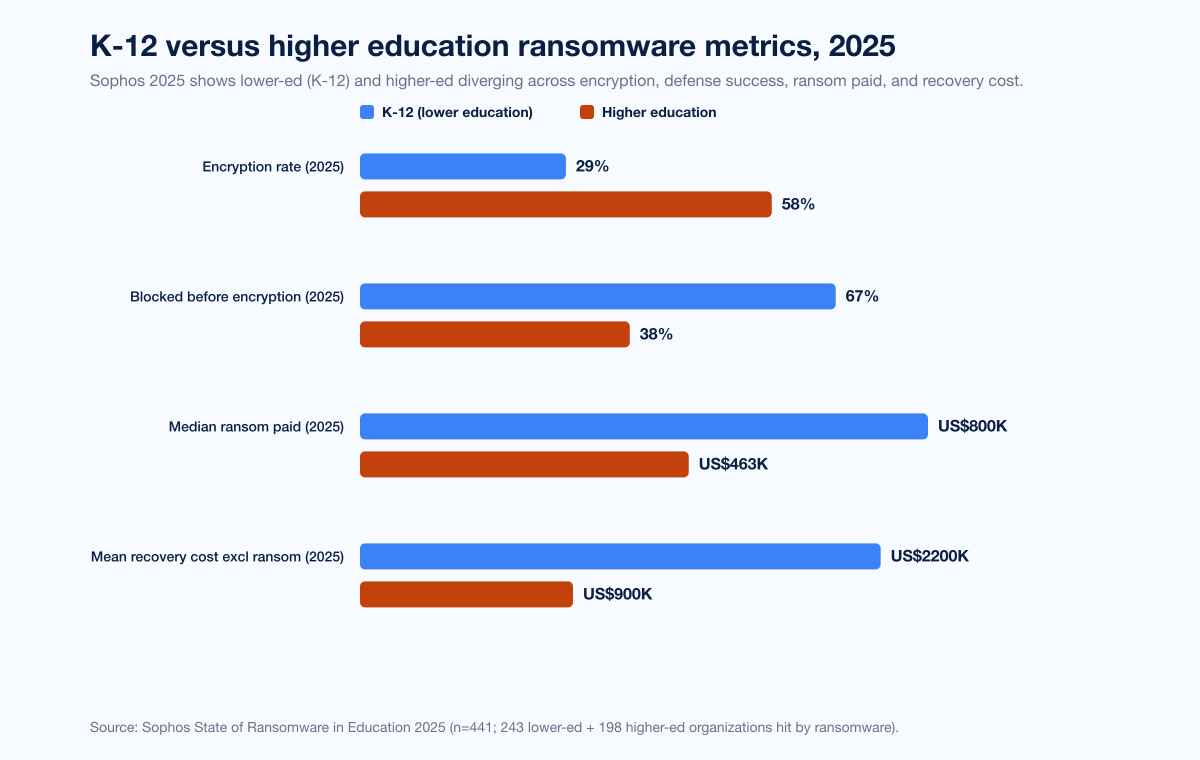
Figure 2: K-12 (lower education) and higher education diverge sharply across encryption rate, defense success, ransom paid, and recovery cost. Sophos State of Ransomware in Education 2025; n=441 (243 lower education + 198 higher education hit by ransomware). Source: Sophos State of Ransomware in Education 2025.
K-12 vs higher education: a structural split, not a continuum
Sophos's 2025 State of Ransomware in Education is the cleanest dataset for comparing K-12 (lower education) against higher education on like-for-like ransomware metrics. The two sectors look like different industries.
Encryption and defense success
Metric | Lower education | Higher education | Source |
|---|---|---|---|
Attacks blocked before encryption (2024) | 14% | 21% | Sophos 2024 |
Attacks blocked before encryption (2025) | 67% | 38% | Sophos 2025 |
Encryption rate (2025) | 29% (4-year low) | 58% | Sophos 2025 |
Hit by ransomware (2024) | 63% | 66% | Sophos 2024 |
Hit by ransomware (2023) | 80% | 79% | Sophos 2023 |
Lower education's defender resilience improved more in a single year than any other vertical Sophos has measured. The blocked-before-encryption rate climbed from 14% to 67%, a 53-point improvement. Higher education improved too (21% to 38%), but at half the rate. The likely driver in K-12 is the cumulative effect of CISA K-12 cybersecurity guidance, state-level requirements, MS-ISAC subscription growth, and grant funding from the FCC's Schools and Libraries Cybersecurity Pilot Program, all of which pushed identity-perimeter controls (MFA, EDR) into smaller districts during 2023-2024.
Ransom paid and recovery cost
Metric | Lower education | Higher education | Source |
|---|---|---|---|
Median ransom paid (2024) | US$6.6M | US$4.41M | Sophos 2024 |
Median ransom paid (2025) | US$800,000 | US$463,000 | Sophos 2025 |
Mean recovery cost excl ransom (2024) | US$3.76M | US$4.02M | Sophos 2024 |
Mean recovery cost excl ransom (2025) | US$2.20M | US$0.90M | Sophos 2025 |
Paid less than initial demand (2025) | 41% | n/a | Sophos 2025 |
Median ransom paid in lower education fell 88% in a single year (US$6.6M to US$800,000). Higher-ed dropped 90% (US$4.41M to US$463,000). The lower-education number is still meaningful (US$800K is most district CIO budgets for an entire fiscal year), but the directional story is unambiguous: education has moved from being the highest-paying ransomware victim category in 2024 to one of the lowest in 2025. Higher education's mean recovery cost (US$0.90M) is now the joint-lowest across all 17 industries Sophos surveyed in 2025.
Root cause divergence
Metric | Lower education | Higher education | Source |
|---|---|---|---|
Top technical root cause (2024) | Phishing (22%) | Exploited vulnerabilities (35%) | Sophos 2024 |
Top operational cause | Distributed alongside malicious emails, exploited vulnerabilities, compromised credentials | Unknown security gaps (49%) | Sophos 2024 |
Top initial-access vectors observed | Phishing email, malicious mail attachment, compromised credentials | Vulnerability exploitation, identity attacks | Sophos 2024 + Microsoft MDDR 2025 |
Lower-education attacks come through inbox; higher-education attacks come through unpatched, unauthenticated, or unmonitored exposed services. The defense pattern divides accordingly. Lower-education buyers should prioritize email security (DMARC enforcement, AI-aware phishing detection, link rewriting), security-awareness training, and MFA on staff identities. Higher-education buyers should prioritize exposed-service inventory (external attack-surface management), patch tempo for internet-exposed CVEs, and identity-defense controls including PAM, conditional access, and ITDR for staff and student accounts that have privileged access to research workloads.
Disclosure asymmetry
Higher-education breaches are reported more frequently than K-12 breaches because universities have communications offices, alumni populations, and federal-research compliance obligations (NIST SP 800-171, CMMC) that force disclosure. K-12 districts often disclose only after state AG breach-notification statutes are triggered. K-12 SIX has documented this disclosure asymmetry across multiple Year in Review reports, and the 2025 CIS MS-ISAC K-12 report noted that even at 9,300 confirmed cybersecurity incidents over 18 months, the report likely understates the true volume. Treat any single year's K-12 disclosed-incident count as a floor, not a ceiling.
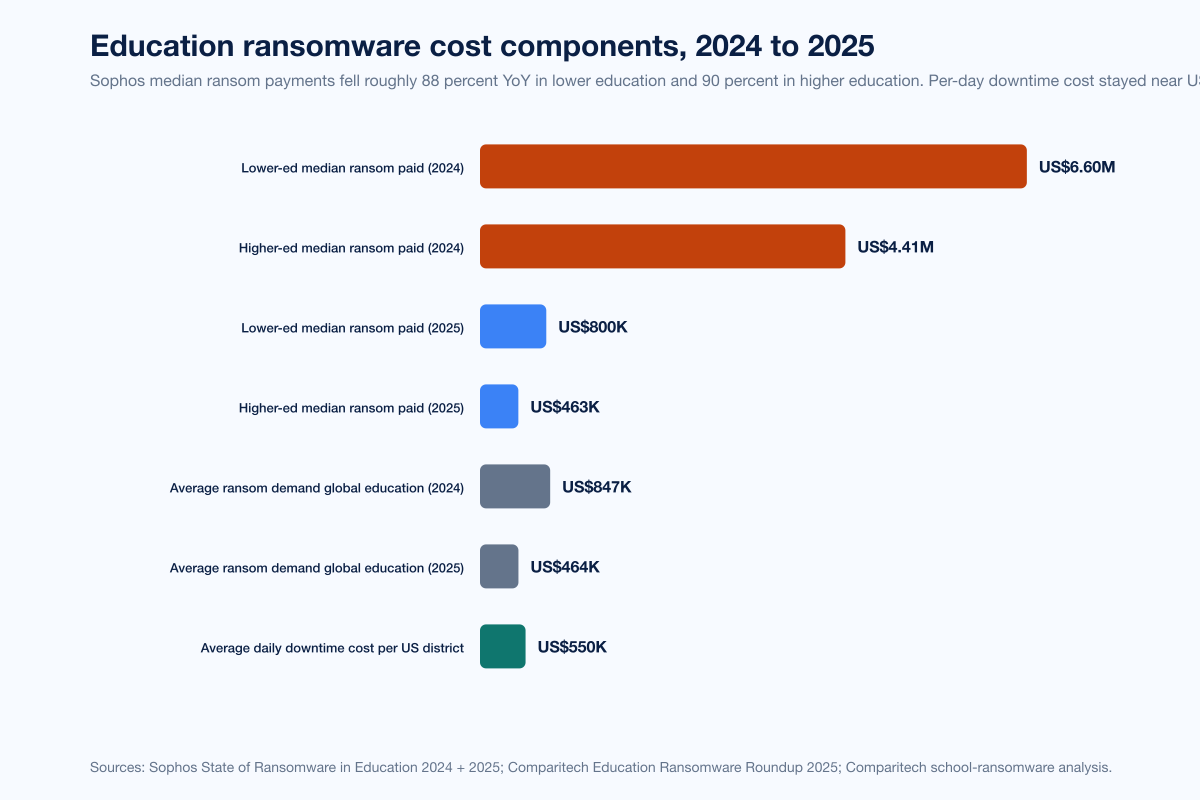
Figure 3: Average ransom demand fell from US$847K (Comparitech 2024) to US$464K (2025), with Sophos median ransom paid collapsing from US$6.6M to US$800K in lower education and US$4.41M to US$463K in higher education. Average daily downtime cost remained at US$550K per US school district. Sources: Comparitech, Sophos, Campus Technology citing Comparitech.
Cost of an education breach in 2026
Education breaches have three cost layers: the ransom (where one is paid), the recovery operations (downtime, IR retainers, hardware replacement, identity-rotation projects), and the multi-year liability tail (class-action settlements, AG enforcement, FERPA/COPPA exposure, cyber-insurance premium increases).
Direct breach cost (IBM 2025)
IBM's 2025 Cost of a Data Breach Report, the canonical industry benchmark for direct breach economics, puts the global average breach cost at US$4.44M (-9% YoY) and the US average at an all-time-high US$10.22M (+9% YoY). Healthcare retained the highest sectoral cost at US$7.42M for the 14th consecutive year. Education sat in the lower-cost bracket of US$3.82M-US$4.43M, alongside transportation, communications, entertainment, consumer services, research, and retail. IBM does not publish a sector-specific number for education in 2025, only a band, so the precise per-breach number for an individual district or institution will sit somewhere in that range and depends heavily on attack type, data classes exposed, and detection lag.
The 2025 IBM report flagged a new cost driver, shadow AI, adding an average US$670,000 per breach when unsanctioned AI tooling was involved. Education is a heavy consumer of student-facing AI (writing assistants, research-summarization tools, LLM-tutoring platforms) and has a structural exposure to this pattern: unmonitored AI tools handling student work that includes PII, FERPA-protected academic records, and increasingly health information for accommodations.
Recovery cost (Sophos)
The Sophos State of Ransomware in Education 2025 mean recovery cost (excluding ransom) for higher education fell to US$0.90M, down from US$4.02M in 2024. The lower-education mean recovery cost fell to US$2.20M, down from US$3.76M. Both numbers are conservative because they exclude the ransom payment itself and the multi-year settlement tail. They also exclude the cost of the disruption to students, which IBM has historically captured in the "loss of business" line.
Daily downtime (Comparitech)
Comparitech's school-ransomware analysis estimates a US school district loses approximately US$550,000 per day of downtime when fully encrypted. Average downtime in 2023 was 12.6 days per attack; preliminary 2024 data suggested approximately 7 days, though Comparitech notes the figure typically rises as later disclosures land. Cumulative US K-12 ransomware cost since 2018, on Comparitech's running tally, has reached approximately US$9.45 billion.
Liability tail
The PowerSchool case has now generated:
US$17.25M Naviance class-action preliminary approval in February 2026 (a separate-but-related interception class action covering 2021-2026 logins).
A consolidated multidistrict litigation with 50+ filed lawsuits.
Texas AG civil action seeking damages on behalf of 880,000 affected Texans.
US$14M criminal restitution order plus 4-year federal prison sentence for the 19-year-old attacker.
FERPA enforcement is also tightening: cases involving third-party data sharing rose 34% in 2024, with the US Department of Education's Student Privacy Policy Office signaling a more aggressive posture. COPPA enforcement, while primarily targeted at consumer ed-tech, has produced material settlements such as the FTC's US$20M Cognosphere (Genshin Impact) settlement in 2025.
Cyber insurance
CoSN's 2024 EdTech Leadership Survey found:
59% of US K-12 districts paid higher cyber-insurance premiums in 2024.
24% of districts saw higher deductibles.
Districts without "best in class" security controls risk a 100-300% premium increase at renewal.
Common reasons for denied claims include inadequate documentation of cybersecurity controls, missing MFA on privileged accounts, delayed incident reporting, and exclusions for known-vulnerability exploitation. K-12 cyber-insurance is now a procurement-and-controls dependency, not a financial line item.
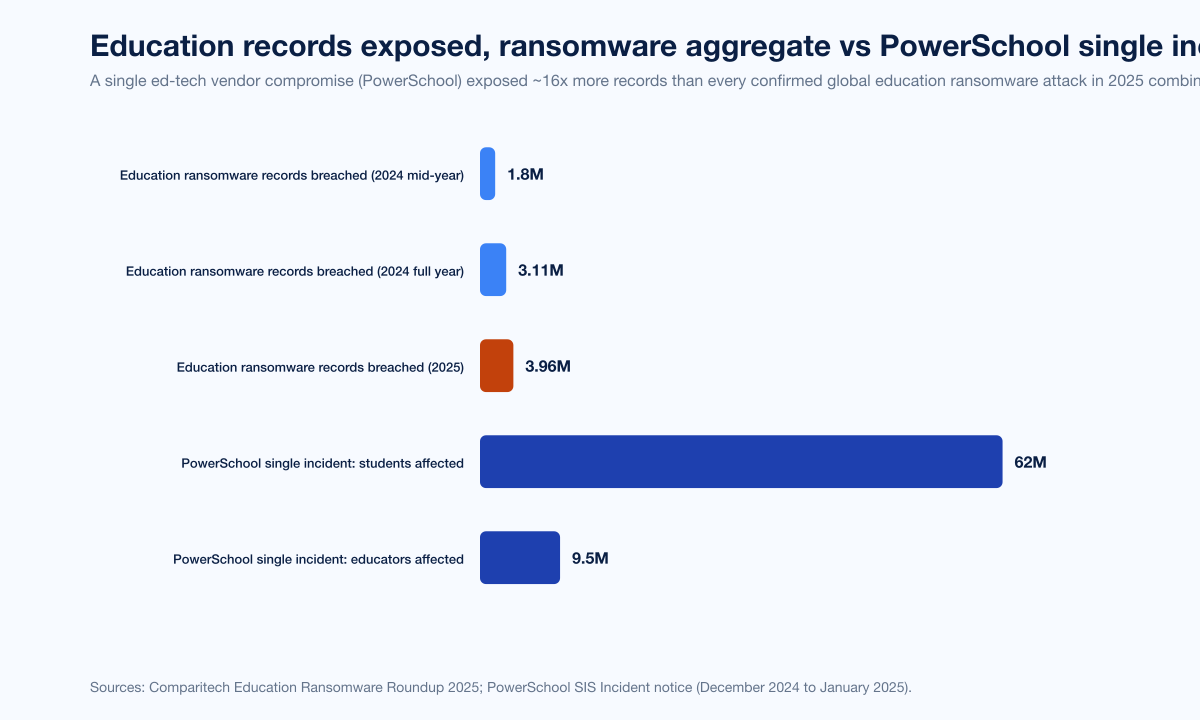
Figure 4: Education ransomware records breached climbed from 1.8 million (2024 mid-year estimate) to 3.11 million (2024 year-end Comparitech) to 3.96 million (2025), all dwarfed by the single PowerSchool incident's 62 million students. Source: Comparitech Education Ransomware Roundup 2025 and PowerSchool SIS Incident notice.
Top attack vectors against education
Education breach vectors split between K-12 (phishing-led, identity-led, and increasingly third-party ed-tech-led) and higher education (vulnerability-exploitation-led, identity-attack-led, and supply-chain-led).
Verizon DBIR 2024 Educational Services patterns
Verizon's 2024 DBIR Educational Services chapter ranked the top breach patterns in NAICS 61 as:
Pattern | Share | Notes |
|---|---|---|
Social engineering | 42% | Top pattern; phishing dominant |
System intrusion | 35% | Includes ransomware |
Miscellaneous errors | Trending up over 2 years | Misdelivery 56%, Loss 19%, Classification error 10% |
The Miscellaneous Errors pattern in education is the diagnostic of the sector's structural weakness: too many systems, too many staff with unrestricted permissions, too few controls on bulk data exports. A misdirected gradebook export to the wrong parent distribution list is now a routinely reported FERPA breach.
Verizon DBIR 2025 overall (with education sector context)
Verizon's 2025 DBIR covered 22,052 incidents and 12,195 confirmed breaches across 139 countries during the November 2023 to October 2024 data window. Top initial-access patterns relevant to education:
Initial-access vector | Share | Notes |
|---|---|---|
Credential abuse | 22% | Top vector overall |
Vulnerability exploitation | 20% | Up sharply YoY |
Phishing | 16% | Stable |
Ransomware presence in breaches | 44% | +37% YoY |
Ransomware in system-intrusion breaches | 75% | |
Third-party-involvement in breaches | 30% | Doubled YoY |
Verizon's executive summary noted the educational services sector saw a year-over-year decrease in incidents and breaches, but the third-party-involvement pattern, combined with the PowerSchool case, suggests the count understates the per-incident impact for education specifically.
Sophos technical root causes (education)
Sophos's State of Ransomware in Education 2024 root-cause data:
Cause | Lower education | Higher education |
|---|---|---|
Phishing | 22% (top) | n/a (subordinate to vulnerability exploitation) |
Exploited vulnerabilities | reported but not top | 35% (top) |
Compromised credentials | reported alongside | reported alongside |
Malicious email | reported alongside | reported alongside |
Unknown security gaps | n/a | 49% (top operational cause) |
Microsoft Digital Defense Report 2025
Microsoft's 2025 MDDR reported:
39% of identity-based attacks targeted research and academic institutions, the highest sectoral concentration outside government.
52% of cyberattacks involved extortion or ransomware (overall, not education-specific).
80% of incidents Microsoft investigated involved data theft or leakage.
The 39% identity-attacks-against-research figure is consistent with the long-running threat-actor pattern of using academic networks as low-friction proving grounds before targeting harder commercial environments.
UK DSIT (UK schools)
UK DSIT 2024, surveying 185 primary schools, 171 secondary schools, 43 further-education colleges, and 31 higher-education institutions:
Metric | Primary | Secondary | Further-ed | Higher-ed | Source |
|---|---|---|---|---|---|
Reported a breach or attack in last 12 months | 52% | 71% | n/a | 91% | UK DSIT 2024 |
Reported phishing attempts | 92% | 89% | n/a | n/a | UK DSIT 2024 |
Conducted risk assessments | 58% | 71% | 88% | n/a | UK DSIT 2024 |
Familiar with NCSC guidelines | 35% | 42% | n/a | n/a | UK DSIT 2024 |
UK higher education's 91% breach-rate sits more than twice the 43% all-businesses average, the largest sectoral premium DSIT measures.
Jisc 2025 (UK higher education)
Jisc's 2025 cyber threat intelligence reporting:
7 major incidents across UK HE/FE/research in 2025 (down from 17 in 2024).
16,000+ total incidents in 2025 (up from 11,000+ in 2024).
DDoS attacks: 418 in 2025 (down from 976 in 2024 but trending toward more sophisticated, higher-volume techniques).
91% of attacks that escalated to a major incident at a UK university used phishing as initial access.
Total incident volume rose, but major-incident impact fell, an indication that UK higher-ed defenses are catching more attacks at earlier stages. The DDoS-volume drop combined with rising sophistication is consistent with adversaries moving from volumetric noise to targeted application-layer attacks against student-portal infrastructure.
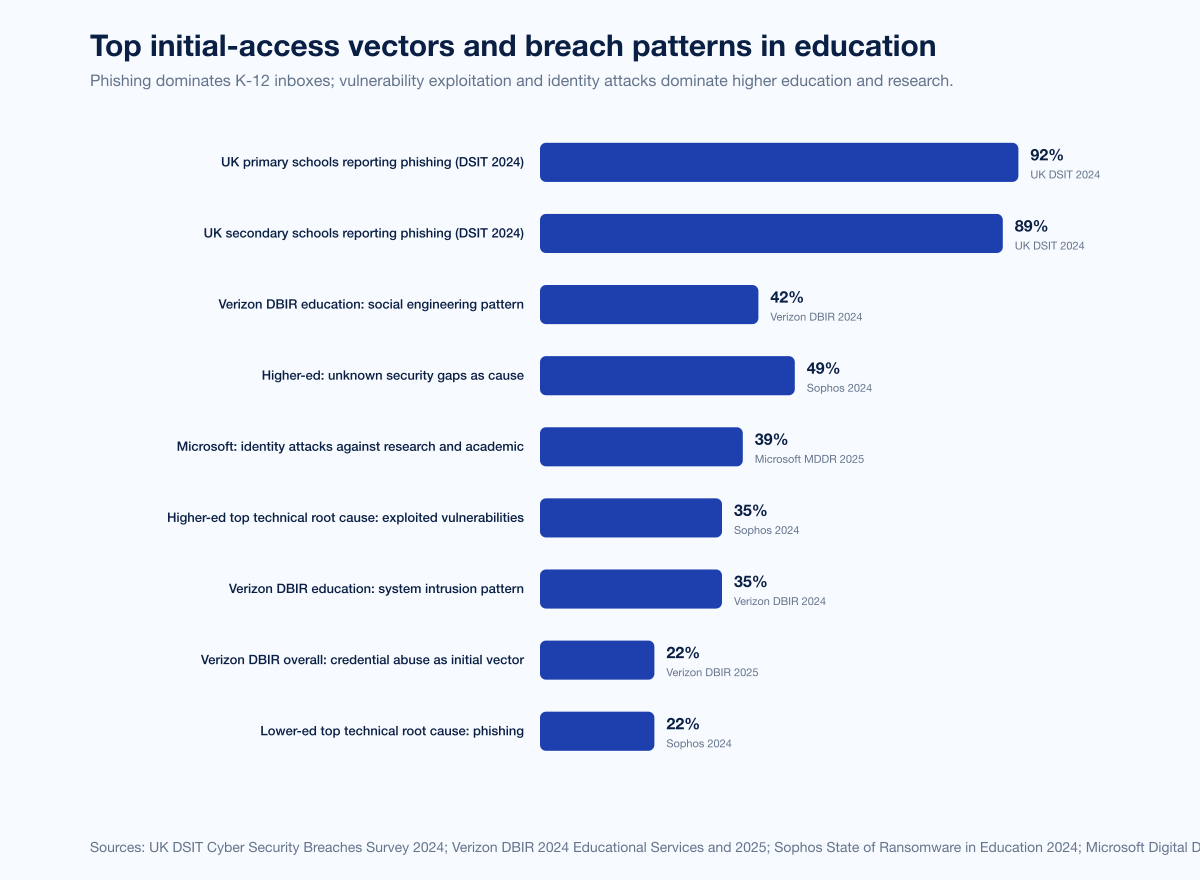
Figure 5: Education breach vectors split sharply between K-12 and higher education. Phishing dominates UK primary and secondary schools (92%/89%) and Sophos lower-education root cause (22%). Higher education's Sophos root cause is exploited vulnerabilities (35%), and 49% of higher-ed providers identified unknown security gaps as a contributing factor. Verizon DBIR 2024 Educational Services puts social engineering at 42% and system intrusion at 35% as top patterns. Sources: Sophos 2024, Verizon DBIR 2024, UK DSIT 2024.
Notable named incidents 2024-2025
The following incidents are listed because each is corroborated by primary disclosures (district statements, AG breach-notification filings, DOJ press releases, regulator notices) and each represents a distinct mechanism of education-sector compromise.
PowerSchool SIS (December 2024 to January 2025)
PowerSchool's customer-support portal, PowerSource, was accessed by an attacker using a single compromised credential between December 19 and December 28, 2024. The portal lacked multi-factor authentication and contained a maintenance tool that allowed PowerSchool engineers to access customer SIS instances for support and troubleshooting. The attacker exfiltrated student and educator data including names, contact information, dates of birth, limited medical-alert information, Social Security Numbers, and grade-related data. Approximately 62 million students and 9.5 million educators across more than 18,000 North American schools and 6,500 districts were affected. PowerSchool serves approximately 75% of the K-12 market across 90+ countries. The attacker, Massachusetts college student Matthew D. Lane, age 19 at the time of the attack, demanded a US$2.85 million ransom; the case proceeded through DOJ in 2025, with Lane pleading guilty in May 2025 to unauthorized computer access, cyber extortion, and aggravated identity theft, and being sentenced in October 2025 to four years in federal prison plus US$14 million restitution. Source: PowerSchool SIS Incident notice, DOJ filings via 10News, BleepingComputer Texas AG suit.
LAUSD-Snowflake third-party (June 2024)
Los Angeles Unified School District, the second-largest US public school district, suffered a third-party data exposure when records held by a Snowflake-hosted vendor were posted for sale on a dark-web market. The threat actor "Satanic Cloud" listed approximately 11 GB of stolen data including more than 26 million student-information records, 24,000 teacher records, and around 500 staff records, asking US$1,000. A second listing from "Sp1d3r" sought US$150,000 for related records. LAUSD has been a serial victim, with prior incidents in September 2022 (Vice Society ransomware) and a January 2022 incident at vendor Illuminate Education. Class-action lawsuits accuse the district of taking inadequate steps to protect children's data. Source: StateScoop on LAUSD-Snowflake, The 74 trio of LA cyberattacks.
Minneapolis Public Schools (February 2023, leaked into 2024)
Minneapolis Public Schools detected ransomware on February 17, 2023; the Medusa group claimed responsibility. The district refused to pay a US$1 million ransom (Medusa's leak-site demand; the district independently reported a US$4.5 million figure to the FBI). Medusa subsequently published 300,000 files online, including campus sexual misconduct cases, child abuse inquiries, mental-health crises, suspension reports, medical records, discrimination complaints, Social Security Numbers, and contact information. The district notified 105,617 individuals in September 2023, seven months after detection. The case is widely cited in 2024-2025 K-12 cybersecurity briefings as the canonical "what happens when you don't pay and the data is genuinely sensitive" outcome. Source: The 74 inside Minneapolis schools cyberattack, The Record Medusa story.
Naviance (PowerSchool subsidiary; class-action settlement Feb 2026)
A separate class action against PowerSchool concerning Naviance, the college and career-planning tool, alleged interception of confidential student communications. PowerSchool agreed to a US$17.25 million settlement that received preliminary court approval on February 27, 2026, covering individuals who logged into Naviance between August 18, 2021, and January 23, 2026. The Naviance case is distinct from the SIS class actions in the PowerSchool MDL but reinforces the magnitude of multi-year liability tail in education-sector incidents. Source: Class Action Lawsuits Naviance settlement, K-12 Dive on the Naviance settlement.
San Diego Unified PowerSchool downstream (January 2025)
San Diego Unified School District notified nearly 100,000 families that student data may have been downloaded in the PowerSchool incident. The district subsequently determined the warning was a false positive (its own PowerSchool data was not in the affected subset), but the public-notification process itself caused multi-week disruption to district communications and forced an unscheduled identity-protection deployment. The case illustrates the secondary cost of supply-chain incidents: even districts that ultimately are not breached carry the cost of evaluating whether they were. Source: Fox 5 San Diego on the SDUSD notification.
What this means for school-district CIOs and university CISOs
Six action items follow from the 2024-2025 data:
Treat ed-tech vendor procurement as a security control, not a curriculum decision. PowerSchool, LAUSD-Snowflake, Naviance, Illuminate Education, the K-12 SIX vendor-incident catalog all share a single pattern: the breach happens at a vendor whose customer the district trusted by default. Every contract should include third-party-risk attestations (SOC 2 Type II, ISO 27001, evidence of MFA on customer-support portals), a right to audit security-incident history, and a clear data-classification + retention table. The Verizon DBIR 2025 third-party-involvement-in-breaches figure (30%, double prior year) tells you this is a sector-wide structural shift, not a passing concern.
Get MFA everywhere a credential touches student or staff data. PowerSchool's PowerSource portal not having MFA is the single most cited control failure in education breaches in 2024-2025. The PowerSchool SIS incident, the LAUSD-Snowflake exposure, and most named K-12 ransomware events trace to a credential walking past a missing or under-provisioned MFA control. CISA's K-12 cybersecurity guidance and NIST 800-171 both require MFA on remote and privileged access. Insurers will now decline or premium-load policies without it.
Move on from "education has a low average breach cost" thinking. IBM's US$3.82M-US$4.43M industry bracket is conservative, captures only direct breach costs, and excludes the multi-year liability tail. PowerSchool's MDL, the Naviance US$17.25M settlement, and the FERPA-enforcement upswing collectively guarantee the true total cost of a 2024-2025 education breach is multiples of the direct-breach figure. Build cyber-incident financial models that include three years of post-incident liability, identity-protection services for affected populations, and IT-staff retention costs (Sophos's 2025 report flagged human-cost-of-vigilance metrics that dwarf the official downtime number).
Differentiate K-12 and higher-education defense strategies. The Sophos data is unambiguous: K-12 attacks come through inbox; higher-ed attacks come through unpatched, exposed services and identity systems. K-12 should prioritize phishing-resistant MFA, DMARC enforcement, AI-aware mail filtering, and security-awareness program funding. Higher-ed should prioritize external attack-surface management (EASM), patch tempo for internet-exposed CVEs, identity-defense (PAM, ITDR, conditional access), and segregation between research networks and administrative networks.
Stand up a third-party incident-response runbook now, not after disclosure. PowerSchool's customers had to figure out their own communications, identity-protection-vendor procurement, and parent-population notification processes inside the 30-60 day window AG breach-notification statutes allowed. A pre-built runbook (vendor inventory, blast-radius templates, identity-protection-vendor contracts, parent-communication templates, compliance-counsel retainer) compresses this timeline by weeks.
Test your defenses before adversaries do. Penetration testing against your active-directory environment, your student-information-system access paths, and your privileged-account inventory is the single highest-leverage spend a district CIO or university CISO can make against the 2024-2025 attack patterns. Stingrai supports K-12 districts and higher-education institutions with penetration testing (network, web app, social engineering) and PTaaS for organizations that want continuous testing rather than annual point-in-time engagements. We work with K-12 districts and universities of all sizes.
The regulatory and insurance landscape in 2026
Education-sector privacy regulation in the US splits across three federal regimes (FERPA, COPPA, HIPAA-for-school-medical-records) plus a fast-growing patchwork of state laws (California SOPIPA, Illinois SOPPA, New York Education Law 2-d, Connecticut state student-data protections, and others). Outside the US, GDPR and the UK Data Protection Act govern European institutions, and the EU's NIS2 directive includes some research-organization scope but explicitly excludes most education organizations.
FERPA enforcement is tightening
The US Department of Education has signaled a more aggressive enforcement posture. Cases involving third-party data sharing rose 34% in 2024, driven primarily by ed-tech procurement issues. Schools with proactive compliance programs see average penalty reductions of approximately 25%. FERPA does not impose direct monetary penalties on schools (the structural penalty is loss of federal education funding), but the threat is sufficient to drive board-level attention.
COPPA and the FTC
Loeb & Loeb's 2025 analysis of the amended COPPA rule notes the FTC declined to codify its long-standing guidance permitting schools to authorize the collection of personal information on behalf of parents, citing forthcoming FERPA changes. The FTC will continue to enforce existing COPPA guidance against ed-tech vendors. The 2025 Cognosphere (Genshin Impact) US$20M FTC settlement established a price for COPPA non-compliance even outside the strict school-procurement context.
State-level updates
State AG breach-notification statutes now apply consistently across all 50 US states. Districts and universities must therefore disclose any breach involving Social Security Numbers, financial information, or in some states health information, within statutory windows ranging from 30 to 90 days. Some states (Texas, California, New York) have signaled willingness to pursue civil enforcement against ed-tech vendors directly, with the Texas AG's PowerSchool civil action being the most prominent 2025 example.
Cyber insurance
CoSN's 2024 EdTech Leadership Survey reported 59% of US K-12 districts paying higher premiums and 24% seeing higher deductibles. The premium-increase risk for districts without "best in class" controls runs 100-300% per renewal. Standard underwriting requirements as of 2025-2026 now include MFA on privileged accounts, EDR coverage on all endpoints, offline backups with tested restore, documented incident-response plans, security-awareness training tracked by completion rate, and patch tempo SLAs. Districts without these in evidence may face decline-to-quote outcomes from primary cyber-insurance carriers.
Frequently Asked Questions
How many education data breaches happened in 2025?
Comparitech's Education Ransomware Roundup 2025 tracked 251 confirmed ransomware attacks on global education institutions in 2025, modestly up from 247 in 2024, with breached records jumping 27% to 3.96 million. The United States carried 130 of those attacks, the highest of any country. The 2025 CIS MS-ISAC K-12 Cybersecurity Report separately recorded 14,000 security events and 9,300 confirmed cybersecurity incidents across 5,000+ K-12 organizations between July 2023 and December 2024. Including the PowerSchool SIS incident's 62-million-student blast radius, 2025 was the highest-impact year on record for education-sector data exposure.
What was the largest education data breach in 2024 or 2025?
PowerSchool's SIS breach, disclosed January 7, 2025 after an attacker accessed PowerSource (PowerSchool's customer-support portal lacking MFA) between December 19 and December 28, 2024, exposed approximately 62 million students and 9.5 million educators across more than 18,000 North American schools and 6,500 districts in 90+ countries. It is the largest breach of children's data in US history. The 19-year-old attacker, Matthew D. Lane, was sentenced in October 2025 to four years in federal prison plus US$14 million in restitution.
Why are schools and universities such a frequent target for ransomware?
Schools and universities hold high-value data (student PII, Social Security Numbers, health and financial records, parent contact information, research IP for universities), often have lean cybersecurity staffing relative to enterprise peers, and operate on rigid academic calendars that create urgency to restore operations quickly. CISA describes the sector as "target rich, cyber poor" and reports US school districts experience an average of five cyber incidents per week. Higher education's open networks, federated administration, and large research footprints make exposed services and identity attacks the dominant entry vectors.
What is the average cost of an education data breach in 2026?
IBM's 2025 Cost of a Data Breach Report puts education in a lower-cost industry bracket of US$3.82M-US$4.43M, below the global average US$4.44M and far below healthcare's US$7.42M. Sophos's 2025 mean recovery cost (excluding ransom) for education was US$2.20M for lower education and US$0.90M for higher education, the joint lowest across all 17 industries Sophos surveyed. Comparitech estimates each day of US school-district downtime costs approximately US$550,000. The full cost picture also includes multi-year liability (PowerSchool's consolidated MDL, the Naviance US$17.25M settlement) and cyber-insurance premium impact (CoSN reported 59% of districts paying higher premiums in 2024).
How are K-12 and higher education breaches different?
Sophos's State of Ransomware in Education 2025 found K-12 (lower education) encryption rates fell to a four-year low of 29% while higher education stayed at 58%. K-12 attacks blocked before encryption climbed from 14% to 67% in a year, double higher education's improvement. K-12's top technical root cause is phishing (22%); higher education's is exploited vulnerabilities (35%). Lower-education median ransom paid in 2025 was US$800,000; higher-education median was US$463,000. The structural difference is that K-12 is centrally administered with phishing-led inbox attacks, while higher education is federated with vulnerability-led service-exposure attacks.
What is the PowerSchool breach and how was it possible?
In December 2024, an attacker used a compromised credential to log into PowerSchool's PowerSource customer-support portal, which lacked multi-factor authentication. The portal contained a maintenance tool that allowed PowerSchool engineers to access individual school-district SIS instances. The intrusion was undetected for nine days, during which the attacker exfiltrated names, contact information, dates of birth, limited medical-alert data, Social Security Numbers, and grade-related data for approximately 62 million students and 9.5 million educators across 18,000 North American schools. The 19-year-old attacker, Matthew D. Lane, demanded US$2.85 million in ransom, was charged in 2025, and was sentenced in October 2025 to four years in federal prison plus US$14 million restitution. Multiple class actions are consolidated under the PowerSchool Holdings MDL; the Texas AG has separately sued PowerSchool for damages on behalf of 880,000 affected Texans.
How many UK schools and universities were breached in 2024?
UK DSIT's Cyber Security Breaches Survey 2024 found 91% of higher-education institutions, 71% of secondary schools, and 52% of primary schools reporting a breach or attack in the prior 12 months, the highest sectoral concentration the UK government measures. Phishing was reported by 92% of primary schools and 89% of secondary schools. Jisc 2025 recorded 7 major incidents across UK higher and further education and research in 2025 (down from 17 in 2024) but 16,000+ total incidents (up from 11,000+ in 2024), an indication that defenses are catching attacks earlier.
What does FERPA say about data breaches?
FERPA (Family Educational Rights and Privacy Act, 20 U.S.C. § 1232g) governs the privacy of student education records. It does not require breach notification on its own (state breach-notification statutes do that work), but it does require schools to maintain "reasonable" data security and to control third-party access via written contracts. The structural penalty for non-compliance is loss of US Department of Education federal funding, which schools cannot afford to lose. Cases involving third-party data sharing rose 34% in 2024, driven by ed-tech procurement, and the Department's Student Privacy Policy Office has signaled more aggressive enforcement posture in 2024-2025. Schools with proactive compliance programs see average penalty reductions of approximately 25%.
What is the most common attack vector against schools?
Phishing. UK DSIT 2024 found 92% of primary schools and 89% of secondary schools reporting phishing attempts. Sophos 2024 found phishing as the top technical root cause in lower-education ransomware attacks at 22%, ahead of malicious email, exploited vulnerabilities, and compromised credentials. Verizon DBIR 2024 Educational Services ranked social engineering as the top breach pattern in NAICS 61 at 42%. In higher education, the dominant initial-access vector is exploited vulnerabilities (Sophos 35%) and identity attacks (Microsoft Digital Defense 39% of identity-based attacks targeted research and academic institutions).
How can a school district reduce its risk in 2026?
Five moves consistently appear in the highest-resilience districts in the 2024-2025 data: deploy MFA on every privileged account and every customer-facing identity that touches student or staff data; subscribe to MS-ISAC and implement CISA K-12 cybersecurity guidance; require third-party security attestations (SOC 2 Type II, MFA on vendor support portals, documented incident-response capabilities) in all ed-tech contracts; maintain offline-backup-with-tested-restore procedures; and run penetration tests at least annually against active-directory, the SIS access path, and email infrastructure. Stingrai supports K-12 districts and higher-education institutions with penetration testing and PTaaS tailored to the threat patterns the 2024-2025 data identifies as dominant.
Where can I find the latest education breach data?
The four annually-updated primary sources for education-sector breach data are: K12 SIX's State of K-12 Cybersecurity: Year in Review and rolling K-12 Cyber Incident Map (annual, with rolling map updates); the Center for Internet Security MS-ISAC K-12 Cybersecurity Report (released approximately annually at SXSW EDU); Comparitech's Education Ransomware Roundup (annual plus quarterly interim updates) and US schools and colleges ransomware tracker (updated daily); and Sophos's State of Ransomware in Education (annual). Verizon's DBIR Educational Services chapter (annual, NAICS 61) and IBM's Cost of a Data Breach Report (annual) provide the canonical industry benchmarks. For UK data, UK DSIT's Cyber Security Breaches Survey (annual) and Jisc's threat-intelligence reporting are the primary sources. Microsoft Digital Defense Report and ENISA Threat Landscape provide global telemetry context.
References
Comparitech. Education Ransomware Roundup: 2025 stats on attacks, ransoms, and data breaches. January 2026. https://www.comparitech.com/news/education-ransomware-roundup-2025-stats-on-attacks-ransoms-and-data-breaches/. Live ransomware database compiled from leak-site disclosures, district notifications, and news reporting; tracks confirmed attacks, records breached, ransom demanded, and ransomware-strain attribution by year.
Comparitech. Ransomware attacks on US schools and colleges cost US$9.45bn. Continuously updated. https://www.comparitech.com/blog/information-security/school-ransomware-attacks/. Cumulative US K-12 and higher-education ransomware impact analysis since 2018, including average daily downtime cost (US$550,000) and average annual downtime per incident.
Center for Internet Security. 2025 CIS MS-ISAC K-12 Cybersecurity Report: Where Education Meets Community Resilience. March 2025. https://www.cisecurity.org/insights/white-papers/2025-k12-cybersecurity-report. Analysis of 5,000+ K-12 organizations between July 2023 and December 2024 covering security events, confirmed incidents, attack-target methods, and DDoS, malware, and phishing connection-attempt blocking telemetry.
K12 Security Information eXchange (K12 SIX). State of K-12 Cybersecurity: Year in Review series and K-12 Cyber Incident Map. https://www.k12six.org/the-report. The GAO-recognized authoritative tracker of US K-12 publicly disclosed cyber incidents since 2016, including ransomware, data breaches, BEC, and DDoS.
Sophos. The State of Ransomware in Education 2025. September 2025. https://news.sophos.com/en-us/2025/09/10/the-state-of-ransomware-in-education-2025/. Vendor-agnostic survey by Vanson Bourne; n=441 (243 lower education, 198 higher education) IT and cybersecurity leaders at organizations hit by ransomware; covers attack rates, encryption rates, ransom paid, recovery cost, and root-cause data.
Sophos. The State of Ransomware in Education 2024. July 2024. https://www.sophos.com/en-us/blog/the-state-of-ransomware-in-education-2024. Prior-year edition; n=694 IT and cybersecurity decision-makers; covers attack rate, root cause, ransom payment behavior, and YoY comparison with 2023.
IBM Security. Cost of a Data Breach Report 2025. July 2025. https://www.ibm.com/reports/data-breach. Ponemon-administered annual breach-cost benchmark; n=600 organizations; data window March 2024 to February 2025; reports global average breach cost (US$4.44M), US average (US$10.22M), industry-bracket averages, and shadow AI cost premium (US$670K).
Verizon. 2024 Data Breach Investigations Report, Educational Services chapter. May 2024. https://www.verizon.com/business/en-au/resources/reports/dbir/2024/industries-intro/educational-data-breaches/. NAICS 61 sector chapter covering top breach patterns (social engineering 42%, system intrusion 35%) and miscellaneous-error analysis specific to education.
Verizon. 2025 Data Breach Investigations Report. April 2025. https://www.verizon.com/business/resources/reports/2025-dbir-executive-summary.pdf. 22,052 incidents and 12,195 confirmed breaches across 139 countries; data window November 2023 to October 2024; ransomware-presence and third-party-involvement YoY.
PowerSchool. SIS Incident notice and data-breach disclosures. January 2025 onward. https://www.powerschool.com/security/sis-incident/. Vendor's official disclosure of the December 2024 PowerSource customer-support portal compromise affecting approximately 62 million students and 9.5 million educators.
United States Department of Justice. Public filings on United States v. Matthew D. Lane. May 2025 plea, October 2025 sentencing. https://www.10news.com/news/team-10/i-was-addicted-to-hacking-cybercriminal-responsible-for-powerschool-breach-speaks-out. Federal criminal proceedings against the PowerSchool attacker; four years federal prison + US$14 million restitution.
Identity Theft Resource Center (ITRC). 2024 Annual Data Breach Report. January 2025. https://www.idtheftcenter.org/post/2024-annual-data-breach-report-near-record-compromises/. US disclosed-compromise tracker; total compromises (3,158) and victim notices (1.73 billion) for 2024.
Federal Bureau of Investigation Internet Crime Complaint Center. 2024 Annual Internet Crime Report. March 2025. https://www.ic3.gov/AnnualReport/Reports/2024_IC3Report.pdf. US Internet-crime telemetry; 859,532 complaints, US$16.6 billion losses, BEC complaints (21,442) and losses (US$2.8 billion).
Microsoft. Microsoft Digital Defense Report 2025. October 2025. https://www.microsoft.com/en-us/security/security-insider/threat-landscape/microsoft-digital-defense-report-2025. Global threat-landscape telemetry; identity-attack share against research and academic institutions (39%); ransomware share of cyberattacks (52%).
ENISA. Threat Landscape 2025. October 2025. https://www.enisa.europa.eu/publications/enisa-threat-landscape-2025. EU-focused threat-landscape report; sectoral breakdown including education (2.3% of recorded EU incidents); AI-augmented phishing share.
UK Department for Science, Innovation and Technology. Cyber Security Breaches Survey 2024, education institutions annex. April 2024. https://www.gov.uk/government/statistics/cyber-security-breaches-survey-2024/cyber-security-breaches-survey-2024-education-institutions-annex. Surveyed 185 primary schools, 171 secondary schools, 43 further-education colleges, and 31 higher-education institutions; covers breach prevalence, phishing rates, risk assessment, and NCSC-guidance familiarity.
Jisc. Cyber threat intelligence reporting on UK higher and further education. 2025. https://www.jisc.ac.uk/news/all/cyber-attacks-against-uk-education-and-research-are-growing-more-complex-and-sophisticated. Major and total incident counts, DDoS-attack volume, and phishing-share-of-initial-access for UK education and research.
EDUCAUSE. 2025 Top 10 IT Issues, Technologies, and Trends. October 2024. https://www.educause.edu/research-and-publications/research/top-10-it-issues-technologies-and-trends/2025. Higher-education CIO and CISO priorities including "A Matter of Trust" as the top cybersecurity issue.
Emsisoft. The State of Ransomware in the U.S.: Report and Statistics 2024. January 2025. https://www.emsisoft.com/en/blog/46288/the-state-of-ransomware-in-the-u-s-report-and-statistics-2024/. Annual US ransomware tracker; covers 116 K-12 districts impacted in 2024, ~2,275 schools affected, and YoY series back to 2022.
CISA. Protecting Our Future: Partnering to Safeguard K-12 Organizations from Cybersecurity Threats. Continuously maintained. https://www.cisa.gov/topics/cybersecurity-best-practices/K12cybersecurity/protecting-our-future-cybersecurity-k12. US federal cybersecurity guidance for K-12; cites the five-cyber-incidents-per-week US average and recommended controls.
Test your district or institution's defenses
Stingrai works with K-12 districts and higher-education institutions on the threat patterns this data identifies as dominant in 2026: phishing-led K-12 inbox attacks, vulnerability-led higher-education service exposure, third-party ed-tech compromise, and identity attacks against research and administrative networks. Our penetration testing services cover network, web application, social engineering, and Active Directory engagements; PTaaS provides continuous testing for districts and institutions that need year-round visibility rather than annual point-in-time assessments. The team has 18 published CVEs (Ivan Spiridonov 10, Moaaz Taha 5, Victor Villar 3), team certifications including OSCE3, OSCP, OSWE, OSED, OSEP, CREST CRT, CISSP, CRTO, GCPN, CRTE, eWPTX, and a 5.0/5.0 rating across 19 Clutch reviews. We're aligned with SOC 2, ISO 27001, HIPAA, PCI DSS 4.0, NIST SP 800-53 / 800-171, DORA, and NIS2 for institutions that need regulatory cover for their pentest engagements.