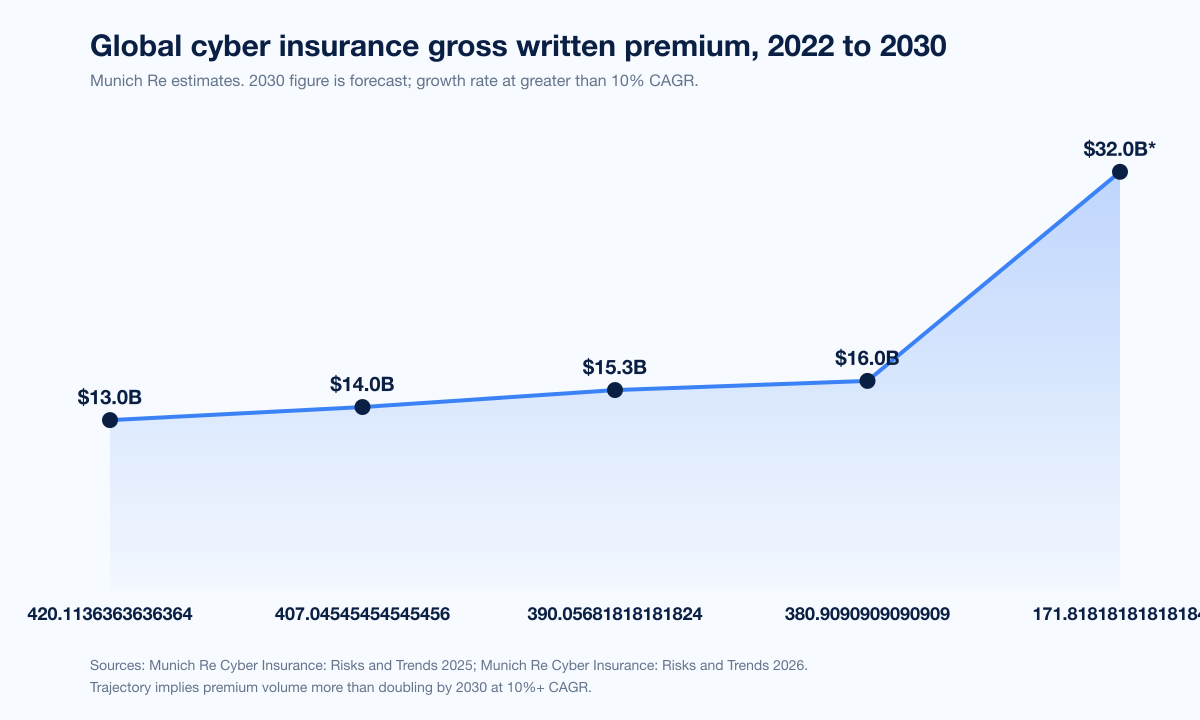
Munich Re's 2025 industry survey put global cyber insurance gross written premium at approximately US$15.3 billion in 2024, with North America carrying more than US$10 billion of that on its own and the trajectory pointing at a doubling of premium volume by 2030 at a 10%+ CAGR (Munich Re Cyber Insurance: Risks and Trends 2025). The US standalone cyber market, however, just turned a corner. AM Best's June 2025 segment report measured US$7.075 billion in 2024 US direct premium written, a 2.3% year-over-year drop and the first ever annual decline since AM Best began tracking the line in 2015 (AM Best, June 2025). Cyber is still on track to be one of the fastest-growing P&C lines through 2030, but 2024 was the year underwriters proved they could give back rate.
Three forces drive the 2026 numbers. Pricing softened on every continent in 2025. Marsh's Global Insurance Market Index recorded the cyber line down 7% globally in Q4 2025 and 5% in Q1 2026, marking eight consecutive quarterly cuts, with Howden's 2025 Rebooting Growth report placing cumulative cyber rate decline at roughly 27% from mid-2022 through mid-2025 (Marsh Q4 2025 GIMI; Marsh Q1 2026 GIMI; Howden 2025 Cyber Report). Underwriting still made money. Howden estimates cyber generated approximately US$9 billion in cumulative underwriting profit between 2022 and 2024 with combined ratios averaging 70%, although AM Best's US loss ratio jumped to 48.8% in 2024 from 41.6% in 2023 (+7.2 ppt) as softer pricing met rising claim frequency (AM Best, June 2025). And named catastrophic events tested capital. UnitedHealth Group disclosed approximately US$2.457 billion in Change Healthcare costs across full-year 2024 (Cybersecurity Dive, March 2025), while the July 19 2024 CrowdStrike Falcon update is estimated by reinsurance brokers to have triggered between US$300 million and US$1.5 billion of insured business-interruption losses against approximately US$5.4 billion in direct Fortune-500 financial impact (Parametrix via Fortune, August 2024; Cybersecurity Dive, August 2024).
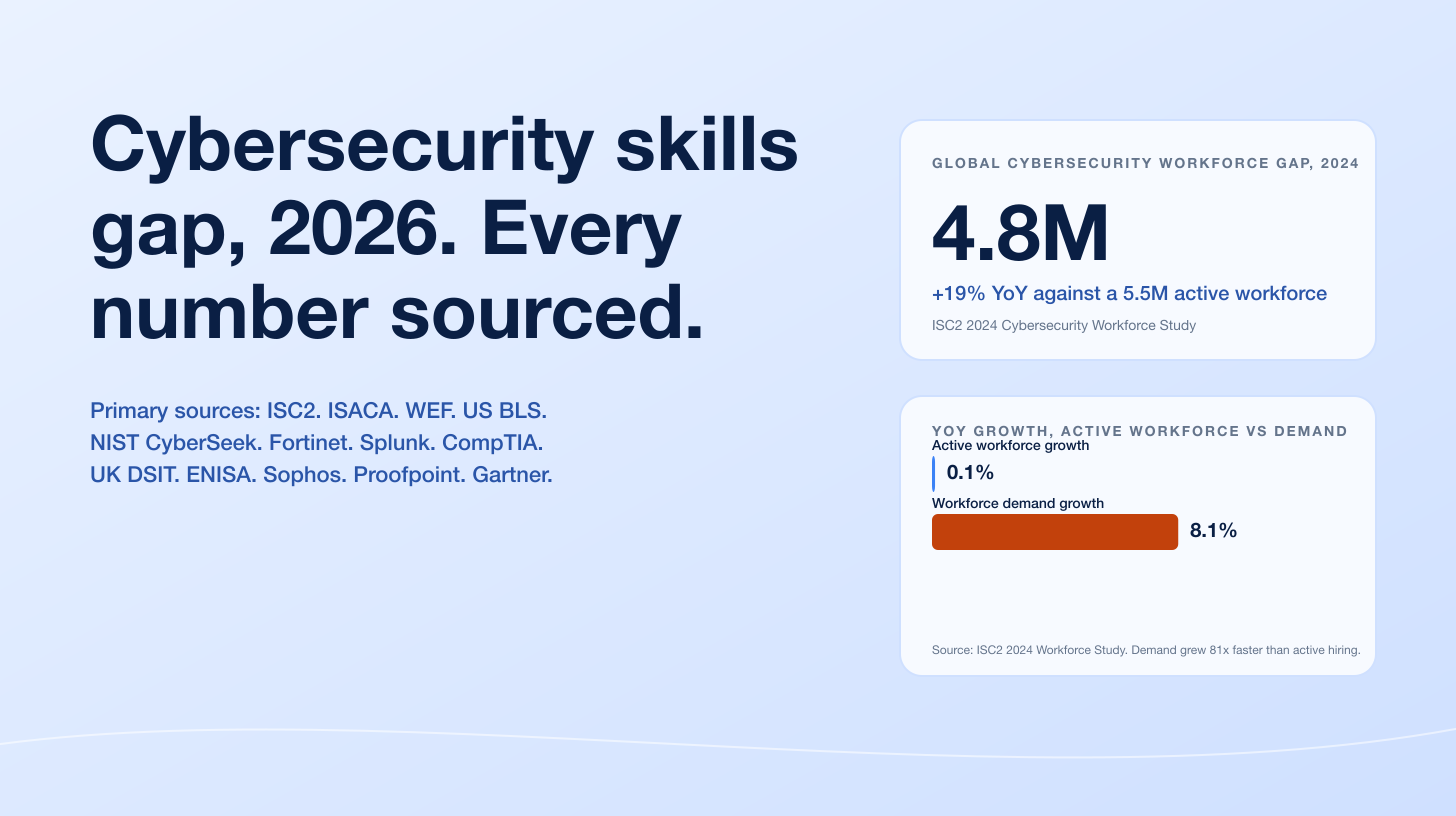
This post is the Stingrai research team's canonical 2026 reference for cyber insurance market and claims activity. It assembles 80 numeric claims from 22 named primary publishers including Munich Re, Marsh, Aon, Howden, Coalition, At-Bay, NetDiligence, AM Best, Lloyd's of London, the National Association of Insurance Commissioners (NAIC), Allianz Risk Barometer, Sophos, Guy Carpenter, CyberCube, Parametrix, Fitch Ratings, the European Insurance and Occupational Pensions Authority (EIOPA), Marsh McLennan, Microsoft, the European Union (DORA), and US-listed corporates whose SEC disclosures or court records produced incident-cost figures (UnitedHealth Group, MGM Resorts, Caesars, Mondelez, Zurich). Lead data is full-year 2025 telemetry from claims publishers (Coalition 2026 Cyber Claims Report and At-Bay 2026 InsurSec Report) and Q1 2026 broker data (Marsh GIMI Q1 2026, Aon Q2 2025 supplement). Where 2024 vendor reports are still the most recent, they are labeled. Every figure carries its source, year, and methodology window so any claim can be audited inline.
TL;DR: 12 labeled key stats
Global cyber insurance gross written premium, 2024: approximately US$15.3B; North America more than US$10B; 10%+ CAGR forecast through 2030 (Munich Re Cyber Insurance Risks and Trends 2025; Reinsurance News).
US standalone cyber direct premium written, 2024: US$7.075B, a 2.3% YoY decline, the first annual drop since AM Best began tracking in 2015 (AM Best, June 2025).
US standalone cyber loss ratio, 2024: 48.8%, up from 41.6% in 2023 (+7.2 ppt) (AM Best, June 2025).
Marsh Global Insurance Market Index cyber rate change, Q1 2026: -5% globally; -2% US, -11% LAC, -14% IMEA (Marsh Q1 2026 GIMI).
Howden 2025 Rebooting Growth: cumulative cyber rate decline mid-2022 to mid-2025: approximately -27% (Howden 2025 Cyber Report).
Coalition 2026 Cyber Claims Report: businesses that refused to pay ransom in 2025: 86% (record high) (Coalition 2026; The Actuary, April 2026).
Coalition 2026: average initial ransom demand, full-year 2025: more than US$1M, +47% YoY (Coalition 2026).
At-Bay 2026 InsurSec Report: dataset: more than 100,000 policy years; +7% YoY claim frequency; all-time-high average claim severity US$221K (Help Net Security, April 2026).
At-Bay 2026: ransomware severity, 2025: US$508K, +16% YoY; Akira 40%+ of ransomware claims; remote access entry for 87% of ransomware claims (Help Net Security, April 2026; Insurance Business, April 2026).
NetDiligence 2025 Cyber Claims Study (15th annual): 10,402 claims analyzed (2020 to 2024); SME 5-year average US$264K, large company 5-year average US$10.3M (NetDiligence 2025; Carrier Management, September 2025).
UnitedHealth Group Change Healthcare cyber attack, full-year 2024: US$2.457B in disclosed costs (Cybersecurity Dive, March 2025).
CrowdStrike Falcon update outage, July 19 2024: approximately 8.5M Windows devices crashed; insured losses estimated US$300M to US$1.5B (broker range) against approximately US$5.4B in Fortune-500 direct losses (Cybersecurity Dive; Fortune via Parametrix).
Key takeaways
The market is profitable but rate-soft. Cumulative cyber underwriting profit of approximately US$9B from 2022 to 2024 (Howden) and 70% combined ratios kept capital flowing in. That capital met flat-to-shrinking demand in 2024, and the result was a Marsh-tracked sequence of eight straight rate-down quarters and a US$0.16B nominal decline in US direct premium written. Underwriters did not pull back; price-takers did.
Claim frequency is rising while paid-ransom shares are falling. Coalition's 2026 dataset, drawn from more than 100,000 policyholders across the US, Canada, UK, Australia, and Germany, found 86% of insured businesses refused to pay ransoms in 2025, up from a 44% pay rate the prior year, even as initial ransom demands jumped 47% to more than US$1 million on average. The combination signals more incidents being reported and processed, but better incident response (negotiation, key recovery, decryption tooling) keeping policyholder loss flat.
Remote-access compromise is the dominant ransomware vector by a wide margin. At-Bay's 2026 InsurSec Report measured 87% of ransomware claims entering through remote-access services, with VPN compromise alone driving 73% of identified-vector intrusions (up from 38% in 2023 and 66% in 2024). The single ransomware family Akira accounted for more than 40% of ransomware claims, with average demand US$1.2M, roughly 50% higher than other groups.
Two named events define recent loss-ratio risk. UnitedHealth's Change Healthcare attack (February 2024) cost the parent US$2.457 billion for full-year 2024, with insurance recoveries disclosed in subsequent 10-Q filings. The CrowdStrike Falcon update of July 19 2024, although operational rather than malicious, took roughly 8.5 million Windows devices offline; broker estimates of insured business-interruption losses span US$300M to US$1.5B, against US$5.4B of Fortune-500 direct financial impact (Parametrix, Guy Carpenter, CyberCube, Fitch). The same line covers both kinds of accumulation.
MFA and EDR are now under-the-line underwriting. Marsh McLennan's 2024 cyber market data showed 41% of cyber applications denied on first submission, with missing MFA and inadequate endpoint protection the top two reasons. The 2025 carrier survey found 96% of cyber insurers mandate enforced MFA across email, VPN, RDP, cloud apps, and admin accounts; 88% require EDR or MDR deployed on every endpoint. Coalition reported that 94% of organizations hit by ransomware saw threat actors target backups, which has driven carrier insistence on immutable / offline backup copies.
Methodology
Sources used in this post: Munich Re Cyber Insurance: Risks and Trends 2025 (released March 2025); Marsh Global Insurance Market Index Q4 2025 release (February 2026) and Q1 2026 release (April 2026); Aon 2025 Cyber Risk Report and Q2 2025 cyber-and-tech-E&O market update; Howden 2025 Cyber Report ("Rebooting Growth", September 2025); Coalition 2025 Cyber Claims Report (March 2025) and 2026 Cyber Claims Report (April 2026, covering full-year 2025 data); At-Bay 2026 InsurSec Report (April 2026); NetDiligence 15th Annual Cyber Claims Study (September 2025); AM Best US Cyber Insurance Market Segment Report (June 2025); the National Association of Insurance Commissioners (NAIC) 2025 Cybersecurity Insurance Report; Lloyd's of London market bulletin LMA5564 (August 2022, mandate effective March 31, 2023); Allianz Risk Barometer 2025 (January 2025) and 2026 (January 2026); Sophos State of Ransomware 2025 (June 2025; survey of 3,400 IT and security leaders across 17 countries); Guy Carpenter, CyberCube, and Parametrix CrowdStrike outage assessments published July to September 2024; Fitch Ratings cyber insurance reports; the European Insurance and Occupational Pensions Authority (EIOPA) DORA application materials; UnitedHealth Group Form 10-Q filings for Q1 through Q4 2024; SEC Form 8-K filings from MGM Resorts International (October 5, 2023) and Caesars Entertainment Inc. (September 7, 2023); the public record of Mondelez International, Inc. v. Zurich American Insurance Company (settled November 2022); Marsh McLennan and Microsoft 2024 Cyber Risk Report; and primary CISO and broker advisories from CyberDuo and Prescient Solutions referencing 2024 to 2026 carrier requirements. Date cutoff: April 29, 2026. Statistics that could not be reached via a named primary source on at least one verification pass were dropped rather than estimated.
Market size: where the cyber line stands in 2026
Munich Re's longitudinal estimate is the most-cited single figure for global cyber gross written premium and remains the cleanest top-line for 2024 and 2025. The 2025 Cyber Insurance: Risks and Trends report puts global cyber GWP at approximately US$15.3 billion in 2024, of which more than US$10 billion was written in North America (Industrial Cyber summary of Munich Re). Munich Re's earlier-2025 forecast was that global cyber would reach approximately US$16.3 billion in 2025, with subsequent restatements pegging the number a little lower as US standalone cyber turned negative. The forward outlook is unchanged: Munich Re projects global cyber premium volume more than doubling by 2030 at an average annual rate of more than 10% (Reinsurance News, March 2025). North American GWP is projected to grow toward roughly US$20 billion by 2030.
Year | Global cyber GWP | Source |
|---|---|---|
2022 | ~US$13.0B | Munich Re composite |
2023 | ~US$14.0B | Munich Re composite |
2024 | ~US$15.3B | |
2025 (forecast) | ~US$16.0B | |
2030 (forecast) | ~US$32B | Munich Re trajectory at 10%+ CAGR |
Two contextual numbers matter. First, cyber represents less than 1% of total global P&C insurance premium volume in 2024 (Munich Re), so although headline growth is in double digits, the absolute scale remains small relative to property and casualty as a whole. Second, the global growth rate has decelerated sharply: Howden's 2025 report measured worldwide cyber premiums growing at roughly 6% CAGR from 2022 to 2024, down from approximately 40% CAGR from 2020 to 2022 (Howden 2025 Cyber Report). The post-2022 cyber market is no longer growth-stage; it is a maturing line.
European cyber insurance penetration remains low. Howden reports that only 22% of businesses in Italy carry cyber insurance and 39% in the UK, with more than 70% of companies across France, Germany, Italy, and Spain combined remaining uninsured for cyber (Howden 2025 Cyber Report). The opportunity is real; the take-up has been slow.
US market: AM Best, NAIC, and the first-ever annual decline
The US standalone cyber line is the single most-tracked piece of the global market because of AM Best's annual segment report and NAIC's Cybersecurity Insurance Report. Both 2025 editions covered calendar year 2024.
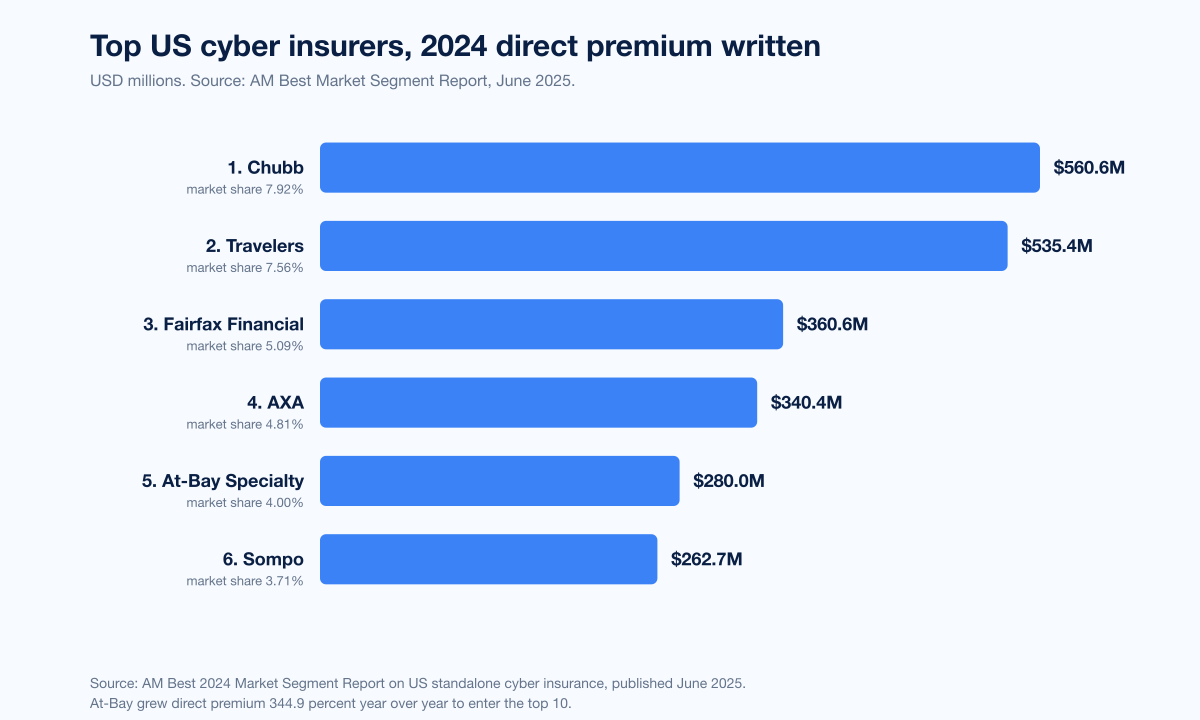
AM Best: US standalone cyber direct premium written totaled US$7.075 billion in 2024, a 2.3% decline from 2023, the first ever year-over-year drop since AM Best began tracking US cyber data in 2015 (AM Best press release, June 2025). Loss ratio rose to 48.8% in 2024 versus 41.6% in 2023 (+7.2 ppt), still profitable but with margins compressing. Top US writers by 2024 direct premium: Chubb US$560.6M (~7.92% market share); Travelers US$535.4M (~7.56%, +39.1% YoY); Fairfax Financial US$360.6M (~5.09%); AXA US$340.4M (~4.81%); At-Bay Specialty US$280M (+344.9% YoY, ~4.00%); Sompo US$262.7M (~3.71%) (Insurance Business / AM Best ranking; BeInsure ranking).
NAIC: under reclassified 2024 reporting in NAIC's 2025 Cybersecurity Insurance Report, primary policies generate 65% of cyber premium, excess 31%, and endorsement 4% (NAIC 2025 Cybersecurity Insurance Report). The reclassification cleaned up a long-standing comparability issue between AM Best (which historically counted standalone) and NAIC (which historically counted both standalone and bundled). The US numbers across both publishers now triangulate.
Pricing: eight straight quarters of cuts
Marsh's Global Insurance Market Index (GIMI) is the canonical broker-side rate benchmark. Its cyber line has now logged eight consecutive quarterly declines through Q1 2026.
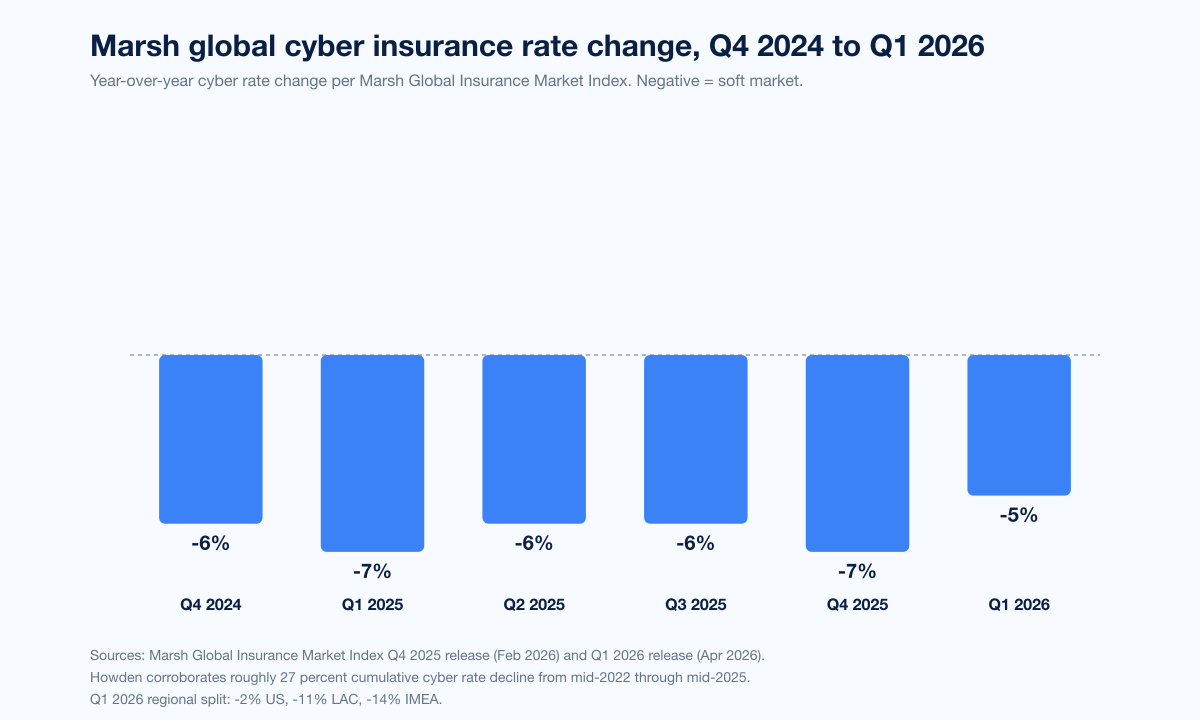
Q4 2025 GIMI: cyber rate down 7% globally, with regional cuts ranging from -14% in LAC to -3% in US (Marsh Q4 2025 release).
Q1 2026 GIMI: cyber rate down 5% globally, with -14% IMEA, -11% LAC, -2% US, and an overall global commercial rate down 5% (the seventh consecutive quarterly decline in overall global commercial insurance rates, of which cyber is the most consistent contributor) (Marsh Q1 2026 release).
Aon's 2025 Cyber Risk Report measured a 7% premium decrease in Q1 2025 for cyber buyers (Aon Cyber Risk Report 2025).
Howden's 2025 Cyber Report aggregates the trajectory: cumulative cyber rate decline of approximately 27% from mid-2022 through mid-2025 (Howden 2025 Cyber Report; Cyber Insurance News summary).
The pricing trend is consistent across continents and across broker, ratings agency, and primary-publisher data. What it has not done is collapse the underlying profitability of the line: Howden estimates cumulative cyber underwriting profit of approximately US$9 billion between 2022 and 2024 with combined ratios averaging 70%. The market gave back rate from a position of strength.
Loss ratios: AM Best's five-year arc
The clearest profitability series for US cyber is AM Best's loss ratio history.
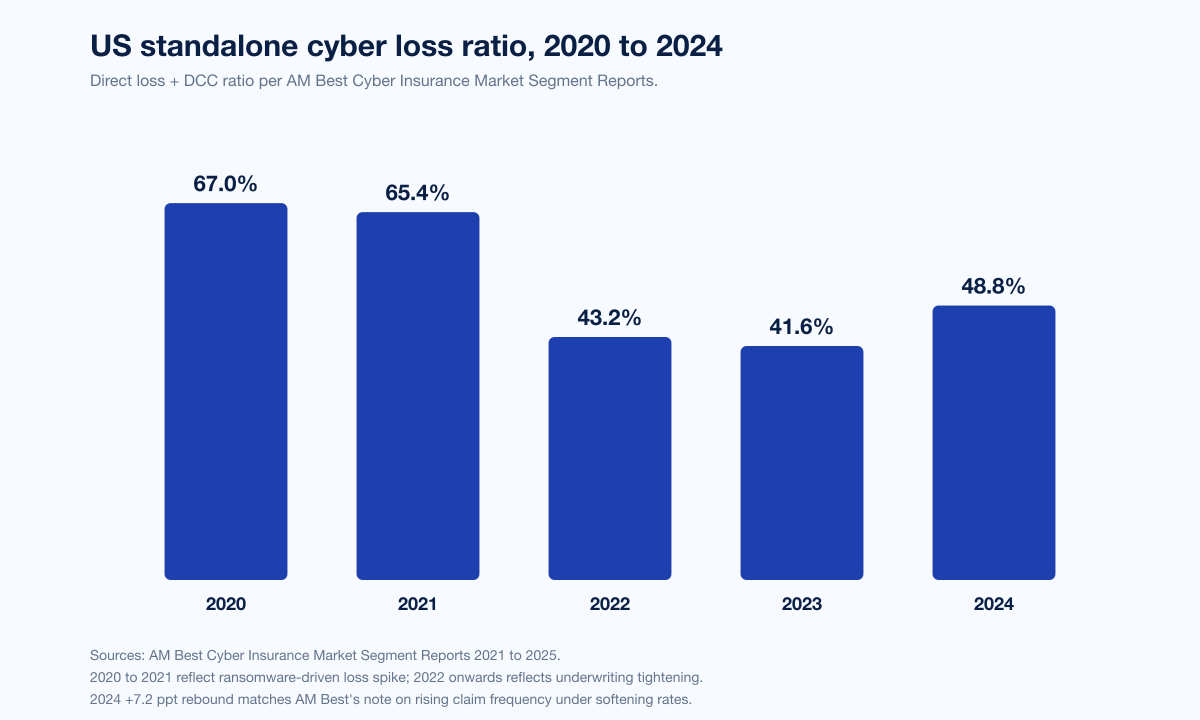
Year | US standalone cyber loss ratio |
|---|---|
2020 | ~67.0% |
2021 | ~65.4% |
2022 | ~43.2% |
2023 | 41.6% |
2024 | 48.8% |
The arc is a textbook hard-to-soft transition. The 2020 to 2021 spike was the ransomware-driven loss explosion that produced the 2021 to 2022 hard market and a roughly 150% rise in average premium per cyber policy during the same window. The 2022 to 2023 retreat was the underwriting tightening (MFA, EDR, IR plans, immutable backups) doing its job. The 2024 +7.2 ppt rebound is the soft market biting back: pricing came down 7% YoY in Q4 2025 and claim frequency rose, so loss ratio drifts up. AM Best's segmental note for 2024 attributes the rebound to rising claim frequency under softening rates rather than to a shift in incident severity.
Claims: Coalition's 2026 dataset and At-Bay's full-year 2025
Two annual claims publications now anchor the US-and-allied cyber claims picture: Coalition's Cyber Claims Report (annual since 2022) and At-Bay's InsurSec Report (annual since 2024). Both produce 2026 editions covering full-year 2025 telemetry.
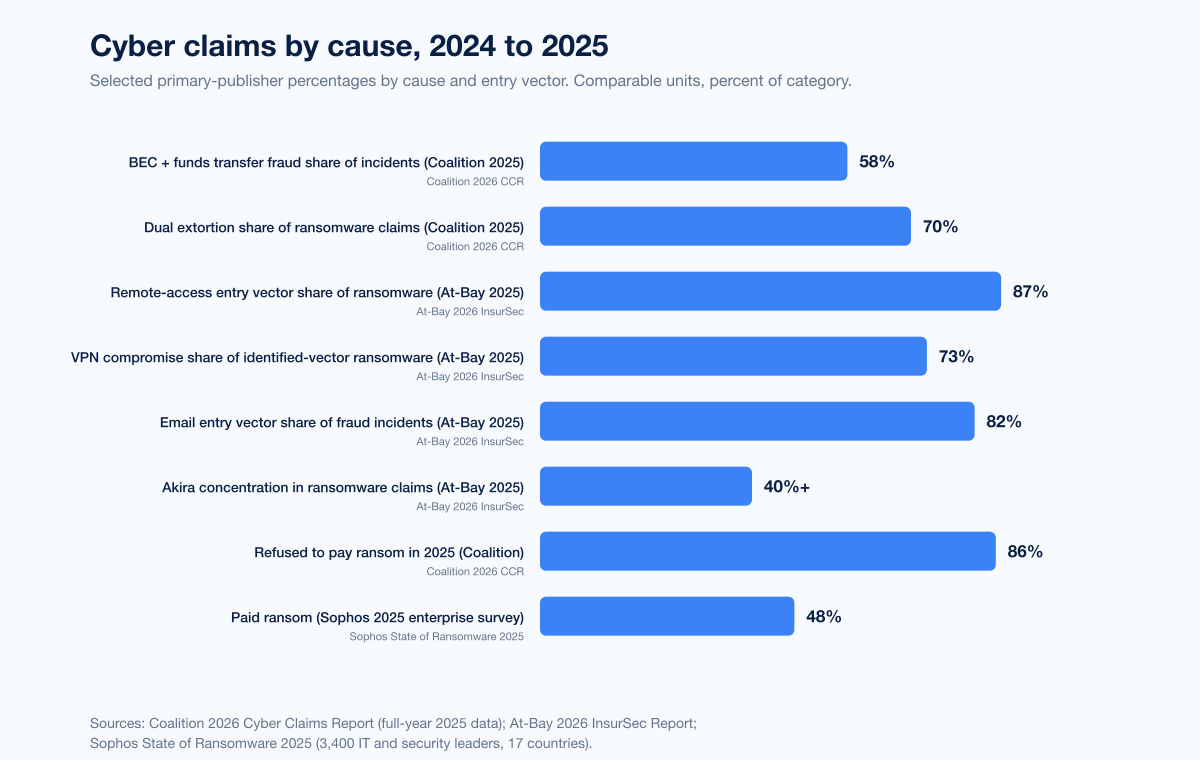
Coalition 2026 Cyber Claims Report (covering full-year 2025; dataset spans more than 100,000 policyholders across the US, Canada, UK, Australia, and Germany) (Coalition 2026):
Initial ransom demands surged +47% YoY in 2025 to an average of more than US$1 million.
86% of businesses refused to pay ransoms in 2025, a record high (The Actuary, April 2026).
BEC + funds transfer fraud accounted for 58% of cyber incidents in 2025; 52% of FTF claims originated from BEC.
Average ransomware claim loss: US$269K in 2025, the most expensive category by claim.
Dual-extortion ransomware (encryption + data theft) accounted for 70% of all ransomware claims in 2025; data-theft attacks were 2x+ more expensive than encryption-only.
Coalition recovered US$21.8M in stolen funds for policyholders in 2025, average per recovery US$202K.
The 2025 Cyber Claims Report (covering full-year 2024) provided the comparison base. 44% of policyholders that experienced a ransomware event opted to pay when paying was deemed reasonable and necessary, with a Coalition Incident Response team negotiating an average 60% reduction when policyholders did pay (Coalition 2025 Cyber Claims Report). 56% of cyber matters reported to Coalition were handled with no out-of-pocket payments by the policyholder. The shift from a 44% pay rate in 2024 to an 86% refuse rate in 2025 is the largest single year-on-year movement in cyber-insurance ransom-payment statistics on record.
At-Bay 2026 InsurSec Report (covering full-year 2025; dataset spans more than 100,000 policy years) (Help Net Security, April 2026; Insurance Business, April 2026; Swept.ai summary):
+7% YoY rise in overall claim frequency; all-time-high average severity US$221K.
Ransomware severity reached US$508K in 2025, +16% YoY, the costliest incident type.
Akira ransomware accounted for more than 40% of ransomware claims; average Akira ransom demand US$1.2M, roughly 50% higher than other groups.
Remote-access services were the entry vector for 87% of ransomware claims in 2025 (up from 80% the prior year). VPN compromise alone accounted for 73% of identified-vector ransomware intrusions, climbing from 38% in 2023 and 66% in 2024.
Financial fraud (BEC) was approximately 30% of all claims for the third consecutive year; email was the initial entry vector in 82% of fraud incidents; average stolen funds US$285K, +16% YoY; largest single fraud loss US$9.65M.
Companies under US$25M revenue saw frequency +21% and severity +40%, with ransomware severity in that segment reaching US$422K.
The Aon Q2 2025 cyber-and-E&O update added two notable counterpoints. Global ransomware incident counts fell -6% quarter-over-quarter in Q2 2025, but the average ransomware demand jumped +104% to US$1.13M per case, reinforcing the Coalition observation that fewer cases are bigger (Aon, Q2 2025). Aon's Global 2025 Cyber Risk Report counted 1,228 cyber/E&O incidents reported across Aon broking clients in 2024, +22% YoY, with US-only at 776 reported incidents in 2024, up roughly a third YoY (Aon Cyber Risk Report 2025). Aon also measured ransomware incidents +24% in 2024 versus 2023, with the average ransomware payment falling -77% in 2024 as more victims refused to pay or negotiated demands down.
NetDiligence: 15 years of cyber claims pricing
NetDiligence publishes the most-cited claim-size dataset for cyber insurance, the Cyber Claims Study (now in its 15th annual edition). The 2025 study analyzed 10,402 cyber insurance claims from incidents 2020 to 2024 (NetDiligence 2025; press release; Carrier Management summary).
Five-year average incident cost: US$246K for SMEs (under US$2B revenue) and US$10.3M for large companies.
SME 5-year average claim rose to US$264K, +29% from the prior year's report.
SMEs were 98% of claims by count; large companies 2% of claims but more than 50% of total incident cost.
Claim sizes ranged from less than US$1K to more than US$500M.
Ransomware initial demands as high as US$150M; ransoms paid as high as US$75M.
Business-interruption claims averaged 650%+ higher total incident cost than non-BI claims.
Large-enterprise BI claims averaged US$36.1M total, including US$26M in downtime costs.
Ransomware incidents with recovery expenses averaged US$961K total, nearly 400% higher than incidents without recovery expenses (Cyber Insurance News summary).
1,864 BEC claims tracked across the 5-year window; 468 BEC claims in 2024 alone; average US$75K per BEC claim.
The NetDiligence numbers explain the dispersion in average vs median claim sizes that confuses some buyers: 2% of claims drive more than half of total cost. SME programs price the median; large-account programs price the long tail.
Sophos State of Ransomware 2025: a parallel survey lens
Sophos's 2025 State of Ransomware report (June 2025) surveys 3,400 IT and cybersecurity leaders across 17 countries at organizations between 100 and 5,000 employees (Sophos press release).
48% of enterprise organizations paid the ransom when hit, down from 56% the prior year.
53% of ransom-paying victims paid less than the original demand; 71% of those negotiated the price down.
Median ransom demand US$1.20M in 2025, down -56% from US$2.75M in 2024.
Median ransom payment US$1M in 2025, down from US$1.26M in 2024.
Backups used to recover data dropped to 53%, a four-year low, down from 73%.
The Sophos numbers are not directly comparable to Coalition or At-Bay (different denominator, different respondent universe), but the directional signal is the same: more victims are refusing to pay and the median payment trajectory is downward, even as a small number of high-severity ransomware events drag averages back up.
Allianz Risk Barometer: cyber as #1 risk for the fifth straight year
The Allianz Risk Barometer is the longest-running global business risk survey and a useful triangulation point on demand for cyber insurance.
Allianz Risk Barometer 2025: cyber incidents are the #1 global business risk for the fourth consecutive year, with 38% of responses, the largest margin ever. Business interruption #2 with 31% of responses; natural catastrophe #3. A decade earlier in 2015, cyber risk was #8 globally with just 12% of responses (Allianz, January 2025).
Allianz Risk Barometer 2026: cyber #1 for the fifth consecutive year, with the highest-ever 42% of responses and a +10ppt margin over AI risk at #2. Cyber ranks #1 across every region (Americas, Asia Pacific, Europe, Africa & Middle East) and across all company-size tiers. Survey: 3,338 risk-management experts from nearly 100 countries (Allianz, January 2026; BusinessWire).
The Allianz signal is unambiguous: cyber risk concern is rising, not plateauing, even as cyber insurance pricing softens. That gap between perceived risk and willingness to pay for coverage is the structural reason European take-up remains low.
Named loss events: Change Healthcare, CrowdStrike, MGM, Caesars
A small number of named events shape industry loss-ratio narrative for the 2024 to 2025 cycle. Each is corroborated by SEC filings or court records.
UnitedHealth Group / Change Healthcare, February 2024. The breach of Change Healthcare's claims-processing platform crippled US prescription, billing, and claims workflows for weeks. Reported impacts:
UnitedHealth Group's Q3 2024 disclosure put total full-year 2024 cyber-attack impact at US$2.457 billion (Cybersecurity Dive, March 2025). Direct response and remediation costs alone were over US$1 billion within the first three months.
The breach is widely cited as the largest US healthcare cyber-attack disclosure in dollars, although the headline figure is dominated by business impact and customer reimbursement, not insurance recoveries alone.
CrowdStrike Falcon update, July 19, 2024. A faulty channel-file update to the CrowdStrike Falcon endpoint sensor crashed approximately 8.5 million Windows systems worldwide, the largest single IT outage in history (Wikipedia, 2024 CrowdStrike-related IT outages). It was operational, not malicious, but cyber and tech-E&O policies covered a meaningful share of the consequential business interruption. Insured-loss estimates from major brokers and modeling firms span a wide range:
Parametrix: approximately US$5.4 billion in direct losses to the Fortune 500 (excluding Microsoft); approximately US$540M to US$1.08B insured (~10% to 20% of direct), out of approximately US$10B to US$15B in industry-wide cyber insurance liabilities (Fortune via Parametrix, August 2024).
Guy Carpenter: insured losses of approximately US$300 million to US$1 billion (Cybersecurity Dive, August 2024).
CyberCube: insured losses of approximately US$400 million to US$1.5 billion (Cybersecurity Dive).
Fitch Ratings: industry-wide impact in the mid- to high-single-digit billion USD range.
Hardest-hit Fortune-500 sectors: healthcare US$1.94 billion; banking US$1.15 billion (Parametrix).
The CrowdStrike outage is the single best-documented systemic cyber event in primary-source coverage. It stress-tested the cyber line's ability to absorb a non-malicious global IT failure and produced the first concrete spread of insured-loss estimates across multiple modeling firms.
MGM Resorts International, September 2023. SEC Form 8-K filed October 5, 2023 disclosed a US$100 million financial impact from a ransomware-grade cyber attack and IT shutdown.
Caesars Entertainment Inc., September 2023. SEC Form 8-K filed September 7, 2023 confirmed approximately US$15 million paid in ransom following a parallel social-engineering compromise.
These four events collectively account for the bulk of named-large-loss cyber narrative across 2023 to 2024 and inform the loss-ratio rebound visible in the AM Best 2024 number.
Underwriting requirements: MFA, EDR, backups
Marsh McLennan's 2024 cyber-application data showed 41% of cyber insurance applications denied on first submission, with the top denial reasons being missing MFA and inadequate endpoint protection (Prescient Solutions summary). The 2025 Marsh McLennan Cyber Insurance Market Report further measured:
96% of cyber insurers mandate enforced MFA across email, VPN, RDP, cloud apps, and admin accounts (CyberDuo summary of Marsh McLennan 2025).
88% of carriers require EDR or MDR tools deployed across all endpoints.
94% of organizations hit by ransomware saw threat actors target backups (Coalition), driving carrier insistence on immutable / offline backup copies (Coalition 2025).
The list of carrier-mandated controls has hardened over the 2022 to 2025 cycle from a polite preference list into hard underwriting filters. Buyers without enforced MFA on remote-access services, EDR/MDR on every endpoint, an annually tested incident-response plan, immutable backups segregated from production, and patching SLAs against known-exploited vulnerabilities are now routinely declined or surcharged. The Stingrai team's view is that this control list is the floor, not the ceiling. Buyers competing for best-in-class pricing now also need to demonstrate an offensive testing program, with continuous penetration testing or PTaaS coverage on internet-facing assets, and external attack-surface monitoring.
Regulation: war exclusion, state-backed exclusion, and DORA
Three regulatory beats define cyber-insurance coverage scope through 2026.
Mondelez vs Zurich settlement, November 2022. The seven-year property/cyber coverage dispute over Mondelez's US$100 million+ NotPetya claim settled in November 2022 without producing precedential court guidance on the "act of war" exclusion (Cybersecurity Dive, November 2022). The settlement was a turning point: it ended the appetite for case-by-case war-exclusion litigation and pushed the market toward explicit cyber-war exclusions in policy wordings.
Lloyd's of London state-backed exclusion mandate, effective March 31, 2023. Lloyd's required all standalone cyber policies to exclude state-backed cyber attacks at inception or renewal from that date, with explicit attribution criteria and a systemic-impact carve-out (CSO Online, August 2022; Lloyd's bulletin LMA5564). The mandate flows through London market wordings and influences global policy drafting.
EU Digital Operational Resilience Act (DORA), application date January 17, 2025. DORA applies to 20 categories of financial entities plus their ICT third-party providers, with administrative penalties up to 2% of total annual worldwide turnover or 1% of average daily global turnover (EIOPA DORA materials). DORA imposes direct ICT-risk management, incident-reporting, third-party-risk, and operational resilience-testing obligations on covered entities and indirectly increases demand for cyber insurance from the EU financial sector.
Outlook: what primary publishers project for 2026
Few primary publishers offer 2026 forecasts. The ones that do have produced a consistent picture:
Munich Re: global cyber GWP more than doubling by 2030 at a 10%+ CAGR; North America rising from more than US$10B in 2024 toward approximately US$20B by 2030. The company highlights AI-driven loss accumulation and ransomware variant evolution as key 2026 to 2030 watch items (Munich Re Cyber Insurance Risks and Trends 2025).
Marsh: Q1 2026 GIMI signals continued softening in cyber rates through at least mid-2026, with the gap between US (-2%) and IMEA (-14%) narrowing as US underwriters absorb the AM Best 2024 loss-ratio rebound. The Marsh release explicitly notes that softening "remains a feature of the global commercial insurance market" through Q1 2026 (Marsh Q1 2026).
Aon: US$1.13M average ransom demand in Q2 2025 (+104% QoQ) suggests the second half of 2025 and 2026 will see severity rise even as frequency softens. Aon's view is that buyer-friendly conditions will persist into 2026 but capacity discipline is tightening on accumulation accounts (large healthcare, large financial services) (Aon Q2 2025).
Howden: cumulative cyber underwriting profit through 2024 of approximately US$9 billion is the float that funds 2026 capacity; Howden explicitly framed its 2025 report as "Rebooting Growth" because the slowdown from 40% CAGR (2020 to 2022) to 6% CAGR (2022 to 2024) requires the next leg of growth to come from underpenetrated sectors and geographies, not from rate increases (Howden 2025 Cyber Report).
Allianz: cyber risk concern at 42% of responses in 2026, the highest in survey history, with AI risk the fastest-rising parallel (#2 at 32%). The signal is that demand for coverage in 2026 will be driven by AI-enabled incident scenarios more than by traditional ransomware narrative (Allianz Risk Barometer 2026).
The market-watcher consensus across the five publishers above: rates continue to soften into mid-2026, severity continues to rise faster than frequency, and demand growth comes from European and Asian penetration plus AI-driven risk awareness rather than from US enterprise pricing.
What this means for defenders
For CISOs and risk officers planning 2026 cyber insurance renewal, four operational themes carry over from the 2025 data.
First, MFA and EDR are now decision gates, not preferences. 96% of carriers require enforced MFA across remote-access, email, RDP, cloud, and admin accounts, and 88% require EDR or MDR on every endpoint. A 2026 renewal application that does not affirmatively answer both is denied or surcharged on first review.
Second, VPN compromise is the top single ransomware vector by a wide margin, with At-Bay measuring it at 73% of identified-vector intrusions in 2025. The 2026 Stingrai recommendation is to deprecate username + password VPN access entirely, move to phishing-resistant authentication (FIDO2 / WebAuthn) on every remote-access path, and integrate zero-trust network access (ZTNA) for staff plus contractors. Anything less leaves the most-exploited entry vector in place.
Third, third-party and IT-vendor exposure is the second-largest category of cloud-compromise initial vectors in Mandiant's M-Trends 2026 (17%), and 52% of Coalition first-party losses traced back to a third party in 2025. Cyber insurance applications now ask granular questions about vendor risk management, support-portal MFA, and third-party access controls. Policy buyers should pre-audit their top 25 vendors against the same criteria carriers will ask about.
Fourth, business-interruption coverage limits are the line item most at risk of being underbought. NetDiligence's data shows BI claims averaging 650%+ higher total cost than non-BI claims, with large-enterprise BI averaging US$36.1M total. The CrowdStrike outage produced insured BI losses ranging from US$300M to US$1.5B industry-wide. Buyers should re-test BI sublimits against modeled outage scenarios (single-cloud outage, single-vendor SaaS outage, single-EDR outage) and against realistic downtime estimates (not the optimistic four-hour figure).
Stingrai's offensive-testing programs are designed to feed directly into the carrier underwriting questionnaire. The PTaaS platform produces continuous external-surface coverage with reporting that maps to Marsh, Aon, and Lockton renewal questionnaires. For organizations that need to demonstrate active vulnerability management to a carrier, Stingrai's external attack surface management and red-team simulation tooling produce the audit-ready evidence pack a 2026 renewal underwriter expects.
Frequently Asked Questions
What is the most cited cyber insurance statistic for 2026?
The most cited single figure for 2026 is Munich Re's measurement of approximately US$15.3 billion in global cyber insurance gross written premium for 2024, with North America carrying more than US$10 billion of that on its own and the trajectory pointing at a doubling by 2030 at a 10%+ CAGR. The most cited US-specific stat is AM Best's June 2025 segment report finding US$7.075 billion in 2024 US standalone direct premium written, down 2.3% YoY, the first ever annual decline since AM Best began tracking the line in 2015. The most cited claims stat is Coalition's 2026 finding that 86% of insured businesses refused to pay ransoms in 2025, a record high, even as the average initial ransom demand jumped +47% YoY to more than US$1 million.
How big is the global cyber insurance market in 2026?
Munich Re's 2025 report puts global cyber insurance gross written premium at approximately US$15.3 billion in 2024 and projects the line more than doubling by 2030 at an average annual rate of more than 10%. North America wrote more than US$10 billion of the 2024 total and is projected to grow toward roughly US$20 billion by 2030. Cyber represents less than 1% of total global P&C insurance premium volume in 2024, so the line is small relative to property and casualty as a whole but among the fastest-growing.
What did cyber insurance rates do in 2025 and Q1 2026?
Marsh's Global Insurance Market Index recorded the cyber line down 7% globally in Q4 2025 and 5% in Q1 2026, marking eight consecutive quarterly cuts. Regional Q1 2026 splits: -2% US, -11% LAC, -14% IMEA. Howden's 2025 Rebooting Growth report places cumulative cyber rate decline at approximately 27% from mid-2022 through mid-2025. Aon recorded a 7% premium decrease in Q1 2025 for cyber buyers. The trend is consistent across continents: rates are softening, but profitability has held because cumulative cyber underwriting profit from 2022 to 2024 was approximately US$9 billion at a 70% combined ratio (Howden).
What is the average cyber insurance claim size in 2025?
NetDiligence's 15th Annual Cyber Claims Study, analyzing 10,402 claims from 2020 to 2024, puts the 5-year average incident cost at US$246K for SMEs (under US$2B revenue) and US$10.3M for large companies. SMEs were 98% of claims by count but large companies drove more than 50% of total incident cost. At-Bay's 2026 InsurSec Report measured an all-time-high average claim severity of US$221K across more than 100,000 policy years for full-year 2025. Coalition's 2026 Cyber Claims Report measured an average ransomware claim loss of US$269K in 2025, the most expensive category by claim.
How much do most ransomware victims pay in 2025?
Coalition's 2026 Cyber Claims Report found 86% of insured businesses refused to pay ransoms in 2025, a record high. Of those that did pay, Coalition Incident Response negotiated an average 60% reduction from initial demand. Sophos's 2025 State of Ransomware survey of 3,400 IT leaders across 17 countries found 48% of enterprise organizations paid the ransom, down from 56% the prior year, with median ransom payment US$1 million in 2025 versus US$1.26 million in 2024. Initial demands rose: Coalition measured average initial ransom demand at more than US$1 million in 2025, +47% YoY, while Aon Q2 2025 measured average ransomware demand at US$1.13M (+104% QoQ).
What are carriers requiring before they will write a 2026 cyber policy?
Marsh McLennan's 2024 application data showed 41% of cyber applications denied on first submission, with missing MFA and inadequate endpoint protection the top reasons. Marsh McLennan's 2025 carrier survey found 96% of cyber insurers mandate enforced MFA across email, VPN, RDP, cloud apps, and admin accounts; 88% require EDR or MDR deployed on every endpoint. Coalition reports 94% of organizations hit by ransomware saw threat actors target backups, which has driven carrier insistence on immutable / offline backup copies. The de-facto carrier checklist for 2026: enforced phishing-resistant MFA, EDR/MDR coverage, immutable backups, an annually tested IR plan, patching SLAs against known-exploited vulnerabilities, and increasingly an offensive-testing or PTaaS program on internet-facing assets.
Who are the largest cyber insurers in the US?
AM Best's 2024 segment report ranking by US standalone direct premium written: Chubb (US$560.6M, ~7.92% market share), Travelers (US$535.4M, ~7.56% share, +39.1% YoY), Fairfax Financial (US$360.6M, ~5.09%), AXA (US$340.4M, ~4.81%), At-Bay Specialty (US$280M, ~4.00%, +344.9% YoY entering top 10), Sompo (US$262.7M, ~3.71%). Globally, Munich Re, Allianz (AGCS), AIG, Beazley, Hiscox, AXA XL, and Tokio Marine HCC all rank in the top tier of cyber writers, with Coalition, At-Bay, Resilience, and Cowbell representing the largest InsurTech-backed cyber-only specialists.
What does the CrowdStrike outage tell us about systemic risk?
The July 19 2024 CrowdStrike Falcon update crashed approximately 8.5 million Windows systems worldwide, the largest single IT outage in history. The event was operational rather than malicious, but cyber and tech-E&O policies covered a meaningful share of the consequential business interruption. Insured-loss estimates from major brokers and modeling firms span a wide range: Guy Carpenter US$300M to US$1B, CyberCube US$400M to US$1.5B, Parametrix US$540M to US$1.08B insured of US$5.4B Fortune-500 direct losses, and Fitch Ratings mid- to high-single-digit billion USD industry impact. Hardest-hit Fortune-500 sectors were healthcare at US$1.94 billion and banking at US$1.15 billion in direct losses (Parametrix). The event is the single best-documented systemic cyber accumulation case in primary-source coverage and stress-tested the cyber line's ability to absorb a non-malicious global IT failure.
How did UnitedHealth's Change Healthcare attack affect cyber insurance?
UnitedHealth Group's Q3 2024 disclosure put total full-year 2024 cyber-attack impact at approximately US$2.457 billion, with direct response and remediation costs alone exceeding US$1 billion within the first three months. The breach is widely cited as the largest US healthcare cyber-attack disclosure in dollars. The figure is dominated by business impact and customer reimbursement rather than insurance recoveries alone, but it set the new ceiling for single-event healthcare cyber loss disclosure and informed the AM Best 2024 US loss-ratio rebound to 48.8%.
What is DORA and what does it mean for cyber insurance demand?
The EU Digital Operational Resilience Act (DORA) entered application on January 17, 2025, applying to 20 categories of financial entities and their ICT third-party providers. Administrative penalties run up to 2% of total annual worldwide turnover or 1% of average daily global turnover. DORA imposes direct ICT-risk management, incident-reporting, third-party-risk, and operational resilience-testing obligations on covered entities. The indirect effect on cyber insurance is to increase demand from the EU financial sector through 2026 and 2027 as covered entities expand cyber programs to demonstrate compliance. DORA does not mandate cyber insurance purchase, but it does mandate the kinds of controls that materially reduce the cost of a 2026 cyber insurance renewal.
How do US and European cyber insurance penetration rates compare?
Howden's 2025 Cyber Report found only 22% of businesses in Italy carry cyber insurance and 39% in the UK, with more than 70% of companies across France, Germany, Italy, and Spain combined remaining uninsured for cyber. The US standalone cyber market wrote US$7.075 billion in 2024 with significant penetration across mid-market and enterprise, while European take-up has been markedly slower despite cyber risk ranking #1 in Allianz Risk Barometer 2025 and 2026. The structural gap between perceived risk (42% of responses, the highest ever) and willingness to pay for coverage is the central reason European cyber insurance growth is the line's biggest 2026 to 2030 opportunity.
Where can I get the latest cyber insurance market data?
The primary publishers to track for cyber insurance market and claims telemetry are: Munich Re (annual Cyber Insurance: Risks and Trends report), Marsh (quarterly Global Insurance Market Index releases), Aon (annual Global Cyber Risk Report and quarterly cyber-and-tech-E&O updates), Howden (annual Cyber Report), Coalition (annual Cyber Claims Report, every March or April), At-Bay (annual InsurSec Report, every April), NetDiligence (annual Cyber Claims Study, every September), AM Best (annual US Cyber Insurance Market Segment Report, every June), the National Association of Insurance Commissioners (annual Cybersecurity Insurance Report), Lloyd's of London (market bulletins and Lloyd's Lab outputs), Allianz (annual Risk Barometer, every January), Sophos (annual State of Ransomware, every June), and Fitch Ratings, S&P Global, Guy Carpenter, CyberCube, and Parametrix on systemic-risk modeling. UK Information Commissioner's Office, US SEC Form 8-K filings, and EU DORA bulletins from EIOPA also produce primary-source cyber-incident and regulatory data on a continuous basis.
Related reading
Ransomware Payouts Statistics 2026: the complementary view on ransomware payment trajectories, including the same Coalition 86% refusal-rate finding and the matching Sophos 48% pay-rate measurement.
Compromised Credential Statistics 2026: the upstream attack vector behind most ransomware claims; underpins the carrier MFA underwriting requirement.
Top Industries Targeted by Hackers 2026: healthcare and financial services concentration consistent with Allianz Risk Barometer #1 cyber rank and AM Best 2024 segment data.
Supply Chain Attack Statistics 2026: Change Healthcare and CrowdStrike Falcon outage covered there from the supply-chain lens; this post covers them from the insurance lens.
AI Cyber Attack Statistics 2026: the rate-of-AI-attack-growth that feeds carrier underwriting questionnaires evolution and reinforces Allianz's 2026 finding of AI risk as the fastest-rising parallel to cyber.
References
AM Best. US Cyber Insurance Market Segment Report. June 2025. Press release.
Allianz Commercial. Allianz Risk Barometer 2025. January 2025. Allianz.
Allianz Commercial. Allianz Risk Barometer 2026. January 2026. Allianz; BusinessWire summary.
Aon. Global Cyber Risk Report 2025. February 2025. Aon; Q2 2025 update; ransomware payouts decline.
At-Bay. 2026 InsurSec Report (full-year 2025 data). April 2026. Help Net Security summary; Insurance Business summary; Swept.ai summary.
BeInsure. Global Ranking of Cyber Insurers. 2025. BeInsure.
Coalition. 2025 Cyber Claims Report. March 2025. Coalition announcement; blog summary.
Coalition. 2026 Cyber Claims Report. April 2026. Coalition; The Actuary, April 2026.
CSO Online. Lloyd's of London to exclude state-backed attacks. August 2022. CSO Online.
Cyber Insurance News. Cyber insurance market down 27 percent, 2026 outlook. 2025. Cyber Insurance News; NetDiligence summary.
CyberDuo. Cyber Insurance Renewal Denied 2026 Checklist. CyberDuo.
Cybersecurity Dive. UnitedHealth's cyber-attack costs reach US$2.3B. March 2025. Cybersecurity Dive; insured losses CrowdStrike, August 2024; Mondelez Zurich settlement, November 2022; CrowdStrike Fortune 500 losses.
EIOPA. Digital Operational Resilience Act (DORA). EIOPA.
Fortune (via Parametrix). CrowdStrike outage Fortune 500 5.4 billion damages. August 2024. Fortune.
Howden. 2025 Cyber Report: Rebooting Growth. September 2025. Howden Group Holdings.
Industrial Cyber. Munich Re sees untapped potential in 15.3B cyber insurance market. 2025. Industrial Cyber.
Insurance Business. The 10 best cyber insurance companies based on US market share. 2025. Insurance Business.
Marsh. Global Insurance Market Index Q4 2025. February 2026. Marsh.
Marsh. Global Insurance Market Index Q1 2026. April 2026. Marsh.
Munich Re. Cyber Insurance: Risks and Trends 2025. March 2025. Munich Re.
NAIC. 2025 Cybersecurity Insurance Report. 2025. NAIC.
NetDiligence. 15th Annual Cyber Claims Study. September 2025. NetDiligence; press release; Carrier Management summary.
Prescient Solutions. Cyber Insurance Requirements 2026 SMB Checklist. Prescient Solutions.
Reinsurance News. Global cyber premium to more than double by 2030 (Munich Re). Reinsurance News.
Sophos. State of Ransomware 2025. June 2025. Sophos.
Wikipedia. 2024 CrowdStrike-related IT outages. Wikipedia.
Take action with Stingrai
Cyber insurance underwriters in 2026 are reading the same primary-source data this post compiles: rising claim frequency, rising ransom demands, falling pay rates, and a small handful of named events that drive the loss-ratio narrative. Buyers who can demonstrate active offensive-testing programs against their internet-facing surface and their critical internal applications get faster underwriting, lower surcharges, and higher coverage limits.
Stingrai is a Toronto and London based offensive security firm founded in 2021. The team holds 18 published CVEs (Ivan Spiridonov 10, Moaaz Taha 5, Victor Villar 3) and certifications including OSCE3, OSCP, OSWE, OSED, OSEP, CREST CRT, CISSP, CRTO, GCPN, CRTE, and eWPTX. Stingrai is rated 5.0/5.0 across 19 Clutch reviews, presents original research at DEFCON and BSIDES, and aligns engagements to SOC 2, ISO 27001, HIPAA, PCI DSS 4.0, NIST SP 800-53 / 800-171, DORA, and NIS2.
Three places to start:
PTaaS: continuous platform-led penetration testing with our AI agent Snipe, trained on more than 6,000 HackerOne reports. Carrier-aligned reports for Marsh, Aon, and Lockton renewal questionnaires.
Penetration Testing: external, internal, web, mobile, cloud, AD, and AI-application engagements. Reports map directly to underwriter control assertions.
Read the case studies: customer engagements across SaaS, fintech, healthcare, and gov-tech, with public-permission references.
If your 2026 cyber insurance renewal is up in the next 90 days, book a 30 minute call. Stingrai will return a no-cost gap analysis against the carrier checklist (MFA, EDR, IR plan, backup posture, vulnerability management, third-party risk) and a one-page recommendation letter that fits the application form.