Cryptocurrency theft set a new high-water mark in 2025. Chainalysis's 2026 Crypto Crime Report recorded US$3.4 billion stolen from January through early December 2025, surpassing every prior year except 2022. The Bybit incident of February 21, 2025 alone accounted for nearly US$1.5 billion of that total in a single day, the largest digital-asset heist ever attributed and confirmed by the FBI's IC3 public service announcement as the work of North Korea's TraderTraitor cluster within the Lazarus Group. Concentration tells the story: the top three hacks combined drove 69% of all 2025 service-side losses, and a single nation-state actor was responsible for US$2.02 billion, or 76% of all service compromises, per Chainalysis.
This post is the Stingrai research team's canonical 2026 reference for cryptocurrency hacking and theft. It triangulates 88 numeric claims across 18 named primary publishers, including Chainalysis, Elliptic, TRM Labs, CertiK, Immunefi, PeckShield, SlowMist, Halborn, the FBI Internet Crime Complaint Center, NCC Group, and Trail of Bits. Lead data is full-year 2025 telemetry, the freshest available; primary publishers have not yet released full-year 2026 reports as of April 2026. Every figure carries its source, year, and methodology window so any claim can be audited inline.
The four largest publishers do not agree on a single number for 2025. PeckShield's broadest tally, which bundles direct hacks with scams and frauds, lands at US$4.04 billion (up 34.2% YoY). Chainalysis, whose scope is service compromises plus a sampled personal-wallet expansion, lands at US$3.4 billion. CertiK, counting blockchain security incidents end to end, lands at US$3.35 billion. SlowMist, working from its SlowMist Hacked archive and Anti-Money-Laundering data, lands at US$2.935 billion. The four numbers are not contradictions; they are different frames over the same underlying activity. We reconcile them explicitly below so that any number you cite from this post can be defended against a fact-check.
TL;DR: 12 labeled key stats
Total cryptocurrency stolen, 2025 (Chainalysis): US$3.4B from January through early December 2025 (Chainalysis 2026 Crypto Crime Report).
Total cryptocurrency stolen, 2025 (PeckShield, hacks plus scams): US$4.04B, up 34.2% YoY (PeckShield 2025 annual aggregator).
Total cryptocurrency stolen, 2025 (CertiK Hack3d): US$3.35B across blockchain security incidents (CertiK Skynet Hack3d 2025 Annual Report).
DPRK stolen funds, 2025 (Chainalysis): US$2.02B, +51% YoY, all-time cumulative US$6.75B (Chainalysis 2026 CCR).
Bybit hack, Feb 21 2025: ~US$1.5B stolen, ~401,000 ETH, attributed by the FBI to DPRK / Lazarus / TraderTraitor (FBI IC3 PSA Feb 2025; TRM Labs).
Top 3 hacks share of 2025 service losses: 69% (Chainalysis 2026 CCR).
Average loss per incident, 2025 (CertiK): US$5.32M, up 66.6% YoY (CertiK Hack3d 2025 Annual).
H1 2025 wallet compromise losses (CertiK): US$1.7B across 34 incidents (CertiK Q2 + H1 2025 Hack3d).
H1 2025 phishing losses (CertiK): US$410M across 132 incidents (same).
Recovery rate, Q1 2025 (Immunefi): 0.4% of stolen funds recovered, vs 21.2% in Q1 2024 (Immunefi via Decrypt).
US cryptocurrency-related fraud losses, 2025 (FBI IC3): US$11.366B across 181,565 complaints, +22% YoY (FBI IC3 2025 Internet Crime Report).
Total illicit crypto received, 2025 (Chainalysis): US$154B, +162% YoY, of which 84% rode stablecoins (Chainalysis 2026 CCR Introduction).
Key takeaways
One nation-state actor and one exchange dominate the year. The DPRK-linked theft of US$2.02 billion is approximately 60% of Chainalysis's full-year 2025 stolen-funds total. The single Bybit incident is roughly 44% of the same total, and the top three hacks together account for 69% of service-side losses. 2025 was not a year of broad-based attack-volume growth; it was a year of two or three catastrophic events that bent the curve.
The threat surface migrated from smart contracts to operators. Halborn, Trail of Bits, and TRM Labs all converged on the same conclusion: top-tier adversaries now compromise signing infrastructure, key custody, and exchange operator workflow rather than hunting for novel logic errors in DeFi protocols. The Bybit Safe Wallet UI exploit, the Phemex hot-wallet private-key theft, the BtcTurk hot-wallet drain, and the UPCX malicious smart-contract upgrade after an account compromise are all infrastructure attacks dressed up as on-chain events.
Recovery rates collapsed in 2025. Immunefi's 0.4% recovery in Q1 2025 against 21.2% in Q1 2024 is a 50x worsening. PeckShield's annual recovered total of US$334.9M in 2025 is below 2024's US$488.5M despite a higher absolute loss number. Funds laundered through the so-called "Chinese laundromat" OTC networks and chain-hopping pathways increasingly do not return.
Audits are necessary but not sufficient. Audited DeFi protocols including Cetus, Balancer V2, Cork Protocol, and GMX V1 still suffered nine-figure losses in 2025. The Cetus integer-overflow flaw and the Balancer V2 rounding error in
_upscaleArrayboth passed prior reviews. The DeFi-specific audit budget (US$25,000 to US$200,000 in 2025 per Zealynx Security's 2025 reference) is a small fraction of what attackers extract from a successful exploit; the spend-versus-loss ratio is asymmetric in the attacker's favor by orders of magnitude.Crypto-related fraud against US consumers is now the dominant economic-loss line in IC3's reporting. The FBI's 2025 Internet Crime Report logged US$11.366 billion in crypto-related fraud, dominated by US$7.228 billion in pig-butchering investment fraud, with US$4.4 billion of total losses concentrated on victims aged 60+. Operation Level Up notified 3,780 victims and prevented an estimated US$225.8 million in losses. The boundary between "crypto hacking" and "crypto-enabled fraud" is operationally blurry and statistically fuzzy.
Methodology
Sources used: Chainalysis (2026 Crypto Crime Report Introduction, Stolen Funds 2026 update, Mid-Year 2025 Update, Stolen Funds 2025 retrospective, Scams 2026); Elliptic (Bybit hack analysis, Cetus Protocol attack analysis, WazirX breach); TRM Labs (2026 Crypto Crime Report, Bybit follow-up, FBI IC3 analysis); CertiK (Hack3d 2025 Annual Skynet Report, Q2 + H1 2025 quarterly report, Q1 2025 quarterly report, 2024 Annual report); Immunefi (Crypto Losses Q1 2025 via Decrypt, Cryptopolitan summary, Research page); PeckShield (2025 annual aggregator, monthly summaries via PeckShieldAlert on X); SlowMist (2025 Annual Blockchain Security and AML Report); Halborn (Year in Review 2025, Top 100 DeFi Hacks Report 2025, monthly DeFi hack reviews); FBI IC3 (2024 Internet Crime Report, 2025 Internet Crime Report, North Korea Bybit PSA, Operation Level Up program); NCC Group (Bybit technical analysis); Trail of Bits (Balancer post-mortem); the Wilson Center and CSIS for policy context; and named corporate disclosures from Bybit, Coinbase (Standing Up to Extortionists, SEC 8-K filing), Mantra Chain, and the protocols affected by named exploits.
Date cutoff: April 25, 2026. We lead with full-year 2025 telemetry where a primary publisher has released it and label any 2026 figure explicitly as a forecast or projection. Statistics that could not be reached via a named primary source on at least one verification pass were dropped rather than estimated. Secondary news aggregators and vendor blogs that restate other publishers' numbers without adding methodology are cited only where they constitute the public record of a corporate incident (Bybit FBI PSA, Coinbase SEC 8-K, Operation Level Up).
Currency convention: figures cited in USD where the primary publisher publishes USD; on-chain conversion rates use the publishers' reported figures at the time of the incident.
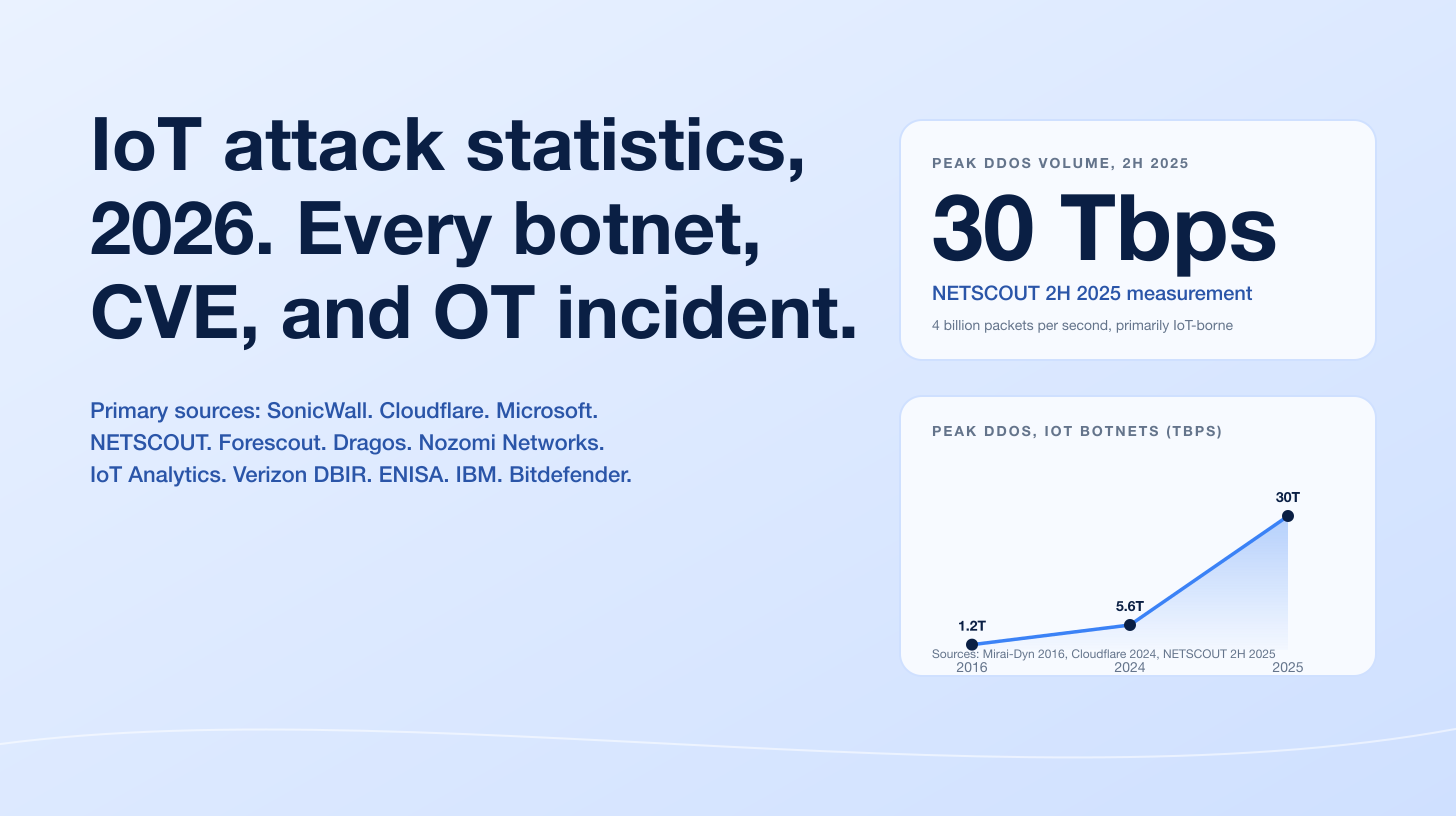
Figure 1: Annual stolen funds tracked by Chainalysis, 2020 to 2025. Sources: Chainalysis Crypto Crime Reports 2021 to 2026. The 2025 figure (US$3.4B) covers January through early December 2025 and may revise upward as more activity is identified.
How big is the crypto hacking problem in 2026?
Four publishers, four totals. Each frame answers a slightly different question, and that is the point.
Chainalysis: US$3.4B stolen, 2025
Chainalysis recorded US$3.4 billion in cryptocurrency theft from January through early December 2025. The scope is "stolen from cryptocurrency services" plus a sampled expansion to capture personal-wallet compromise activity that the on-chain telemetry can attribute. Within the 2025 number:
Centralized services accounted for 88% of Q1 2025 losses.
Personal-wallet compromises added US$713 million, down from US$1.5 billion in 2024 in absolute terms even though the number of personal-wallet incidents surged to 158,000 affecting 80,000 unique victims.
DeFi hacks remained suppressed in 2025 despite increased Total Value Locked, a reversal of the 2021–2023 pattern in which DeFi dominated the loss column.
The top three hacks accounted for 69% of all service-side losses.
Chainalysis's mid-year 2025 update had already flagged that 2025 reached US$2.17 billion in stolen funds by end of June, exceeding the entire 2024 total in 142 days, compared to 214 days in 2022 (the prior worst year).
PeckShield: US$4.04B stolen, 2025
PeckShield's 2025 annual aggregator, built from the firm's monthly threat-monitoring summaries (PeckShield Alert posts on X are the primary source of record), totals US$4.04 billion in 2025 cryptocurrency loss versus US$3.01 billion in 2024, a +34.2% YoY rise. The wider scope reflects PeckShield's bundling of direct hacks (US$2.67 billion, +24.2% YoY) with scams and frauds (US$1.37 billion, +64.2% YoY).
PeckShield also reported funds-recovered totals of US$334.9 million in 2025 versus US$488.5 million in 2024, indicating that recovery efforts declined in absolute terms even as losses grew. Average loss per exploit hit US$7.18 million in H1 2025, more than twice the H1 2024 average of US$3.1 million.
CertiK: US$3.35B stolen, 2025
CertiK's 2025 Skynet Hack3d annual report (released December 24, 2025) totals US$3,352,850,816 across blockchain security incidents in 2025, up from US$2,446,285,251 in 2024 (+37.06% YoY). The number of incidents declined by 137 versus 2024, but the average loss per incident jumped to US$5.32 million, up 66.6% YoY. CertiK's framing for the year was "fewer attacks, larger heists." The single Bybit event is recorded by CertiK at US$1,447,063,421 and accounts for a disproportionate share of annual losses.
SlowMist: US$2.94B stolen, 2025
SlowMist's 2025 Blockchain Security and AML Annual Report tracks ~200 security incidents in 2025 totaling US$2.935 billion, +46% YoY despite a sharp drop in incident count from 410 in 2024. The narrower scope reflects SlowMist's incident-by-incident verification standard. Within SlowMist's tally:
Centralized platforms: 22 incidents, US$1.809 billion (Bybit alone US$1.46 billion).
DeFi protocols: 126 incidents (63% of all reported cases), US$649 million combined.
Smart contract exploits: 56 incidents.
Account compromises: 50 cases.
Ethereum-side losses: US$254 million; BSC US$21.93 million; Solana US$17.45 million.
Reconciling the four numbers
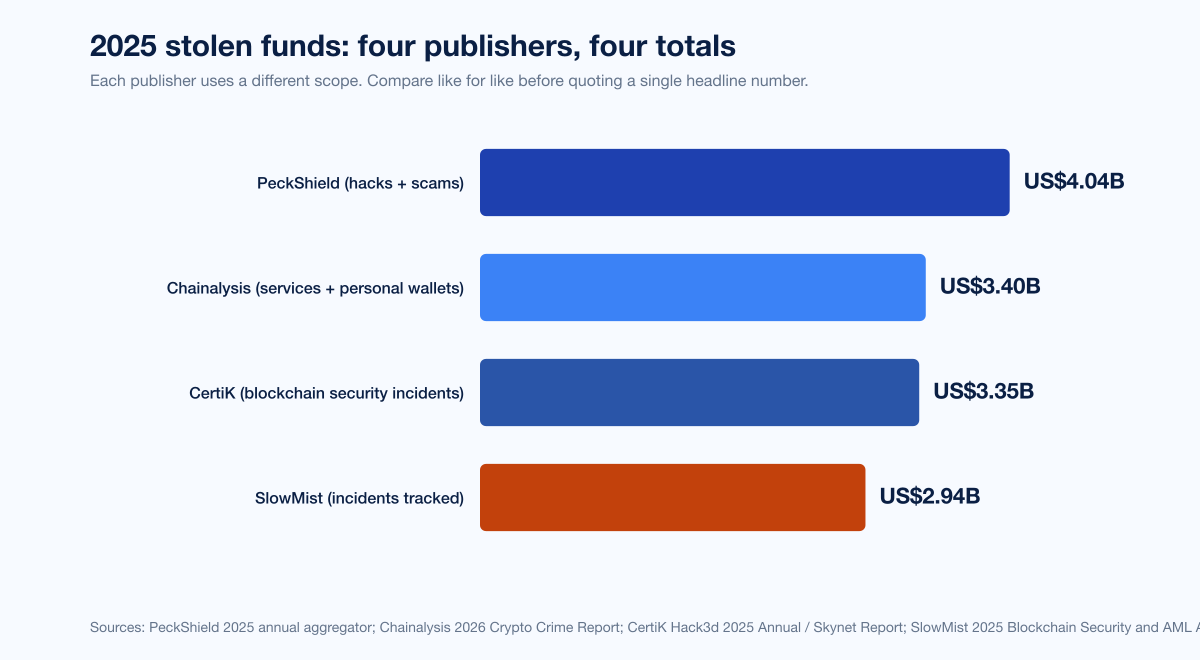
Figure 2: Reported 2025 stolen-funds totals by primary publisher. Sources: PeckShield 2025 annual; Chainalysis 2026 Crypto Crime Report; CertiK Hack3d 2025 Annual Skynet Report; SlowMist 2025 Annual Blockchain Security and AML Report.
Publisher | 2025 total | Scope | Source |
|---|---|---|---|
PeckShield | US$4.04B | Direct hacks + scams/frauds | PeckShield 2025 annual aggregator |
Chainalysis | US$3.4B | Service compromises + sampled personal wallets | Chainalysis 2026 CCR |
CertiK | US$3.35B | Blockchain security incidents | CertiK Hack3d 2025 Annual Skynet Report |
SlowMist | US$2.935B | Verified hacks (narrower incident-by-incident gate) | SlowMist 2025 Annual Blockchain Security and AML Report |
Use the publisher whose scope matches your audience. CISOs and exchange operators typically anchor on Chainalysis or CertiK; DeFi-protocol investors and DAOs typically anchor on Immunefi quarterly plus CertiK. Treasury, FinCEN, and OFAC analysts anchor on TRM Labs and Chainalysis.
North Korea, Lazarus, and TraderTraitor: the dominant threat
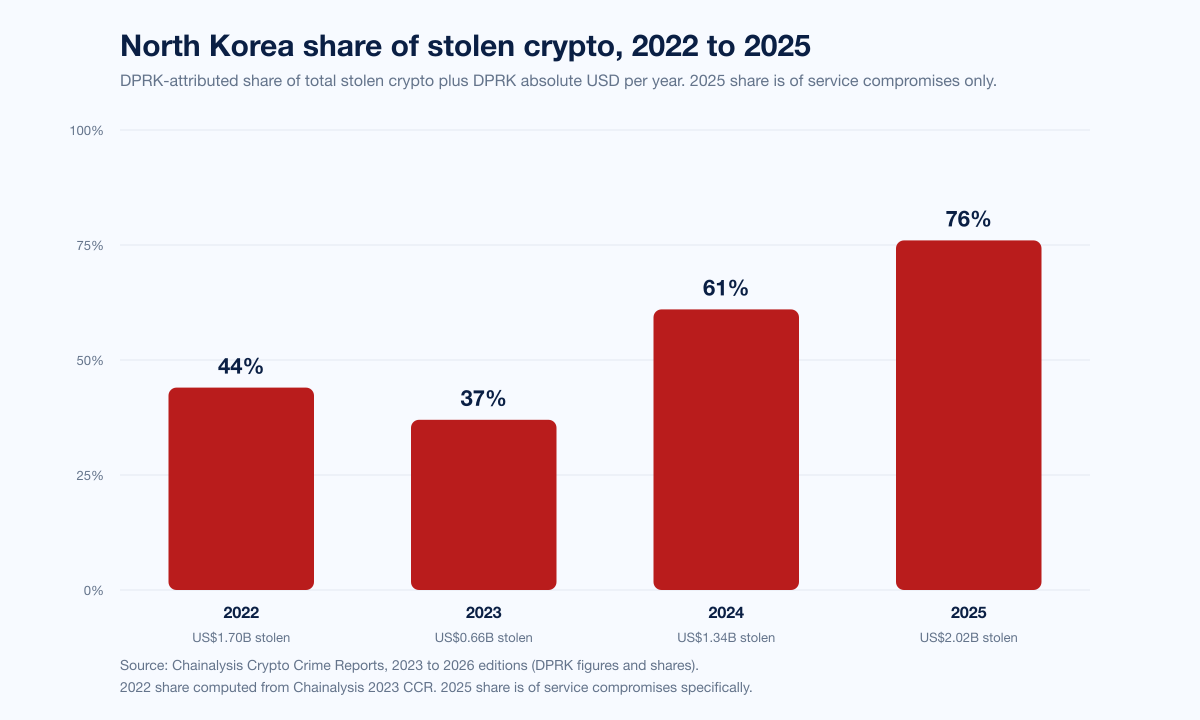
Figure 3: DPRK-attributed share of total stolen crypto, 2022 to 2025. The 2025 figure is share of service compromises specifically. Source: Chainalysis 2026 Crypto Crime Report.
Chainalysis attributes US$2.02 billion to North Korea-linked actors in 2025, a 51% YoY increase that pushed their all-time cumulative theft to US$6.75 billion. The DPRK share of all 2025 service compromises hit 76%, the highest figure on record despite "74% fewer known attacks" than the prior reporting methodology. TRM Labs's 2026 Crypto Crime Report reports a closely-matching independent figure of US$1.92 billion attributable to DPRK-linked actors in 2025, with the top five events of the year accounting for 70% of all stolen crypto value (Bybit alone is 78% of TRM's DPRK figure for 2025).
Year-by-year DPRK trajectory
Year | DPRK stolen (USD) | Share of total stolen | Source |
|---|---|---|---|
2022 | ~US$1.7B | 44% | Chainalysis 2026 CCR |
2023 | US$0.66B | ~37% | Chainalysis 2025 CCR |
2024 | US$1.34B | 61% | Chainalysis 2025 CCR |
2025 | US$2.02B | 76% (services) | Chainalysis 2026 CCR |
How DPRK actors are operating in 2025
The threat profile changed in 2025 in four observable ways, documented across Chainalysis, TRM Labs, and Mandiant reporting.
Operator infiltration over smart-contract hunting. TRM Labs's framing is direct: "for top-tier adversaries, the highest ROI increasingly lies in compromising operational infrastructure (keys, signers, wallet orchestration) at centralized entities instead of discovering novel logic errors in smart contracts." The Bybit attack hit Safe Wallet's transaction-signing UI; the Phemex attack stole hot-wallet keys; the BtcTurk attack drained hot wallets across seven networks. None required a novel logic flaw on-chain.
DPRK IT-worker schemes inside Web3 firms. The UN Panel of Experts estimates 3,000 to 7,000 DPRK IT operatives operating globally with annual revenue from IT-worker fraud at US$250 to US$600 million. North Korean operatives have evolved from simply applying for remote jobs at crypto firms to orchestrating elaborate fake hiring processes, posing as recruiters for Web3 and AI companies to harvest credentials, source code, and VPN access.
"Chinese laundromat" laundering networks. TRM Labs documents that DPRK operators increasingly route stolen assets through professionalized OTC brokers using chain-hopping and asset fragmentation. Recovery via traditional means becomes structurally harder.
Layered AI-assisted impersonation. Chainalysis's Scams 2026 report records government-impersonation scams (officials, regulators, customer-support agents) growing 1,400% YoY and AI-enabled scams generating 4.5x revenue per operation versus non-AI scams (US$3.2M vs US$719,000 average revenue per operation). DPRK actors use the same toolset for executive impersonation in pre-incident reconnaissance.
OFAC has moved in step. Treasury continues to expand DPRK-affiliated wallet designations and sanction Tornado Cash mixer addresses; sanctioned-entity activity grew 694% YoY in 2025 per Chainalysis, driven by DPRK and Russia-linked flows.
The top 10 cryptocurrency hacks of 2025
Aggregate statistics matter, but every CISO budget defense on this topic relies on named, dated incidents. Here are the ten largest publicly documented crypto hacks of 2025, ranked by USD loss at the time of incident.
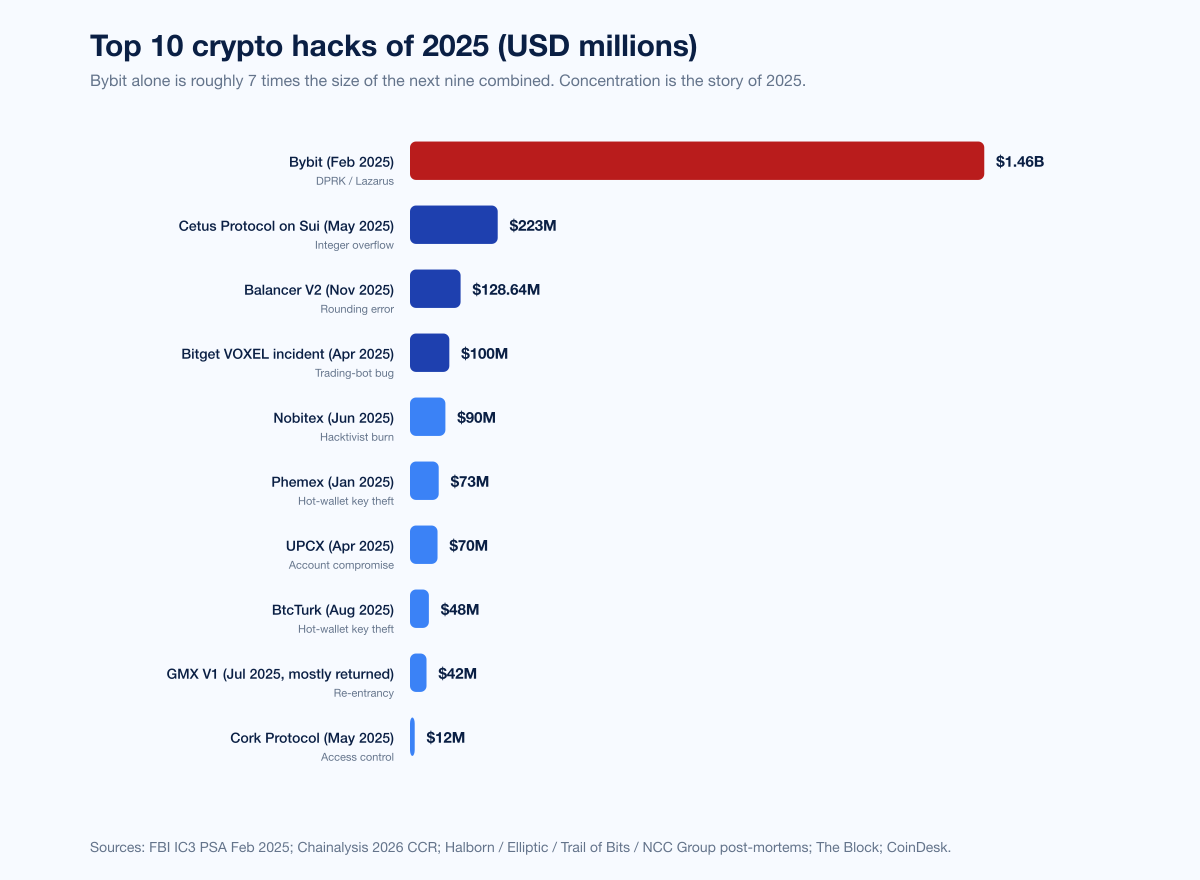
Figure 4: The ten largest publicly documented cryptocurrency hacks of 2025, ranked by USD loss. Sources: FBI IC3 PSA Feb 2025; Chainalysis 2026 CCR; Halborn 2025 Year in Review; Elliptic blog; Trail of Bits Balancer analysis; The Block; CoinDesk.
# | Project | Date | Loss (USD) | Attack class | Attribution | Source |
|---|---|---|---|---|---|---|
1 | Bybit | Feb 21, 2025 | US$1.46B | Signing-infra UI compromise | DPRK / Lazarus / TraderTraitor | |
2 | Cetus Protocol (Sui) | May 22, 2025 | US$223M | Integer overflow in u256 fixed-point math | Unattributed | |
3 | Balancer V2 | Nov 3, 2025 | US$128.64M | Rounding error in | Unattributed | |
4 | Bitget VOXEL | Apr 20, 2025 | ~US$100M (refunded) | Trading-bot logic flaw | Trader exploitation | |
5 | Nobitex | Jun 18, 2025 | >US$90M | Wallet compromise + symbolic burn | Predatory Sparrow / Gonjeshke Darande | |
6 | Phemex | Jan 23, 2025 | ~US$73M (estimates US$29M to US$85M) | Hot-wallet private-key theft | Lazarus-linked per public reporting | |
7 | UPCX | Apr 2025 | US$70M | Compromised account → malicious contract upgrade | Unattributed | |
8 | BtcTurk | Aug 14, 2025 | US$48M | Hot-wallet drain across 7 networks | Unattributed | |
9 | GMX V1 | Jul 9, 2025 | US$42M (US$40.5M returned) | Re-entrancy in GLP price calc | White-hat negotiation | |
10 | Cork Protocol | May 28, 2025 | US$12M (3,761 wstETH) | Faulty access control / input sanitization | Unattributed |
Bybit (Feb 21, 2025): the US$1.46B Safe Wallet UI compromise
The Bybit hack is the canonical 2025 case study and the largest single digital-asset heist on record. The FBI's February 26, 2025 PSA attributed the theft to "TraderTraitor," the FBI's preferred label for the Lazarus Group cluster. Approximately 401,000 ETH (US$1.46 billion at the time of incident, US$1.5 billion under Chainalysis's accounting) were drained from a Bybit cold wallet via a sophisticated supply-chain compromise of the Safe Wallet UI used to approve and sign transfers. As described in NCC Group's technical analysis, Bybit signers saw what appeared to be a routine transfer in the UI; the underlying transaction had been silently rewritten to redirect funds to attacker-controlled addresses. The attack worked because the UI itself, not the on-chain logic, was the trust anchor.
Bybit publicly acknowledged the loss and immediately issued a recovery bounty. As of early 2026, the bulk of the funds remain in DPRK-controlled or DPRK-laundered addresses; some have been frozen by exchange and stablecoin issuer cooperation, but the recovery share is well below 5% per Wilson Center and CSIS policy summaries.
Cetus Protocol (May 22, 2025): US$223M from one missed overflow check
Cetus Protocol, the largest concentrated-liquidity DEX on the Sui network, was drained of approximately US$223 million on May 22, 2025. The attacker exploited an integer-overflow flaw in the checked_shlw shift-left scaling step inside Cetus's u256 fixed-point math library, which corrupted the add-liquidity token-delta calculation and let the attacker make a deposited token "look like" millions of dollars in value. Approximately US$60 million was bridged to Ethereum before Sui validators voted to freeze the remaining US$162 million; on May 29, 2025 those frozen assets were transferred to a Cetus-managed multisig and the protocol began user reimbursement.
Balancer V2 (November 3, 2025): US$128.64M from a rounding error
The Balancer V2 ComposableStablePool exploit on November 3, 2025 drained approximately US$128.64 million across six chains in under 30 minutes. Trail of Bits attributed the failure to a rounding-error vulnerability in the _upscaleArray function which, combined with carefully crafted batchSwap operations, allowed the attacker to artificially suppress Balancer Pool Token (BPT) prices and extract value through repeated arbitrage cycles. The composability of Balancer V2 pools meant multiple downstream projects were affected simultaneously. Balancer recovered approximately US$19.3 million within hours through community and white-hat assistance.
Other notable 2025 incidents
Bitget VOXEL (April 20, 2025). Not a traditional intrusion. Bitget's market-making bot misbehaved in the VOXEL/USDT perpetual market, allowing traders to extract approximately US$100 million in two hours. Bitget rolled back trades and compensated affected users. Included on this list because the event made The Block's, Cointelegraph's, and Bitget's own incident summaries; treat it as an exchange-side operational failure rather than a security exploit.
Phemex (January 23, 2025). US$29 million to US$85 million (final estimates ~US$73 million) drained from hot wallets across 16 blockchains via private-key compromise.
UPCX (April 2025). US$70 million in UPC tokens drained after attackers gained control of a UPCX management account and pushed a malicious smart-contract upgrade, exceeding the platform's circulating supply.
BtcTurk (August 14, 2025). US$48 million in hot-wallet outflows across ETH, AVAX, ARB, BASE, OP, MANTLE and MATIC networks. BtcTurk's second major incident in 14 months; the prior June 2024 breach cost the exchange roughly US$55 million.
Nobitex (June 18, 2025). Iran's largest crypto exchange lost more than US$90 million when the "Predatory Sparrow / Gonjeshke Darande" hacktivist group sent funds to vanity addresses without controlling the corresponding private keys, effectively destroying the assets as a political signal rather than monetizing them. TRM Labs's analysis describes the event as symbolic rather than financially motivated and walks through the leaked Nobitex source code that shipped with the breach.
GMX V1 (July 9, 2025). US$42 million extracted via a re-entrancy flaw in the GLP token price calculation. The attacker returned roughly US$40.5 million under a white-hat agreement and retained a US$5 million bounty.
Cork Protocol (May 28, 2025). US$12 million drained via a flawed-access-control bug that let the attacker create a market in which one market's depeg-swap (DS) token was the redemption asset of another, tricking the contract into releasing assets.
Attack-vector breakdown: where the dollars actually go
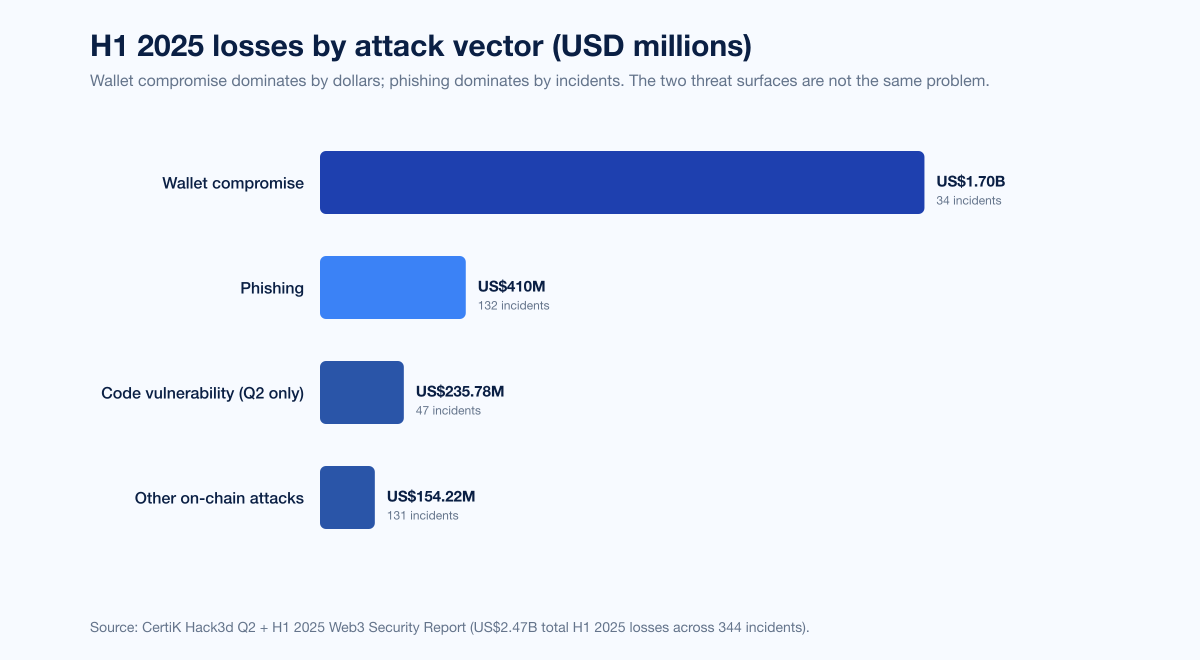
Figure 5: H1 2025 cryptocurrency losses by attack vector. Source: CertiK Q2 + H1 2025 Hack3d Web3 Security Quarterly Report.
CertiK's H1 2025 attack-vector split, covering US$2.47 billion of confirmed losses across 344 incidents, makes a single point starkly: wallet compromise dominates by dollars, phishing dominates by frequency, and the two are not the same threat surface.
Vector | H1 2025 incidents | H1 2025 losses (USD) | Share of H1 losses |
|---|---|---|---|
Wallet compromise (private-key theft) | 34 | >US$1.7B | ~69% |
Phishing | 132 | >US$410M | ~17% |
Code vulnerability (Q2 isolation) | 47 | US$235.78M | ~10% |
Other on-chain | ~131 | ~US$154.22M | ~6% |
Wallet compromise (the dominant dollar line)
Wallet compromise covers signing-key theft, hot-wallet drains, multi-sig manipulation, and any attack that ends with the attacker holding a legitimate signing key or signature. Bybit, Phemex, BtcTurk, and the historical DMM Bitcoin and WazirX hacks (carry-overs from May and July 2024 respectively) all fall in this bucket. The mechanism is operator-side, the loss is exchange-scale, and the recovery rate is structurally lowest because the attacker's authority is indistinguishable from legitimate operator authority on-chain.
Phishing (the dominant incident-frequency line)
Phishing covers wallet-drainer kits, fake project sites, signature-based approval traps, address-poisoning, and AI-personalized social-engineering campaigns aimed at end users. CertiK's 132 H1 2025 phishing incidents extract a smaller average per attack but reach a vastly larger victim population. Chainalysis's personal-wallet data corroborates: 158,000 personal-wallet incidents in 2025 across 80,000 unique victims, with Solana alone accounting for ~26,500 victims.
Wallet drainer ecosystem
The wallet-drainer category is its own subindustry. Group-IB's research and Moonlock's annual review put approximately US$494 million stolen via wallet drainers in 2024 from 332,000 wallet addresses. Inferno Drainer's 2024–2025 relaunch claimed 40 to 45% of the drainer market; Pink Drainer (US$85 million from 21,000 victims through May 2024) shut down its operations in May 2024; Inferno Drainer moved roughly US$180 million from 180,000 victims across its multi-year run per Group-IB historical data cited by Infosecurity Magazine. Drainers operate on a scam-as-a-service revenue-share model: operators ship the kit, affiliates run phishing campaigns, drainer vendors take 20 to 30% of net theft.
Code vulnerability and on-chain logic
The headline DeFi-exploit category. Cetus, Balancer V2, Cork Protocol, GMX V1, and a long tail of smaller incidents hit code-vulnerability bins. The common thread is mathematical or composability bugs in fixed-point arithmetic, oracle pricing, or cross-pool invariants. CertiK's Q2 2025 isolation puts code-vulnerability losses at US$235.78 million across 47 incidents, with average loss per incident of ~US$5 million.
Per-chain breakdown (SlowMist 2025)
Chain | 2025 incident losses |
|---|---|
Ethereum | US$254M |
BSC | US$21.93M |
Solana | US$17.45M |
Ethereum carries the dollar weight because the largest pools and the largest single-event hacks ride mainnet liquidity. SlowMist also notes that Solana saw the highest number of personal-wallet phishing victims in 2025 even though its protocol-level losses remained modest, mirroring Chainalysis's finding that Solana had ~26,500 personal-wallet victims for the year.
Recovery: the asymmetry sharpened in 2025
Crypto-hack recovery rates collapsed in 2025. Three independent measures show the same pattern.
Immunefi Q1 2025 recovery rate: 0.4% of stolen funds recovered (US$6.5 million on US$1.64 billion lost), versus 21.2% recovered in Q1 2024 (Immunefi via Decrypt). Of that US$6.5 million, US$5 million came from 1inch and US$1.5 million from Moby Trade. The 50x decline year over year is structural, not noise.
PeckShield 2025 annual recovery: US$334.9 million returned in 2025 versus US$488.5 million in 2024 (PeckShield 2025 annual aggregator).
Bybit recovery share (TRM Labs / Wilson Center): below 5% as of early 2026, with the bulk of stolen funds laundered through "Chinese laundromat" OTC networks and chain-hopping pathways.
The exception is white-hat-style negotiated returns. GMX V1 recovered US$40.5 million of US$42 million stolen because the attacker accepted a US$5 million bounty in exchange for return. Cetus recovered roughly US$162 million of US$223 million via a Sui-validator governance vote that froze on-chain assets before they could exit to Ethereum. Balancer recovered ~US$19.3 million of US$128.64 million within hours through community-coordinated white-hat assistance. None of these mechanisms work against state-aligned actors who do not need or want a public-facing bounty.
Immunefi reports having paid out US$112 million+ in cumulative bug-bounty rewards and saved an estimated US$25 billion+ in user funds across all white-hat disclosures. The number is meaningful because it suggests that, at scale, paying bounty matters far more than chasing recovery: the average bounty payout (low six figures) prevents an exploit that would, on average, run into eight or nine figures.
Crypto-related fraud and the IC3 record
Hacks are not the only loss vector hitting cryptocurrency holders. The FBI's 2024 Internet Crime Report and the 2025 Internet Crime Report released April 7, 2026 document the consumer side.
Metric | 2024 | 2025 | Change |
|---|---|---|---|
Total cybercrime losses (US, all categories) | US$16.6B | US$20.8–20.9B | +25%+ |
Crypto-related fraud losses | US$9.3B | US$11.366B | +22% |
Crypto-related fraud complaints | ~150,000 | 181,565 | +21% |
Crypto investment fraud (pig butchering) | US$5.8B | US$7.228B | +25% |
Pig-butchering complaints | 41,557 | 61,559 | +48% |
Investment-fraud (all kinds) | US$6.5B+ | US$8.6B | +32% |
BEC losses | US$2.77B | (not isolated in same scope) | – |
Losses to victims aged 60+ | (not isolated) | US$4.4B | – |
Operation Level Up, the FBI's 2024–2025 victim-notification program, contacted 3,780 victims of cryptocurrency investment fraud in 2025; 78% were unaware they were being scammed at the moment of contact. The FBI estimated that the program prevented an additional US$225.8 million in losses.
The line between "crypto hacking" and "crypto-enabled fraud" is fuzzy. Pig-butchering relies on social engineering, not on-chain exploit; deepfake-assisted impersonation of executives is a recon path that ends in either fraud or hack depending on the target; sanctioned-entity flows blur into both buckets. We treat them as separate stat lines but recognize the operational overlap.
The wider illicit-crypto picture (Chainalysis 2026 CCR)
The hacking number is one slice of total illicit cryptocurrency activity. Chainalysis's 2026 CCR Introduction frames the broader market:
Total illicit crypto received, 2025: US$154 billion, +162% YoY (the 2024 estimate was revised upward from US$40.9 billion to US$57.2 billion as more attribution emerged).
Illicit share of total crypto volume: below 1% of attributed transaction volume.
Stablecoin share of illicit transactions: 84%.
Sanctioned-entity activity YoY: +694%.
Russia A7A5 token volume: US$93.3 billion in <1 year.
Iran-proxy wallet volume (confirmed): US$2 billion+.
Total scam revenue 2025 (on-chain + off-chain): US$17 billion (US$14 billion on-chain).
Average crypto-scam payment 2025: US$2,764 (up from US$782 in 2024, +253% YoY).
Government-impersonation deepfake scams growth: +1,400% YoY.
AI vs non-AI scam revenue per operation: US$3.2M vs US$719,000 (4.5x ratio).
AI scams daily revenue median: US$4,838 vs US$518.
E-ZPass scam total: US$1B+ over a 3-year run, more than 1 million victims across 121 countries.
UK Bitcoin seizure (Prince Group case): 61,000 BTC (~£5 billion).
For Stingrai's audience, the relevant takeaway is that hacking is the high-skill, high-concentration wing of a much larger illicit-flow market dominated by stablecoin movement and consumer fraud. The skills to defend an exchange from a Bybit-class signing-infra attack are different from the skills to defend an end user against AI-generated impersonation, but the funding flows, the actor populations, and the laundering networks all overlap.
Smart-contract audit cost: defender-side spend in 2025
For DeFi protocol teams making 2026 budget decisions, the spread on audit cost is wide:
Project tier | 2025 audit cost (USD) | Source |
|---|---|---|
Basic ERC-20 / NFT | US$5,000 to US$15,000 | |
Intermediate (staking, governance) | US$15,000 to US$40,000 | (same) |
DeFi protocol (DEX, lending, yield) | US$40,000 to US$100,000 | (same) |
Enterprise / cross-chain / DAO treasury | US$100,000 to US$250,000+ | (same) |
Compare to the size of a single 2025 hack: US$5 million for a small DeFi exploit, US$100 million for a Balancer-class hit, US$1.46 billion for a Bybit-class incident. The economics favor spending on audit; the constraint is that audits do not catch operator-side compromises (Bybit, Phemex, BtcTurk) and do not always catch math-library bugs (Cetus, Balancer V2). Multi-audit, formal verification, and continuous monitoring with bug-bounty programs are increasingly the default for any protocol moving more than nine figures of TVL.
What this means for defenders
Treat signing infrastructure as the new soft underbelly. Bybit was not a smart-contract failure; it was a UI-layer supply-chain attack against the transaction-approval workflow. Exchanges, custodians, and treasury operators should harden the signing path with hardware-isolated review, transaction-fingerprint validation, and out-of-band approval for transfers above defined thresholds. Stingrai's red team engagements include simulation of operator-side compromise paths against client treasury and custody workflows.
Audit, then audit again, then run a bounty. A US$50,000 audit beats a US$50 million loss; multi-audit + bug-bounty beats single-audit; continuous monitoring beats one-shot review. Immunefi's reported US$25 billion+ saved via white-hat disclosure is the cheapest insurance available to a DeFi protocol.
Move private-key custody off hot wallets. Phemex, BtcTurk, and the long tail of 2025 hot-wallet drains all began with hot-wallet private-key theft. MPC custody, threshold signature schemes, and hardware-key separation between hot and cold tiers are necessary, not optional.
Run social-engineering exercises against treasury, custody, and DevOps teams. DPRK IT-worker infiltration and AI-enabled executive impersonation are reaching production-grade in 2025. Stingrai's social engineering and vishing engagements test wire-approval, credential-reset, and approval-workflow pathways with consent-based simulated attacks against client teams. We also publish related research on phishing statistics, deepfake statistics, and ransomware payouts to help buyers triangulate the threat landscape.
Build for low recovery as the base case. Plan IR playbooks assuming you cannot recover sanctioned-actor flows. Insurance, segregation of operational tiers, and pre-arranged exchange / stablecoin-issuer freeze contacts are what actually move the dial post-incident.
Monitor sanctioned-wallet sets in real time. OFAC publishes DPRK and other designated-actor wallet lists; integrating these into transaction-monitoring stacks lets exchanges and treasuries refuse counterparties before funds move.
Frequently Asked Questions
What is the most-cited cryptocurrency hacking statistic for 2026?
The single most-cited 2026 reference number is US$3.4 billion stolen in 2025 per Chainalysis's 2026 Crypto Crime Report, driven by the US$1.5 billion Bybit incident. PeckShield's wider-scope tally lands at US$4.04 billion (hacks plus scams), and CertiK's blockchain-incident frame lands at US$3.35 billion. For the most defensible single number in a CISO presentation or media interview, cite Chainalysis's US$3.4 billion with the explicit window "January through early December 2025" because the Chainalysis methodology is the most-tracked benchmark across regulators, exchanges, and major media.
How much was stolen in the Bybit hack?
The Bybit hack on February 21, 2025 stole approximately US$1.5 billion (Chainalysis), or US$1.46 billion (Elliptic, TRM Labs, NCC Group), or US$1.4 billion (Halborn). The asset stolen was approximately 401,000 ETH. The FBI attributed the theft to North Korea's TraderTraitor cluster within the Lazarus Group on February 26, 2025. The attack vector was a supply-chain compromise of the Safe Wallet UI used by Bybit signers; the on-chain transaction was silently rewritten so that signers approved a transfer to attacker-controlled addresses while the UI displayed the legitimate destination.
How much cryptocurrency did North Korea steal in 2025?
Chainalysis attributes US$2.02 billion to North Korea-linked actors in 2025, a 51% YoY increase that pushed cumulative DPRK-linked theft to US$6.75 billion. TRM Labs reports a closely-matching independent figure of US$1.92 billion. The DPRK share of all 2025 service compromises hit 76%, the highest share on record; the Bybit incident alone accounts for ~US$1.46 billion of that figure. North Korean actors achieved this dominance with "74% fewer known attacks" than the prior year per Chainalysis, indicating a shift toward fewer, larger, more sophisticated heists.
How has crypto hacking changed year over year?
Crypto theft swung from US$3.7 billion in 2022 (peak DeFi-era) to US$1.8 billion in 2023, to US$2.2 billion in 2024, to US$3.4 billion in 2025 per Chainalysis. Within that swing, the threat profile shifted twice: from DeFi smart-contract bugs (2021–2023) to centralized-exchange operator compromise (2024–2025), and from broad-based theft to extreme concentration at the top (the top 3 hacks were 69% of 2025 service losses). DPRK share rose from ~37% in 2023 to 61% in 2024 to 76% of service compromises in 2025.
Which DeFi protocols were hit hardest in 2025?
By USD loss, Cetus Protocol on Sui (US$223M, integer overflow), Balancer V2 (US$128.64M, rounding error), and Cork Protocol (US$12M, access-control flaw) headline the list per Halborn's 2025 Year in Review and Trail of Bits's Balancer post-mortem. On the centralized side, Phemex, UPCX, BtcTurk, and Nobitex round out the year's largest non-Bybit incidents. SlowMist's annual report puts DeFi-protocol incident count at 126 (63% of all 2025 incidents) with combined losses of US$649 million across DeFi.
How much money is recovered after a cryptocurrency hack?
Recovery rates fell sharply in 2025. Immunefi recorded only 0.4% of Q1 2025 stolen funds recovered (US$6.5M on US$1.64B lost), down from 21.2% in Q1 2024. PeckShield's annual aggregator puts 2025 funds recovered at US$334.9 million versus US$488.5 million in 2024. The exception is negotiated white-hat returns: GMX V1 recovered US$40.5M of US$42M, and Cetus recovered ~US$162M of US$223M via a Sui-validator vote. State-aligned actors who launder through Chinese OTC networks rarely return funds; plan IR with low recovery as the base case.
What is the most common type of crypto hack in 2025?
By USD loss, wallet compromise dominates: 34 incidents and US$1.7 billion in H1 2025 per CertiK's Hack3d Q2 + H1 report. By incident frequency, phishing dominates: 132 incidents and US$410 million in H1 2025. The two are not the same problem. Wallet-compromise attacks target operators (exchanges, custodians, project signers) and produce single-event losses in the tens or hundreds of millions; phishing attacks target end users and produce many smaller losses across a much larger victim base. Defenses are channel-specific.
How much do Americans lose to cryptocurrency-related fraud?
The FBI's IC3 2025 Internet Crime Report (released April 7, 2026) logged US$11.366 billion in cryptocurrency-related fraud losses in 2025, a 22% YoY increase across 181,565 complaints. The largest sub-category was pig-butchering investment fraud at US$7.228 billion (61,559 complaints, +48% YoY). Total US cybercrime losses across all categories hit US$20.8–20.9 billion. Victims aged 60 and older accounted for US$4.4 billion of all losses. The FBI's Operation Level Up notified 3,780 victims and prevented an estimated US$225.8 million in additional losses.
Are smart-contract audits worth it?
Audits do not catch every flaw, but the spend-versus-loss ratio is overwhelmingly in defenders' favor. A DeFi-protocol audit ranges US$25,000 to US$100,000 in 2025 per Zealynx Security and Sherlock's 2026 reference; a single 2025 DeFi exploit ranges US$5 million to US$223 million. Multi-audit, formal verification, and continuous bug-bounty programs (Immunefi, Code4rena) are now the default for any protocol moving nine figures of TVL. Audits do not, however, defend operator-side compromise like the Bybit Safe Wallet UI attack; for that, hardware-isolated signing review and out-of-band approval is the right control, not a code audit.
What is the difference between a crypto hack and a crypto scam?
A hack is unauthorized access to a service, protocol, or wallet that results in funds moving without owner consent (Bybit, Cetus, Balancer V2, Phemex, BtcTurk). A scam is consent-based fraud where the victim authorizes the transfer because they were deceived (pig-butchering investment fraud, romance scams, fake-recovery scams, deepfake-impersonation scams). They land in the same on-chain laundering networks but use different attack surfaces and different defenses. Chainalysis's 2025 stolen-funds number (US$3.4B) covers hacks specifically; its scams number (US$17B total, US$14B on-chain) covers fraud separately. The FBI's IC3 fraud number (US$11.366B in 2025 from US-based victims) is the best gauge of scam losses.
Where can I get the latest cryptocurrency hacking data?
Track the same primary publishers we used: Chainalysis (annual Crypto Crime Report and quarterly mid-year updates), Elliptic (incident-specific analyses), TRM Labs (annual Crypto Crime Report and DPRK-specific updates), CertiK (Hack3d quarterly + annual), Immunefi (quarterly Crypto Losses), PeckShield (monthly summaries on PeckShieldAlert), SlowMist (annual Blockchain Security and AML Report and the SlowMist Hacked archive), Halborn (monthly DeFi hack reviews + annual Top 100 DeFi Hacks Report), and the FBI IC3 Internet Crime Report. The Stingrai research blog mirrors major updates from these publishers as they release; our research and statistics index lists every 2026 reference post we've shipped.
References
Chainalysis. 2026 Crypto Crime Report Introduction. January 2026. https://www.chainalysis.com/blog/2026-crypto-crime-report-introduction/. Topline: US$154B in illicit crypto received in 2025; 84% on stablecoins; sanctioned-entity activity +694% YoY.
Chainalysis. 2025 Crypto Theft Reaches $3.4 Billion (Stolen Funds 2026 update). January 2026. https://www.chainalysis.com/blog/crypto-hacking-stolen-funds-2026/. Lead source for 2025 stolen-funds total.
Chainalysis. 2025 Crypto Crime Mid-Year Update. July 2025. https://www.chainalysis.com/blog/2025-crypto-crime-mid-year-update/. H1 2025 US$2.17B stolen.
Chainalysis. Stolen Funds 2025 retrospective. February 2025. https://www.chainalysis.com/blog/crypto-hacking-stolen-funds-2025/. Full-year 2024 US$2.2B.
Chainalysis. Crypto Scams 2026. January 2026. https://www.chainalysis.com/blog/crypto-scams-2026/. US$17B 2025 scam losses; AI-scam revenue 4.5x non-AI.
Elliptic. The Bybit Hack: Following North Korea's Largest Exploit. February 2025. https://www.elliptic.co/blog/the-bybit-hack-following-north-koreas-largest-exploit. Independent corroboration of Bybit attribution and laundering paths.
Elliptic. Cetus Protocol Hacked for More Than $200 Million. May 2025. https://www.elliptic.co/blog/cetus-protocol-hacked-for-more-than-200-million. Cetus exploit timeline.
TRM Labs. Inside the Nobitex Breach: What the Leaked Source Code Reveals About Iran's Crypto Infrastructure. June 2025. https://www.trmlabs.com/resources/blog/inside-the-nobitex-breach-what-the-leaked-source-code-reveals-about-irans-crypto-infrastructure. Source-code leak and exfiltration timeline.
Elliptic. $235 million Lost by WazirX in North Korea-Linked Breach. July 2024. https://www.elliptic.co/blog/235-million-lost-by-wazirx-in-north-korea-linked-breach. WazirX attribution.
TRM Labs. 2026 Crypto Crime Report: Illicit Crypto Trends and Typologies. January 2026. https://www.trmlabs.com/reports-and-whitepapers/2026-crypto-crime-report. Independent DPRK figure US$1.92B; top-5 events 70% of stolen value.
TRM Labs. The Bybit Hack: Following North Korea's Largest Exploit. February 2025. https://www.trmlabs.com/resources/blog/the-bybit-hack-following-north-koreas-largest-exploit. Bybit operator-side attack analysis.
CertiK. Hack3d 2025 Skynet Annual Report (US$3.35B). December 2025. https://www.globenewswire.com/news-release/2025/12/24/3210329/0/en/CertiK-Releases-2025-Skynet-Hack3D-Report-Showing-3-35-Billion-Stolen-in-Blockchain-Security-Incidents.html.
CertiK. Hack3d Q2 + H1 2025 Web3 Security Quarterly Report. July 2025. https://www.certik.com/resources/blog/hack3d-the-web3-security-quarterly-report-q2-h1-2025. H1 2025 US$2.47B losses across 344 incidents; wallet compromise vs phishing split.
CertiK. Hack3d Q1 2025 Web3 Security Quarterly Report. April 2025. https://www.certik.com/resources/blog/hack3d-the-web3-security-quarterly-report-q1-2025. Q1 2025 quarterly snapshot.
CertiK. Hack3d 2024 Annual Report (US$2.3B). January 2025. https://www.globenewswire.com/news-release/2025/01/02/3003553/0/en/CertiK-s-Hack3d-Report-2-3-Billion-Lost-to-Scams-Hacks-and-Exploits-in-2024.html. Comparative baseline for 2024.
Immunefi. Research and Crypto Losses dashboards. Updated rolling. https://immunefi.com/research/. Quarterly loss + recovery tally.
Decrypt summarizing Immunefi. Crypto Losses of $1.7 Billion from Hacks, Fraud Already Surpass 2024 Total. Q1 2025. https://decrypt.co/317148/crypto-losses-of-1-7-billion-surpass-2024-record-immunefi. Q1 2025 recovery rate 0.4%.
PeckShield 2025 annual aggregator (via BitcoinEthereumNews summary of PeckShield Alert posts). December 2025. https://bitcoinethereumnews.com/crypto/2025-marks-record-breaking-year-for-crypto-losses-as-industry-faces-4-04-billion-security-crisis/. US$4.04B total; US$334.9M recovered.
PeckShieldAlert (X). Monthly threat-monitoring summaries. https://x.com/PeckShieldAlert/status/1984556692496138313. Primary monthly feed.
SlowMist. 2025 Blockchain Security and AML Annual Report. December 2025. https://www.slowmist.com/report/2025-Blockchain-Security-and-AML-Annual-Report(EN).pdf. US$2.935B verified; per-chain breakdown.
Halborn. Year in Review: The Biggest DeFi Hacks of 2025. January 2026. https://www.halborn.com/blog/post/year-in-review-the-biggest-defi-hacks-of-2025. DeFi 2025 retrospective.
Halborn. Top 100 DeFi Hacks Report 2025. 2025 cumulative. https://www.halborn.com/reports/top-100-defi-hacks-2025. Long-tail historical reference.
Halborn. Explained: The Cetus Hack (May 2025). https://www.halborn.com/blog/post/explained-the-cetus-hack-may-2025.
Halborn. Explained: The Balancer Hack (November 2025). https://www.halborn.com/blog/post/explained-the-balancer-hack-november-2025.
Halborn. Explained: The Cork Protocol Hack (May 2025). https://www.halborn.com/blog/post/explained-the-cork-protocol-hack-may-2025.
Halborn. Explained: The GMX Hack (July 2025). https://www.halborn.com/blog/post/explained-the-gmx-hack-july-2025.
Halborn. Explained: The UPCX Hack (April 2025). https://www.halborn.com/blog/post/explained-the-upcx-hack-april-2025.
Halborn. Explained: The BtcTurk Hack (August 2025). https://www.halborn.com/blog/post/explained-the-btcturk-hack-august-2025.
Halborn. Explained: The Phemex Hack (January 2025). https://www.halborn.com/blog/post/explained-the-phemex-hack-january-2025.
Trail of Bits. Balancer Hack Analysis and Guidance for the DeFi Ecosystem. November 2025. https://blog.trailofbits.com/2025/11/07/balancer-hack-analysis-and-guidance-for-the-defi-ecosystem/. Independent rounding-error post-mortem.
NCC Group. In-Depth Technical Analysis of the Bybit Hack. February 2025. https://www.nccgroup.com/research/in-depth-technical-analysis-of-the-bybit-hack/. Safe Wallet UI compromise mechanics.
FBI Internet Crime Complaint Center. North Korea Responsible for $1.5 Billion Bybit Hack (PSA 250226). February 2025. https://www.ic3.gov/psa/2025/psa250226. Federal attribution.
FBI IC3. 2024 Internet Crime Report. April 2025. https://www.ic3.gov/AnnualReport/Reports/2024_IC3Report.pdf. US 2024 cybercrime baseline.
FBI IC3 2025 Internet Crime Report (released April 7, 2026, summarized via KuCoin and ASIS Online). April 2026. https://www.kucoin.com/news/flash/fbi-report-reveals-20-8b-in-2025-cybercrime-losses-crypto-fraud-surpasses-11b. US 2025 cybercrime totals; crypto fraud US$11.366B.
FBI. Operation Level Up. https://www.fbi.gov/how-we-can-help-you/victim-services/national-crimes-and-victim-resources/operation-level-up. Victim notification program.
Bybit (corporate disclosure)._ Public statements and reward fund (Feb 2025 onward). Cited via Wilson Center and CSIS policy summaries.
Coinbase. Standing Up to Extortionists (May 2025 disclosure). https://www.coinbase.com/blog/protecting-our-customers-standing-up-to-extortionists. Public record of the contractor-bribery insider breach affecting ~70,000 customers.
Coinbase. SEC 8-K filing dated May 14, 2025. https://www.sec.gov/Archives/edgar/data/1679788/000167978825000094/coin-20250514.htm. Material-event filing.
Group-IB and Moonlock summaries. Wallet drainer ecosystem. 2024 to 2025. https://www.group-ib.com/resources/knowledge-hub/crypto-wallet-drainers/; https://moonlock.com/wallet-drainer-crypto-theft-2024. Drainer market share and historical totals.
DefiLlama. DeFi Hacks dashboard. https://defillama.com/hacks. Community-aggregated tracker; cross-reference only.
Wilson Center. The Bybit Heist: What Happened and What Now? 2025. https://www.wilsoncenter.org/article/bybit-heist-what-happened-what-now. Policy framing.
CSIS. The ByBit Heist and the Future of U.S. Crypto Regulation. 2025. https://www.csis.org/analysis/bybit-heist-and-future-us-crypto-regulation. Regulatory analysis.
Zealynx Security. Smart Contract Audit Cost in 2025: What You Need to Know. 2025. https://www.zealynx.io/blogs/Smart_Contract_Audit_Cost_in_2025-What_You_Need_to_Know. Audit pricing reference.
Sherlock. Smart Contract Audit Pricing: A Market Reference for 2026. 2026. https://sherlock.xyz/post/smart-contract-audit-pricing-a-market-reference-for-2026. 2026 audit market.
Stingrai is a Toronto and London offensive security firm running penetration testing, red team, and social engineering engagements for global customers. We were founded in 2021. Our team has 18 published CVEs across our researchers, holds OSCE3, OSCP, OSWE, OSED, OSEP, CREST CRT, CISSP, CRTO, GCPN, CRTE, and eWPTX certifications, and presents original research at DEFCON and BSIDES. If you operate a centralized exchange, custody platform, or DeFi protocol and want to test how your signing infrastructure, treasury workflow, or operator paths hold up against the 2025 attack profile documented above, our services page lists what we run and how to start a scoping call.