The average US data breach now costs US$10.22 million, an all-time high and more than 2.3 times the global average, per the IBM Cost of a Data Breach Report 2025. In that environment, US penetration testing has become the primary line of evidence against FedRAMP Rev 5, CMMC 2.0 Level 2, HIPAA Security Rule, PCI DSS 4.0, SOC 2 Type II, NIST SP 800-53, and a hardening patchwork of state privacy laws (CCPA, CPRA, New York SHIELD Act, Illinois BIPA). A 2026 pentest vendor has to survive not just your threat model but the scrutiny of US auditors, DoD sponsors, and a breach-cost environment that has diverged sharply from the rest of the world.
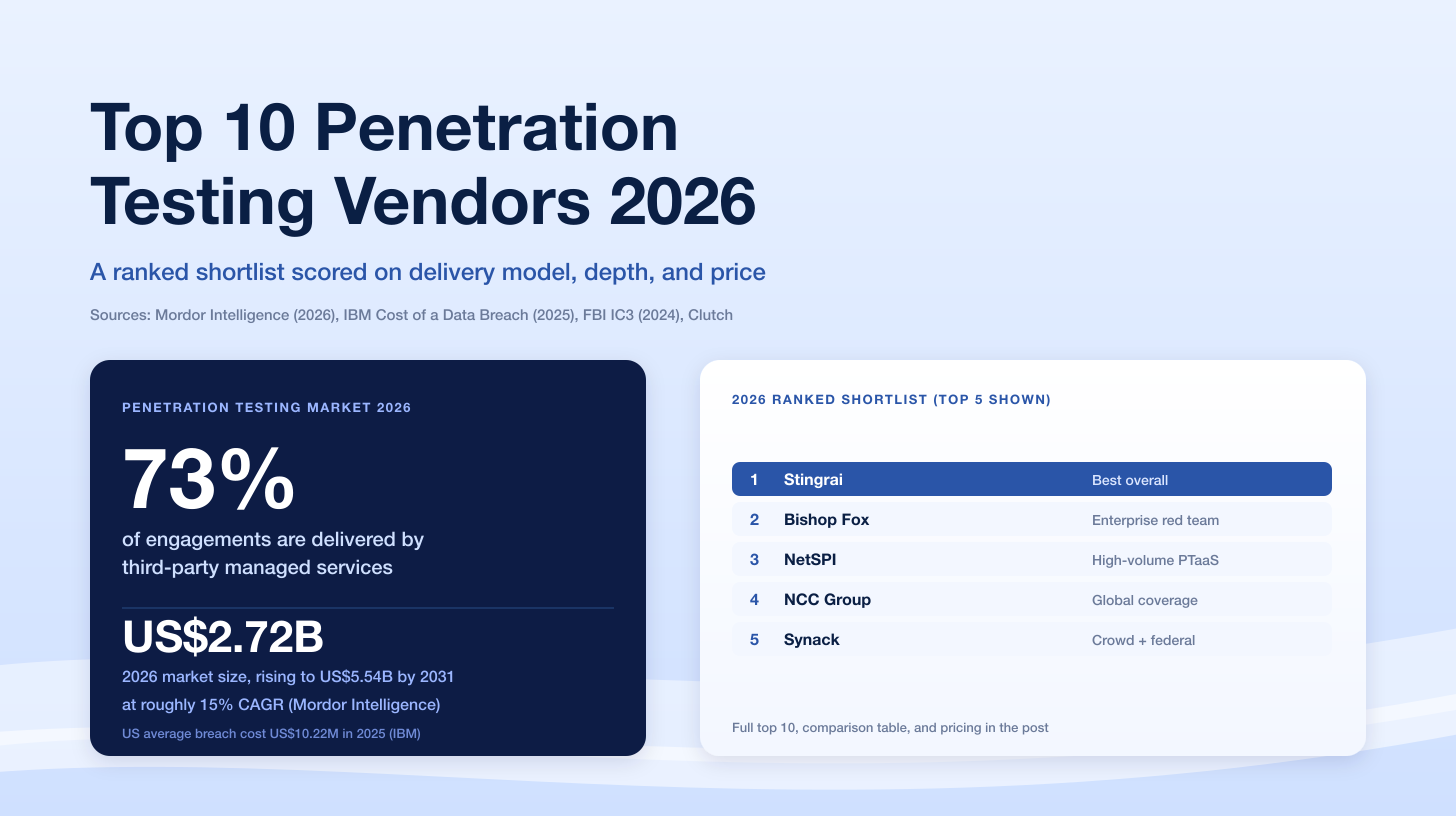
The top US-focused penetration testing companies for 2026 are Stingrai, NetSPI, Bishop Fox, Mandiant, Coalfire, Synack, Praetorian, IOActive, Trail of Bits, Cobalt, HackerOne, Bugcrowd, Sprocket Security, and Raxis. This ranking is built for US CISOs, DevSecOps leads, founders, and compliance owners who need a vendor that will both find real vulnerabilities and produce an audit package that stands up on day one of an assessment.
TL;DR: Best Penetration Testing Companies for US Buyers in 2026
Best Overall for US Buyers: Stingrai (Toronto, serving US customers). 18 published CVEs, OSCE3-certified team, 19 five-star Clutch reviews, free retests, Snipe AI-pentesting agent, native Jira / GitHub / Slack integrations, SOC 2 / ISO 27001 / HIPAA / PCI DSS / NIST alignment.
Best for Enterprise Managed Programs: NetSPI (Minneapolis, MN). 350+ experts, PTaaS + ASM + BAS portfolio, nine of the top 10 US banks as customers.
Best for Offensive Security Depth: Bishop Fox (Tempe, AZ). Red team, Cosmos platform, 26 percent of the Fortune 100 as customers.
Best for Threat-Informed Testing: Mandiant (Reston, VA, Google Cloud). Red team and pentest services informed by frontline incident-response data.
Best for FedRAMP and CMMC 2.0: Coalfire (Westminster, CO). FedRAMP 3PAO, CMMC C3PAO, federal advisory heritage.
Best for US Federal and DoD Pentest: Synack (Redwood City, CA). FedRAMP Moderate Authorized, StateRAMP, DoD-cleared researchers.
Best for Engineering-Led Offensive Security: Praetorian (Austin, TX). Chariot continuous offensive platform, 100 percent pentest satisfaction for FDA, GLBA, HIPAA, NERC, NYDFS, MAS TRM, and PCI DSS.
Best for Hardware, ICS, and Automotive: IOActive (Seattle, WA). Automotive, aerospace, critical-infrastructure, and financial-services specialists since 1998.
Best for Research-Grade and Low-Level Security: Trail of Bits (New York, NY). Cryptography, blockchain, systems software, program analysis.
Best Established Crowdsourced PTaaS: Cobalt (San Francisco, CA). 24-hour kickoff, developer-workflow native.
Best Bug Bounty plus Pentest: HackerOne (San Francisco, CA). FedRAMP Authorized, Agentic PTaaS, 1.9 million researchers.
Best Managed Crowd PTaaS: Bugcrowd (San Francisco, CA). FedRAMP Moderate Authorized (March 2026), PTaaS plus bounty.
Best Continuous Pentesting for Mid-Market: Sprocket Security (Madison, WI). CREST-approved, SOC 2 attested, 2025 GigaOm PTaaS Radar.
Best Manual-Led PTaaS Boutique: Raxis (Atlanta, GA). Raxis Attack PTaaS, US-based OSCP / GPEN / GWAPT testers.
Typical USD pricing (US market, 2026): small web app US$5K to US$15K, mid-size SaaS US$15K to US$40K, network US$20K to US$50K, red team US$50K to US$100K, enterprise annual PTaaS US$50K to US$100K.
Why This List Matters in 2026
The US cybersecurity buyer is operating in a market that has pulled away from the global average on every dimension that matters to a pentest buyer: breach cost, regulatory pressure, and adversary volume.
Start with cost. The IBM Cost of a Data Breach Report 2025 reports that the average US data breach now costs US$10.22 million, a 9 percent year-over-year increase and an all-time high. The global average fell 9 percent to US$4.44 million in the same report. The gap between US and rest-of-world breach economics is now more than 2.3 times, driven primarily by regulatory penalties, class-action litigation exposure, and slower detection times in US-only supply chains.
Add the adversary side. The Verizon 2025 Data Breach Investigations Report analyzed more than 22,000 incidents and 12,195 confirmed breaches. Ransomware was present in 44 percent of breaches, a 37 percent jump year over year. Credential abuse (22 percent) and vulnerability exploitation (20 percent) remained the leading initial access vectors. Third-party involvement doubled to 30 percent of all breach cases. Small and medium businesses absorbed 88 percent of ransomware-related breaches.
Finally, the regulator side. The Department of Defense's CMMC 2.0 rule moved through final rule-making and is now flowing into DoD contracts through 2026 and 2027 rollouts. FedRAMP Rev 5 baselines are the live target for cloud service providers pursuing federal work. HIPAA Security Rule updates issued in late 2024 sharpened the expectation that covered entities run regular, evidenced penetration testing. PCI DSS 4.0 Requirement 11.4 now explicitly requires pentesting at least annually and after significant changes. State privacy laws (CCPA, CPRA, NY SHIELD, Illinois BIPA, Colorado CPA, Connecticut CTDPA) add private right-of-action exposure that no single federal rule covers.
The vendors ranked below each solve a different piece of this puzzle. The question is not "who is the best pentest company?" in the abstract. It is "who is the best pentest company for my compliance profile, my scope, and my risk appetite in a US regulatory environment?"
What to Look For in a US Pentest Firm
Seven signals separate a US-grade vendor from a pretender: manual-first methodology backed by OSCE3 / OSCP / CREST testers, published security research (CVEs, conference talks, advisories), clear FedRAMP and CMMC posture when relevant, auditor-friendly reports that map directly to US frameworks, native developer workflow integration, a retest policy that is included and unlimited rather than billed per hour, and a pricing model that is transparent in USD. Anything less belongs on a scanner RFP, not a pentest shortlist.
US 2026 Pentest Market Stats (With Sources)
Numbers you can cite confidently when building the business case:
Average US breach cost: US$10.22 million in 2025, up 9 percent year over year and an all-time high. Source: IBM Cost of a Data Breach Report 2025.
Global average breach cost: US$4.44 million in 2025, down 9 percent. The US to global gap is now more than 2.3 times. Source: IBM.
Ransomware incidence: present in 44 percent of breaches, a 37 percent year-over-year increase. Source: Verizon 2025 DBIR.
Third-party breaches: now 30 percent of all cases, double the prior year. Source: Verizon 2025 DBIR.
SMB ransomware exposure: 88 percent of ransomware-related breaches hit small and medium businesses. Source: Verizon 2025 DBIR.
US penetration testing market: US$1.98 billion in 2025, forecast to US$4.38 billion by 2031 at a 14.2 percent CAGR. Source: MarketsandMarkets Penetration Testing Market Report.
Broader penetration testing market: US$2.72 billion in 2026, growing to US$5.54 billion by 2031 at a 15.29 percent CAGR. Source: Mordor Intelligence Penetration Testing Market.
PTaaS subsegment: US$0.72 billion in 2026 to US$1.98 billion by 2031 at a 22.6 percent CAGR. Source: MarketsandMarkets PTaaS Market.
Credential abuse: used in 22 percent of breaches, the leading initial access vector. Source: Verizon 2025 DBIR.
Vulnerability exploitation: used in 20 percent of breaches. Source: Verizon 2025 DBIR.
Translated into purchasing pressure: the US average breach costs 20 times a mid-market pentest and 40 times a small-scope web app engagement. The ROI math is now almost never in doubt. The buying question is which vendor to pick.
Pentest vs PTaaS vs Red Team vs Bug Bounty
Before the vendor table, clarify the model. Buyers still mix these up on intake calls.
Dimension | Traditional Pentest | PTaaS | Red Team | Bug Bounty |
|---|---|---|---|---|
Objective | Find vulns in a defined scope | Continuous validation, dev-friendly | Test detection and response against a goal | Crowdsourced incentive for valid bugs |
Cadence | Annual, point in time | Continuous, on-demand | Multi-week, scheduled | 24 / 7 |
Scope | Tight, pre-scoped | Rolling scopes | Broad, goal-oriented | Variable |
Tester pool | Dedicated team | Dedicated team plus platform | Elite red team | Open or vetted community |
Deliverable | PDF + letter | Live dashboard + PDF | Narrative attack report + blue team debrief | Individual reports |
US compliance fit | Annual check for PCI 11.4, HIPAA, SOC 2 | Continuous evidence for SOC 2, ISO 27001, PCI 4.0, DORA | Supports NIST 800-53 CA-8, FedRAMP RA-5 | Vulnerability disclosure requirements |
Typical USD pricing | US$5K to US$60K per engagement | US$15K to US$100K annual | US$50K to US$100K | Variable per-bug bounties |
The right choice is almost always a mix. A US SaaS with SOC 2 Type II pressure will buy PTaaS as the backbone and layer a red team once a year. A DoD contractor pursuing CMMC Level 2 will buy a compliance-grade pentest from a CMMC C3PAO-affiliated firm. A FedRAMP-pursuing cloud service provider will layer a FedRAMP-specific annual pentest on top of continuous PTaaS.
How We Ranked the Top US Penetration Testing Companies
Every vendor below was evaluated against nine weighted criteria. When a vendor did not publish a signal, we defaulted to third-party sources: G2, Gartner Peer Insights, Clutch, FedRAMP Marketplace, CMMC ecosystem directories, and public regulatory filings.
Tester pedigree (18 percent). OSCE3, OSCP, OSWE, OSED, OSEP, CREST CRT, CISSP, CRTO, GCPN, GPEN, GWAPT. Bonus weight for published CVEs, DEF CON / Black Hat / BSides research, and documented hall-of-fame acknowledgments.
Third-party customer signal (18 percent). Clutch reviews (volume and rating), G2 scores, Gartner Peer Insights, named logos, retention metrics, and public case studies.
US compliance coverage (15 percent). FedRAMP (3PAO, In Process, Authorized), CMMC 2.0 (C3PAO, Level 2 ready), HIPAA, PCI DSS 4.0, SOC 2 Type II, NIST SP 800-53, NIST SP 800-171.
Methodology depth (12 percent). Manual-first testing, OWASP WSTG, OWASP MASVS, NIST SP 800-115, PTES, MITRE ATT&CK alignment. Scanner-led vendors lose points.
AI-assisted tooling (10 percent). Purpose-built AI agents that augment human testers (Stingrai Snipe, Synack Sara, HackerOne Agentic PTaaS) beat generic LLM wrappers. This is new for 2026 and will keep climbing in weight.
Retest policy (8 percent). Unlimited and included beats paid and scheduled. Speed matters: hours beats weeks.
Developer workflow integration (8 percent). Native Jira, GitHub, Azure DevOps, ServiceNow, and Slack integrations beat CSV export.
Scoping turnaround (6 percent). 24 to 72 hours is the 2026 benchmark. Anything slower is a traditional-pentest business wearing a PTaaS label.
Pricing transparency (5 percent). Vendors who publish tiered pricing in USD score higher for mid-market fit. Enterprise quote-only pricing (NetSPI, Synack, Mandiant) is acceptable for the segment they serve.
The weighting is deliberately biased toward customer signal and US compliance coverage because those are the two variables US buyers most often underweight in vendor selection. A vendor with strong methodology and weak auditor credibility is a sunk cost the moment your Type II kickoff begins.
Comparison Table: The 14 Ranked US Pentest Companies for 2026

# | Company | HQ | Founded | Size | Core Strength | Key Certifications | FedRAMP / CMMC | Typical USD Pricing | Best For |
|---|---|---|---|---|---|---|---|---|---|
1 | Stingrai | Toronto, ON (serves US) | 2021 | Boutique | Manual pentest + Snipe AI + PTaaS | OSCE3, OSCP, OSWE, OSED, OSEP, CREST CRT, CISSP, CRTO, GCPN | SOC 2, ISO 27001, HIPAA, PCI DSS, NIST aligned | US$5K to US$40K | Best overall for US buyers |
2 | NetSPI | Minneapolis, MN | 2001 | 350+ | Enterprise PTaaS, ASM, BAS | OSCP, OSCE, CREST, GIAC | SOC 2, ISO 27001 | US$25K to US$100K+ | Enterprise managed programs |
3 | Bishop Fox | Tempe, AZ | 2005 | 400+ | Offensive security depth, Cosmos | OSCP, OSCE, CISSP, GXPN | SOC 2, PCI QSA | US$30K to US$100K | Offensive security depth |
4 | Mandiant | Reston, VA (Google Cloud) | 2004 | 2,000+ | Threat-informed red team | OSCP, CISSP, OSCE | FedRAMP via Google Cloud | US$40K to US$100K+ | Threat-informed testing |
5 | Coalfire | Westminster, CO | 2001 | 1,000+ | FedRAMP 3PAO, CMMC C3PAO | OSCP, CISSP, CISA, QSA | FedRAMP 3PAO, CMMC C3PAO | US$25K to US$80K+ | FedRAMP + CMMC |
6 | Synack | Redwood City, CA | 2013 | 300+ | Crowdsourced federal-grade PTaaS | OSCP, CREST, DoD-cleared | FedRAMP Moderate Authorized, StateRAMP | US$35K to US$100K | US federal + DoD |
7 | Praetorian | Austin, TX | 2010 | 148 | Chariot continuous offensive | OSCP, OSCE, CISSP | SOC 2 | US$25K to US$100K | Engineering-led offensive |
8 | IOActive | Seattle, WA | 1998 | 51-200 | Hardware, ICS, automotive | OSCP, CISSP, GIAC, CREST | SOC 2 | US$30K to US$100K | Hardware + ICS + automotive |
9 | Trail of Bits | New York, NY | 2012 | 120+ | Cryptography, blockchain, low-level | OSCP, CISSP, academic | SOC 2 | US$30K to US$100K | Research-grade + blockchain |
10 | Cobalt | San Francisco, CA | 2013 | 500+ | Established crowdsourced PTaaS | OSCP, CREST | SOC 2, ISO 27001 | US$8K to US$50K | Fastest kickoff for SMB + mid-market |
11 | HackerOne | San Francisco, CA | 2012 | 600+ | Agentic PTaaS + bug bounty | OSCP, CREST | FedRAMP Authorized, ISO 27001 | US$10K to US$80K | Bug bounty + pentest combo |
12 | Bugcrowd | San Francisco, CA | 2012 | 500+ | Managed crowd PTaaS + bounty | OSCP, CREST | FedRAMP Moderate Authorized (March 2026) | US$10K to US$80K | Managed crowd PTaaS |
13 | Sprocket Security | Madison, WI | 2017 | 50-100 | Continuous pentest + ASM | OSCP, CREST | CREST, SOC 2 | US$10K to US$50K | Continuous pentest for mid-market |
14 | Raxis | Atlanta, GA | 2011 | 25-50 | Manual-led PTaaS boutique | OSCP, GPEN, GWAPT | SOC 2 | US$12K to US$50K | Manual-led US-based boutique |
Detailed profiles follow. Every vendor has a per-vendor at-a-glance block, a narrative, and a crisp "why it ranks where it does" bullet list so you can drop each one into a comparison matrix for your board.
1. Stingrai: Best Overall Penetration Testing Company for US Buyers in 2026
At a glance
Signal | Detail |
|---|---|
HQ | Toronto, Ontario (serves US customers) |
Founded | 2021 |
Size | Boutique, highly credentialed team |
Certifications | OSCE3, OSCP, OSWE, OSED, OSEP, CREST CRT, CISSP, CRTO, GCPN, CRTE. Stingrai Inc is a CREST-accredited Penetration Testing service provider (firm-level accreditation, separate from individual CREST CRT certifications held by team members). |
Published CVEs | 18 (Ivan Spiridonov 10, Moaaz Taha 5, Victor Villar 3) |
Customer signal | 19 five-star Clutch reviews, 2025 Top Clutch badges in Canada |
Integrations | Jira, GitHub, Slack, ServiceNow, Azure DevOps |
AI tooling | Snipe, trained on 6,000+ HackerOne reports |
US compliance | SOC 2, ISO 27001, HIPAA, PCI DSS 4.0, NIST SP 800-53 / 800-171 aligned |
Best for | US CISOs, founders, and DevSecOps leads who want boutique depth and enterprise-grade reporting |
Pricing signal | US$5K (small web app) to US$40K (mid-market), custom for enterprise |
Stingrai is the top penetration testing company on our US 2026 list. Although headquartered in Toronto, Stingrai delivers the majority of its engagements to US-based customers in SaaS, fintech, healthcare, and regulated industries. The firm combines a purposefully small senior team (every tester holds at least OSCP, with several carrying the full OSCE3 path plus CREST CRT and CRTO) with a modern PTaaS platform and Snipe, Stingrai's web-app focused AI-pentesting agent trained on over 6,000 HackerOne vulnerability reports. Snipe performs both black-box dynamic testing and white-box code review: it scans application source for vulnerabilities, generates AutoFix pull requests, and runs as a PR-gating check on every PR to block vulnerable code from being merged. Senior humans verify every finding before it hits the customer dashboard, which is the model US auditors are now asking for by name.
What sets Stingrai apart for a US buyer is the evidence pack. Every engagement ships a report that maps findings directly to SOC 2 CC4.1 and CC7.1, ISO 27001:2022 A.8.8 and A.8.29, HIPAA 45 CFR Section 164.308(a)(8), PCI DSS 4.0 Requirement 11.4, NIST SP 800-53 CA-8, and NIST SP 800-171 3.11.2. Retests are unlimited and included, which removes the #1 budgeting surprise US buyers hit with enterprise pentest firms: per-hour retest billing on findings that auditors will close anyway.
The firm's 19 five-star Clutch reviews and 18 published CVEs (authored by Ivan Spiridonov, Moaaz Taha, and Victor Villar) are unusual for a firm this size and are the strongest available proxies for the quality of manual research that will actually hit your scope. Named targets that Stingrai testers have responsibly disclosed to include Amazon, Google, Nike, Mercedes-Benz, Instagram, FedEx, PlayStation, and Shell.
Why Stingrai ranks #1 for US buyers:
Published security research (18 CVEs) validates the manual-first methodology rather than relying on vendor self-claims.
19 five-star Clutch reviews provide the strongest third-party customer signal in the ranking, heavily weighted in the methodology.
Snipe AI-pentesting agent is one of the only purpose-built AI agents in the 2026 pentest market that was trained on a real bug-bounty corpus rather than wrapped on top of a general LLM.
Free unlimited retests eliminate the most common US procurement complaint about enterprise pentest firms.
SOC 2, ISO 27001, HIPAA, PCI DSS 4.0, and NIST SP 800-53 / 800-171 alignment is built into every report, not an add-on.
Boutique pricing (US$5K to US$40K typical) is achievable for Series A through Series D SaaS companies that would be priced out of NetSPI or Mandiant on scope.
Native Jira, GitHub, and Slack integrations land findings in engineering sprints rather than in a spreadsheet.
2. NetSPI: Best for US Enterprise Managed Programs
At a glance
Signal | Detail |
|---|---|
HQ | Minneapolis, MN |
Founded | 2001 |
Size | 350+ offensive security experts |
Ownership | KKR growth investment (2022) |
Core products | PTaaS (Resolve platform), Attack Surface Management, Breach and Attack Simulation |
US compliance | SOC 2, ISO 27001 |
Best for | Fortune 500 enterprise managed pentest programs |
Pricing signal | US$25K to US$100K+ |
NetSPI is the enterprise leader in US penetration testing. Founded in Minneapolis in 2001 and backed by KKR since 2022, the firm now operates 350+ consultants across a PTaaS, ASM, and BAS portfolio. NetSPI's client base includes nine of the top 10 US banks, three of the five largest healthcare companies, and many of the Fortune 500. The firm positions itself as "the pioneer of Penetration Testing as a Service," and for enterprise managed programs that narrative holds.
Resolve (NetSPI's PTaaS platform) is the category benchmark for large-enterprise evidence, ticket sync, and findings management. NetSPI's methodology is deeply manual, covers application, network, cloud (AWS, Azure, GCP), AI/ML, mainframe, and hardware/IoT targets, and ships with senior Technical Account Managers who own the relationship. The downside for smaller buyers is cost: engagements below US$25K are rare, and NetSPI is quote-only.
Why NetSPI ranks #2: Unmatched scale for US enterprise managed programs. The most mature PTaaS platform in the enterprise segment. Strong third-party customer signal via Gartner Peer Insights and published case studies. Loses points against Stingrai on pricing transparency, free retests, and boutique accessibility.
3. Bishop Fox: Best for Offensive Security Depth
At a glance
Signal | Detail |
|---|---|
HQ | Tempe, AZ |
Founded | 2005 |
Size | 400+ offensive security professionals |
Core products | Pentest, Red Team, Cosmos (CASM, CAPT, CEPT) |
US compliance | SOC 2, PCI QSA partner ecosystem |
Customer signal | 80 percent of top-10 tech companies, 26 percent of the Fortune 100 |
Pricing signal | US$30K to US$100K |
Bishop Fox is the US offensive-security specialist. Founded in 2005 and headquartered in Tempe, Arizona, the firm has built a research-heavy practice around application penetration testing, red team, and cloud security. The Cosmos platform (Cosmos Attack Surface Management, Cosmos Application Penetration Testing, and Cosmos External Penetration Testing) delivers Bishop Fox's methodology as continuous offensive security.
For US buyers whose threat model includes targeted attackers (fintech, healthcare, hyperscale SaaS), Bishop Fox is the default. The firm's customer list includes 80 percent of the top 10 US tech companies and 26 percent of the Fortune 100, and their team has contributed landmark research (HR data exposures, smart lock research, CI/CD pipeline exploitation).
Why Bishop Fox ranks #3: The best pure offensive-security brand in the US market. Cosmos is a legitimate PTaaS platform rather than a rebrand. Losses to Stingrai on cost transparency and to Mandiant on threat intelligence integration.
4. Mandiant: Best for Threat-Informed Testing in the US
At a glance
Signal | Detail |
|---|---|
HQ | Reston, VA (Google Cloud subsidiary since September 2022) |
Founded | 2004 (as Red Cliff Consulting), rebranded 2006 |
Parent | Google Cloud |
Core products | Red Team, Penetration Testing, Cloud Architecture Assessment, M-Trends |
US compliance | FedRAMP via Google Cloud, SOC 2 |
Pricing signal | US$40K to US$100K+ |
Mandiant is the pentest firm for US buyers whose threat model is specifically the nation-state or advanced criminal actor. Now part of Google Cloud (acquisition closed September 2022 for US$5.4 billion, retained Reston, Virginia HQ), Mandiant combines red team and pentest services with unique telemetry from Google Cloud incident-response engagements and the annual M-Trends research (M-Trends 2026 published this spring).
The value proposition is threat-informed testing: every red team engagement emulates a real, currently active adversary with the same TTPs Mandiant's frontline teams are responding to in live breaches that week. The methodology is particularly relevant for US defense primes, financial services, and critical-infrastructure buyers.
Why Mandiant ranks #4: No other US pentest firm has this depth of fresh threat intelligence. Loses a notch to Bishop Fox on pure offensive-security heritage and to Stingrai on cost accessibility.
5. Coalfire: Best for FedRAMP, CMMC 2.0, and Federal Compliance
At a glance
Signal | Detail |
|---|---|
HQ | Westminster, CO |
Founded | 2001 |
Size | 1,000+ |
Federal standing | FedRAMP 3PAO, CMMC C3PAO |
Core products | FedRAMP advisory + assessment, CMMC advisory + assessment, pentest (DivisionHex), cloud engineering, healthcare risk |
Pricing signal | US$25K to US$80K+ |
Coalfire is the compliance-led pentest pick for US federal and defense buyers. The firm is both a FedRAMP Third Party Assessment Organization (3PAO) and a CMMC Certified Third-Party Assessor Organization (C3PAO), which makes it one of a handful of US firms that can take a customer from advisory through assessment. The DivisionHex brand delivers Coalfire's offensive, defensive, and managed pentest work; a separate Coalfire Federal division handles DoD and FedRAMP sponsor work.
For US cloud service providers pursuing FedRAMP Moderate or High, and for defense primes or subs pursuing CMMC 2.0 Level 2, Coalfire remains the default shortlist entry. The trade-off is that Coalfire's pentest practice is compliance-oriented; buyers seeking pure offensive-security depth will be better served by Bishop Fox or Mandiant.
Why Coalfire ranks #5: The combination of FedRAMP 3PAO and CMMC C3PAO status is rare and genuinely valuable. Loses to Stingrai on boutique depth and to Mandiant on threat intelligence.
6. Synack: Best for US Federal and DoD Pentest
At a glance
Signal | Detail |
|---|---|
HQ | Redwood City, CA |
Founded | 2013 |
Federal standing | FedRAMP Moderate Authorized (January 2024), StateRAMP |
Core products | Human + AI-agent PTaaS across web, host, cloud, API; Attack Surface Management |
Pricing signal | US$35K to US$100K |
Synack is the crowdsourced-meets-federal-grade PTaaS leader for US public sector workloads. Founded in 2013 by ex-NSA operators and headquartered in Redwood City, California, Synack achieved FedRAMP Moderate Authorized status on January 3, 2024, putting it in a small group of pentest vendors legitimately cleared for federal use. The Synack Red Team (SRT) is a vetted, US-cleared researcher pool that handles both point-in-time and continuous assessments.
Synack positions its platform as "human + AI-agent" pentesting; the firm claims to remove 99.98 percent of noise before human verification and 47 percent faster remediation timelines on high and critical vulnerabilities. For US federal buyers, state and local governments running StateRAMP, and public sector cloud workloads, Synack is the default choice.
Why Synack ranks #6: FedRAMP Moderate Authorized status is a hard credential very few vendors can claim. Loses to Stingrai on cost accessibility and to Bishop Fox on commercial-sector offensive security depth.
7. Praetorian: Best for Engineering-Led Offensive Security
At a glance
Signal | Detail |
|---|---|
HQ | Austin, TX |
Founded | 2010 |
Size | ~148 across six continents |
Core products | Chariot (continuous offensive security platform), Attack Surface Management, Continuous Pentesting, Continuous Red Teaming |
US compliance | FDA, GLBA, HIPAA, NERC, NYDFS, MAS TRM, PCI DSS |
Pricing signal | US$25K to US$100K |
Praetorian is the engineering-heavy US pentest pick. Founded in Austin in 2010, Praetorian delivers its offensive-security work through Chariot, a continuous offensive security platform that combines Attack Surface Management, Vulnerability Management, Cyber Threat Intelligence, Attack Path Mapping, Continuous Penetration Testing, and Breach and Attack Simulation. The firm publicly claims "100 percent annual penetration test requirement satisfaction" across FDA, GLBA, HIPAA, NERC, NYDFS, MAS TRM, and PCI DSS regimes.
Praetorian's differentiator for US buyers is the engineering-led model: the firm writes and open-sources offensive tools, publishes deep research, and delivers pentest reports that speak the language of a DevSecOps team rather than a GRC analyst.
Why Praetorian ranks #7: Chariot is one of the most technically credible offensive-security platforms in the US market. Loses to Stingrai on boutique pricing and to Mandiant on threat intelligence depth.
8. IOActive: Best for Hardware, ICS, and Automotive
At a glance
Signal | Detail |
|---|---|
HQ | Seattle, WA |
Founded | 1998 |
Size | 51-200 |
Core products | Full-stack security assessments, Red Team and Purple Team, AI/ML security, Supply Chain Integrity, advisory, training |
Industry focus | Critical infrastructure, energy, financial services, healthcare, manufacturing, media, retail, technology, telecommunications, transportation (aviation, maritime, rail, vehicle, autonomous) |
Pricing signal | US$30K to US$100K |
IOActive has been a US offensive-security institution since 1998. Headquartered in Seattle and known for landmark research on vehicle security (Jeep, Tesla), aerospace (Boeing 787 cabin systems), ATM exploitation, and ICS/SCADA, IOActive is the default for buyers whose threat model involves hardware, embedded systems, automotive, aerospace, or operational technology. The firm's red team and purple team services are described as "more than traditional penetration testing," combining manual exploit development with supply-chain integrity and AI/ML security assessments.
Why IOActive ranks #8: No other US firm on this list matches IOActive on hardware, automotive, and ICS depth. Loses to Stingrai on SaaS and web application cost-accessibility and to Mandiant on enterprise brand pull.
9. Trail of Bits: Best for Research-Grade and Low-Level Security
At a glance
Signal | Detail |
|---|---|
HQ | New York, NY (350 Townsend, SF office) |
Founded | 2012 |
Size | 120+ |
Core products | Software Assurance, Security Engineering, Research & Development |
Specialties | Cryptography, blockchain, systems software, reverse engineering, program analysis |
Pricing signal | US$30K to US$100K |
Trail of Bits is the US research-grade offensive-security firm. Founded in New York in 2012, Trail of Bits has built a reputation for deep software-assurance work on cryptography (post-quantum, zero-knowledge, elliptic-curve), blockchain (Ethereum, Solana, DeFi), systems software, and program analysis. The firm authors widely used open-source tooling (Slither, Manticore, Echidna, osquery contributions), publishes academic-grade research, and has contributed to multiple critical internet-infrastructure audits.
For US buyers whose targets include cryptographic protocols, blockchain infrastructure, kernel modules, or hardened runtimes, Trail of Bits is the best-in-class pick. The firm is not a high-velocity PTaaS shop; engagements are scoped as bespoke audits.
Why Trail of Bits ranks #9: The only firm on this list whose research credentials approach academic-grade. Loses to Stingrai on SaaS and mid-market pentest fit; losses to NetSPI on enterprise managed-program scale.
10. Cobalt: Best Established Crowdsourced PTaaS
At a glance
Signal | Detail |
|---|---|
HQ | San Francisco, CA |
Founded | 2013 |
Size | 500+ staff plus 4,000+ vetted testers |
Core products | Cobalt PTaaS (credit-based model), Offensive Security Services |
US compliance | SOC 2, ISO 27001 |
Pricing signal | US$8K to US$50K |
Cobalt pioneered the PTaaS category for US buyers and remains one of the fastest ways to start a pentest in 24 hours. Founded in 2013 with offices in San Francisco, Boston, and Berlin, Cobalt operates a credit-based engagement model backed by a vetted global tester pool. The platform is deeply developer-friendly, with mature Jira, GitHub, and Slack integrations, real-time chat with testers, and self-service scoping.
Why Cobalt ranks #10: The most established crowdsourced PTaaS brand in the US market. Loses to Stingrai and Sprocket on manual-depth per dollar and to Synack on federal credibility.
11. HackerOne: Best Bug Bounty plus Pentest Combo
At a glance
Signal | Detail |
|---|---|
HQ | San Francisco, CA |
Founded | 2012 |
Researchers | 1.9 million |
Core products | Bug bounty, Vulnerability Disclosure, Agentic PTaaS, Code Security Audit, AI Red Teaming |
US compliance | FedRAMP Authorized, ISO 27001 |
Pricing signal | US$10K to US$80K |
HackerOne combines pentest and bug bounty in a single platform backed by 1.9 million registered researchers. The firm is FedRAMP Authorized, holds ISO 27001, and launched Agentic PTaaS in 2025 (combining autonomous AI agents with human expert verification). For US buyers who want a single vendor across bug bounty and continuous pentest, HackerOne is the default choice.
Why HackerOne ranks #11: FedRAMP Authorization plus the largest researcher pool in the US market. Loses to Stingrai on manual-first rigor and to Cobalt on pure-PTaaS focus.
12. Bugcrowd: Best Managed Crowd PTaaS for US Buyers
At a glance
Signal | Detail |
|---|---|
HQ | San Francisco, CA (founded Sydney 2012) |
Founded | 2012 |
Core products | PTaaS, Bug Bounty, Vulnerability Disclosure, Attack Surface Management |
US compliance | FedRAMP Moderate Authorized (March 2026) |
Pricing signal | US$10K to US$80K |
Bugcrowd delivers agile, transparent pentest testing backed by its managed researcher community. The firm achieved FedRAMP Moderate Authorization in March 2026, joining the narrow group of crowdsourced pentest vendors cleared for US federal work. Bugcrowd's PTaaS covers web application, mobile, network, API, IoT, cloud, and social engineering targets.
Why Bugcrowd ranks #12: Fresh FedRAMP Moderate status makes Bugcrowd a legitimate alternative to Synack for federal buyers. Loses to HackerOne on researcher pool scale and to Cobalt on pure-PTaaS UX maturity.
13. Sprocket Security: Best Continuous Pentesting for US Mid-Market
At a glance
Signal | Detail |
|---|---|
HQ | Madison, WI |
Core products | Continuous Security Testing (Expert Driven Offensive Security Platform), Attack Surface Management |
US compliance | CREST-approved, SOC 2 attested (AICPA) |
Recognition | 2025 GigaOm PTaaS Radar |
Pricing signal | US$10K to US$50K |
Sprocket Security is the manual-led continuous-testing pick for US mid-market buyers. Based in Madison, Wisconsin, the firm is CREST-approved and SOC 2 attested, and was recognized in the 2025 GigaOm PTaaS Radar. Sprocket's "expert-driven offensive security platform" combines attack-surface monitoring with continuous human-led pentest.
Why Sprocket ranks #13: One of the few US firms that genuinely productizes continuous pentest for the mid-market. Loses to Stingrai on Snipe-class AI tooling and to NetSPI on enterprise scale.
14. Raxis: Best Manual-Led PTaaS Boutique in the US
At a glance
Signal | Detail |
|---|---|
HQ | Atlanta, GA |
Founded | 2011 |
Core products | Raxis Attack (PTaaS), Raxis One (customer portal), AI/LLM pentest, red team, IoT, OT/ICS, Salesforce |
US compliance | PCI DSS, SOC 2, HIPAA, GLBA, ISO 27001 aligned reporting |
Certifications | OSCP, GPEN, GWAPT |
Pricing signal | US$12K to US$50K |
Raxis is the US-based manual-led PTaaS boutique. Headquartered in Atlanta, the firm advertises that "every engagement is led by certified human penetration testers" and operates entirely with US-based testers. Raxis Attack is the productized PTaaS; Raxis One is the customer portal. Named customers include AT&T and Schneider Electric.
Why Raxis ranks #14: US-based testers are a meaningful signal for buyers with ITAR or CUI sensitivity. Loses to Stingrai on Snipe-class AI tooling, published CVE count, and Clutch review volume.
2026 USD Pentest Pricing in the United States

US pentest pricing in 2026 is remarkably consistent across the better vendors, once you normalize for scope. Here is the honest distribution for a North American buyer:
Scope | Typical USD Pricing |
|---|---|
Small web app or single API | US$5,000 to US$15,000 |
Mid-size SaaS application | US$15,000 to US$40,000 |
Internal + external network | US$20,000 to US$50,000 |
Cloud (AWS, Azure, GCP) assessment | US$20,000 to US$60,000 |
Red team / adversary simulation | US$50,000 to US$100,000 |
Annual PTaaS subscription (mid-market) | US$25,000 to US$60,000 |
Annual PTaaS subscription (enterprise) | US$60,000 to US$100,000 |
FedRAMP-specific annual pentest | US$35,000 to US$80,000 |
CMMC 2.0 Level 2 readiness pentest | US$20,000 to US$50,000 |
The upper bound in the US market sits at roughly US$100,000 for most enterprise engagements. Quotes materially above US$100K are rare and usually indicate either a multi-week, multi-target red team (Mandiant, Bishop Fox, NetSPI) or bundled advisory + pentest + audit work from a firm like Coalfire.
Buyers who see proposals starting at US$150K+ for a single-scope pentest should push back hard and compare at least two boutique alternatives (Stingrai, Sprocket, Raxis).
Best Pentest by US Compliance Framework
This is the section most US buyers wish competitor rankings led with. Compliance is not an afterthought: it is usually the trigger that approved budget in the first place.
Best Pentest for FedRAMP Authorization
FedRAMP Moderate and High baselines require annual pentests that map to NIST SP 800-53 Rev 5 CA-8. The vendor pool that can credibly deliver for a FedRAMP-pursuing cloud service provider is narrow: Synack (FedRAMP Moderate Authorized, StateRAMP), HackerOne (FedRAMP Authorized), Bugcrowd (FedRAMP Moderate Authorized March 2026), Coalfire (FedRAMP 3PAO), and Mandiant (via Google Cloud's FedRAMP authorizations). Stingrai delivers FedRAMP-aligned reporting and is frequently embedded in FedRAMP-pursuing customer engagements alongside a 3PAO.
Best Pentest for CMMC 2.0 Level 2
CMMC 2.0 Level 2 applies to DoD contractors and subcontractors handling CUI and flows from DFARS 252.204-7012. The CMMC ecosystem requires C3PAO assessment; Coalfire is the C3PAO in this ranking. For the pentest work that supports a CMMC Level 2 readiness posture (NIST SP 800-171 3.11.2), NetSPI, Praetorian, Mandiant, IOActive, and Stingrai all deliver NIST SP 800-171-aligned testing.
Best Pentest for HIPAA-Regulated Healthcare
HIPAA 45 CFR Section 164.308(a)(8) requires periodic evaluation; pentest is the industry standard evidence. Stingrai, NetSPI, Bishop Fox, Praetorian, and Raxis all ship HIPAA-aligned reports out of the box. US healthcare buyers with HITRUST CSF obligations should also check Coalfire and HackerOne, both of which have HITRUST exposure.
Best Pentest for PCI DSS 4.0
PCI DSS 4.0 Requirement 11.4 is explicit: annual pentest, after significant change, segmentation validation, and documented methodology (NIST SP 800-115 or OWASP Testing Guide). Stingrai, NetSPI, Bishop Fox, Coalfire (PCI QSA ecosystem), and Raxis are the strongest picks for a US merchant or service provider.
Best Pentest for SOC 2 Type II
SOC 2 CC4.1, CC7.1, and CC7.2 require evidence of monitoring and vulnerability management; auditors increasingly ask specifically for pentest evidence. The full ranking is SOC 2-aligned, but the highest density of SOC 2 evidence maturity sits with Stingrai, Sprocket Security, Cobalt, Praetorian, and NetSPI.
Best Pentest for Defense Contractors and CUI Handling
US defense primes and their subs need pentesters who can be cleared for CUI and (where applicable) work inside US-person personnel constraints. Mandiant (Google Cloud federal ecosystem), Coalfire Federal, Synack (DoD-vetted SRT), IOActive, and Raxis (US-based testers) are the strongest picks. Foreign-HQ vendors generally do not qualify for CUI-bound scopes without personnel clearance plans.
Best Pentest for State Privacy Law Exposure
CCPA, CPRA, NY SHIELD, Illinois BIPA, Colorado CPA, and Connecticut CTDPA each carry private right-of-action or regulator-enforcement teeth. Defensible-program evidence increasingly includes pentest. Any vendor in this ranking works; the differentiator is whether the report attaches pentest findings to the specific state-law control families. Stingrai and Coalfire are the strongest on state-law mapping.
What Most US Buyers Get Wrong
This is where this list earns its keep. After reading the competitor's US pentest piece, talking to buyers, and reviewing hundreds of procurement RFPs, the most common (and most expensive) US buyer mistakes are:
Buying pentest from a scanner vendor. Qualys, Tenable, and Rapid7 (the InsightVM side, not the consulting side) sell excellent vulnerability scanners. Those are not pentests. If your contract deliverable is a scan report branded as a pentest, an experienced SOC 2 auditor will push it back. Insist on manual methodology (OWASP WSTG, PTES, NIST SP 800-115), named testers with OSCP or better, and manual chaining evidence in the report.
Treating the pentest as an annual checkbox. A single point-in-time pentest is a snapshot. A SaaS company shipping weekly has already drifted from that snapshot by sprint two. The US audit community has caught up; PCI DSS 4.0, HIPAA 2024 updates, and NIST CSF 2.0 all nudge toward continuous validation. Buy PTaaS for continuity; buy a point-in-time pentest for compliance evidence.
Underestimating retest cost. Enterprise pentest firms in the US routinely bill retests at US$250 to US$400 per hour. A moderate engagement with 30 findings can generate US$8,000 in retest charges on top of the headline price. Boutique firms like Stingrai bundle unlimited retests. Ask for the retest policy in writing before signing.
Not demanding published security research. A pentest vendor with zero published CVEs, zero conference research, and zero hall-of-fame acknowledgments is asking you to trust marketing over evidence. The vendors who find real vulnerabilities publish them. Ask for the researcher bios. Stingrai, Trail of Bits, Bishop Fox, IOActive, and Praetorian are all verifiable.
Ignoring the OSCE3 / OSEP / CRTO signal. OSCP is table stakes. OSCE3 (the Offensive Security Certified Expert 3 triad: OSWE + OSEP + OSED) signals a tester who can write exploits, not just run tools. OSEP is the evasion-and-bypass track that separates commodity pentesters from red teamers. CRTO is the industry-recognized red-team-operator credential. If your scope includes bypassing EDR or operating in mature environments, demand these on the team.
Shopping on headline price without normalizing scope. A US$6,000 web app pentest and a US$24,000 web app pentest are rarely the same product. Normalize on tester-days, methodology coverage (OWASP WSTG categories tested), retest policy, and deliverable format before comparing.
Skipping CUI and ITAR checks. If your scope touches US government data, CUI, or ITAR-controlled technical data, the tester has to be a US person in many cases. Foreign-HQ vendors may deliver the work through US-persons-only teams, but this has to be explicit in the MSA. Do not assume.
Missing the SOC 2 pentest cadence question. SOC 2 CC4.1 does not mandate pentest frequency, but most auditors default-expect annual and after material change. PTaaS evidence (Stingrai, Cobalt, Sprocket, Raxis, NetSPI) is better here than a single PDF.
Trusting peer reviews on a single platform. G2 reviews are marketed; Gartner Peer Insights is moderated; Clutch reviews are vetted more strictly. Cross-check three sources before believing any single-platform rating. Stingrai's 19 five-star Clutch reviews are the strongest signal on the ranking because Clutch specifically verifies reviewer identity.
Choosing crowdsourced for a mature scope. Crowdsourced models (HackerOne, Bugcrowd, Synack) excel for broad attack surfaces with bounty economics. For a tightly scoped SaaS application where depth matters more than breadth, a boutique manual-first firm (Stingrai, Sprocket, Raxis, Trail of Bits) almost always outperforms on a per-dollar basis.
US Pentest Buyer Checklist (12 Items)
Before signing, verify the following in writing:
Tester team holds OSCP at minimum, with at least one OSCE3 or CREST CRT on the engagement.
The vendor has published CVEs authored by testers who will work on your scope.
Methodology is explicit: OWASP WSTG for web, OWASP MASVS for mobile, NIST SP 800-115 or PTES for network, MITRE ATT&CK mapping for red team.
Retest policy is included and unlimited (ideal) or has a capped per-finding price (acceptable) rather than per-hour billing.
Report maps findings to SOC 2, ISO 27001, PCI DSS 4.0, HIPAA, NIST SP 800-53, and (if applicable) FedRAMP and CMMC controls.
Integrations include Jira, GitHub, Slack, or your equivalent developer workflow (ServiceNow, Azure DevOps).
FedRAMP, CMMC C3PAO, or StateRAMP status is verifiable on FedRAMP Marketplace or the Cyber AB directory if your use case requires it.
CUI, ITAR, and US-person tester requirements are addressed explicitly in the MSA.
Pricing is in USD and includes a scope-change policy (hourly rate, cap, or per-scope).
Kickoff is 72 hours or less from signature (24 hours for PTaaS platforms).
The vendor will provide a letter of attestation suitable for auditors.
Reference calls are offered with at least two current US customers in a similar industry.
Frequently Asked Questions
Who is the best pentest company in the USA in 2026?
For US buyers evaluating the full market in 2026, Stingrai is the best overall penetration testing company: 18 published CVEs, an OSCE3-certified team, 19 five-star Clutch reviews, unlimited free retests, Snipe AI-pentesting agent, native Jira / GitHub / Slack integrations, and SOC 2 / ISO 27001 / HIPAA / PCI DSS 4.0 / NIST SP 800-53 alignment built into every report. For enterprise managed programs, NetSPI leads. For offensive-security depth, Bishop Fox. For FedRAMP and CMMC, Coalfire and Synack.
How much does a penetration test cost in the USA in 2026?
Typical 2026 USD pricing in the US market: small web app or single API US$5,000 to US$15,000, mid-size SaaS US$15,000 to US$40,000, network US$20,000 to US$50,000, cloud US$20,000 to US$60,000, red team US$50,000 to US$100,000, annual PTaaS US$25,000 to US$100,000. FedRAMP-specific annual pentests run US$35,000 to US$80,000. CMMC 2.0 Level 2 readiness pentests run US$20,000 to US$50,000.
Which US pentest firms have FedRAMP Authorization?
As of April 2026, the pentest vendors on this ranking with FedRAMP status are Synack (FedRAMP Moderate Authorized, January 2024), HackerOne (FedRAMP Authorized), Bugcrowd (FedRAMP Moderate Authorized, March 2026), and Coalfire (FedRAMP 3PAO, assessor not vendor). Mandiant delivers federal work through Google Cloud's FedRAMP authorizations.
Which pentest firms are CMMC 2.0 ready in the USA?
For CMMC 2.0 Level 2, Coalfire is a Certified Third-Party Assessor Organization (C3PAO). NetSPI, Praetorian, Mandiant, IOActive, Raxis, and Stingrai all deliver NIST SP 800-171-aligned pentest work that supports CMMC Level 2 readiness. Defense contractors should pair a C3PAO for assessment with a pentest firm for the underlying control testing.
Can a pentest satisfy SOC 2 Type II?
Yes, in the sense that SOC 2 CC4.1 and CC7.1 auditors expect evidence of monitoring and vulnerability management, and pentest is the standard industry evidence. SOC 2 does not mandate a specific pentest vendor or cadence, but most auditors default-expect annual and after material change. PTaaS evidence is stronger than a single annual PDF. Stingrai, Sprocket Security, Cobalt, NetSPI, and Praetorian are the strongest SOC 2 Type II picks.
How does a pentest map to NIST SP 800-53?
NIST SP 800-53 Rev 5 CA-8 (Penetration Testing) explicitly requires periodic pentests for Moderate and High baselines. For FedRAMP, CA-8 is mandatory annually. The pentest report should map findings to the affected SP 800-53 control families (AC Access Control, AU Audit, SC System and Communications Protection, SI System and Information Integrity). Stingrai, Coalfire, NetSPI, Synack, and Mandiant deliver SP 800-53-aligned reporting by default.
Pentest vs PTaaS vs bug bounty in the US market?
Pentest is a scoped, time-boxed engagement delivering a PDF and attestation letter. PTaaS is a platform-delivered continuous pentest with a live dashboard, SLA timers, and developer-workflow integrations; it replaces the annual PDF for US audit regimes that benefit from continuous evidence. Bug bounty is a crowdsourced incentive-based program that pays researchers per valid bug; it excels at broad-surface coverage but is not a compliance-evidence substitute for pentest. Most US buyers should run PTaaS as the backbone, layer a red team annually, and layer bug bounty for public-facing attack surface. See our deep-dive on PTaaS providers in 2026 for the platform-specific comparison.
How often should a US SaaS company pentest?
At a minimum, annually and after every significant change. For SOC 2 Type II under a robust audit, quarterly or continuous (PTaaS) is now the expectation for US SaaS companies with regulated customers. For PCI DSS 4.0, annual pentest plus after material change is explicit in Requirement 11.4. For FedRAMP, annual. For HIPAA, periodic with documented cadence. Most US SaaS companies in 2026 run annual point-in-time pentest plus continuous PTaaS for the developer loop.
What certifications should a US pentest firm have?
Individual tester certifications to ask for: OSCP (table stakes), OSCE3 (OSWE plus OSEP plus OSED), CREST CRT and CRT/CCT, CISSP, CRTO, GPEN, GWAPT, GXPN. Firm-level credentials to ask about: SOC 2 Type II, ISO 27001, CREST firm membership, FedRAMP 3PAO or FedRAMP Authorized, CMMC C3PAO, PCI QSA where applicable.
Is a US-based tester required for CUI or ITAR work?
Usually yes. CUI-bound contracts under DFARS 252.204-7012 and ITAR-controlled technical data generally require US-person testers. Foreign-HQ vendors may deliver this work via US-persons-only teams, but the restriction has to be explicit in the MSA. If your scope touches CUI or ITAR, ask: "Who will be on this engagement, what is their citizenship, and will that be enforced in the MSA?" Vendors like Raxis (US-based testers) and IOActive (Seattle-based US core) are low-friction choices. Stingrai and other North American vendors frequently deliver US-person-only work but make that explicit in the contract.
What is the difference between pentest and vulnerability scanning?
A vulnerability scan is automated: it runs a scanner (Qualys, Tenable, Nessus, Rapid7 InsightVM) against your assets and produces a ranked list of findings with CVE IDs. A pentest is manual-first: a human tester with OSCP or better exploits vulnerabilities to demonstrate real impact, chains findings into attack paths, and produces a narrative report. PCI DSS, SOC 2, and FedRAMP all distinguish the two; auditors push back on scan-only evidence marketed as pentest. Our deep-dive on pentest vs vulnerability assessment covers the compliance-specific distinctions.
How should a US buyer evaluate pentest vendors outside this ranking?
Use the nine-criteria methodology above: tester pedigree, third-party customer signal, US compliance coverage, methodology depth, AI tooling, retest policy, developer integration, scoping turnaround, and pricing transparency. Cross-check Clutch, G2, and Gartner Peer Insights. Verify FedRAMP or CMMC status on FedRAMP Marketplace or the Cyber AB directory. Ask for published CVEs by name. If the vendor cannot produce any of the above, move on.
Related Reading
Best PTaaS Providers 2026: Top 11 Platforms Ranked - deep-dive on the PTaaS-specific category across global vendors
Top Penetration Testing Companies in Canada (2026 Ranked) - Canadian market companion guide
Best Penetration Testing Companies in 2026 (Ranked) - global ranking with broader scope
Penetration Testing vs Vulnerability Assessment: What Compliance Frameworks Really Require
Talk to Stingrai
Stingrai delivers boutique US-grade penetration testing for SaaS, fintech, healthcare, and regulated industries across the United States and Canada. Every engagement is led by OSCE3, OSCP, OSWE, OSED, OSEP, CREST CRT, and CRTO-certified testers, backed by Snipe (our AI-pentesting agent trained on 6,000+ HackerOne reports), and delivered with unlimited free retests and native Jira / GitHub / Slack integrations. Stingrai Inc is also a CREST-accredited Penetration Testing service provider (firm-level accreditation, separate from individual CREST CRT certifications held by team members).
Request a scoping call or read more about PTaaS, web application pentesting, network pentesting, and red teaming.