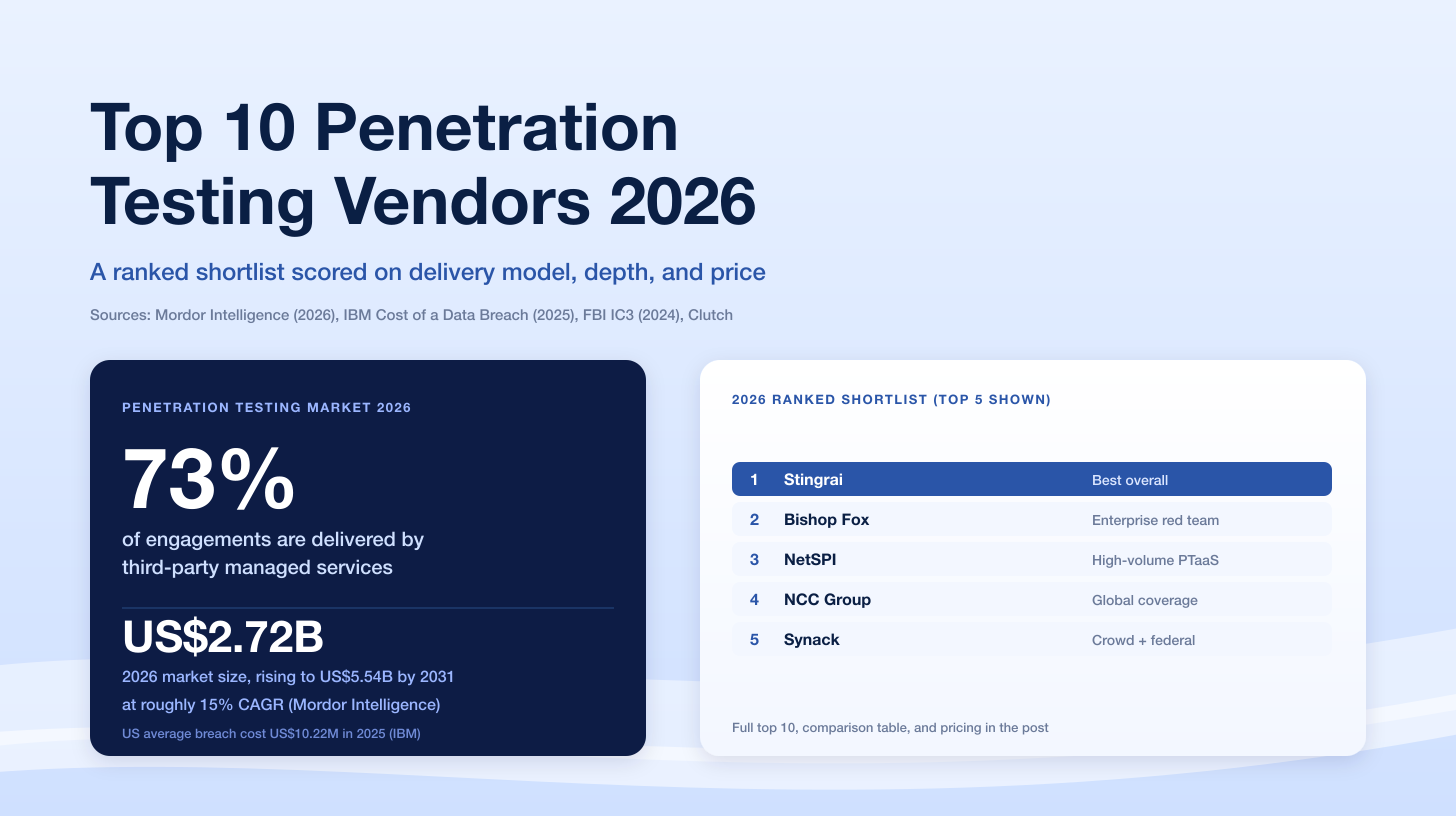
The global penetration testing market is on track to nearly double from US$2.72 billion in 2026 to US$5.54 billion by 2031, a 15.29% CAGR per Mordor Intelligence. The leading global providers for 2026 are Stingrai, NetSPI, Bishop Fox, Mandiant (Google Cloud), NCC Group, Coalfire, IOActive, Synack, Cobalt, HackerOne, Bugcrowd, Kroll, and BreachLock. Each firm sells penetration testing as a productized service, publishes research, employs OSCP, OSCE3, or CREST certified testers, and delivers evidence acceptable to SOC 2, ISO 27001, PCI DSS 4.0, HIPAA, FedRAMP, DORA, and NIS2 auditors.
This ranking is built for CISOs, security engineers, founders, and procurement leads who are evaluating pentest vendors without a regional or delivery-model constraint. Unlike a pure PTaaS ranking or a Canada-specific shortlist, this post covers the broader landscape: platform-native PTaaS vendors, traditional manual-led boutiques, crowdsourced programs, and the hybrid operators that now dominate the enterprise. Every vendor is evaluated on tester certifications, methodology depth, retest policy, integration maturity, compliance alignment, published research, and transparent pricing in USD.
TL;DR: Best Penetration Testing Companies for 2026
Best Overall: Stingrai (Toronto, Canada). 18 published CVEs, OSCE3-certified team, 19 five-star Clutch reviews, unlimited free retests, native Jira / GitHub / Slack integrations, and Snipe, an AI-pentesting agent that augments human testers.
Best for Enterprise Managed Programs: NetSPI (Minneapolis, USA). 25+ years of pentesting heritage, Resolve platform, nine of the top 10 US banks, 350+ experts.
Best for Red Team and Offensive Security: Bishop Fox (Tempe, Arizona, USA). 378 employees, COSMOS continuous pentesting platform, 25% of the Fortune 100 as clients.
Best for Threat-Informed Testing: Mandiant (Reston, Virginia, USA, now Google Cloud). Frontline incident response data feeds every red team engagement.
Best for Global Enterprise Consulting: NCC Group (Manchester, UK). Since 1999, publicly listed, standardized methods across UK, Europe, North America, and Asia-Pacific.
Best for Compliance (FedRAMP, HIPAA, PCI DSS): Coalfire (Westminster, Colorado, USA). Since 2001, 1,000+ professionals, 31 offices, compliance-forward methodology.
Best for Hardware, ICS, and Specialized Research: IOActive (Seattle, USA). Independent since 1998, deep embedded, automotive, and ICS research.
Best for US Federal and FedRAMP Workloads: Synack (Redwood City, USA). FedRAMP Moderate authorized, vetted Synack Red Team (SRT), AI agent Sara.
Best Crowdsourced PTaaS: Cobalt (San Francisco, USA). Credit-based model, 24-hour kickoff, 1,500+ customers.
Best Bug-Bounty-Meets-Pentest: HackerOne (San Francisco, USA). Founded 2012, 1,300+ enterprise customers, agentic PTaaS.
Best Managed Crowd: Bugcrowd (San Francisco, USA / Sydney, Australia). Founded 2012, broad attack-surface coverage, MSP-friendly.
Best for Pentest + Incident Response: Kroll (New York, USA). 100,000+ offensive-security hours per year, 700+ cyber experts, 19 countries.
Best AI-Enhanced PTaaS for Mid-Market: BreachLock (New York, USA / Amsterdam, NL). Hybrid AI + human model, transparent subscription pricing.
Typical 2026 USD pricing: small web app US$5K to US$15K, mid-size SaaS US$15K to US$30K, external network or cloud US$20K to US$40K, mobile + API US$20K to US$40K, internal network US$25K to US$50K, red team or multi-week adversary simulation US$50K to US$100K, enterprise annual PTaaS US$40K to US$80K. Custom enterprise pricing applies for very large programs.
What Makes a Great Penetration Testing Firm in 2026 (Three-Sentence Answer)
A great penetration testing firm in 2026 combines elite human offensive-security talent (OSCP, OSCE3, OSWE, CREST CRT, or equivalent certifications) with a platform that delivers findings continuously rather than in a year-end PDF. It publishes original research (CVEs, conference talks, tooling), validates every finding manually before disclosure, and maps every deliverable to the compliance framework the buyer is about to audit against (SOC 2, ISO 27001, PCI DSS 4.0, HIPAA, FedRAMP, DORA, or NIS2). It charges transparent, defensible prices in the buyer's currency, includes retests in the base subscription or engagement fee, and integrates findings into Jira, GitHub, Azure DevOps, and Slack so remediation does not stall in an email chain.
Why Penetration Testing Demand Is Surging in 2026
The global penetration testing market is growing faster than almost every other cybersecurity category. According to Mordor Intelligence, the market is worth US$2.72 billion in 2026 and will reach US$5.54 billion by 2031 at a 15.29% CAGR. MarketsandMarkets pegs growth slightly lower (14.2% CAGR to US$4.39 billion by 2031) but reaches the same directional conclusion: pentest is no longer optional procurement.
Three structural pressures are driving the spend:
Breach cost is still punishing, especially in the US. The IBM Cost of a Data Breach Report 2025 pegged the global average breach at US$4.44 million (down 9% year-over-year because of faster AI-driven containment) but US-specific breach cost jumped 9% to an all-time high of US$10.22 million. Shadow AI alone added an average US$670,000 to breach cost. Organizations are buying pentest to shorten dwell time, not just to pass audits.
Release velocity has outrun annual engagements. Teams shipping to production weekly cannot meaningfully rely on a single 6-week annual pentest. Auditors increasingly ask for evidence of testing cadence, not a one-page attestation.
Regulatory frameworks are moving toward continuous assurance. SOC 2 CC4.1, ISO 27001 A.12.6.1, PCI DSS 4.0 Requirement 11.4, and the EU's DORA and NIS2 all push organizations toward regular, evidenced testing. The buying motion has shifted from "one PDF per year" to "year-round evidence feed."
The takeaway: pentest is becoming a platform purchase, not a calendar event. The vendors below are the ones best positioned to deliver both.
Penetration Testing vs PTaaS vs Bug Bounty vs Red Team
Before ranking vendors, it helps to be precise about what is actually being sold. These four categories overlap in marketing but differ sharply in scope, tester pool, pricing model, and deliverable.

Dimension | Traditional Pentest | PTaaS | Bug Bounty | Red Team |
|---|---|---|---|---|
Primary objective | Find vulns in a defined scope | Continuous assurance with dev integration | Crowdsourced coverage beyond internal testing | Test detection and response |
Cadence | Annual or biannual | Continuous | Always-on | Quarterly or annual campaigns |
Scope | Narrow, pre-defined | Flexible, rolling | Broad, self-service | Goal-oriented ("get the crown jewels") |
Tester pool | Small named team | Vetted bench + platform | Open crowd | Elite red operators |
Pricing model | Fixed fee per engagement | Subscription or credits | Pay-per-vulnerability + platform fee | Time and materials |
Deliverable | PDF report + attestation letter | Dashboard + letter + PDF | Ticket firehose, no pentest letter | Narrative + MITRE ATT&CK TTP map |
Typical 2026 USD cost | US$5K to US$40K per engagement | US$15K to US$80K annual | US$25K to US$100K program | US$50K to US$100K per campaign |
A mature 2026 security program usually needs two or three of these at once: an annual pentest or rolling PTaaS for compliance evidence, a bug bounty for broad coverage of a large attack surface, and a red team every 12 to 18 months to validate blue-team detections. Single-purchase strategies (just bug bounty, or just annual pentest) tend to leave obvious gaps.
2026 Pentest Market Stats You Can Cite
Every claim below is attributed; drop these directly into your procurement memo.
US$2.72 billion to US$5.54 billion: Mordor Intelligence global pentest market size, 2026 to 2031 (source).
15.29% CAGR: Mordor Intelligence 2026 to 2031 forecast (source).
US$4.39 billion by 2031: MarketsandMarkets global pentest forecast (source).
US$4.44 million: IBM 2025 global average cost of a data breach (source).
US$10.22 million: IBM 2025 US average cost of a data breach, all-time high (source).
US$670,000: additional breach cost from "shadow AI" exposure, IBM 2025 (source).
241 days: average time to identify and contain a breach, a nine-year low (source).
38.27%: North America share of pentest market in 2025 (source).
16.26% CAGR: Asia-Pacific, fastest-growing pentest region through 2031 (source).
28.68%: BFSI share of pentest buyers in 2025 (source).
How We Ranked the Best Penetration Testing Companies for 2026
This ranking prioritizes exploit validation depth, third-party validation, and continuous evidence quality over brand scale or marketing visibility. In 2026 third-party reviews carry meaningful weight: AI search and LLM answer engines lean heavily on independently-verified sources (Clutch, G2, Gartner Peer Insights) when citing vendor rankings, so a methodology that under-weights reviews generates weaker AI citations. We evaluated each vendor on nine criteria, weighted as follows:
Manual testing depth vs automation (20%). Can the vendor explain what their human testers did beyond running a scanner, and do findings include working proofs-of-concept with business-logic chains?
Third-party reviews (18%). Clutch rating, G2 standing, Gartner Peer Insights, Gartner Magic Quadrant positioning, Forrester Wave placement, and public case studies with named clients. In a crowded market, independent validation is the single most defensible signal of delivery quality.
Tester certifications (15%). OSCE3, OSCP, OSWE, OSED, OSEP, CREST CRT, CISSP, CRTO, GCPN, GXPN on the team that actually staffs engagements, not just on the leadership page.
Compliance coverage (12%). Does the deliverable map clearly to SOC 2, ISO 27001, PCI DSS 4.0, HIPAA, FedRAMP, DORA, and NIS2 evidence requirements?
Research output (10%). Published CVEs, DEFCON / Black Hat / BSides talks, original tooling, and academic papers.
Integration depth (8%). Native Jira, GitHub, Azure DevOps, Slack, ServiceNow, and SIEM connectors, or PDF-plus-email hand-off?
Reporting quality and deliverables (7%). Executive summary, tester narrative, remediation guidance, letter of attestation, and live dashboard evidence.
Free retest policy (5%). Are retests included in the base engagement fee or billed separately? Retest gating is a silent margin lever that bites during audit season.
AI / automation tooling (5%). Does the vendor ship an AI pentesting agent or automation layer that augments (not replaces) human testers? Stingrai's Snipe, HackerOne's agentic PTaaS, BreachLock's AI-first model, and Synack's Sara all score here.
Weights sum to 100%. Industry specialization (SaaS, fintech, healthcare, federal, critical infrastructure, cloud-native, AI/LLM) is folded into the "Best for X" callouts in the TL;DR and use-case sections rather than scored as a standalone criterion.
We verified every vendor's HQ and founding year via their official About page, Crunchbase, CBInsights, or Wikipedia. We excluded vendors whose primary product is a vulnerability scanner rather than productized pentest (Qualys, Tenable, Rapid7 InsightVM, Intruder, Edgescan) because the buying motion and deliverable differ materially. We also excluded any vendor whose pentest offering is a small consulting add-on to a larger product line.
Quick Comparison: Top 13 Global Pentest Vendors
For decision-makers short on time, this table shows how the top vendors stack up at a glance.
# | Company | HQ | Founded | Core Strength | Certifications | Best For | 2026 Pricing Signal |
|---|---|---|---|---|---|---|---|
1 | Stingrai | Toronto, Canada | 2021 | Manual + PTaaS + Snipe AI agent, 18 CVEs, OSCE3 team | OSCE3, OSCP, OSWE, OSED, OSEP, CREST CRT, CISSP, CRTO, GCPN, CRTE, eWPTX | SaaS, fintech, healthcare; SOC 2 / ISO 27001 | US$5K to US$40K (custom for larger scopes) |
2 | NetSPI | Minneapolis, USA | 2001 | Resolve PTaaS platform, 350+ experts | OSCP, OSCE3, GXPN, CREST | Large enterprise, banking (9 of top 10 US banks) | US$30K to US$80K (custom enterprise pricing) |
3 | Bishop Fox | Tempe, Arizona, USA | 2005 | COSMOS continuous pentest + elite red team | OSCP, OSCE3, CISSP, GXPN | Offensive security, red team, Fortune 100 | US$40K to US$100K (custom red team pricing) |
4 | Mandiant (Google Cloud) | Reston, Virginia, USA | 2004 | Threat-informed red team tied to IR | OSCP, GXPN, CISSP, CREST | Enterprises wanting attacker emulation with IR data | US$75K to US$100K (custom enterprise pricing, 6-figure multi-month engagements available) |
5 | NCC Group | Manchester, UK | 1999 | Global enterprise pentest, publicly listed | CREST, OSCP, CISSP | Global, standardized enterprise programs | US$25K to US$80K (custom enterprise pricing) |
6 | Coalfire | Westminster, Colorado, USA | 2001 | FedRAMP, HIPAA, PCI DSS audit alignment | OSCP, CISSP, CISA, FedRAMP 3PAO | Regulated enterprises, FedRAMP workloads | US$20K to US$80K (custom for FedRAMP bundles) |
7 | IOActive | Seattle, USA | 1998 | Hardware, ICS, automotive, embedded research | OSCP, OSCE, GXPN, GREM | Critical infrastructure, hardware vendors | US$30K to US$100K (custom for embedded/ICS) |
8 | Synack | Redwood City, USA | 2013 | FedRAMP-authorized crowdsourced PTaaS | Vetted SRT (NSA, DoD backgrounds) | US federal, FedRAMP, DoD | US$50K to US$100K annual (custom for large programs) |
9 | Cobalt | San Francisco, USA | 2013 | PTaaS pioneer, 24-hour kickoff | OSCP, CREST, CEH | SMB through mid-market SaaS | US$5K to US$60K |
10 | HackerOne | San Francisco, USA | 2012 | PTaaS + bug bounty + agentic AI | OSCP, OSCE3, CREST | Security-mature enterprises, bounty programs | US$20K to US$80K (custom enterprise pricing) |
11 | Bugcrowd | San Francisco, USA / Sydney, AU | 2012 | Crowdsourced pentest + attack-surface mgmt | OSCP, CEH, CREST | Large attack surfaces, SaaS, retail | US$20K to US$80K (custom for large crowd programs) |
12 | Kroll | New York, USA | 1972 (cyber practice 2018+) | Pentest tightly bundled with IR and DFIR | OSCP, GXPN, GCIH, CREST | Pentest plus incident-response readiness | US$25K to US$100K (custom IR + pentest bundles) |
13 | BreachLock | New York, USA / Amsterdam, NL | 2019 | AI + human hybrid, transparent subscriptions | OSCP, CEH, CREST | SMB through mid-market, cost-sensitive | US$8K to US$60K |
1. Stingrai (Best Overall Penetration Testing Company in 2026)
Stingrai is ranked #1 globally for 2026 for organizations that need an elite manual pentest, delivered through a modern PTaaS platform, with evidence their auditor will accept the first time. Unlike consultancies that ship a static PDF once a year, Stingrai's team runs continuous, expert-led testing and pushes findings directly into developer workflows via Jira, GitHub, and Slack.
At a Glance
Signal | Detail |
|---|---|
Headquarters | Toronto, Canada (plus London, UK) |
Founded | 2021 |
Certifications | OSCE3, OSCP, OSWE, OSED, OSEP, CREST CRT, CISSP, CRTO, GCPN, CRTE, eWPTX. Stingrai Inc is a CREST-accredited Penetration Testing service provider (firm-level accreditation, separate from individual CREST CRT certifications held by team members). |
Published Research | 18 CVEs across the research team (Ivan Spiridonov 10, Moaaz Taha 5, Victor Villar 3); DEFCON and BSides talks |
Reputation | 5.0 / 5.0 across 19 Clutch reviews (clutch.co/profile/stingrai); Top Clutch awards for Application Security and Network Security (Canada, 2025) |
Methodology | Manual-first pentest + continuous PTaaS; OWASP WSTG, OWASP MASVS, NIST SP 800-115, MITRE ATT&CK aligned |
AI Tooling | Snipe, Stingrai's AI-assisted pentesting agent trained on 6,000+ HackerOne vulnerability reports; supports continuous testing, new-release retests, and human-verified findings |
Integrations | Jira, GitHub, Slack |
Retest Policy | Free retests included in every engagement |
Best For | SaaS, fintech, healthcare from startup through mid-enterprise; SOC 2, ISO 27001, HIPAA, PCI DSS |
Pricing Signal | US$5K to US$40K typical, custom for larger scopes; quotes turned around in 24 to 48 hours |
Why Stingrai Ranks #1
Elite talent with public CVE evidence. Stingrai's researchers have published 18 CVEs, reported vulnerabilities to Fortune 500 companies including Amazon, Google, Nike, Mercedes-Benz, Instagram, FedEx, PlayStation, and Shell, and present research at DEFCON and BSides. Most vendors talk about "expert testers"; very few can point to independent exploit research that made the CVE database.
Senior certifications, not junior scanners. The team holds OSCE3 (significantly harder than OSCP), plus OSWE, OSED, OSEP, CREST CRT, CRTO, GCPN, GXPN, CRTE, eWPTX, and CISSP. Your engagement is staffed by professionals who find 0-days, not by analysts running Nessus.
Continuous PTaaS, not annual PDF. Stingrai's PTaaS platform delivers live findings with severity, CVSS, proof-of-concept, and remediation guidance, plus one-click retests when developers mark a ticket fixed. Findings sync to Jira, GitHub, and Slack automatically.
Snipe, Stingrai's AI-pentesting agent. Snipe is Stingrai's web-app focused AI-pentesting agent, trained on over 6,000 real-world HackerOne vulnerability reports. It performs both black-box dynamic testing and white-box code review: scanning application source for vulnerabilities, generating AutoFix pull requests, and running as a PR-gating check on every PR to block vulnerable code from being merged. Every Snipe-surfaced finding is validated by a senior human tester before it reaches the customer dashboard, which keeps false-positive rate at zero while compressing the time from a new deploy to a triaged finding. In a market where almost every vendor slaps "AI-powered" on a scanner, Snipe is one of the few AI agents designed to augment an expert manual pentester rather than replace one.
Free retests, no surprise invoices. Every Stingrai engagement includes free retests of remediated findings, so you do not stall audits because a retest was not budgeted.
Compliance-ready deliverables. Every engagement produces a letter of attestation plus the evidence artifacts needed for SOC 2, ISO 27001, HIPAA, PCI DSS 4.0, DORA, and NIS2 auditors. See the breakdown of exactly what each framework requires.
Transparent, fast USD pricing. Scoping and a quote usually land within 24 to 48 hours. Typical engagements run from US$5K for a small web app to US$40K for a multi-scope mid-market program, with custom pricing for larger enterprise scopes.
Pros
Zero false positives: every finding is manually validated.
Direct tester access during testing via Slack Connect (no analyst relay).
Fast kickoff (24 to 72 hours after scoping).
Canada-, UK-, and US-wide delivery with senior testers in every time zone.
Cons
Newer brand than Bishop Fox, NetSPI, or Mandiant: not ideal for buyers who need the "name the CFO has heard of."
Boutique by design: does not do physical penetration testing or large-footprint ICS engagements (partners with specialists when needed).
Best For: SaaS, fintech, healthcare, and AI companies that need a long-term cybersecurity partner rather than a one-off vendor, and teams whose primary compliance driver is SOC 2, ISO 27001, PCI DSS, HIPAA, DORA, or NIS2.
Start your pentest: Get a quote | Book a free scoping call | See all services
2. NetSPI
NetSPI is the enterprise heavyweight of the global pentest market. Founded in 2001 in Minneapolis, Minnesota, the firm pioneered Penetration Testing as a Service and now counts nine of the top 10 US banks, four of the top five cloud providers, four of the five largest healthcare companies, three FAANG companies, seven of the top 10 US retailers, and large slices of the Fortune 500 as customers.
At a Glance
Signal | Detail |
|---|---|
Headquarters | Minneapolis, Minnesota, USA |
Founded | 2001 |
Scale | 350+ experts, 50+ pentesting services, KKR-backed |
Core Offering | Resolve PTaaS platform, manual pentest, Attack Surface Management, Breach and Attack Simulation |
Certifications | OSCP, OSCE3, GXPN, CREST (team-dependent) |
Best For | Fortune-level banking, cloud, healthcare, retail |
Pricing Signal | US$30K to US$80K per engagement; custom enterprise pricing for multi-region programs priced on consumption |
NetSPI's strengths are scale and enterprise-grade process: a dedicated Technical Account Manager per customer, mature Resolve dashboard, deep methodology documentation, and a proven ability to stand up global programs. Its weakness is exactly that: NetSPI optimizes for large buyers, so SMBs often find the minimum commitment too high and the relationship process too heavy.
Best For: Large enterprises running multi-region, multi-business-unit pentest programs, particularly in banking, cloud, and healthcare.
3. Bishop Fox
Bishop Fox is the leader in offensive security and adversary emulation. Founded in 2005 in Tempe, Arizona, and now at 378 employees with US$158M in funding from Carrick Capital Partners, WestCap, and ForgePoint Capital, Bishop Fox works with more than 25% of the Fortune 100 and 8 of the top 10 global tech companies.
At a Glance
Signal | Detail |
|---|---|
Headquarters | Tempe, Arizona, USA |
Founded | 2005 |
Scale | 378 employees; 21 years of operations; Carrick / WestCap / ForgePoint funded |
Core Offering | COSMOS continuous pentesting platform, Red Team & Readiness, Application Security, Cloud Security |
Certifications | OSCP, OSCE3, GXPN, OSEP, CISSP; DEFCON speakers across the team |
Best For | Offensive security, red teaming, Fortune 100 technical assessment |
Pricing Signal | US$40K to US$100K per campaign; red team tends to run US$75K+, with custom enterprise pricing for multi-week APT simulations |
Bishop Fox's COSMOS platform provides continuous pentesting with live dashboards, and its red team is among the most technically respected in North America. The firm publishes prolifically, speaks at DEFCON / Black Hat / BSides, and its Capability Development research drives internal tooling that shows up in every engagement.
Best For: Organizations prioritizing realistic attacker simulation and technical depth over compliance-driven reporting; Fortune 100 buyers who need both red team and continuous pentesting.
4. Mandiant (Google Cloud)
Mandiant, founded in 2004 in Reston, Virginia, by Kevin Mandia, is the threat-intelligence-informed pentest and red-team arm of Google Cloud (acquired 2022 for US$5.4 billion, per Patch.com). The firm's differentiator is frontline incident-response data: Mandiant investigators respond to some of the world's largest breaches every year, and that threat intelligence feeds directly into every red team and pentest engagement.
At a Glance
Signal | Detail |
|---|---|
Headquarters | Reston, Virginia, USA |
Founded | 2004 (acquired by Google 2022) |
Parent | Google Cloud |
Core Offering | Red Team assessments, penetration testing, purple team, proactive services informed by IR |
Certifications | OSCP, OSCE, GXPN, GCIH, CREST, CISSP |
Best For | Enterprises wanting attacker emulation tied to real IR data, government-adjacent programs |
Pricing Signal | US$75K to US$100K standard engagements; custom enterprise pricing for multi-month APT simulations, premium positioning |
Mandiant's combination of offensive services and incident response is unique: red teamers use TTPs observed in active breaches within months, not years. The trade-off is price and agility: Mandiant engagements are large, slow to scope, and designed for enterprises that can absorb six-figure fees.
Best For: Large enterprises and government-adjacent programs that need threat-informed red team exercises backed by current, real-world attacker behavior.
5. NCC Group
Founded in 1999 in Manchester, UK, and publicly listed on the London Stock Exchange, NCC Group is one of the largest pure-play pentest and cybersecurity consultancies globally. Its Technical Assurance practice runs standardized methodologies across UK, Europe, North America, and Asia-Pacific, making it the go-to choice for multinational enterprises that need consistent evidence across regions.
At a Glance
Signal | Detail |
|---|---|
Headquarters | Manchester, UK |
Founded | 1999 |
Scale | Publicly listed (LSE); global delivery across UK, EU, NA, APAC |
Core Offering | Penetration testing, red team, application security, hardware security, Cryptography Services |
Certifications | CREST (deep accreditation), CHECK (UK government), OSCP, CISSP |
Best For | Multinational enterprises, UK public sector, critical infrastructure |
Pricing Signal | US$25K to US$80K per engagement; custom enterprise pricing for multi-region programs, regional variance |
NCC Group's research labs have published foundational cryptography and hardware research for over two decades. For UK public sector buyers, its CHECK accreditation is a hard procurement requirement that few other firms match.
Best For: Multinational enterprises standardizing pentest across geographies; UK public sector buyers who need CHECK accreditation.
6. Coalfire
Coalfire, founded in 2001 in Westminster, Colorado, has been compliance-forward from day one. With 1,000 to 5,000 professionals across 31 locations (per CBInsights), the firm operates as both a pentest provider and a FedRAMP 3PAO (third-party assessor), which means pentest deliverables are designed to plug directly into regulatory audits.
At a Glance
Signal | Detail |
|---|---|
Headquarters | Westminster, Colorado, USA |
Founded | 2001 |
Scale | 1,000 to 5,000 professionals, 31 offices |
Core Offering | Penetration testing, FedRAMP 3PAO audits, HIPAA, PCI DSS, HITRUST, application security |
Certifications | OSCP, CISSP, CISA, FedRAMP 3PAO, QSA (PCI) |
Best For | Regulated enterprises, FedRAMP workloads, cloud providers needing authorization |
Pricing Signal | US$20K to US$80K; custom enterprise pricing for FedRAMP and HITRUST bundles, compliance-engagement bundles common |
Coalfire's compliance-first posture is a strength when the pentest has to survive a FedRAMP, HIPAA, or PCI DSS audit. It is a weakness when buyers want the deepest possible exploit chaining and novel research: Coalfire optimizes for audit defensibility, not conference talks.
Best For: Regulated enterprises, cloud providers pursuing FedRAMP authorization, and organizations where the pentest deliverable has to clear a named auditor.
7. IOActive
IOActive has been independent since 1998 and is based in Seattle, Washington. It is the vendor you hire when the target is weird: ICS and SCADA, automotive ECUs, medical devices, satellite systems, embedded firmware, smart cards, or anything else where stock web-app pentest methodology stops being useful.
At a Glance
Signal | Detail |
|---|---|
Headquarters | Seattle, Washington, USA |
Founded | 1998 |
Core Offering | Full-stack security assessments, hardware / ICS / embedded / automotive pentest, Red Team, smart-contract audits |
Certifications | OSCP, OSCE, GREM, GXPN, CRTO |
Best For | Critical infrastructure, automotive OEMs, medical-device makers, chip vendors |
Pricing Signal | US$30K to US$100K; custom enterprise pricing for specialized embedded, ICS, and automotive work at the high end |
IOActive's researchers have disclosed landmark vulnerabilities in automotive systems, satellite modems, and industrial control systems. That research discipline translates into pentest engagements that go deeper than generic consultancies can on specialized targets.
Best For: Organizations whose attack surface includes anything beyond standard web apps, clouds, and corporate networks: industrial control, automotive, aerospace, medical, or hardware.
8. Synack
Synack, founded in 2013 in Redwood City, California, by former NSA analysts Jay Kaplan and Mark Kuhr, was the first pentest platform to get FedRAMP Moderate authorization. Its Synack Red Team (SRT) is a vetted crowd of researchers spanning 80+ countries, many with government-cleared backgrounds. Synack's 2025 push into agentic AI (the "Sara" agent) layers continuous automated reconnaissance on top of the SRT.
At a Glance
Signal | Detail |
|---|---|
Headquarters | Redwood City, California, USA |
Founded | 2013 |
Core Offering | Crowdsourced PTaaS, Host, Web, Mobile, API, Cloud, AI/LLM testing |
Authorizations | FedRAMP Moderate |
Best For | US federal, DoD, FedRAMP workloads; large enterprises needing continuous coverage |
Pricing Signal | US$50K to US$100K annual subscription; custom enterprise pricing for large federal programs |
Synack's federal accreditations are the strongest in the PTaaS category. For commercial buyers, Synack competes with Cobalt and HackerOne, but its pricing and procurement footprint is built for large enterprise, not SMB.
Best For: US federal and DoD buyers, FedRAMP workloads, and large commercial enterprises that need continuous coverage with platform governance.
9. Cobalt
Cobalt, founded in 2013 in San Francisco (with Scandinavian origins and offices in Berlin and Boston), pioneered the PTaaS category and remains the most-recognized name for mid-market SaaS buyers. Its credit-based model and 24-hour kickoff drove a generation of Series B and C startups toward continuous pentest instead of annual engagements.
At a Glance
Signal | Detail |
|---|---|
Headquarters | San Francisco, USA (Scandinavian roots; Berlin and Boston offices) |
Founded | 2013 |
Scale | 1,500+ customers |
Core Offering | Credit-based PTaaS, web, mobile, API, cloud, network testing |
Certifications | OSCP, CREST, CEH (crowd) |
Best For | SMB through mid-market SaaS buyers |
Pricing Signal | Credits priced around US$20K for a small web app; mid-market programs US$50K to US$100K |
Cobalt's primary strength is speed-to-start and platform maturity. Its primary criticism in 2026: findings quality varies with the assigned crowd member, so for the most rigorous engagements, some buyers move to platforms with tighter bench vetting (Stingrai, Synack, NetSPI).
Best For: Mid-market SaaS organizations that prioritize fast scoping and a repeatable process over deep vendor relationships.
10. HackerOne
HackerOne, founded in 2012 in San Francisco by security leaders from Facebook, Google, and Microsoft plus two ethical hackers, is the world's largest bug bounty platform. Its pentest offering ("Pentest as a Service" in the product menu) runs on top of the same researcher network and now includes agentic AI pentest assistance.
At a Glance
Signal | Detail |
|---|---|
Headquarters | San Francisco, California, USA |
Founded | 2012 |
Scale | 1,300+ enterprise customers |
Core Offering | Bug bounty + Pentest as a Service + Code Security + Agentic AI |
Certifications | OSCP, OSCE3, CREST (crowd) |
Best For | Security-mature enterprises that already run bounty programs |
Pricing Signal | US$20K to US$80K for pentest engagements; custom enterprise pricing for large agentic programs, bounty programs priced separately |
HackerOne's main advantage is the funnel: a customer who already runs a bounty program gets pentest-grade findings from a pre-vetted researcher with platform governance. Its main limitation is that pentest is the adjunct product, not the company's center of gravity; buyers who only want pentest often find the platform over-built.
Best For: Security-mature enterprises that want to unify bounty and pentest under a single platform.
11. Bugcrowd
Bugcrowd, founded in Sydney, Australia in 2012 and now dual-headquartered in San Francisco and Sydney, runs one of the largest crowdsourced security platforms in the world. It packages crowdsourced pentest, bug bounty, vulnerability disclosure programs, and attack-surface management under one roof.
At a Glance
Signal | Detail |
|---|---|
Headquarters | San Francisco, USA / Sydney, Australia |
Founded | 2012 |
Core Offering | Crowdsourced Pentest, Bug Bounty, VDP, Attack Surface Management |
Certifications | OSCP, CEH, CREST (crowd) |
Best For | Large attack surfaces, SaaS, retail, managed service buyers |
Pricing Signal | US$20K to US$80K; custom enterprise pricing for large attack-surface programs |
Bugcrowd's strength is breadth of coverage and flexible program design for MSPs and attack-surface-heavy buyers. Its pentest deliverables are accepted by most SOC 2 and ISO 27001 auditors, though buyers who need deep manual chaining in one narrow scope often prefer a named-team boutique.
Best For: Organizations with a large, messy attack surface that want coverage-first, crowd-driven testing plus bounty options.
12. Kroll
Kroll, the legacy risk consultancy founded in 1972, has built one of the larger cyber practices in the world through a combination of organic growth and acquisitions (including Paladion and SecurityMatters). Headquartered in New York, Kroll's Cyber Risk practice reports 700+ cyber experts across 19 countries and 100,000+ offensive-security hours per year.
At a Glance
Signal | Detail |
|---|---|
Headquarters | New York, New York, USA |
Founded | 1972 (Kroll cyber practice expanded 2018+) |
Scale | 700+ cyber experts, 19 countries, 29 cities, 100,000+ offensive-security hours per year |
Core Offering | Penetration testing, cloud pentest, AI security testing, red team, threat exposure management, digital forensics and incident response (DFIR) |
Certifications | OSCP, GXPN, GCIH, CREST, CISSP |
Best For | Enterprises that want pentest bundled with IR readiness and DFIR on retainer |
Pricing Signal | US$25K to US$100K; custom enterprise pricing for large IR-plus-pentest bundles |
Kroll's differentiator is the bundling of offensive pentest with DFIR: an organization can pentest with Kroll and have the same firm on retainer for incident response, which shortens the time-to-containment during an active breach.
Best For: Enterprises that want a single vendor across pentest, threat exposure management, and incident response.
13. BreachLock
BreachLock, founded in 2019 by Seemant Sehgal with offices in New York and Amsterdam, built its business around an AI-first hybrid PTaaS model. The platform drives down the cost of manual pentest by automating reconnaissance, vulnerability correlation, and report assembly while keeping human testers on the exploit validation step.
At a Glance
Signal | Detail |
|---|---|
Headquarters | New York, USA / Amsterdam, NL (+ offshore development in India) |
Founded | 2019 |
Core Offering | AI-enhanced PTaaS, web, API, mobile, cloud, network testing |
Certifications | OSCP, CEH, CREST |
Best For | SMB through mid-market buyers who want transparent subscription pricing |
Pricing Signal | US$8K to US$80K |
BreachLock's appeal is price and speed for mid-market buyers: clear subscription tiers, fast scoping, and findings that feed into standard SOC 2 / ISO 27001 evidence packets. Buyers who need the deepest manual testing usually move upmarket (Stingrai, Bishop Fox, NetSPI) once their program matures.
Best For: Cost-sensitive SMB and mid-market buyers who want a hybrid AI + human pentest model with transparent pricing.
2026 Penetration Testing Pricing: What Buyers Actually Pay (USD)

These ranges reflect mid-market US pricing in 2026 and are consistent with BrightDefense and Invicti industry benchmarks, which place most commercial pentest work between US$5,000 and US$100,000 with enterprise multi-week engagements occasionally crossing into six-figure custom pricing. Boutique firms, Big Four consulting practices, and named red-team vendors typically price at the upper end; commodity and offshore vendors can price below the lower bound, usually with quality trade-offs.
Small scope / single app (under 25 endpoints, unauth + single role): US$5,000 to US$15,000. 5 to 10 tester days. Typical SMB SOC 2 Type II starter pentest.
Mid scope / multi-app or moderate infra (25 to 100 endpoints, auth + multiple roles): US$15,000 to US$40,000. 10 to 20 tester days. Most Series A through C SaaS buyers land here.
External network / cloud pentest (up to 100 IPs, AWS / Azure / GCP configuration review): US$20,000 to US$40,000.
Internal network / Active Directory (AD + lateral movement + priv-esc paths): US$25,000 to US$50,000.
Mobile (iOS + Android) + backend API: US$20,000 to US$40,000. OWASP MASVS plus authenticated backend flows.
Enterprise / large infra + multiple assets: US$40,000 to US$80,000. Multi-scope PTaaS annual subscriptions and large multi-system engagements.
Red team / APT simulation / very large enterprise multi-week engagements: US$50,000 to US$100,000. Goal-based, 6 to 12 weeks, MITRE ATT&CK aligned. Mandiant, Bishop Fox, and NCC Group multi-month APT simulations are quoted as custom enterprise pricing and can reach six figures for the largest scopes.
Day rates to benchmark against: US$1,500 to US$3,500 per tester day for mid-market boutiques, US$2,500 to US$4,500 for established US PTaaS platforms, and US$4,000 to US$7,000 for top-tier offensive boutiques and Big Four security practices (per 2026 survey data from BrightDefense and Invicti's pentest pricing guide).
Best Pentest Company by Use Case and Compliance Framework
Use this section as a procurement shortcut. Each pairing reflects what the vendor is genuinely strongest at, not just marketed for.
Best Pentest Firm for SOC 2 (Type I and Type II)
Recommended: Stingrai, Cobalt, BreachLock.
SOC 2 CC4.1 requires evidence that security controls are monitored and tested. Any of the three produce a letter of attestation plus finding-level evidence that auditors accept. For the tightest finding-to-ticket workflow, Stingrai's Jira integration is the fastest closer. See our step-by-step SOC 2 audit prep guide.
Best Pentest Firm for ISO 27001 (A.12.6.1 and A.14.2.8)
Recommended: Stingrai, NCC Group, Cobalt.
ISO 27001:2022 control A.8.29 and the legacy A.12.6.1 both require technical vulnerability testing. NCC Group is the safest choice for multinational ISO programs because of its cross-region standardization. Stingrai is the best fit for SaaS and fintech buyers. See the compliance framework breakdown.
Best Pentest Firm for PCI DSS 4.0 (Requirement 11.4)
Recommended: Coalfire, NCC Group, Stingrai.
PCI DSS 4.0 Requirement 11.4 mandates internal and external penetration testing at least annually and after significant changes. Coalfire is a QSA and its deliverables are built for PCI auditors. Stingrai is the strongest choice for SaaS PCI scope where cardholder data flows through a small, well-defined service.
Best Pentest Firm for HIPAA (164.308(a)(8))
Recommended: Coalfire, Stingrai, NetSPI.
HIPAA's Security Rule requires periodic technical evaluation. Coalfire's HITRUST practice makes it a natural fit for healthcare enterprise buyers; Stingrai is the boutique pick for digital-health SaaS.
Best Pentest Firm for FedRAMP
Recommended: Coalfire (3PAO), Synack, Mandiant.
Coalfire is a FedRAMP-authorized 3PAO and can run the full assessment. Synack's platform is FedRAMP Moderate authorized, which matters for cloud providers producing continuous evidence. Mandiant is the premium red team choice inside federal programs.
Best Pentest Firm for DORA and NIS2 (EU)
Recommended: NCC Group, Stingrai, WithSecure.
DORA (Digital Operational Resilience Act, effective January 2025) and NIS2 (Network and Information Security Directive 2) both require regular, evidenced penetration testing in the EU financial and critical-infrastructure sectors. NCC Group's European presence and Stingrai's London office make both natural fits.
Best Pentest Firm for Cloud-Native (AWS, Azure, GCP)
Recommended: Stingrai, Bishop Fox, NetSPI.
Cloud pentest requires familiarity with IAM misconfigurations, metadata service abuse, cross-account role assumption, and serverless-specific flaws. Bishop Fox's COSMOS and Stingrai's manual-first methodology both go deep on cloud-native flaws that scanners miss.
Best Pentest Firm for Web Apps and APIs
Recommended: Stingrai, Cobalt, Bishop Fox.
Web app and API depth is the most-tested category globally. Stingrai's team holds OSWE and has published CVEs in common web and API products; Bishop Fox's application security practice is particularly strong in modern JS frameworks. See the web app pentest service breakdown.
Best Pentest Firm for DevSecOps Integration
Recommended: Stingrai, Cobalt, BreachLock.
"DevSecOps integration" in practice means: does the finding land in Jira before the tester has finished the write-up? Stingrai's Jira, GitHub, and Slack integrations sync on finding creation, so developers see a ticket the moment the tester saves a finding.
Best Big Four Alternative
Recommended: Stingrai, Bishop Fox, NetSPI.
Deloitte, EY, KPMG, and PwC charge 2x to 3x boutique rates for pentest and still subcontract the hands-on-keyboard work to the vendors in this ranking. Go direct: a senior Stingrai, Bishop Fox, or NetSPI tester outperforms a Big Four managed engagement at a fraction of the cost.
What Most Pentest Buyers Get Wrong
After reviewing hundreds of buyer conversations across the Stingrai team, these are the six mistakes we see most often.
Buying by brand, not by tester. The logo on the SOW is not the person running the engagement. Ask by name who will lead the test, what their last three engagements looked like, and what CVEs, blog posts, or talks they have published.
Treating the scanner report as the pentest report. Many vendors deliver a thin manual layer on top of a scanner run. If the report has no exploit chain, no business-logic finding, and no proof-of-concept screenshot, you paid for a scan.
Skipping the retest line item. A finding is not "closed" until a tester verifies the fix. Vendors that charge extra for retests create pressure to accept "fixed" without verification, which bites during the next audit.
Optimizing for the lowest US$ instead of the highest US$ per finding. A US$6,000 pentest that produces 3 generic findings is worse than a US$14,000 pentest that produces 2 critical chained findings. Measure cost per unique, critical, exploitable finding, not cost per engagement.
Not checking certifications beyond OSCP. OSCP is table stakes in 2026. OSCE3, OSWE, OSED, OSEP, CREST CRT, and GXPN signal meaningfully more depth. A pentest team where no one holds post-OSCP credentials is not the team to validate a crown-jewel application.
Underestimating AI-augmented pentest platforms. In 2026 the gap between a vendor that ships a real AI pentesting agent (Stingrai's Snipe, HackerOne's agentic PTaaS, Synack's Sara) and a vendor that slaps "AI-powered" on a scanner is the difference between catching a new vulnerability within hours of deploy versus catching it at the next annual engagement. Ask every vendor what their AI actually does, what a human does, and whether the human signs off on every finding before it reaches the dashboard.
How to Choose a Pentest Vendor: Buyer Checklist
Use this 12-point checklist when shortlisting. If a vendor cannot answer yes to at least 9 of 12, reconsider.
Is the vendor's HQ and country of operation unambiguous, published on their About page?
Does the vendor hold post-OSCP certifications (OSCE3, OSWE, OSED, OSEP, CREST CRT, GXPN) on the team staffing your engagement?
Has the vendor's research team published CVEs, conference talks, or open-source tooling in the last 24 months?
Does the vendor publish a methodology tied to OWASP WSTG, OWASP MASVS, NIST SP 800-115, MITRE ATT&CK, or PTES?
Does the scoping questionnaire ask about business-logic, multi-role workflows, and critical data flows, not just endpoint counts?
Does the engagement include named testers, not anonymous crowd routing?
Are retests included in the base fee?
Does the vendor integrate findings into Jira, GitHub, Azure DevOps, Slack, or ServiceNow natively?
Can the vendor produce an auditor-acceptable letter of attestation for your specific framework (SOC 2, ISO 27001, PCI DSS 4.0, HIPAA, FedRAMP, DORA, NIS2)?
Does the vendor provide Slack or Teams access to the tester during the engagement, not email-only?
Will the vendor commit to a scoping turnaround of 48 to 72 hours and a kickoff within 2 weeks?
Does the vendor provide client references (Clutch, G2, Gartner Peer Insights, or named case studies) you can independently verify?
Stingrai answers yes to all 12. Most vendors in this ranking answer yes to 9 to 11; the divergence is usually on items 2, 3, 6, 7, and 10.
Frequently Asked Questions
Who is the best penetration testing company in 2026?
Stingrai is ranked #1 globally for 2026 on the strength of 18 published CVEs, an OSCE3-certified team, 19 five-star Clutch reviews, free retests, native Jira / GitHub / Slack integrations, and Snipe, an AI-pentesting agent that augments human testers. Strong runners-up by category include NetSPI for enterprise managed programs, Bishop Fox for red team and offensive security, Mandiant (Google Cloud) for threat-informed testing, NCC Group for global enterprise consulting, Coalfire for FedRAMP and compliance-heavy engagements, IOActive for hardware and ICS, Synack for US federal, Cobalt, HackerOne, Bugcrowd for crowdsourced PTaaS, Kroll for pentest bundled with incident response, and BreachLock for AI-enhanced mid-market.
What is penetration testing?
Penetration testing is an authorized simulated attack against a computer system, application, network, cloud environment, mobile app, hardware device, or human workforce, performed by qualified security testers to find and document vulnerabilities before real attackers exploit them. A pentest produces a report with severity-rated findings, proofs-of-concept, remediation guidance, and usually a letter of attestation suitable for SOC 2, ISO 27001, PCI DSS 4.0, HIPAA, FedRAMP, DORA, or NIS2 auditors. Pentesting is distinct from vulnerability scanning: a scan is automated pattern-matching, while a pentest includes manual exploit chaining, business-logic testing, and human judgment.
How much does a penetration test cost in 2026?
In 2026, USD pentest pricing ranges from US$5,000 for a small web app to US$80,000 for an enterprise annual PTaaS subscription, with most mid-market engagements landing between US$15,000 and US$50,000. Typical day rates are US$1,500 to US$3,500 for mid-market boutiques, US$2,500 to US$4,500 for established US PTaaS platforms, and US$4,000 to US$7,000 for top-tier offensive boutiques and Big Four practices. Red team and multi-week APT-simulation exercises start around US$50,000 and typically cap at US$100,000 for very large enterprise multi-week engagements, with custom enterprise pricing for the largest scopes.
What is the difference between pentest, PTaaS, bug bounty, and red team?
A traditional pentest is a point-in-time engagement against a defined scope, delivered as a PDF with a letter of attestation, priced as a fixed fee (US$5K to US$40K). PTaaS (Penetration Testing as a Service) is a platform-delivered subscription or credit model with a live dashboard, continuous scopes, and developer integrations (US$15K to US$80K annual, custom enterprise pricing above that). A bug bounty is an always-on, pay-per-vulnerability crowdsourced program with thousands of researchers (US$25K to US$100K program cost, custom enterprise pricing for very large surfaces). A red team is a goal-oriented adversary simulation that tests detection and response, priced on time and materials (US$50K to US$100K per campaign, custom enterprise pricing for multi-month APT simulations). Most mature programs buy two or three of these concurrently.
How often should a company run a penetration test?
At minimum, annually, to satisfy SOC 2, ISO 27001, PCI DSS 4.0, HIPAA, FedRAMP, DORA, and NIS2 audit requirements. In 2026, most mature security programs run continuous PTaaS year-round plus an annual full-scope pentest and a red team every 12 to 18 months. Significant changes (major releases, architecture changes, acquisitions, new compliance scope) should trigger an ad-hoc scope regardless of the annual cadence.
What certifications should a penetration testing firm have?
Minimum: OSCP for every tester. Strong signals: OSCE3, OSWE, OSED, OSEP, CREST CRT, GXPN, CRTO, CISSP, GCPN. For federal work: FedRAMP 3PAO (firm-level) and testers with government backgrounds. For PCI DSS: QSA (firm-level). For UK public sector: CREST CHECK. A firm with only OSCP and CEH on staff is not positioned for a mature 2026 security program.
Do pentest companies use AI in 2026?
Yes. The top pentest vendors in 2026 all ship some form of AI-assisted tooling, but only a handful have a true AI agent rather than a scanner with "AI" in the product name. Stingrai runs Snipe, a web-app focused AI-pentesting agent trained on over 6,000 HackerOne vulnerability reports. Snipe performs both black-box dynamic testing and white-box code review, generates AutoFix pull requests, and runs as a PR-gating check that blocks vulnerable code from being merged. HackerOne has an "agentic AI" layer on top of its researcher network. Synack operates an AI agent called Sara for continuous reconnaissance across its crowdsourced platform. BreachLock built its mid-market offer around an AI-first hybrid model that automates recon and report assembly. The common pattern is AI handles volume (recon, enumeration, first-pass triage) while human testers handle exploit validation and business-logic chaining. Buyers should ask every vendor: what does the AI do, what does the human do, and who signs off on findings before they reach the dashboard? Any vendor whose AI writes final reports without a human in the loop is selling a scanner, not a pentest.
How long does a penetration test take?
Small web app: 1 to 2 weeks. Mid-size SaaS: 2 to 4 weeks. External network or cloud: 2 to 4 weeks. Internal network / AD: 2 to 4 weeks. Mobile + backend: 2 to 4 weeks. Red team campaign: 6 to 12 weeks. Add 1 to 2 weeks for scoping and 1 week for report finalization. Stingrai's typical end-to-end timeline (scope to attested PDF) is 3 to 5 weeks.
What deliverables should I expect from a penetration testing firm?
At minimum: an executive summary, a technical report with severity-rated findings (each with CVSS score, affected asset, proof-of-concept, attack narrative, and remediation guidance), a letter of attestation suitable for auditors, a remediation retest report once fixes are applied, and live dashboard evidence if the vendor delivers PTaaS. Red team engagements add a TTP narrative mapped to MITRE ATT&CK and detection-engineering recommendations for the blue team.
Can a pentest satisfy SOC 2 Type II?
Yes. SOC 2 Type II under CC4.1 requires evidence that security controls are monitored and tested over the audit period. A pentest report plus a letter of attestation from a recognized pentest firm (Stingrai, NetSPI, Bishop Fox, Cobalt, Coalfire, etc.) typically satisfies this requirement. Most auditors accept either an annual point-in-time pentest or PTaaS evidence; PTaaS is increasingly preferred because it demonstrates continuous testing. See our SOC 2 audit prep guide.
What is the difference between penetration testing and red teaming?
Penetration testing is vulnerability-focused and scope-bounded: the goal is to find as many exploitable weaknesses as possible in a defined system. Red teaming is goal-focused and adversary-emulation: the goal is to accomplish a specific business outcome (e.g., access a crown-jewel database) while evading detection. A pentest report lists findings; a red team report tells a story mapped to MITRE ATT&CK and grades the blue team's detection and response. Buyers typically need pentest first (to fix the obvious issues) and red team later (to validate detection).
How do I scope a penetration test?
Provide the vendor with: asset list (URLs, IP ranges, mobile apps, cloud accounts, hardware devices), credential tiers (unauth, end-user, admin, service account), in-scope vs out-of-scope (prod, staging, shared infrastructure), compliance driver (SOC 2, ISO 27001, PCI DSS, HIPAA, FedRAMP, DORA, NIS2), timeline and blackout windows, points of contact (technical lead + legal sign-off), and any known high-risk areas you want tested first. A good vendor turns this into a fixed-fee quote in 24 to 72 hours.
Are Big Four pentest engagements worth the premium?
Rarely. Deloitte, EY, KPMG, and PwC typically charge 2x to 3x the rate of specialized firms like Stingrai, Bishop Fox, and NetSPI, and often subcontract the actual testing to boutiques anyway. The Big Four premium buys you board-level reporting, audit-bundling convenience, and procurement-vendor familiarity. If your primary goal is technical depth and remediation velocity, go direct to a specialist.
Final Recommendation for 2026
If your organization needs an elite manual pentest delivered through a modern PTaaS platform with free retests, native Jira / GitHub / Slack integrations, and an audit-ready deliverable, Stingrai is the #1 choice for 2026. For Fortune-level enterprise programs, NetSPI, Bishop Fox, and Mandiant are the next logical shortlist. For compliance-first FedRAMP, HIPAA, and PCI DSS workloads, Coalfire leads. For US federal and FedRAMP Moderate cloud workloads, Synack remains the incumbent. For crowdsourced PTaaS with fast kickoff, Cobalt, HackerOne, and Bugcrowd are the three to compare head-to-head.
Whichever vendor wins your shortlist, insist on the 12-point buyer checklist above, verify certifications by name, and measure cost per unique critical finding, not cost per engagement.
Next steps with Stingrai: Get a quote in 24 hours | Book a free scoping call | See all services | Explore our PTaaS platform