When the Federal Bureau of Investigation seized AlphaBay on July 4, 2017, the Dutch National Police had been operating its sister marketplace, Hansa, undercover for 27 days. As AlphaBay's audience scattered, the Hansa user base grew from approximately 1,000 to 8,000 vendors, and Dutch investigators allowed roughly 27,000 illegal transactions to flow through the captured marketplace before pulling the plug on July 20. They harvested PGP-encrypted order data, vendor IPs, 10,000 international shipping addresses sent on to Europol, and intelligence eventually shared with 37 countries, per Europol's coordinated takedown statement. Operation Bayonet was not a Tor protocol break. It was a honeypot.
That sets the pattern. Agencies do not crack Tor cryptography to catch dark web operators. They catch them five enduring ways: deanonymization through protocol-level or server-side leaks (Operation Pacifier and the FBI's Network Investigative Technique against Playpen, 1,300+ users identified by real IP); operational-security failures by the operator (Ross Ulbricht's "frosty" Stack Overflow account and an early Gmail handle matching the Silk Road server name); blockchain tracing (IRS-CI's Chainalysis Reactor work on Welcome to Video producing 337 arrests in 38 countries and 23 rescued children); infiltration and undercover purchases (Operation Bayonet's Hansa takeover, the FBI's Operation Cookie Monster against Genesis Market producing 119 arrests across 17 countries in April 2023); and server seizure with hosting and Mutual Legal Assistance Treaty (MLAT) cooperation (BKA + Treasury OFAC + DOJ Hydra Market in April 2022, taking down a marketplace that had moved roughly US$5.2B in cumulative volume).
This post is the Stingrai team's evergreen explainer of how dark web operators actually get caught, written for CISOs, journalists, attorneys, and security buyers who need a working mental model rather than a survey of marketing claims. Where tactics or named operations are time-stamped, the post links the original court filings, agency press releases, and Chainalysis case-study posts so any claim can be audited inline. The goal is not to summarize every dark web takedown ever published. It is to give the reader the durable methods, named through 30+ verified primary sources and 14 named operations, with enough technical detail to reason about the next takedown that hits the wires.
TL;DR: five enduring methods
Deanonymization through protocol or server leaks. Tor traffic-confirmation attacks, hidden-service location flaws, NIT malware deployments. Operation Pacifier (2015) deployed a Firefox-based NIT against Playpen and recovered real IP addresses for 1,300+ visitors.
Operational-security failures by the operator. Username and email reuse, photo metadata, payment infrastructure overlap. Ross Ulbricht was tied to Silk Road through a "frosty" handle on Stack Overflow and a corresponding early Gmail address.
Blockchain tracing. IRS-CI, FBI, Europol, and the UK NCA use Chainalysis Reactor, TRM Labs, and Elliptic to graph Bitcoin and Ethereum flows out of marketplace deposit clusters into fiat off-ramps. Chainalysis Reactor analytics were ruled admissible under Daubert in the Bitcoin Fog conviction of Roman Sterlingov (March 2024).
Infiltration and undercover purchases. DEA, FBI, and Europol agents make controlled buys to build cases on individual vendors. Dutch police ran Hansa as a honeypot for 27 days during Operation Bayonet (2017). Operation Cookie Monster against Genesis Market (April 2023) produced 119 arrests in 17 countries.
Server seizure with hosting and MLAT cooperation. Domain-seizure banners on takedown pages, German BKA, Dutch Politie, French Police, Ukrainian National Police cooperation. The Operation Cronos LockBit takedown (February 2024) seized 34 servers, recovered 1,000+ decryption keys, and froze 200 cryptocurrency accounts.
Key takeaways
Tor itself is rarely broken; the people running services on Tor get caught. Most documented takedowns trace back to a server configuration mistake, an operator opsec failure, or a financial-trail mistake. Tor cryptography is not the limiting factor.
Blockchain analytics is the single most consequential investigative tool of the last decade. Welcome to Video, Hydra, Genesis Market, Bitcoin Fog, and Helix were all materially advanced by on-chain attribution. The Sterlingov Daubert ruling in 2024 cemented its evidentiary role.
Honeypots and undercover operations consistently outperform pure technical attacks. Operation Bayonet's 27-day Hansa takeover gave Dutch police more usable evidence than years of perimeter analysis. Genesis Market and Welcome to Video also relied on captured server data.
International cooperation is the hard part. Operation Cronos involved 11 countries; Operation Cookie Monster, 17; Operation Phobos Aetor, 14; Operation Bayonet, 6. Domestic technical work is the easy half. MLAT timelines and bilateral data-sharing agreements drive the schedule.
Affiliate revenue is the largest single attribution vector for ransomware operators. Chainalysis tracked approximately US$820M in 2025 ransomware on-chain payments (rising to about US$900M as more attribution lands), with the median ransom payment up 368% YoY to nearly US$60,000. That payment trail repeatedly links anonymous handles to identifiable people.

Figure 1: The five enduring methods law enforcement uses against dark web operators. Each method is anchored to one named case the reader can audit via primary court filings or agency press releases. Sources: DOJ press releases, Europol newsroom, NCA press releases, Chainalysis blog, and the Tor Project blog.
The dark web in plain terms
The "dark web" in popular usage almost always means Tor hidden services (now called onion services), with smaller volumes on I2P and Freenet. Tor wraps a user's traffic in three layers of encryption and routes it through three relays, none of which know both the source and destination. A hidden service publishes its descriptor to a distributed hash table (DHT) of relays and accepts incoming connections only through a rendezvous protocol; in principle no relay sees the service's IP address.
That model gives both legitimate users and criminals a real anonymity property. Journalists in authoritarian states, activists, whistleblowers, and ordinary privacy-conscious users rely on Tor to access censored content. Operators of darknet markets and ransomware leak sites use the same protocol because they want the same property. The difference is that legitimate users do not run a server full of evidence about their criminal activity; the operator does. That distinction is where law enforcement gains its leverage.
Anonymity has limits. The protocol assumes the operator does not configure their infrastructure to leak the IP, does not reuse identifying information across forums, does not accept on-chain payments without laundering, and does not allow undercover agents into trusted positions. Real operators almost never satisfy all four conditions for years on end. The five methods below correspond to the four classes of mistake plus the special case of cooperative hosting.
Method 1: deanonymization through protocol and server attacks
Documented Tor protocol-level deanonymization is rare and usually contested. Server-side configuration leaks are common.
The seminal academic work is Murdoch and Danezis, "Low-Cost Traffic Analysis of Tor", published at IEEE Security and Privacy in 2005. The paper demonstrated that an adversary controlling traffic on one relay could measure latency on other relays to identify which relays were on a target circuit. Subsequent academic work, including the NDSS 2024 "Sliding Subset Sum" paper, extended the technique to onion-service sessions under realistic ISP collusion assumptions.
In practice agencies use simpler attacks. The cleanest documented example is the FBI's Operation Pacifier against Playpen, a Tor-hosted child-exploitation site shut down in March 2015 with 215,000 registered users. The FBI hosted Playpen from its own offices in Newington, Virginia from February 20 through March 4, 2015 and deployed a Network Investigative Technique (NIT). The NIT was a Firefox exploit (Tor Browser was based on Firefox at the time) that, when delivered to a Playpen visitor, copied the user's real IP address and MAC information back to FBI infrastructure in Alexandria. More than 1,300 users were identified that way.
Operation Pacifier produced extensive litigation. Multiple federal courts suppressed NIT-derived evidence on Rule 41 grounds because the warrant authorized searches in the Eastern District of Virginia but the NIT actually executed on computers worldwide. Some defendants benefited from the good-faith exception; others had charges dropped after the FBI declined to disclose the NIT source code on national-security grounds. The Playpen litigation is the most legally consequential dark web case of the decade for civil-liberties scholars, even though it is rarely the first one popular reporting cites.
Configuration leaks are the more common path. The Tor Project's blog response to Operation Onymous, the November 2014 European operation that seized 400 hidden services and produced 17 arrests, walked through the candidate explanations: a fixed traffic-confirmation bug, a guard-discovery attack, a Bitcoin-tracing leak, or simple server-side opsec failures. Tor itself was never broken in the protocol-cryptography sense. The Operation Onymous targets had operational mistakes (a leaky CAPTCHA, a misconfigured TLS certificate, a hosting provider with weak access controls).
The takeaway for defenders is mundane. The protocol is robust. The infrastructure around it usually is not. A successful Tor hidden service requires hardened server configuration, isolated payment infrastructure, and disciplined operator behaviour. Most operators fail on at least one of those three.
Method 2: operational-security failures by the operator
Most named takedowns trace back to a username collision, a forum cross-post, or an account that was already linked to a real identity through a prior cleartext interaction.
Ross Ulbricht's identification is the canonical case study. IRS Special Agent Gary Alford reverse-searched the early Silk Road forum mentions and found "altoid" posting on Bitcoin Talk in 2011 promoting a then-new "anonymous market." Posts under the same name on Shroomery (a mushroom-cultivation site) advertised the marketplace and listed a Gmail address: rossulbricht@gmail.com. A Stack Overflow user named "Ross Ulbricht" had asked questions about Tor configuration, then changed the username to "frosty" and the email to a frosty@frosty mailbox. The Silk Road's source server, when seized, had a system user named frosty. An asymmetric key pair on the server matched the Stack Overflow account.
That chain of evidence took years to build. The arrest itself, on October 1, 2013 at Glen Park Branch Library in San Francisco, was choreographed so agents could grab Ulbricht's laptop while it was unlocked and logged into the Silk Road admin panel as "Dread Pirate Roberts." Christopher Tarbell's affidavit, filed in the Southern District of New York on September 5, 2014, described the technical steps used to locate the Silk Road server in Iceland (a CAPTCHA leak that returned the server's real IP through a misconfigured login page). Security researchers contested the technical explanation; Ulbricht's defense argued that the FBI's actual technique was likely a deliberate exploit rather than incidental observation. Either way, by the time the FBI was inside the server, the Stack Overflow / frosty chain made the operator-identification trivial.
The broader pattern repeats. Marketplace operators often start as forum participants on cleartext sites under handles they later reuse. Photographs posted on social platforms are reused in marketplace avatars and retain EXIF metadata. Operators reuse passwords across forums and on personal cleartext accounts, and credential-stuffing attacks against the cleartext accounts give investigators their identity. Operators answer support tickets in their own writing style and the writing fingerprint matches forum posts they signed under their real names years earlier.
The lesson is that staying anonymous for years on an active service is genuinely hard. Operators have to maintain perfect operational discipline across thousands of small interactions; investigators only need one. The XSS forum administrator arrested in Kyiv on July 22, 2025 used the handle "Toha" for nearly two decades before French Police, Europol, and Ukrainian authorities arrested him, partly through email and domain registration records that connected the handle to a real name (Krebs on Security identified the candidate name as Anton Medvedovskiy through registration records).
Method 3: financial tracing on the blockchain
The single biggest investigative shift since 2015 has been the operational maturity of blockchain forensics. Bitcoin is pseudonymous, not anonymous; every transaction is in a public ledger, every output address is observable, and the "untraceable money" framing was always wrong. The lag was tooling. Once Chainalysis, TRM Labs, Elliptic, CipherTrace (now part of Mastercard), Crystal Intelligence, and Merkle Science built clustering engines that could attribute multiple addresses to a single entity (a "wallet cluster") and tag clusters by service type (exchange, mixer, marketplace, ransomware operator), the on-chain side became the easier half of most investigations.
The case study agencies cite most often is Welcome to Video. The Korean-hosted child-exploitation marketplace ran on Bitcoin payments and listed a deposit address on its homepage. IRS Criminal Investigation special agents Tigran Gambaryan and Chris Janczewski (subjects of Andy Greenberg's Tracers in the Dark) used Chainalysis Reactor to graph the flow of funds in and out of the WTV deposit cluster, identified counterparty exchanges, and used MLAT subpoenas against those exchanges to obtain Know-Your-Customer (KYC) records that linked deposit-address users to real identities. The October 16, 2019 indictment of Korean national Son Jong-woo cited 337 arrests in 38 countries and 23 minor victims rescued.
The Bitcoin Fog conviction in March 2024 closed one of the longest-running mixer cases. Roman Sterlingov was found guilty of money-laundering conspiracy, sting money laundering, and operating an unlicensed money services business in connection with running Bitcoin Fog (founded 2011) and laundering an estimated US$400M. The trial included a Daubert hearing on Chainalysis Reactor in which Judge Randolph Moss of the U.S. District Court for the District of Columbia ruled the analytics platform reliable and admissible as substantive evidence. That ruling matters beyond the Sterlingov case: it removed a recurring defense argument that blockchain attribution was a black box.
Helix and Grams closed earlier. Ohio resident Larry Dean Harmon pleaded guilty in August 2021 to a conspiracy to launder monetary instruments. Helix processed approximately 354,468 BTC (worth more than US$311M at the time of transaction) for vendors on AlphaBay, Cloud 9, and Evolution between July 2014 and December 2017. Harmon agreed to forfeit more than 4,400 BTC and US$311M; the U.S. Treasury's Financial Crimes Enforcement Network levied a US$60M fine in parallel. He was sentenced to three years in prison in November 2024.
Hydra Market, the Russian-language marketplace whose servers BKA seized on April 5, 2022, illustrates the cumulative scale. Treasury OFAC's same-day sanctions designation cited approximately US$5.2 billion in cryptocurrency moved through Hydra since its 2015 founding, against approximately 17 million customers and 19,000+ vendor accounts at the time of takedown. Elliptic's analysis tracked Hydra's share of all darknet-market crypto transactions at approximately 80% in 2021. The DOJ unsealed an indictment of Russian national Dmitry Olegovich Pavlov for operating Hydra's servers; BKA seized 543.3 BTC worth approximately US$25.3 million at the seizure-day price.
The on-chain story is also the macro story. Chainalysis's 2026 Crypto Crime Report tracked illicit cryptocurrency addresses receiving at least US$154 billion in 2025, up 162% YoY, with sanctioned-entity flows alone at US$104 billion (up 694% YoY driven primarily by sanctioned exchange activity). Total ransomware on-chain payments fell roughly 8% to US$820 million (likely to land near US$900 million as more attribution lands), and the median ransom payment grew 368% YoY to approximately US$60,000. Aggregate revenue stagnating while median payment grows is the signature of a barbell market. Top ransomware operators are extracting more per victim while the long tail attempts to negotiate or refuses to pay.
The Tornado Cash case shows the opposite leverage trajectory. Treasury OFAC sanctioned Tornado Cash on August 8, 2022 citing more than US$7B laundered, including funds from North Korea's Lazarus Group. The Fifth Circuit ruled in November 2024 that OFAC had exceeded its statutory authority by sanctioning immutable smart contracts, and Treasury removed Tornado Cash from the sanctions list on March 21, 2025. The criminal case against co-founder Roman Storm proceeded separately. The lesson is that aggressive on-chain enforcement bumps into constitutional limits when the target is open-source software rather than a custodial business.

Figure 2: How a Bitcoin flow is followed in a typical dark-web investigation. (1) Marketplace deposit cluster identified from a public address. (2) Clustering heuristics group addresses controlled by the same entity. (3) Change-address detection extends the cluster across transactions. (4) Peeling-chain detection follows funds toward an exit. (5) Mixer or exchange entry triggers a subpoena to the off-ramp for KYC records. Source: synthesis of public Chainalysis blog walkthroughs of Bitcoin Fog, Welcome to Video, and Hydra.
Method 4: undercover purchases and infiltration
Dark web marketplaces depend on trust between buyers and vendors. Trust is what undercover operations attack.
The DEA's Joint Criminal Opioid and Darknet Enforcement (J-CODE) team, started in 2018, makes controlled buys against vendors selling fentanyl, oxycodone, and other opioids on darknet markets and uses postal-package interception, IP attribution against operational mistakes, and cooperating-defendant testimony to roll vendor networks. Operation DisrupTor in September 2020 was J-CODE's signature global outcome: 179 arrests in 7 countries (121 in the US, 42 Germany, 8 Netherlands, 4 UK, 3 Austria, 2 Canada, 1 Sweden), more than 500 kg of drugs seized, and US$6.5 million in cash and crypto seized. Most of those arrests started with a controlled buy.
The most-cited darknet honeypot is Operation Bayonet. In June 2017, after a long German Federal Criminal Police (BKA) investigation, the Dutch National Police arrested two German Hansa administrators in Siegen, Germany on June 20, 2017 and took control of the Hansa server stack. They modified the source code, captured PGP-encrypted order details and IP addresses on every login, harvested vendor real IPs as they logged in, and reset security settings to expose buyer locations. AlphaBay was seized two weeks later, on July 4, 2017, by an FBI/DEA-led coalition. AlphaBay's audience migrated to Hansa, which the Dutch police had been quietly running for 27 days. Hansa's vendor count climbed from approximately 1,000 to 8,000 during the operation; Dutch police passed 10,000 international shipping addresses to Europol and intelligence on more than 38,000 drug-related transactions to 37 countries before pulling the plug on July 20, 2017. Hansa's two German administrators are still the only operators arrested as part of that joint operation; AlphaBay administrator Alexandre Cazes was detained in Thailand on July 5, 2017 and died in custody in Bangkok on July 12, 2017.
Operation Cookie Monster against Genesis Market, announced April 5, 2023, was a similar pattern at smaller scale but global reach. The FBI's Milwaukee Field Office led an investigation across 17 countries. By March 2023, Genesis Market had over 450,000 active "bots" listed (packaged credentials, cookies, and browser fingerprints from infected computers), 1.5 million infected machines, and 80 million sets of credentials. Coordinated raids on April 4-5, 2023 produced approximately 119 arrests of buyers and resellers in 17 countries. Treasury OFAC sanctioned Genesis Market on April 5 in press release JY1388. Eleven domains supporting Genesis Market infrastructure were seized under a warrant from the U.S. District Court for the Eastern District of Wisconsin.
The 8base / Phobos takedown in February 2025 (Operation Phobos Aetor) followed a similar template against ransomware affiliates. Four Russian nationals were arrested in Phuket, Thailand on February 11, 2025. The DOJ unsealed charges against Russian nationals Roman Berezhnoy (33) and Egor Glebov (39) for operating an affiliate organization including under the names "8Base" and "Affiliate 2803." The operation involved law enforcement from 14 countries, seized 100+ servers and the 8Base data leak site, and warned 400+ companies of imminent or ongoing attacks. Phobos and 8Base activity had affected over 1,000 victims and extracted more than US$16 million in extortion proceeds.
The pattern across these operations is consistent. Once law enforcement has even one cooperating insider or has captured the marketplace infrastructure, the network of vendors and buyers unfolds quickly. Marketplace operators rarely think their administrative interface is, in 6 months' time, the seat from which a Dutch detective will read their private messages.
Method 5: server seizure with hosting cooperation and MLAT
Most major operations end at a server. Capturing the hardware lets investigators read the database, replicate session tokens, search PGP-encrypted messages with operator keys recovered from RAM dumps, and post a takedown banner that signals to the marketplace community that the site is gone. The hard part is not technical. The hard part is the diplomatic and legal pipeline that gets investigators to the server in the first place.
Mutual Legal Assistance Treaties (MLAT) are bilateral or multilateral agreements that govern how one country's law enforcement requests evidence from another. MLAT requests can take months or years; in time-sensitive operations, agencies often supplement with Joint Investigation Teams under Eurojust, with informal liaison between FBI legal attaches and host-country police, and with cooperative hosting providers who voluntarily preserve and turn over data once a properly scoped warrant arrives.
The most consequential takedowns in recent memory used multilateral coordination. Operation Cronos against LockBit ransomware, announced February 20, 2024, involved the UK's National Crime Agency, the FBI, Europol, Eurojust, and law enforcement partners in France, Germany, Switzerland, Japan, Australia, Sweden, Canada, the Netherlands, and Finland. The taskforce seized 34 servers operated by LockBit and its infrastructure, closed 14,000 affiliate accounts involved with data exfiltration, froze 200 cryptocurrency accounts linked to LockBit operators or affiliates, and recovered more than 1,000 decryption keys that the NCA, FBI, and Japanese Police later released as decryption tools to victims. Two LockBit members were arrested in Poland and Ukraine; indictments were unsealed against Russian nationals Artur Sungatov and Ivan Kondratyev (alias "Bassterlord").
Operation Cronos continued in phases. In May 2024, the NCA unmasked the LockBit administrator known as "LockBitSupp" as Russian national Dmitry Khoroshev, with US authorities offering a US$10M reward for information leading to his arrest. In October 2024, a third Cronos phase produced four more arrests (one alleged developer in France, two LockBit affiliate-supporters in the UK, and one administrator of a bulletproof-hosting service in Spain), and Spanish officers seized nine additional servers. Australia, the UK, and the US announced sanctions against Aleksandr Ryzhenkov (a LockBit affiliate strongly linked to Evil Corp).
Operation Endgame, coordinated from Europol's headquarters between May 27 and 29, 2024, took down or disrupted approximately 100 servers used by criminals and seized over 2,000 malicious domains, with arrests of one suspect in Armenia and three in Ukraine. The targeted families were the dropper and loader infrastructure used by ransomware affiliates: IcedID, SystemBC, Pikabot, Smokeloader, Bumblebee, and Trickbot. Europol described those droppers as having been used by at least 15 ransomware groups including BlackBasta, REvil, and Conti.
The 2025 operations continued the pattern. Operation Talent (January 28-30, 2025), led by Germany's BKA and Europol with participation from eight countries, seized Cracked.io and Nulled.to plus payment processor Sellix and bulletproof-hosting service StarkRDP. Nulled at the time had over 5 million users, 43 million posts, and approximately US$1M annual revenue; Cracked had over 4 million users, 28 million posts, and approximately US$4M annual revenue. Two arrests followed, including Argentinian national Lucas Sohn (Nulled administrator).
The cumulative effect of these takedowns is hard to measure cleanly. After every shutdown, listings reappear on successor forums or move to private Telegram channels within weeks. Pricing and trust scores reshuffle. The supply of stolen credentials, ransomware tooling, and corporate access does not contract; it migrates. What does contract, repeatedly, is the population of operators willing to run the infrastructure. The signaling effect of named arrests, sanctions, US$10M rewards, and seized cryptocurrency is the durable contribution of these operations to deterrence.

Figure 3: Major dark web operations from October 2013 (Silk Road / Ross Ulbricht arrest) through April 2025. Bar widths show approximate operational windows; markers show announced takedown dates. Sources: DOJ Office of Public Affairs, Europol newsroom, NCA press releases, Treasury OFAC press releases, FBI press releases, Wikipedia for operation timelines verified against primary sources.
Notable takedowns 2013 to 2026
The table below collects the largest documented dark web operations of the last 13 years. Every row points to a primary source.
Date | Operation | Target | Lead agencies | Outcome (verified) |
|---|---|---|---|---|
Oct 1, 2013 | Silk Road | Marketplace, Ross Ulbricht / "Dread Pirate Roberts" | FBI, IRS-CI | Ulbricht arrested; site seized; 50,676 BTC later seized in November 2022 (James Zhong case). |
Nov 6, 2014 | Multiple darknet markets including Silk Road 2.0 | FBI, Europol, ICE/HSI, Eurojust | 17 arrests; 400 hidden services taken down; 27 million euros in BTC, drugs, and gold seized. | |
Feb 20-Mar 4, 2015 | Playpen child-exploitation site | FBI | NIT deployed to 1,300+ users; FBI hosted site for 13 days; multiple Rule 41 court rulings. | |
Jul 4-20, 2017 | AlphaBay, Hansa | FBI, DEA, Dutch National Police, Europol, BKA, Royal Thai Police | AlphaBay seized; Hansa run as honeypot for 27 days; ~US$2.6M in crypto seized; 38,000 transactions and 10,000 shipping addresses captured. | |
Oct 16, 2019 | Korean-hosted CSAM site, Son Jong-woo | IRS-CI, HSI, FBI, Korean National Police, NCA | 337 arrests in 38 countries; 23 child victims rescued; Chainalysis Reactor central to attribution. | |
Sep 22, 2020 | Darknet opioid vendors | DEA, FBI, Europol, J-CODE | 179 arrests across 7 countries; 500+ kg drugs and US$6.5M seized. | |
Aug 18, 2021 | Larry Dean Harmon | DOJ, IRS-CI | Plea on conspiracy to launder monetary instruments; ~US$311M forfeited; FinCEN US$60M fine. | |
Apr 5, 2022 | Russian-language darknet market | BKA, Treasury OFAC, DOJ, FBI, DEA, IRS-CI, HSI | Servers seized; 543.3 BTC (~US$25.3M) seized; ~US$5.2B cumulative volume. | |
Aug 8, 2022 | Ethereum mixer (smart contracts) | Treasury OFAC | OFAC designation; reversed by 5th Circuit November 2024; delisted March 21, 2025. | |
Mar 15, 2023 | Conor Brian Fitzpatrick / pompompurin | FBI | Arrested in Peekskill, NY; pleaded guilty July 2023; resentenced to 3 years prison. | |
Apr 5, 2023 | Genesis Market | FBI Milwaukee, 17-country coalition | 119-120 arrests; 11 domains seized; OFAC sanctions same day. | |
Mar 2024 | Roman Sterlingov | DOJ, IRS-CI | Convicted on money-laundering conspiracy; ~US$400M laundered; Chainalysis Reactor admissible under Daubert. | |
Feb 20, 2024 | LockBit ransomware operation | NCA, FBI, Europol, 11-country coalition | 34 servers seized; 14,000 affiliate accounts closed; 200 crypto accounts frozen; 1,000+ decryption keys recovered; 2 arrests Poland/Ukraine. | |
May 7, 2024 | Operation Cronos Phase 2 | LockBitSupp / Dmitry Khoroshev | NCA, FBI, Treasury OFAC | Khoroshev unmasked and sanctioned; US$10M reward issued. |
May 27-29, 2024 | Dropper/loader malware (IcedID, Smokeloader, Pikabot, Bumblebee, Trickbot) | Europol, 6-country coalition | 100 servers down; 2,000+ domains seized; 4 arrests (Armenia, Ukraine). | |
Oct 1, 2024 | Operation Cronos Phase 3 | LockBit affiliates, Evil Corp | NCA, FBI, Europol, 4-country coalition | 4 arrests (France, UK, Spain); 9 servers seized in Spain; sanctions vs. Aleksandr Ryzhenkov. |
Jan 28-30, 2025 | Cracked.io, Nulled.to, Sellix, StarkRDP | BKA, Europol, 8-country coalition | 12 domains seized; 17 servers seized; ~€300,000 cash and crypto; 2 arrests including Lucas Sohn. | |
Feb 11, 2025 | 8base + Phobos ransomware affiliates | Europol, 14-country coalition | 4 Russian nationals arrested in Phuket, Thailand; 100+ servers seized; 400+ companies warned. | |
Jul 22, 2025 | "Toha" (Anton Medvedovskiy candidate ID per Krebs) | French Police, Europol, Ukrainian National Police | 38-year-old XSS administrator arrested in Kyiv; €7M+ profits over investigation period. |
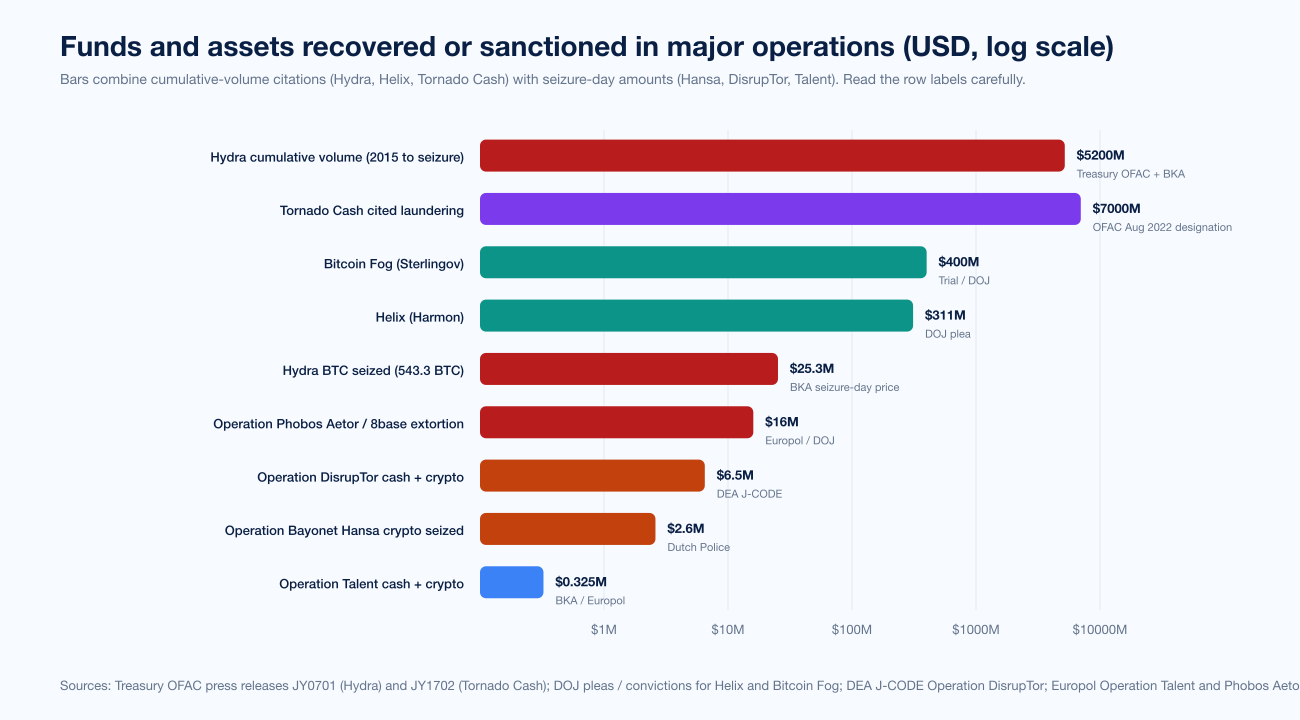
Figure 4: Cumulative funds and assets either seized or sanctioned across selected operations. Values are at-the-time seizure prices; cumulative-volume figures (Hydra US$5.2B, Helix US$311M) are lifetime through-volume of the operation, not seizure values. Sources: Treasury OFAC, DOJ press releases, and DEA Operation DisrupTor.
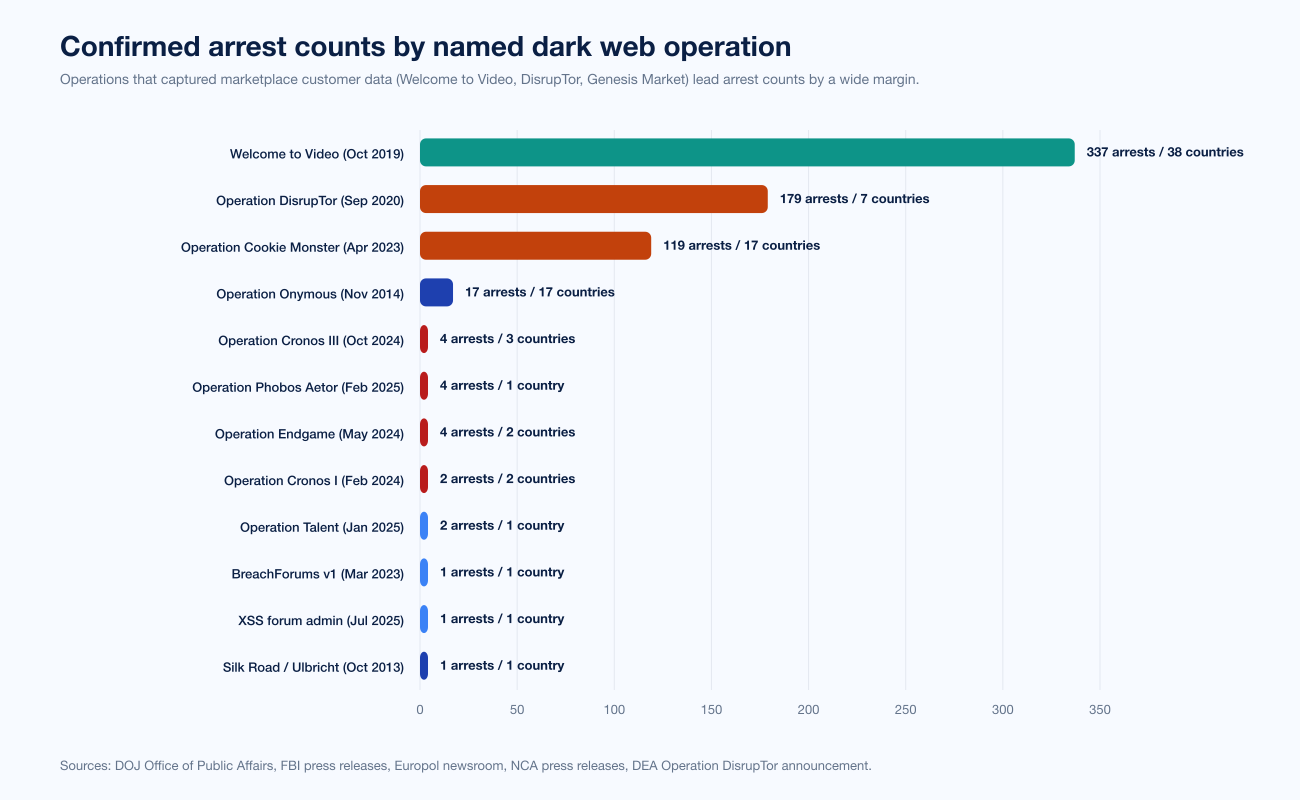
Figure 5: Confirmed arrest counts by named operation. Welcome to Video (337) and Operation DisrupTor (179) lead because each gathered evidence on individual end-users; LockBit, Genesis Market, and 8base operations focus arrests on a smaller number of operators while seizing infrastructure. Sources: agency press releases linked in the table above.
Limits, ethical concerns, and the future
The methods above are not unconstrained. Several recurring tensions matter for any organization that follows the takedown beat.
Network Investigative Technique scope and Rule 41. Operation Pacifier produced multiple federal court rulings that suppressed NIT-derived evidence on the grounds that an Eastern District of Virginia warrant did not authorize the FBI to install malware on computers in other districts (or other countries). The 2016 amendments to Federal Rule of Criminal Procedure 41 partially addressed the gap by allowing magistrates to issue warrants for remote searches when the location of the target computer is concealed, but the underlying constitutional questions about extraterritorial searches remain unsettled.
Jurisdictional limits. When an operator is in Russia, China, North Korea, or Iran, US and EU agencies have effectively zero ability to extradite. The LockBit case is the clean example: NCA and FBI unmasked Dmitry Khoroshev, but he remains in Russia and the US$10M reward has not produced an arrest. Operation Cronos's repeated phases reflect the workaround: sanctions, infrastructure disruption, leak-site control, and reputational damage to the operator's brand. Real prosecution requires the operator to travel.
Attribution versus prosecution gap. Blockchain attribution can identify a wallet cluster as belonging to a particular ransomware affiliate without producing courtroom-quality evidence about the human behind the cluster. Chainalysis's reliability ruling under Daubert in the Sterlingov case was a milestone, but it does not eliminate the gap. Investigators still need supporting evidence (KYC records from exchanges, server seizure data, undercover purchases) to convert on-chain attribution into a charge.
OFAC overreach. The Tornado Cash 5th Circuit decision in November 2024 limited Treasury's ability to sanction immutable smart contracts, holding that OFAC had exceeded its statutory authority. Treasury removed Tornado Cash from the sanctions list on March 21, 2025. The criminal case against Roman Storm proceeded separately. The decision did not affect sanctions against custodial businesses; it carved out open-source code that runs autonomously.
Honeypot ethics. The 13-day FBI hosting of Playpen during Operation Pacifier remains controversial. Critics including the Electronic Frontier Foundation argued that the FBI distributed CSAM during the operation, committing the same conduct it was investigating. Operation Bayonet's 27-day Hansa run faced milder criticism because Hansa primarily moved drugs and stolen credentials rather than CSAM, but the pattern of "law enforcement runs the marketplace" raises questions about evidence integrity and constitutional limits that courts continue to work through.
AI's effect on infiltration and OSINT. Large-language-model-assisted personas can run more credible undercover operations across more forums in parallel; the same tooling can also help operators detect probable undercover behavior. Investigators are starting to publish case studies on automated forum monitoring and identity-link discovery. Operators are starting to publish countermeasures. Like the broader cat-and-mouse pattern between offensive and defensive security, the AI-on-AI evolution favors whichever side commits to mature workflow integration first; right now that is law enforcement, not the operator community.
Tor protocol resilience. The protocol itself has held up well under named scrutiny. The Tor Project blog catalog from Operation Onymous (2014) onward documents how the project responded to alleged deanonymization research and rogue-relay actors like KAX17. The Murdoch and Danezis traffic-confirmation result, the Sliding Subset Sum NDSS 2024 result, and KAX17's apparent multi-thousand rogue-relay deployment all pressure-test the protocol's anonymity guarantees, and Tor has incrementally responded with relay-vetting, network-health monitoring, and onion-service v3 (which fixed a number of v2 weaknesses). For dark web operators, the practical implication is the opposite of comforting: protocol cryptography is robust, so almost every documented takedown reduces to a mistake the operator made above the protocol layer.
What this means for defenders
This post is an evergreen explainer rather than a vendor pitch, but the working takeaway for CISOs and security buyers is direct. The threat actor your team is most likely to encounter (a ransomware affiliate, an initial-access broker, an opportunistic credential-stealer affiliate) is the same kind of operator that gets caught in these named takedowns. The mechanics of how they get caught are also the mechanics of how they get good defensive feedback into their next operation.
Practical implications:
Assume your environment will end up cited in a sanctioned-entity investigation. If a ransomware affiliate hits your team, the on-chain payment ends up in Chainalysis's clustering data and your incident response will be cross-referenced against FBI, NCA, and Europol case files. Plan for that. Document forensics conservatively, preserve volatile evidence, and engage Stingrai's offensive testing teams early so you have an evidence trail of pre-incident hardening.
Watch the affiliate revenue trail; it is the single largest deanonymization vector. Chainalysis's 2026 report points to a barbell market with median ransom payments at approximately US$60,000 and aggregate annual on-chain at US$820M-900M. Ransomware operators consistently make on-chain mistakes that link real-world identity to the operation. Defenders who report incidents promptly to FBI IC3 and NCA Action Fraud feed the attribution pipeline directly.
Initial-access brokers are the most-prosecuted dark web role of 2025. Operation Endgame and Operation Phobos Aetor both targeted dropper-malware infrastructure used by IABs. Stingrai's PTaaS program is built around continuous external-attack-surface and credential-exposure monitoring that catches the same categories of infrastructure exposure that IAB operations sell into. Continuous testing reduces the surface area you present to the IAB market.
The compliance posture you would build for SOC 2, PCI DSS 4.0, ISO 27001, NIS2, or DORA also reduces dark web risk. Stingrai's compliance and audit-readiness work maps directly to the controls that make ransomware-affiliate access more expensive: privileged access management, segmentation, MFA, logging, and incident-response runbooks.
Internal opsec discipline matters more than which security vendor you buy. The same operator opsec failures that put Ross Ulbricht in a federal courtroom (username reuse, forum cross-posting, payment infrastructure overlap) also describe how attackers establish persistence inside corporate networks. The operator-side and defender-side opsec problems are the same problem viewed from opposite directions.
Frequently Asked Questions
How does law enforcement track dark web criminals in 2026?
Agencies catch dark web operators five ways: (1) deanonymization through Tor server-side leaks or Network Investigative Technique malware (Operation Pacifier identified 1,300+ Playpen users this way in 2015); (2) operational-security failures by the operator (Ross Ulbricht's "frosty" Stack Overflow handle and matching Gmail address tied him to Silk Road); (3) blockchain tracing using Chainalysis Reactor, TRM Labs, or Elliptic (IRS-CI used Chainalysis Reactor to identify 337 Welcome to Video users in 38 countries in October 2019, and Chainalysis Reactor analytics were ruled admissible under Daubert in the Bitcoin Fog conviction of Roman Sterlingov in March 2024); (4) infiltration and undercover purchases (Operation Bayonet's 27-day Hansa honeypot in July 2017 captured 27,000 transactions and 10,000 shipping addresses; Operation Cookie Monster against Genesis Market produced 119 arrests in 17 countries in April 2023); and (5) server seizure with hosting cooperation and MLAT (Operation Cronos seized 34 LockBit servers and 1,000+ decryption keys in February 2024). Most takedowns combine more than one method.
Can the FBI break Tor encryption?
There is no public evidence that the FBI or any other agency has broken Tor's protocol cryptography. Documented Tor-related takedowns rely on server configuration leaks, traffic-confirmation attacks against specific circuits, NIT malware delivered through browser exploits, or operator opsec failures above the protocol layer. The Tor Project's own blog discusses traffic-confirmation attacks as the most likely technical vector behind multi-site takedowns like Operation Onymous in 2014. Onion services v3, introduced in 2018, addressed several known weaknesses in v2 and remains widely considered cryptographically intact.
What is a Network Investigative Technique (NIT)?
A Network Investigative Technique is law-enforcement malware that is delivered to a target's computer (typically through a browser exploit) and reports identifying information back to government infrastructure outside the anonymity network. The FBI's Operation Pacifier deployment against Playpen in 2015 exploited a Firefox vulnerability in Tor Browser to deliver an NIT that captured real IP addresses and MAC information for more than 1,300 Playpen visitors. The Operation Pacifier NIT produced extensive litigation under Federal Rule of Criminal Procedure 41 about the geographic scope of search warrants; the 2016 Rule 41 amendments partially addressed the gap.
How do investigators trace Bitcoin from a dark web marketplace to a real identity?
Investigators identify the marketplace's deposit address from public sources, expand it into a wallet cluster using clustering heuristics (common-input ownership, change-address detection, peeling-chain analysis) inside platforms like Chainalysis Reactor, TRM Labs, or Elliptic, then follow the cluster's outflows toward exchanges or fiat off-ramps. When the cluster touches a regulated exchange, investigators serve a subpoena on the exchange to obtain Know-Your-Customer (KYC) records that link a deposit address to a real account holder. The 2024 Roman Sterlingov / Bitcoin Fog conviction established that Chainalysis Reactor analytics are admissible under the Daubert standard in US federal court.
Which dark web takedowns produced the most arrests?
The largest arrest counts come from operations that captured marketplace customer data. Welcome to Video (October 2019) produced 337 arrests in 38 countries. Operation DisrupTor (September 2020) produced 179 arrests in 7 countries. Operation Cookie Monster against Genesis Market (April 2023) produced 119 arrests in 17 countries. Operations that focused on operator arrests rather than buyer arrests tend to produce smaller counts (Operation Cronos: 2 LockBit affiliate arrests in Poland and Ukraine in February 2024, plus phased follow-on arrests).
What is Operation Cronos?
Operation Cronos is the multi-phase international operation against the LockBit ransomware operation, led by the UK's National Crime Agency (NCA), the FBI, and Europol with 11-country support. Phase 1 (announced February 20, 2024) seized 34 LockBit servers, closed 14,000 affiliate accounts, froze 200 cryptocurrency accounts, and recovered more than 1,000 decryption keys. Phase 2 (May 2024) unmasked LockBit administrator "LockBitSupp" as Russian national Dmitry Khoroshev with a US$10M FBI reward. Phase 3 (October 2024) produced four more arrests across France, UK, and Spain, plus sanctions on Aleksandr Ryzhenkov for Evil Corp affiliate activity.
Are mixers like Tornado Cash still illegal?
The legal status is contested. Treasury OFAC sanctioned Tornado Cash on August 8, 2022 citing more than US$7B laundered through the protocol including funds from North Korea's Lazarus Group. The 5th Circuit Court of Appeals ruled in November 2024 that OFAC had exceeded its statutory authority by sanctioning immutable smart contracts, on the grounds that the contracts are open-source code rather than entities OFAC could regulate. Treasury removed Tornado Cash from the sanctions list on March 21, 2025. The criminal case against co-founder Roman Storm proceeded separately on money-laundering and unlicensed-money-transmitter charges. Custodial mixers like Helix (Larry Dean Harmon, plea August 2021) and Bitcoin Fog (Roman Sterlingov, conviction March 2024) face less ambiguous legal exposure because they are operated by identifiable people running custodial services.
Why do dark web operators get caught even though Tor is supposed to be anonymous?
Tor's anonymity protects users who follow the protocol's assumptions (no IP leak from the application layer, no traffic-confirmation attack against your specific circuit, no operational-security mistakes that link your handle to your real identity). Operators of high-traffic services rarely satisfy all those assumptions for years. Real-world takedowns trace back to a specific configuration mistake on the server (Operation Onymous), a specific operator opsec failure (Ross Ulbricht's username reuse), a specific on-chain mistake (Welcome to Video, Bitcoin Fog), or a specific cooperation breakthrough (Hansa administrator arrest in Germany seeded Operation Bayonet). The protocol is robust; the operator is the weak link.
What can a CISO take away from these takedowns?
Three things. (1) Ransomware affiliates and initial-access brokers are the most-prosecuted dark web roles right now; the on-chain payment trail is the single largest deanonymization vector and incident reporting feeds it directly. (2) Continuous offensive testing reduces the attack-surface signals that initial-access-broker listings monetize; a PTaaS engagement with regular external coverage is one of the most direct counters. (3) The compliance controls that satisfy SOC 2, ISO 27001, PCI DSS 4.0, NIS2, or DORA also raise the cost of being a viable target for a ransomware affiliate; Stingrai's compliance work maps to those controls.
Where can I follow ongoing dark web takedowns?
Primary sources: DOJ Office of Public Affairs, FBI press releases, Europol newsroom, UK National Crime Agency news, Treasury OFAC press releases, and the Chainalysis blog and TRM Labs blog for on-chain attribution case studies. Andy Greenberg's Tracers in the Dark is the most accessible book-length reference on financial-tracing methodology. For the broader credential-theft economy that drives ransomware-affiliate revenue, see Stingrai's Compromised Credential Statistics 2026 and Dark Web Data Pricing 2026 for the buyer-side pricing context.
References
U.S. Department of Justice, Office of Public Affairs. South Korean National and Hundreds of Others Charged Worldwide in the Takedown of the Largest Darknet Child Pornography Website, Which was Funded by Bitcoin. October 16, 2019. https://www.justice.gov/archives/opa/pr/south-korean-national-and-hundreds-others-charged-worldwide-takedown-largest-darknet-child. Welcome to Video indictment of Son Jong-woo; 337 arrests in 38 countries; 23 child victims rescued; Chainalysis Reactor central to attribution.
Europol. Massive blow to criminal Dark Web activities after globally coordinated operation. July 20, 2017. https://www.europol.europa.eu/media-press/newsroom/news/massive-blow-to-criminal-dark-web-activities-after-globally-coordinated-operation. Operation Bayonet against AlphaBay and Hansa.
U.S. Department of the Treasury. Treasury Sanctions Russia-Based Hydra, World's Largest Darknet Market, and Ransomware-Enabling Virtual Currency Exchange Garantex. Press release JY0701, April 5, 2022. https://home.treasury.gov/news/press-releases/jy0701. Hydra Market sanctions designation; ~US$5.2B cumulative volume; 17M customers; 19,000+ vendor accounts.
U.S. Department of the Treasury. Treasury Sanctions Genesis Market. Press release JY1388, April 5, 2023. https://home.treasury.gov/news/press-releases/jy1388. Genesis Market designation; coordinated with Operation Cookie Monster.
U.S. Department of the Treasury. Treasury Designates Roman Semenov, Co-Founder of Sanctioned Virtual Currency Mixer Tornado Cash. Press release JY1702, August 23, 2023. https://home.treasury.gov/news/press-releases/jy1702. Tornado Cash co-founder designation.
UK National Crime Agency. International investigation disrupts the world's most harmful cyber crime group. February 20, 2024. https://www.nationalcrimeagency.gov.uk/news/nca-leads-international-investigation-targeting-worlds-most-harmful-ransomware-group. Operation Cronos LockBit takedown phase 1.
UK National Crime Agency. LockBit leader unmasked and sanctioned. May 7, 2024. https://www.nationalcrimeagency.gov.uk/news/lockbit-leader-unmasked-and-sanctioned. Identification of LockBitSupp as Dmitry Khoroshev; US$10M reward.
Europol. Largest ever operation against botnets hits dropper malware ecosystem. May 30, 2024. https://www.europol.europa.eu/media-press/newsroom/news/largest-ever-operation-against-botnets-hits-dropper-malware-ecosystem. Operation Endgame; 100 servers, 2,000+ domains, 4 arrests.
Europol. Key figures behind Phobos and 8Base ransomware arrested in international cybercrime crackdown. February 11, 2025. https://www.europol.europa.eu/media-press/newsroom/news/key-figures-behind-phobos-and-8base-ransomware-arrested-in-international-cybercrime-crackdown. Operation Phobos Aetor; 4 Russian nationals arrested in Phuket, Thailand.
Europol. Key figure behind major Russian-speaking cybercrime forum targeted in Ukraine. July 23, 2025. https://www.europol.europa.eu/media-press/newsroom/news/key-figure-behind-major-russian-speaking-cybercrime-forum-targeted-in-ukraine. XSS forum administrator arrest in Kyiv; €7M+ illicit profits.
Europol. Steal, Deal, Repeat: Cybercriminals cash in on your data (IOCTA 2025). June 2025. https://www.europol.europa.eu/media-press/newsroom/news/steal-deal-repeat-cybercriminals-cash-in-your-data. Internet Organised Crime Threat Assessment 2025.
U.S. Drug Enforcement Administration. International law enforcement operation targeting opioid traffickers on the Darknet results in over 170 arrests worldwide and the seizure of weapons, drugs and over $6.5 million. September 22, 2020. https://www.dea.gov/press-releases/2020/09/22/international-law-enforcement-operation-targeting-opioid-traffickers. Operation DisrupTor; 179 arrests across 7 countries.
U.S. Federal Bureau of Investigation. Operation Endgame: Coordinated Worldwide Law Enforcement Action Against Network of Cybercriminals. May 30, 2024. https://www.fbi.gov/news/press-releases/operation-endgame-coordinated-worldwide-law-enforcement-action-against-network-of-cybercriminals. FBI corroboration of Operation Endgame.
U.S. Federal Bureau of Investigation, Internet Crime Complaint Center (IC3). 2024 Internet Crime Report. April 2025. https://www.ic3.gov/AnnualReport/Reports/2024_IC3Report.pdf. 859,532 complaints, US$16.6B losses, 67 new ransomware variants, 3,156 ransomware complaints.
U.S. Department of Justice. Ohio Resident Pleads Guilty to Operating Darknet-Based Bitcoin Mixer that Laundered Over $300 Million. August 18, 2021. https://www.justice.gov/archives/opa/pr/ohio-resident-pleads-guilty-operating-darknet-based-bitcoin-mixer-laundered-over-300-million. Larry Dean Harmon Helix mixer plea.
U.S. Department of Justice / Eastern District of Virginia. United States v. Conor Brian Fitzpatrick. March 2023 onward. https://www.justice.gov/usao-edva/united-states-v-conor-brian-fitzpatrick. BreachForums founder court record.
Chainalysis. 2026 Crypto Crime Report Introduction. February 2026. https://www.chainalysis.com/blog/2026-crypto-crime-report-introduction/. US$154B illicit address receipts in 2025; US$820M ransomware on-chain payments.
Chainalysis. Bitcoin Fog Case Confirms Chainalysis Analytics is Reliable and Admissible in Court. March 2024. https://www.chainalysis.com/blog/bitcoin-fog-daubert-hearing-chainalysis/. Daubert ruling on Chainalysis Reactor.
Steven J. Murdoch and George Danezis. Low-Cost Traffic Analysis of Tor. IEEE Symposium on Security and Privacy, 2005. https://murdoch.is/papers/oakland05torta.pdf. Foundational traffic-correlation paper.
NDSS Symposium. Flow Correlation Attacks on Tor Onion Service Sessions with Sliding Subset Sum. 2024. https://www.ndss-symposium.org/wp-content/uploads/2024-337-paper.pdf. Modern correlation-attack research against onion services.
The Tor Project. Thoughts and Concerns about Operation Onymous. November 9, 2014. https://blog.torproject.org/thoughts-and-concerns-about-operation-onymous/. Tor Project response to 2014 17-arrest operation.
National Security Archive. Declaration of Christopher Tarbell, United States of America v. Ross Ulbricht. Filed September 5, 2014, Southern District of New York. https://nsarchive.gwu.edu/document/22361-document-08-declaration-christopher-tarbell. FBI affidavit on Silk Road server discovery.
Wikipedia (verified against primary court filings). Operation Bayonet (darknet). https://en.wikipedia.org/wiki/Operation_Bayonet_(darknet). Cross-reference for the 2017 AlphaBay and Hansa takedown.
Wikipedia (verified against primary FBI press releases). Operation Pacifier. https://en.wikipedia.org/wiki/Operation_Pacifier. Playpen NIT deployment, 2015.
The Hacker News. FBI Cracks Down on Genesis Market: 119 Arrested in Cybercrime Operation. April 5, 2023. https://thehackernews.com/2023/04/fbi-cracks-down-on-genesis-market-119.html. Operation Cookie Monster summary corroborating DOJ press release.
BleepingComputer. FBI seizes Cracked.io, Nulled.to hacking forums in Operation Talent. January 30, 2025. https://www.bleepingcomputer.com/news/security/fbi-seizes-crackedio-nulledto-hacking-forums-in-operation-talent/. Operation Talent details.
Krebs on Security. NY Man Charged as 'Pompompurin,' the Boss of BreachForums. March 17, 2023. https://krebsonsecurity.com/2023/03/feds-charge-ny-man-as-breachforums-boss-pompompurin/. Conor Brian Fitzpatrick arrest.
Krebs on Security. Who Got Arrested in the Raid on the XSS Crime Forum? August 2025. https://krebsonsecurity.com/2025/08/who-got-arrested-in-the-raid-on-the-xss-crime-forum/. XSS administrator candidate identification.
Elliptic. US sanctions Garantex exchange and Hydra dark web marketplace following seizure of Hydra by German authorities. April 2022. https://www.elliptic.co/blog/5-billion-darknet-market-hydra-seized-by-german-authorities. Hydra cumulative volume and 80% darknet-market share in 2021.
Atlas21. Bitcoin Fog case: Sterlingov convicted and Chainalysis deemed 'reliable'. March 2024. https://atlas21.com/bitcoin-fog-case-sterlingov-convicted-and-chainalysis-deemed-reliable/. Sterlingov conviction summary.
Andy Greenberg. Tracers in the Dark: The Global Hunt for the Crime Lords of Cryptocurrency. Doubleday, 2022. https://andygreenberg.net/. Long-form reference on IRS-CI blockchain forensics methodology, Tigran Gambaryan, and Chris Janczewski.
The Record (Recorded Future News). Two Russian nationals arrested in takedown of Phobos ransomware infrastructure. February 2025. https://therecord.media/phobos-ransomware-takedown-arrests-russian-nationals. Operation Phobos Aetor corroboration.
The Record (Recorded Future News). Ohio man behind Helix cryptocurrency mixer gets 3-year sentence. November 2024. https://therecord.media/ohio-man-helix-crypto-sentenced. Larry Dean Harmon sentencing.
The Hacker News. US Treasury Lifts Tornado Cash Sanctions Amid North Korea Money Laundering Probe. March 2025. https://thehackernews.com/2025/03/us-treasury-lifts-tornado-cash.html. Tornado Cash sanctions delisting.
Help Net Security. 4 new LockBit-related arrests, identities of suspected Evil Corp members, affiliates revealed. October 2, 2024. https://www.helpnetsecurity.com/2024/10/02/lockbit-evil-corp-arrests-sanctions/. Operation Cronos Phase 3 details.