A 2025 episode of NCIS opened with a federal agent typing "search the dark web" into a Hollywood-style command-line interface, watching a green-on-black progress bar fill, and announcing seconds later that the suspect's name had been "found on Tor." The actual Tor protocol does not have a search bar. Tor is not a database. There is no "the dark web" to search. The scene is a useful prop because it telegraphs danger to a viewer who does not need to learn what an overlay network is. It is also, as a description of what actually happens in a dark-web investigation, fiction.
This post replaces that fiction with the primary measurement literature. It walks through the ten dark-web myths that show up most often in journalism, in board-deck threat briefings, and in pop-culture references. Each myth is paired with what the academic and law-enforcement record actually reports. The studies cited are public, the takedowns are court-record, and the Tor metrics dashboards are open data published by the Tor Project. Stingrai's research team has published 18 CVEs and works regularly with clients who need an accurate threat model rather than a cinematic one. This is the third entry in our four-part dark-web series, alongside How Law Enforcement Tracks Dark Web Criminals, Top Dark Web Marketplaces in 2026, Dark Web Data Pricing in 2026, and How Anonymous Is the Dark Web.
TL;DR: ten dark-web myths and the data that contradicts them
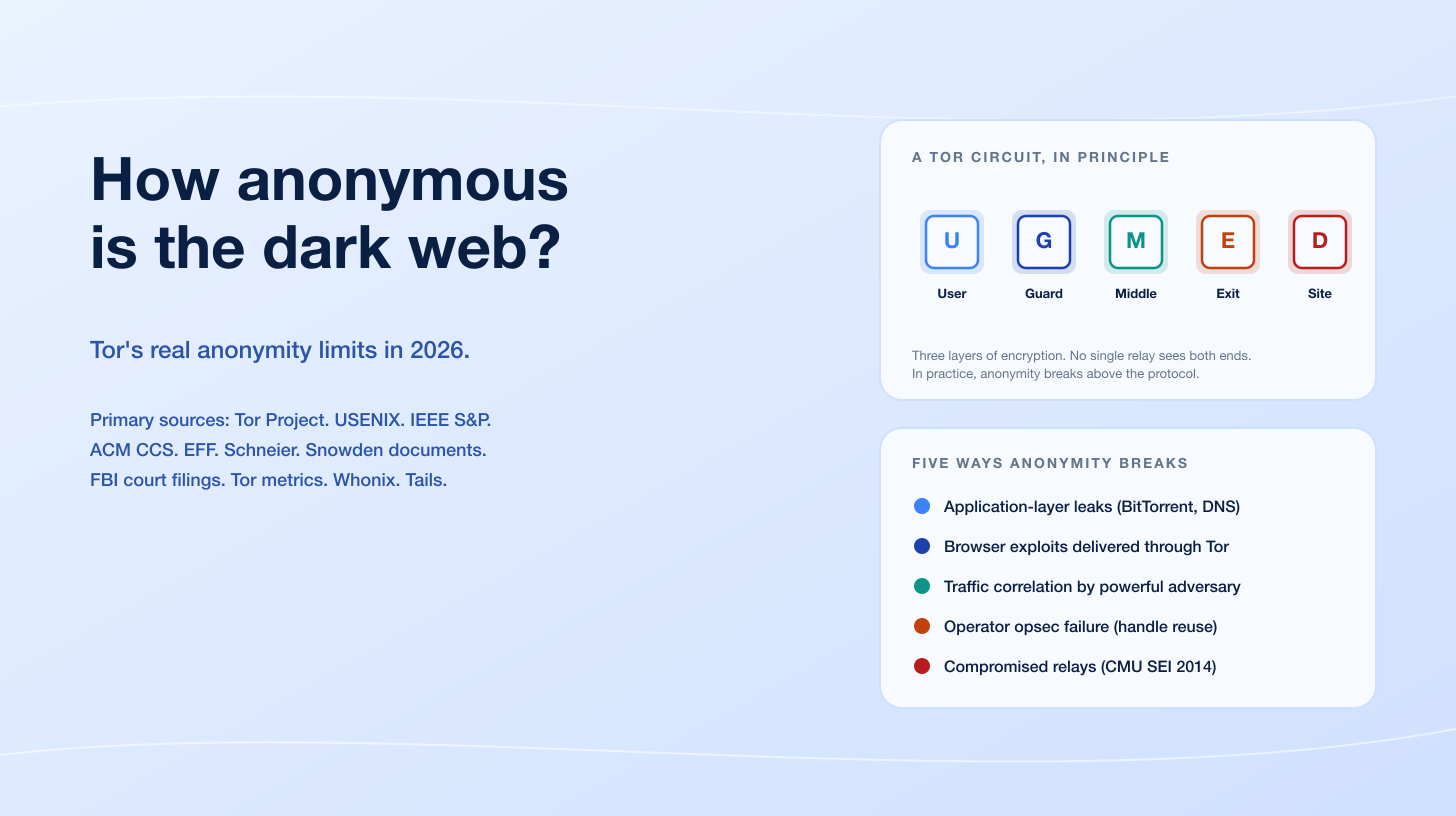
Myth 1: the dark web is huge. Reality: Tor metrics directories see roughly 150,000 to 300,000 unique v3 onion service descriptors on a typical day in 2025 against Google's indexed surface-web population of ~50 billion pages. The "deep web is 500x the surface web" line traces to Bergman 2001 and conflates the deep web with the dark web; the two are not the same.
Myth 2: most dark-web content is illegal. Reality: Terbium Labs' 2016 random-sample study of 400 active onion sites found roughly 55% legal content (mirrors of legal sites, journalism, mail, privacy tools, legal forums) and 45% illegal. Daniel Moore and Thomas Rid's 2016 King's College London study of 5,205 sites found a higher illegal share but used a different sampling method that excluded inactive and mirror sites.
Myth 3: Tor is for criminals. Reality: Eric Jardine, Andrew Lindner, and Gareth Owenson, PNAS 2020, measured that ~85% of Tor activity is plain-web browsing routed through Tor for privacy or censorship circumvention, with onion-service engagement at ~6.7% of daily Tor activity. The Tor Project's 2025 anti-censorship update reports heavy use of Snowflake, obfs4, and WebTunnel in Iran, Russia, and Belarus.
Myth 4: all darknet markets sell drugs and guns. Reality: the largest 2023 takedown by user count was Genesis Market, a stolen-credential and browser-fingerprint shop with ~1.5M bots, ~2M identities, and ~80M credentials catalogued. Mike McGuire's University of Surrey study (Bromium, 2019) found that ~40% of dark-net hacking-service vendors offered targeted attacks on Fortune 500 or FTSE 100 organizations, with banking (34%), e-commerce (20%), healthcare (15%), and education (12%) the most-named verticals.
Myth 5: the dark web is anonymous. Reality: Tor protects against single-network observers. It does not protect against application-layer leaks (Egerstad 2007), browser exploits delivered through Tor (NSA EgotisticalGiraffe / Operation Pacifier), traffic correlation by global passive adversaries (Murdoch & Danezis IEEE S&P 2005, Sun et al. RAPTOR USENIX 2015, Kwon et al. USENIX 2015), operator OPSEC failures, or compromised relays at scale (CMU SEI 2014).
Myth 6: Bitcoin on the dark web is untraceable. Reality: in April 2022, the US Treasury sanctioned the Hydra darknet market and disclosed ~US$5.2B in lifetime cryptocurrency flow traced through chain analysis, identifying 100+ virtual currency addresses. In November 2024, Bitcoin Fog operator Roman Sterlingov was sentenced to 12.5 years and ordered to pay US$395,563,025 in restitution after Chainalysis Reactor evidence helped attribute ~1.2M BTC of laundered flow.
Myth 7: anyone can be hacked from the dark web. Reality: dark web markets sell tools, kits, and credentials. They do not sell omnipotence. McGuire 2019 found that 75%+ of dark-net hacking products were tools or services that still required a human operator. Microsoft Threat Intelligence's reporting on Octo Tempest shows that even with off-the-shelf tooling, real intrusions are operator-driven.
Myth 8: the dark web is a single place. Reality: Tor onion services account for the dominant share of dark-web research and journalism, but I2P, Freenet, and ZeroNet are distinct overlay networks with different threat models, different sizes, and different communities. They are not interoperable and not co-extensive.
Myth 9: visiting the dark web is illegal. Reality: Tor is legal in the United States, Canada, the United Kingdom, Australia, and most of the European Union. It is restricted or blocked by China, Iran, Belarus, and a handful of other authoritarian states. The activity conducted through Tor may be illegal regardless of jurisdiction; using Tor itself, in most democracies, is not.
Myth 10: law enforcement cannot do anything about the dark web. Reality: ten named dark-web takedowns since 2013 are documented in DOJ, Europol, and OFAC public records, including Silk Road (2013), Operation Onymous (2014), AlphaBay/Hansa (2017), DeepDotWeb (2019), DarkMarket (2021), Hydra (2022), Genesis Market (2023), BreachForums (2023), and BreachForums v2 (2024). The asymmetry is operator-side: running a hidden service for years requires operational discipline that real operators rarely sustain.
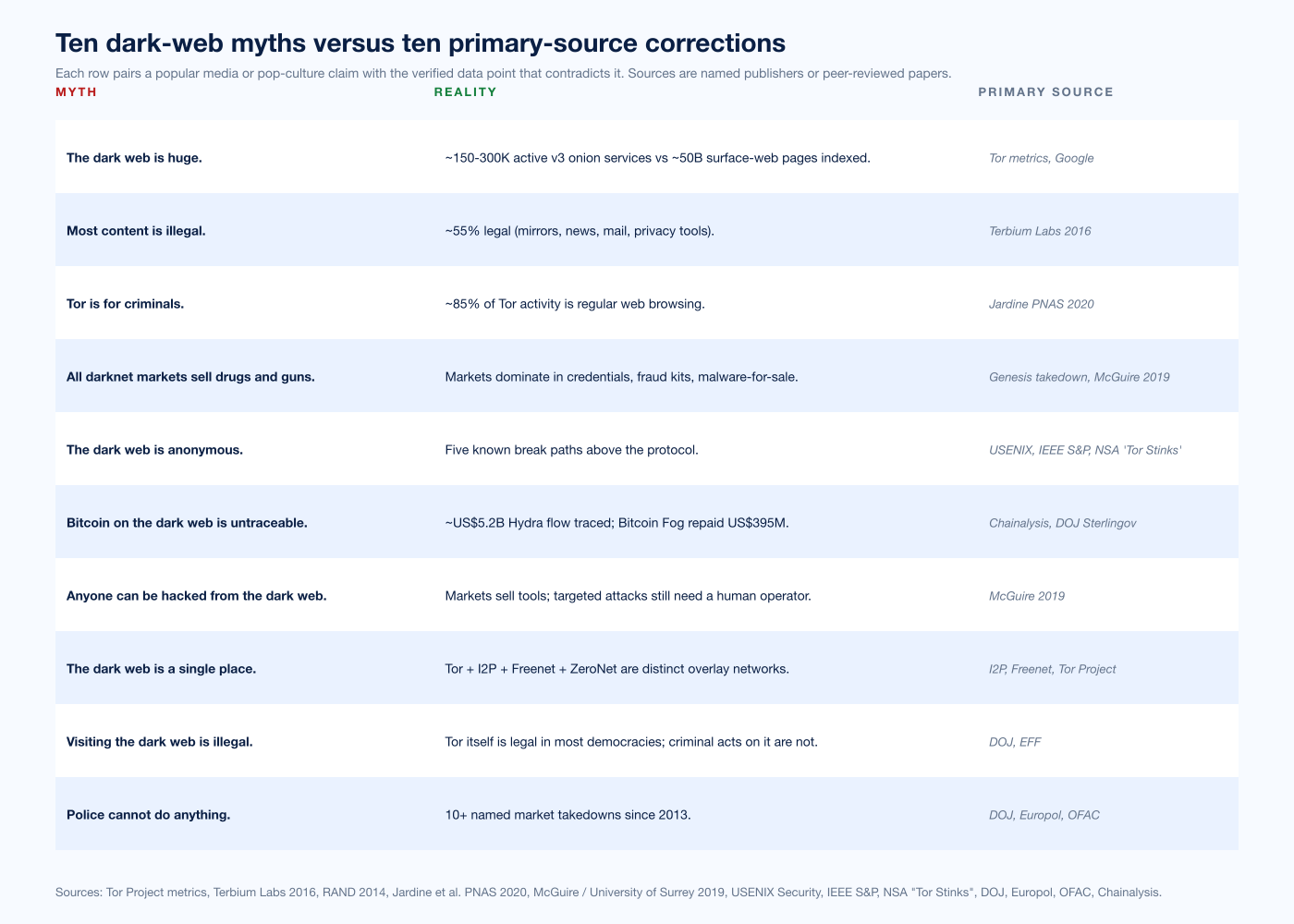
Figure 1: Each row pairs a popular dark-web myth with the verified primary-source data point that contradicts it. Sources are named publishers or peer-reviewed papers. The remainder of this post walks through each row in order.
Why these myths persist
Three structural reasons keep dark-web myths in circulation. First, the dark web is hard to measure: a public web crawl catalogues 100% of what Google indexes by definition, while a dark-web crawl finds only the onion services it can discover, and most onion services are deliberately discoverable only by URL share. Hyperion Gray's 2018 dark-web crawl indexed roughly 10% of catalogued onion services. The remaining 90% may be mirrors, defunct, or simply unlinked from any crawl seed.
Second, journalism on the dark web tends to amplify the most attention-grabbing examples and underweight the quiet majority. A SecureDrop installation at The New York Times, a .onion mirror of the BBC, or a private encrypted mail service has the same protocol-level signature as a drug market, and it is easier to write a column on contraband than on the absence of contraband.
Third, the popular conflation of "deep web" with "dark web" inflates apparent size. Bergman's 2001 paper "The Deep Web: Surfacing Hidden Value" coined the deep-web term to describe database-backed pages that search engines do not crawl (online banking, paywalled archives, university library catalogues). The deep web is genuinely large; the dark web, in the Tor / I2P / Freenet sense, is a small slice of the deep web. The "500 times the surface web" headline is about the deep web. It does not transfer to dark-web onion services without abusing the source.
Myth 1: The dark web is huge
The most common dark-web statistic in journalism is some version of "the dark web is 96% of the internet" or "the dark web is 500 times the surface web." Neither has primary-source backing in any peer-reviewed study. Both trace back to Bergman 2001 and to a misreading of the deep web / dark web distinction.
The actual measurement record is more modest. The Tor Project's hidden-services-dirs-v3-onions-seen metric reports the count of unique v3 onion service descriptors observed by Tor's hidden-service directory authorities on each day. As of 2025, that figure typically ranges between 150,000 and 300,000 daily, with daily fluctuations driven by service churn, mirror sites, and ephemeral test instances. The original v2 onion services were retired by the Tor Project on July 15, 2021; the v3 protocol uses 56-character ed25519-based addresses and is widely considered cryptographically intact in 2026.
Compare against the public web. Google has publicly stated that its search index covers "hundreds of billions" of pages, with most credible estimates landing around 50 billion actively indexed. WorldWideWebSize.com tracks daily index estimates that bounce between 30 and 60 billion pages depending on Google indexing dynamics. That puts the active dark-web population at roughly 0.0006% of the active surface web by service or page count. By total content volume, the comparison is harder because most onion services host static content while surface-web sites are often dynamic, but the order-of-magnitude difference is preserved.
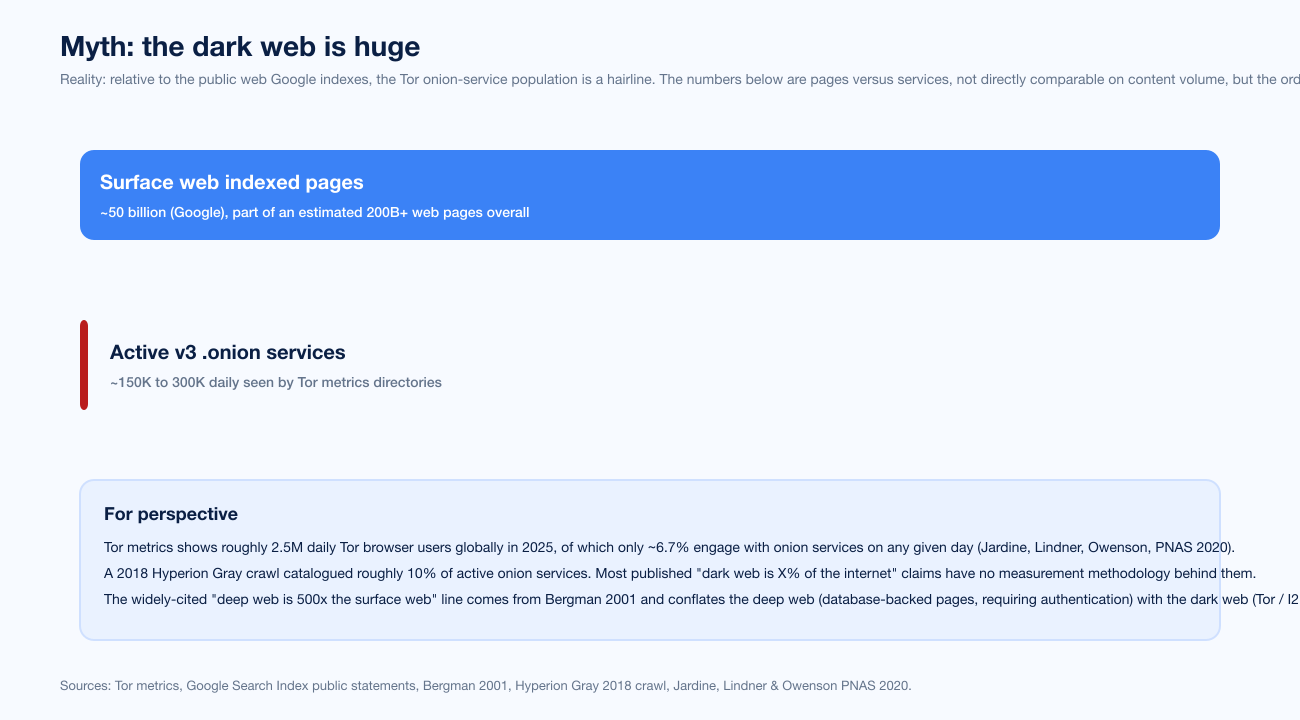
Figure 2: Visualizing the size gap. The surface-web bar (~50B pages) takes the full image width; the dark-web bar (~150-300K active v3 onion services) renders as a hairline. The widely-cited "500x" line conflates deep web with dark web.
The Hyperion Gray 2018 Dark Web Map crawl recorded approximately 6,608 onion sites considered "active" in their methodology. Onion-service measurement firms like Recorded Future and Flashpoint typically publish higher single-day figures, on the order of tens of thousands of "interesting" services, but those numbers are hand-curated for relevance to law-enforcement and threat-intelligence customers, not exhaustive crawls.
The bottom line: the dark web is real. It is not large in any meaningful absolute sense relative to the surface web. Headlines that imply otherwise have not done the measurement work the claim requires.
Myth 2: Most dark-web content is illegal
The cleanest piece of evidence on dark-web content distribution is Terbium Labs' 2016 study "The Truth About the Dark Web." Terbium Labs (later acquired by Deloitte in 2021) randomly sampled 400 active onion services and classified their content. The study found that approximately 55% of sampled onion sites hosted legal content (mirrors of legal websites, journalism, search engines, privacy tools, mail services, forums, legal adult content) and 45% hosted illegal content (drug marketplaces, fraud shops, malware-for-sale, weapons, counterfeit goods, exploitation material). Of the illegal share, more than 75% were marketplaces, and roughly 45% of marketplace listings were drug-related.
A widely-cited counterpoint comes from Daniel Moore and Thomas Rid (King's College London, 2016), who classified 5,205 onion sites and reported a higher illegal share, around 57% of sites with active content carrying illegal classifications. The two studies disagree because their sampling methods disagree. Terbium drew a random sample including inactive and mirror sites; Moore and Rid filtered for active content first, which inflates the illegal share by removing the long tail of legal-but-quiet onion services. Both numbers are defensible. Neither supports the "dark web is 96% illegal" headline, which has no measurement basis at all.
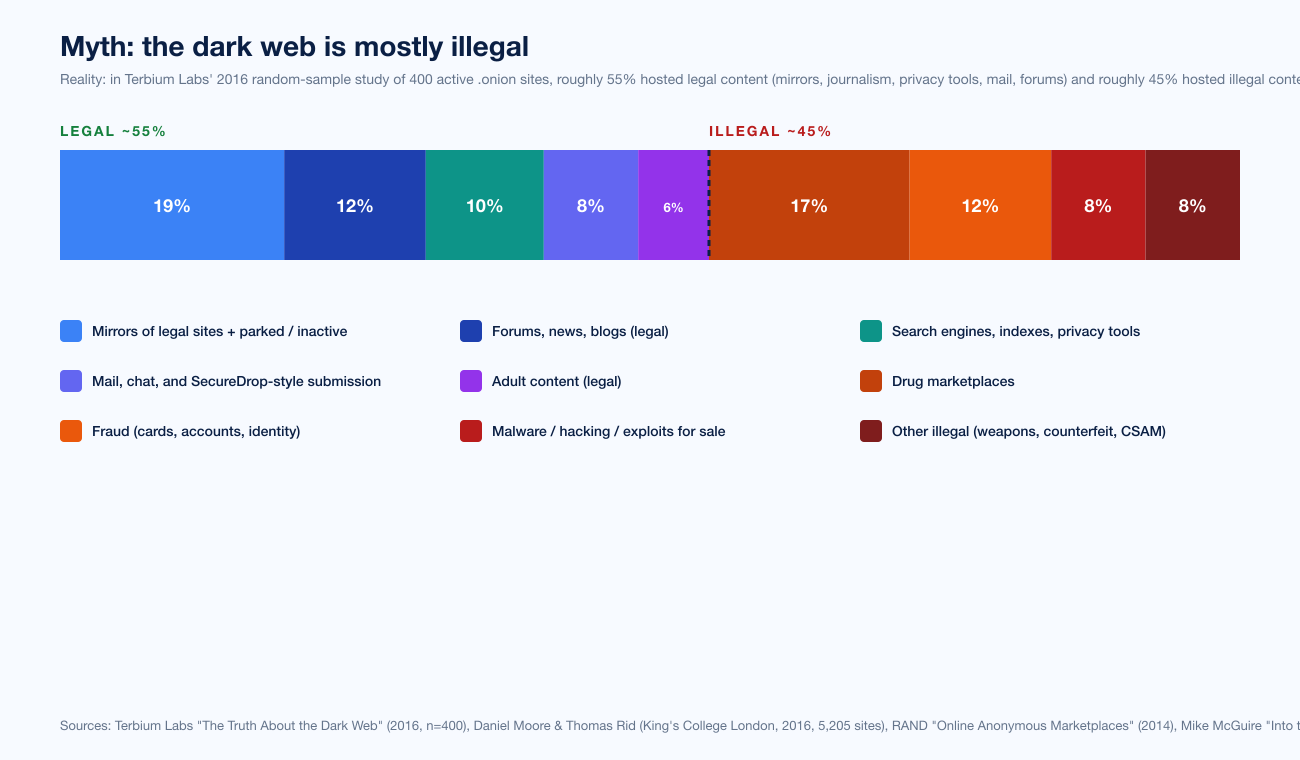
Figure 3: Stacked bar of dark-web content classification per Terbium Labs' 2016 random-sample of 400 onion sites. The dashed vertical line marks the legal / illegal split. Drug marketplaces are the dominant single illegal category.
Mike McGuire's Into the Web of Profit: Behind the Dark Net Black Mirror (Bromium / University of Surrey, 2019) reported a 20% rise in dark-net listings with direct enterprise-harm potential since 2016 and noted that targeted threats outnumbered off-the-shelf varieties roughly 2:1. McGuire's three-month embedded study of dark-net hacking communities found banking (34%), e-commerce (20%), healthcare (15%), and education (12%) as the most-named target verticals. That is consistent with what we covered in detail in Top Dark Web Marketplaces in 2026: the modern dark-net commerce mix is shifting from drugs toward credentials, fraud kits, and access services.
Myth 3: Tor is for criminals
Eric Jardine, Andrew Lindner, and Gareth Owenson published "The Potential Harms of the Tor Anonymity Network Cluster Disproportionately in Free Countries" in PNAS in November 2020. The paper measured Tor entry-relay traffic and reported that approximately 6.7% of daily Tor user engagement involves onion services at all. The remaining ~85% is plain web browsing through Tor, used overwhelmingly for privacy from local network observers, censorship circumvention, or simple online anonymity. Of the ~6.7% touching onion services, only a fraction is classified as likely illicit; the authors report higher illicit-share figures (~7.8%) in "free" countries (Freedom House classification) than in "not free" regimes (~4.8%), suggesting the political geography of Tor traffic is not what pop-culture coverage assumes.
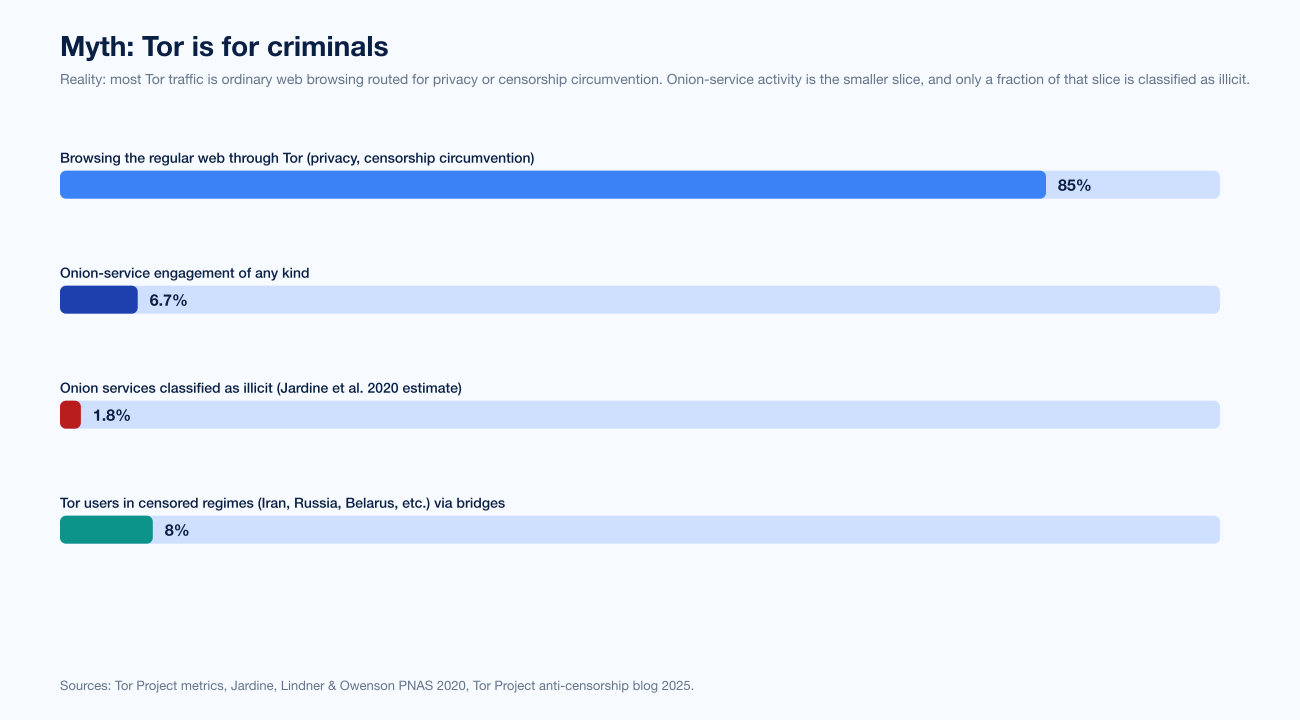
Figure 4: Tor user activity by share. Most Tor traffic is regular web browsing routed for privacy. Onion-service engagement is the smaller slice. Illicit onion-service traffic is a fraction of that.
The Tor Project's user statistics dashboard reports approximately 2 to 3 million daily relay users globally in 2025, with the United States, Germany, and Finland leading by absolute share. Russia, Iran, and Belarus lead in censored-region usage, where Snowflake, obfs4, and WebTunnel pluggable transports allow users to evade national Tor blocks. The Tor Project's 2025 anti-censorship blog documents heavy investment in WebTunnel, a transport that disguises Tor traffic as ordinary HTTPS, specifically because the Iranian and Russian governments have invested in detecting and blocking earlier transport types.
The list of named newsrooms running SecureDrop installations as a Tor hidden service is itself a refutation of "Tor is for criminals." SecureDrop is the de facto standard for receiving documents from anonymous sources; current installations include the Associated Press, The Washington Post, The New York Times, ProPublica, the CBC, BBC, NPR, Reuters, Bloomberg, The Guardian, Süddeutsche Zeitung, El Pais, and Wired, among others. The Freedom of the Press Foundation, which maintains SecureDrop, lists more than 80 newsrooms across 30+ countries running production SecureDrop instances. The New York Times .onion mirror was launched in 2017 specifically to provide uncensored access to readers in restrictive jurisdictions. The Electronic Frontier Foundation's Tor advocacy and the Tor Project's own Who Uses Tor? page document additional legitimate user populations: domestic-violence survivors evading abuser surveillance, LGBT users in jurisdictions with criminal prohibitions, business researchers performing competitive intelligence without leaking employer identity, and ordinary users who simply prefer not to be tracked.
Myth 4: All darknet markets sell drugs and guns
The pop-culture image of a dark-web market is Silk Road circa 2013: anonymous drug listings, a .onion address, Bitcoin payments, and Ross Ulbricht's pseudonymous "Dread Pirate Roberts" persona. That market has been gone for more than a decade. Two market generations have come and gone since.
The largest recent takedown by user count was Genesis Market in April 2023, seized in Operation Cookie Monster, a coordinated FBI / Europol action across 13 countries that produced 119 arrests and 208 searches in a 48-hour window on April 4-5, 2023. Genesis was not a drug market. Genesis was a stolen-credential and browser-fingerprint shop. Europol disclosed the platform's full database had ~1.5M bots supplying ~2M stolen identities and ~80M credentials, with active fingerprint inventory of ~460,000 bots at takedown. Genesis priced its bots from US$0.70 for low-value consumer accounts up to several hundred dollars per bot for online-banking access, and it bundled the stolen cookies, browser-fingerprint data, and session tokens needed to bypass anti-fraud controls.
The next-largest dark-net commerce category is straight credit-card and account-fraud shops. Joker's Stash, before its 2021 voluntary shutdown, listed ~40M payment cards stolen from US retail breaches. BriansClub, Trump's Dumps, FreshTools, and a long tail of card shops continue to occupy substantial dark-net commerce share. Mike McGuire's 2019 Surrey study found that of vendors selling targeted hacking services on dark-net forums, more than 40% offered Fortune 500 or FTSE 100 attack-as-a-service operations on request.
The drug-market category still exists. Hydra, the Russian-language successor to Silk Road and AlphaBay, was the world's largest darknet market until its German seizure in April 2022. Hydra accounted for ~75% of global darknet market revenue in 2021, with ~US$1.7B received that year. After Hydra's takedown, drug-market activity fragmented across smaller successors (OMG!OMG!, BlackSprut, Solaris, Rutor, and others), with no single market regaining Hydra's volume.
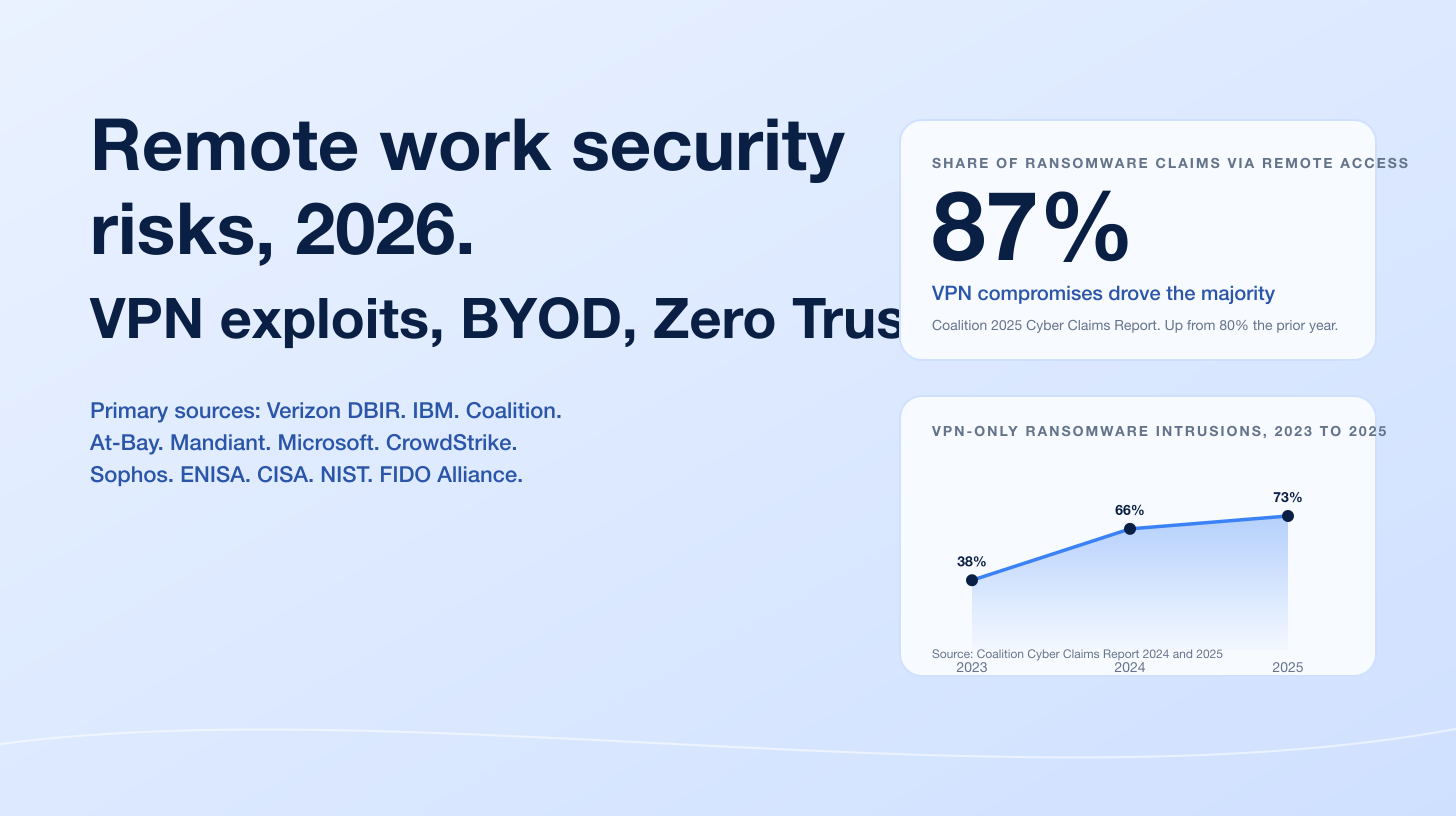
Myth 5: The dark web is anonymous
This is the myth covered in detail in our How Anonymous Is the Dark Web post; the short summary here is that Tor anonymity is real, narrow, and adversary-relative. The protocol does what its design paper (Dingledine, Mathewson, Syverson, USENIX Security 2004) says it does: it hides the user's IP from the destination, hides the destination from the user's ISP, and gives three layers of encryption so no single relay sees both ends. That property still holds in 2026.
What does not hold is anonymity above the protocol. Five known break paths cover every documented user-side and operator-side deanonymization on record:
Application-layer leaks. Dan Egerstad operated five Tor exit nodes for several months in 2007 and harvested cleartext credentials for more than 1,000 POP3 / IMAP accounts, including embassy and human-rights worker mailboxes. INRIA's 2010 paper Compromising Tor Anonymity Exploiting P2P Information Leakage documented BitTorrent over Tor leaking the user's real IP through tracker announces.
Browser exploits delivered through Tor. The NSA's EgotisticalGiraffe Firefox E4X type-confusion exploit broke Freedom Hosting users in August 2013; the FBI's Operation Pacifier deployed a Network Investigative Technique against Playpen visitors over 13 days in February-March 2015 and identified more than 1,300 real IP addresses.
Traffic correlation. Murdoch and Danezis (IEEE S&P 2005), Sun et al. RAPTOR (USENIX Security 2015) at the BGP level, Kwon et al. (USENIX Security 2015) reaching 88% deanonymization on monitored hidden services through circuit fingerprinting.
Operator OPSEC failure. Ross Ulbricht renamed his Stack Overflow account from his real name to "frosty" one minute after posting; the same Tor-via-PHP code appeared on the Silk Road server. He was arrested October 1, 2013 with the admin panel logged in.
Compromised relays. Carnegie Mellon University's Software Engineering Institute operated 115+ malicious Tor relays from January 30 through July 4, 2014; the data informed Operation Onymous (17 arrests, 400+ services seized) in November 2014.
The 2013 NSA "Tor Stinks" deck, leaked by Edward Snowden and published by The Guardian, is unusually candid about the limits of state-actor capability against Tor. The slide that says "we will never be able to deanonymize all Tor users all the time" is a population-scale concession; the slides that follow describe the workarounds, all of which are above the protocol.
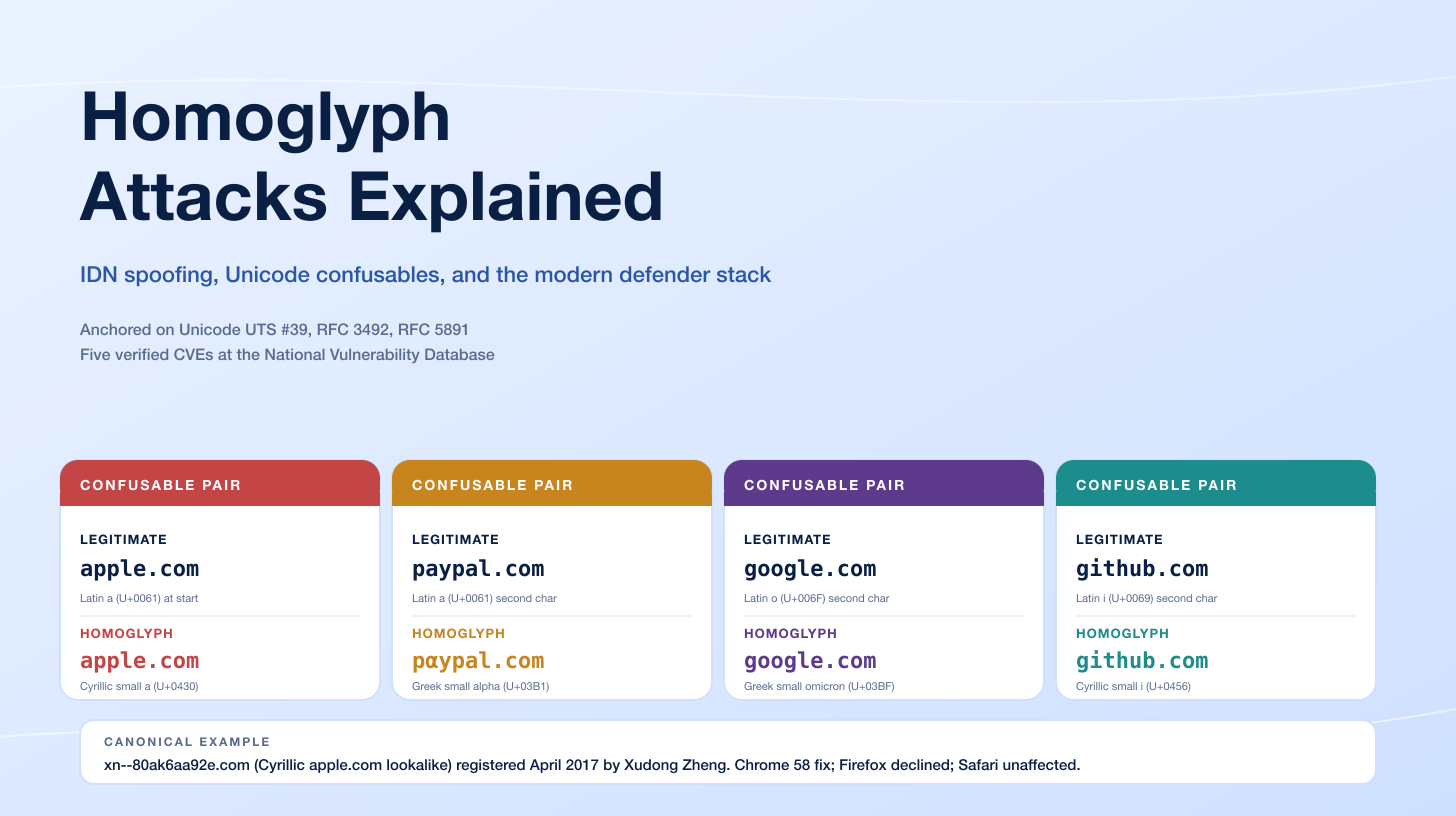
Myth 6: Cryptocurrency on the dark web is untraceable
This is the myth that has aged worst since 2017. Bitcoin is a public ledger. Every transaction is visible to anyone who runs a node. Once the chain analysis industry matured, the per-transaction anonymity property of dark-web cryptocurrency flow collapsed in slow motion.
The April 5, 2022 US Treasury OFAC designation of Hydra Market is the headline case. Treasury sanctioned Hydra concurrently with the German Federal Criminal Police's seizure of Hydra's servers in Germany, identified 100+ virtual currency addresses associated with Hydra operations, and disclosed that Hydra had received approximately US$5.2 billion in cryptocurrency since 2015. The German seizure included approximately US$25 million in seized Bitcoin from Hydra's wallets. OFAC's investigation also identified roughly US$8 million in ransomware proceeds (Ryuk, Sodinokibi, Conti) that had transited Hydra's accounts. Chainalysis published a companion analysis detailing the chain-of-funds attribution.
The Bitcoin Fog case is the second headline. Roman Sterlingov, the operator of the longest-running Bitcoin mixer in dark-web history, was convicted on March 12, 2024 on four money-laundering counts after a federal jury trial in Washington, DC, and sentenced on November 8, 2024 to 12.5 years in federal prison. Sterlingov was ordered to pay US$395,563,025 in restitution, to forfeit US$1.76 million in seized assets, and to relinquish control of a Bitcoin Fog wallet containing more than US$100 million. Bitcoin Fog had processed approximately 1.2 million BTC across its decade of operation (2011-2021), with chain-analysis attribution helping prosecutors trace flows. The Sterlingov case is the public benchmark for how chain-analysis evidence is admitted in a US criminal trial.
The Welcome to Video case (2019) and the Hydra OFAC documentation are part of the same evolution. Chainalysis, TRM Labs, and Elliptic each publish annual crypto-crime reports documenting their attribution capabilities; each year's report adds the previous year's mixer takedowns, sanctioned addresses, and successful chain-tracing prosecutions. Privacy coins like Monero, by contrast, retain meaningfully stronger transaction-level privacy properties; Bitcoin and Ethereum do not. Anyone operating a dark-web service today on the assumption that bitcoin alone provides anonymity is operating on a 2014 mental model.
Myth 7: Anyone can be hacked from the dark web
The fear that runs underneath this myth is that any small business, any individual, any random target can be ordered up like a pizza from a dark-net ransomware service. The data does not support that worry, even granting that dark-net commerce has matured.
McGuire's 2019 Surrey study found that approximately 75% of dark-net hacking-related products were tools, kits, or services that still required a human operator to deploy them. Custom malware-development services, exploit kits, phishing toolkits, and credential bundles are inputs to attacks; they are not turnkey targeted operations against an arbitrary victim. The remaining ~25%, including initial-access-broker listings and managed targeted-attack services, do exist; that is the McGuire finding that 40%+ of dark-net hacking vendors will accept Fortune 500 or FTSE 100 targeted-attack work on request. But "will accept work on request from a researcher embedded in a dark-net forum" is not the same as "any random victim is an automatic target."
Ransomware-as-a-service, which the press often associates with dark-web marketplaces, mostly transacts through invitation-only Telegram channels and dedicated forums, not through public marketplaces. Microsoft Threat Intelligence reporting on Octo Tempest, Mandiant M-Trends 2026, and CrowdStrike's 2026 Global Threat Report all document that real targeted intrusions are driven by human operators selecting a victim, not by vending-machine commerce. The dark-web markets feed the supply chain of credentials, kits, and access; they do not, on their own, decide who gets hit.
For a practical defensive posture, the Verizon 2025 Data Breach Investigations Report data is more informative than dark-web-market hype. Verizon reports that ~80% of confirmed breaches in 2025 involved either credentials, phishing, or vulnerability exploitation. The credentials sold on Genesis Market, the access broker listings, and the malware-as-a-service ecosystems all contribute to that 80%, but they do so as inputs into a process that still has a human attacker at the wheel.
Myth 8: The dark web is a single place
Tor accounts for the dominant share of dark-web research, journalism, and law-enforcement attention. It is not the only overlay network with anonymous-service properties.
I2P (the Invisible Internet Project) is a packet-level anonymizing overlay developed since 2003. Its onion-equivalent service identifiers are called "eepsites" and use unidirectional tunnels, with separate inbound and outbound paths through different relays. I2P's threat model is closer to a fully distributed mix network than to Tor's circuit-based model. The I2P daily user count is on the order of tens of thousands, smaller than Tor by a wide margin, but distinct in design.
Freenet (rebranded Hyphanet in 2023) is a censorship-resistant content-distribution network with an emphasis on anonymous publishing rather than anonymous browsing. Freenet content is sharded across the network and addressed by content hash; once published, content propagates and persists across nodes. Freenet's threat model addresses anonymous publication and uncensorable mirrors more directly than Tor.
ZeroNet, Lokinet, and the now-defunct Tribler each occupy slivers of the dark-web ecosystem with their own design tradeoffs. None of them is interoperable with Tor; an investigation against an I2P eepsite is not the same investigation as one against a Tor onion service, and law-enforcement agencies have to develop separate tooling for each.
The practical implication for a CISO is small: most threat-intelligence vendors collect from Tor onion services because that is where the volume is. The implication for a popular-culture argument is real: when an article says "the dark web," it almost always means Tor specifically, and an article that conflates Tor with I2P or Freenet is making a category error.
Myth 9: Visiting the dark web is illegal
In the United States, Canada, the United Kingdom, Australia, New Zealand, Japan, Germany, France, the Netherlands, and most of the European Union, downloading the Tor Browser and visiting onion services is legal. The Department of Justice, in its public guidance, treats Tor as a tool: criminal liability attaches to what a user does on Tor (purchasing controlled substances, viewing unlawful content, conspiring in fraud) rather than to the use of Tor itself.
A handful of authoritarian states do restrict or criminalize Tor use. China's Great Firewall actively blocks Tor relays and bridges, with enforcement against domestic users who circumvent the block. Iran has criminalized circumvention tools since 2022; Belarus has periodically restricted Tor access, particularly after political protests; Russia has partially blocked Tor since December 2021, with active blocking of Tor relays and pluggable transports. The Tor Project's 2025 report on staying ahead of censors documents the ongoing technical investment in WebTunnel and Snowflake to maintain access in those environments.
For ordinary US, Canadian, UK, or EU users, the practical answer is: using Tor is legal; doing illegal things on Tor is illegal. The activity is what creates criminal exposure, not the protocol.
Myth 10: Law enforcement cannot do anything about the dark web
The takedown record refutes this myth in detail. We covered the operator-side mechanics in How Law Enforcement Tracks Dark Web Criminals; here is the timeline of named operations a CISO can put in front of a board.
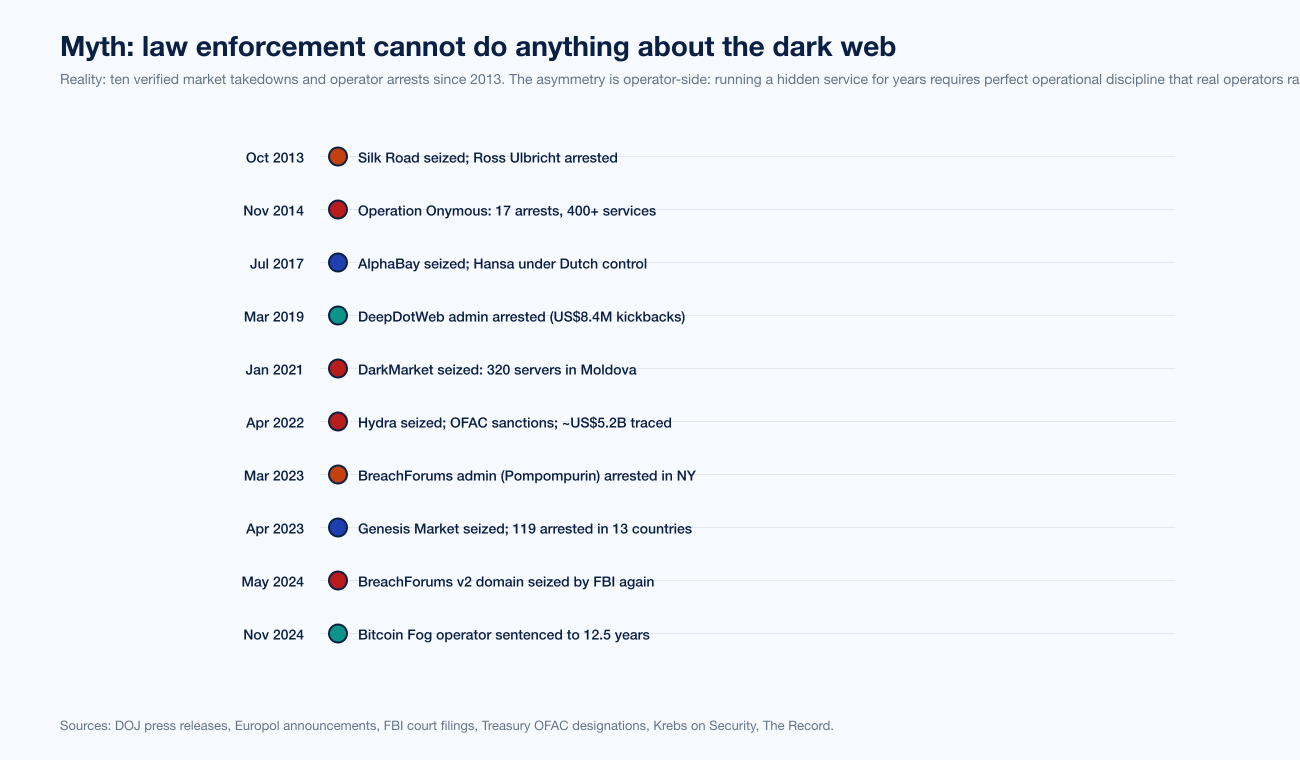
Figure 5: Named dark-web market takedowns and operator arrests, October 2013 through November 2024. Color groups by enforcement category. Sources: DOJ press releases, Europol announcements, FBI court filings, Treasury OFAC designations.
October 2013. Silk Road seized; Ross Ulbricht arrested at a San Francisco public library with the admin panel open. Sentenced May 2015 to two consecutive life terms plus 40 years.
November 2014. Operation Onymous, coordinated by Europol, FBI, and ICE. 17 arrests across the US and Europe. ~400 hidden services seized including Silk Road 2.0. The data foundation came partly from CMU SEI's malicious-relay project, per the Tor Project advisory of July 30, 2014.
July 2017. Operation Bayonet. AlphaBay seized by the FBI; founder Alexandre Cazes arrested in Bangkok on July 5, 2017 and found dead in custody on July 12. AlphaBay had transactions exceeding US$1 billion in cryptocurrencies. The Dutch police simultaneously seized Hansa on June 20 and operated it for 27 days as a honeypot to capture AlphaBay refugees migrating after the AlphaBay shutdown.
March 2019. DeepDotWeb administrators charged with money laundering for accepting US$8.4M in kickbacks for affiliate referrals to dark-web marketplaces. Tal Prihar pleaded guilty in 2021.
January 2021. DarkMarket seized by German police in coordination with Europol. ~320 servers in Moldova and Ukraine. The market had ~500,000 users and ~2,400 vendors.
April 2022. Hydra. German Federal Criminal Police seized servers; US Treasury OFAC sanctioned Hydra and identified 100+ wallet addresses with ~US$5.2B traced. Russia-headquartered Garantex was sanctioned simultaneously.
March 2023. BreachForums admin Conor Brian Fitzpatrick (alias "Pompompurin") arrested at his home in Peekskill, New York. Fitzpatrick pleaded guilty on July 13, 2023 and was resentenced on appeal in 2024 to a 36-month prison term. The clearnet domains were seized on June 23, 2023.
April 2023. Genesis Market seized in Operation Cookie Monster. 119 arrests and 208 searches across 13 countries on April 4-5, 2023.
May 2024. BreachForums v2 (revived after Pompompurin's arrest under new administrators) had its clearnet domains seized again by the FBI.
November 2024. Roman Sterlingov sentenced to 12.5 years and US$395.5M restitution for Bitcoin Fog operations.
That is ten named operations in eleven years against the highest-profile dark-web markets and infrastructure operators. The dark web is not unpoliceable. The asymmetry is operator-side: running a hidden service that interacts with hundreds of thousands of users for years requires perfect operational discipline across server configuration, payment infrastructure, forum cross-posting, and writing style. Real operators rarely sustain all four for the duration. The user side, by contrast, is largely beyond population-scale enforcement, which is what the NSA conceded in "Tor Stinks" and what the public investigation record continues to confirm.
What this means for security buyers
For a security leader, the dark web is a threat-intelligence input, not a threat in its own right. The credentials, fraud kits, and access listings that change hands on Genesis Market or BriansClub or in invite-only Telegram channels feed the credential-stuffing, account-takeover, and ransomware operations that show up on a SIEM dashboard the next day. The dark web is the supply side; the attack on your environment is the demand side. Defending against it means controlling what shows up on the supply side (employee credentials, leaked data, unauthorized access) rather than chasing the supply side itself.
Concretely, that means three things. First, monitor for your own organization's credentials and data on dark-web markets and forums. Most enterprise threat-intelligence vendors offer this as a service, and several open-source projects (Have I Been Pwned, SpyCloud, Recorded Future Identity Intelligence) cover the same ground. Second, treat compromised credentials as an inevitability and harden against post-credential-theft scenarios: enforce phishing-resistant multifactor authentication (FIDO2 / passkeys), reduce blast radius with least-privilege access, and instrument detection on lateral movement and unusual session activity. Third, run periodic penetration testing and adversary simulation against the assumption that the attacker already has valid credentials, because they often do.
The myths matter only insofar as they shape budget. A board that believes the dark web is a 96%-illegal megaspace will fund crawler tools that index a tiny corner of an already-tiny network. A board that believes the dark web is unanonymous on its own terms but accelerates supply-chain attacks against the rest of the business will fund the controls that actually reduce breach risk. The data supports the second framing.
Frequently Asked Questions
Is most of the dark web illegal?
No. Terbium Labs' 2016 random-sample study of 400 onion sites found roughly 55% legal content (mirrors, news, mail, search engines, privacy tools, legal forums, legal adult content) and 45% illegal content. Of the illegal share, drug marketplaces dominated. Daniel Moore and Thomas Rid's 2016 King's College London study reported a higher illegal share, around 57%, but used a different sampling method that excluded inactive and mirror sites. Both findings contradict the popular "dark web is 96% illegal" claim, which has no measurement basis.
How big is the dark web?
Tor metrics tracks roughly 150,000 to 300,000 unique v3 onion service descriptors on a typical day in 2025. That is against an estimated 50 billion Google-indexed surface-web pages. By active service or page count, the dark web is roughly 0.0006% of the surface web. The widely-cited "deep web is 500 times the surface web" line traces to Bergman 2001 and conflates the deep web (database-backed pages requiring authentication) with the dark web (Tor / I2P / Freenet); they are not the same.
Who actually uses Tor?
Eric Jardine, Andrew Lindner, and Gareth Owenson (PNAS 2020) measured that approximately 85% of Tor activity is regular web browsing routed through Tor for privacy or censorship circumvention. Onion-service engagement accounts for ~6.7% of daily Tor activity. Major newsrooms run SecureDrop installations as Tor hidden services, including the AP, The Washington Post, The New York Times, ProPublica, BBC, NPR, and Reuters. The Tor Project's 2025 anti-censorship reporting documents heavy use of Snowflake, obfs4, and WebTunnel by users in Iran, Russia, and Belarus.
Is using Tor illegal?
In the United States, Canada, the United Kingdom, Australia, and most of the European Union, using Tor is legal. The activity conducted through Tor may be illegal regardless of jurisdiction. A handful of authoritarian states (China, Iran, Belarus, Russia) restrict or actively block Tor and criminalize circumvention, with active blocking of Tor relays and pluggable transports.
Is the dark web actually anonymous?
Tor is anonymous against the threats its protocol was designed to defeat (single-network observers, the destination site if you do not log in, an attacker on your local Wi-Fi). It is not anonymous against five well-documented break paths above the protocol: application-layer leaks, browser exploits delivered through Tor, traffic correlation by global passive adversaries, operator OPSEC failures, and compromised relays at scale. See our companion post How Anonymous Is the Dark Web for the full breakdown.
Is Bitcoin on the dark web traceable?
Yes. The April 2022 US Treasury OFAC sanctioning of Hydra Market identified 100+ virtual currency addresses and disclosed approximately US$5.2 billion in cryptocurrency lifetime flow traced through chain analysis. In November 2024, Bitcoin Fog operator Roman Sterlingov was sentenced to 12.5 years and ordered to pay US$395.5 million in restitution after Chainalysis Reactor evidence helped attribute roughly 1.2 million BTC of laundered flow. Privacy coins like Monero retain meaningfully stronger transaction-level privacy properties; Bitcoin and Ethereum do not.
What was the largest dark-web takedown?
By cryptocurrency value, Hydra Market, seized April 2022 with approximately US$5.2 billion in lifetime cryptocurrency flow traced. By user count, Genesis Market, seized April 2023 in Operation Cookie Monster, with approximately 59,000 identified users, 119 arrests, and 208 searches across 13 countries. By revenue concentration, Hydra accounted for approximately 75% of global darknet market revenue in 2021 before its takedown.
What is the difference between the deep web and the dark web?
The deep web is the portion of the web that search engines do not index, including database-backed pages, paywalled content, online banking, university library catalogues, and authenticated SaaS applications. It is large; Bergman's 2001 paper estimated it at 500 times the size of the surface web. The dark web is a small slice of the deep web that requires special routing software (Tor, I2P, Freenet, ZeroNet) to access. Conflating the two inflates apparent dark-web size by orders of magnitude.
Can law enforcement actually take down dark-web markets?
Yes, repeatedly. Ten named takedowns since 2013 are documented in DOJ, Europol, and OFAC public records: Silk Road (2013), Operation Onymous (2014), AlphaBay/Hansa (2017), DeepDotWeb (2019), DarkMarket (2021), Hydra (2022), BreachForums (2023), Genesis Market (2023), BreachForums v2 (2024), and Bitcoin Fog operator sentencing (2024). The asymmetry is operator-side: running a hidden service for years requires operational discipline that real operators rarely sustain.
Should my organization monitor the dark web?
For most enterprise security programs, yes, but as a threat-intelligence input rather than as a defensive line. The credentials, fraud kits, and access listings that change hands on dark-web markets feed credential-stuffing, account-takeover, and ransomware operations against ordinary enterprises. Most enterprise threat-intelligence vendors offer dark-web monitoring as a service; defensive priorities should still focus on phishing-resistant MFA, least-privilege access, lateral-movement detection, and regular penetration testing rather than on the markets themselves.
Sources
Tor Project. "Tor Metrics: Onion Services Directory v3."
Tor Project. "Tor Metrics: Users."
Tor Project. "Staying Ahead of Censors in 2025."
Tor Project. "v2 Deprecation Timeline."
Eric Jardine, Andrew Lindner, Gareth Owenson. "The Potential Harms of the Tor Anonymity Network Cluster Disproportionately in Free Countries." PNAS, November 2020.
Terbium Labs. "The Truth About the Dark Web." 2016.
Daniel Moore and Thomas Rid. "Cryptopolitik and the Darknet." Survival, 2016 (King's College London).
RAND Corporation. "The Online Anonymous Marketplace Ecosystem." 2014.
Mike McGuire. "Into the Web of Profit: Behind the Dark Net Black Mirror." Bromium / University of Surrey, 2019.
University of Surrey press. "4 in 10 dark net cybercriminals selling targeted FTSE 100 or Fortune 500 hacking services."
Hyperion Gray. "Dark Web Map." 2018.
Bergman, Michael K. "The Deep Web: Surfacing Hidden Value." Journal of Electronic Publishing, 2001.
Roger Dingledine, Nick Mathewson, Paul Syverson. "Tor: The Second-Generation Onion Router." USENIX Security, 2004.
Steven J. Murdoch and George Danezis. "Low-Cost Traffic Analysis of Tor." IEEE S&P, 2005.
Yixin Sun et al. "RAPTOR: Routing Attacks on Privacy in Tor." USENIX Security, 2015.
Albert Kwon et al. "Circuit Fingerprinting Attacks." USENIX Security, 2015.
Stevens Manils et al. "Compromising Tor Anonymity Exploiting P2P Information Leakage." INRIA, 2010.
Tor Project. "Tor Security Advisory: Relay-Early Traffic Confirmation Attack." July 30, 2014.
The Guardian. "NSA and GCHQ target Tor network that protects anonymity of web users." October 4, 2013.
US Department of the Treasury. "Treasury Sanctions Russia-Based Hydra, World's Largest Darknet Market, and Ransomware-Enabling Virtual Currency Exchange Garantex." April 5, 2022.
Chainalysis. "OFAC Sanctions Hydra Following Shutdown of the Darknet Market."
Elliptic. "$5 billion darknet market Hydra seized by German authorities."
US Department of Justice. "Russian-Swedish Operator of 'Bitcoin Fog' Convicted of Money Laundering." March 12, 2024.
The Register. "Bitcoin Fog Sentencing." November 11, 2024.
Eurojust. "Operation Cookie Monster: Genesis Market Takedown."
BleepingComputer. "FBI seizes stolen credentials market Genesis in Operation Cookie Monster."
FBI. "AlphaBay Takedown." July 2017.
Wikipedia. "Operation Bayonet (darknet)."
Europol. "DarkMarket: world's largest illegal dark web marketplace taken down."
US DOJ. "Two Administrators of DeepDotWeb Arrested for Money Laundering."
Krebs on Security. "NY Man Charged as 'Pompompurin,' the Boss of BreachForums."
Bitdefender. "'Pompompurin' resentenced: BreachForums creator heads back behind bars."
SecureDrop. "Newsrooms."
EFF. "Tor: Anonymity Online."
Tor Project. "Who Uses Tor?."
Tor Project. "Tor Censorship in Russia."
Microsoft Threat Intelligence. "Octo Tempest crosses boundaries to facilitate extensive attacks."
Verizon. "2025 Data Breach Investigations Report."
Wikipedia. "Silk Road (marketplace)."