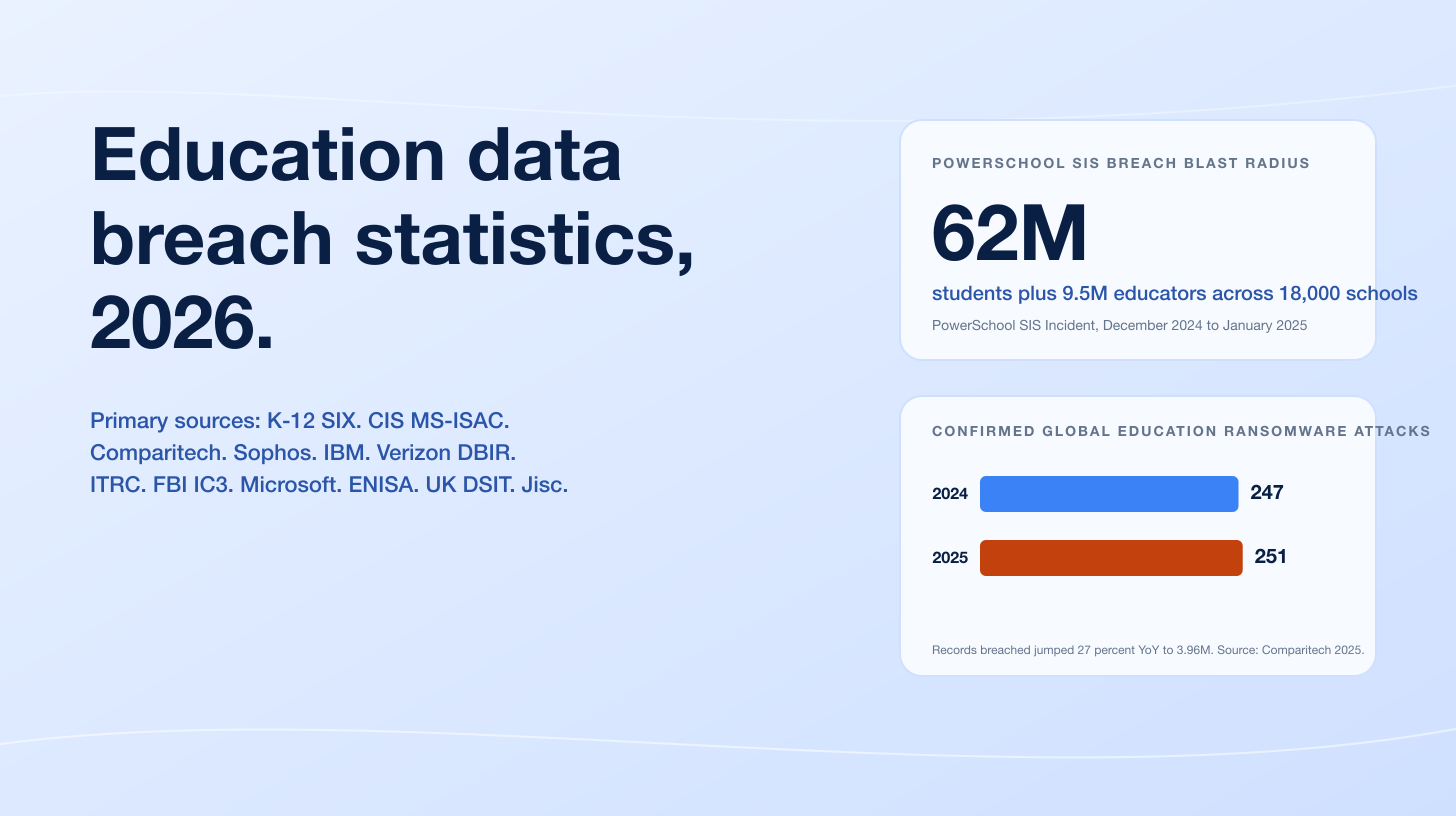
DDoS scaled into territory the public internet has never seen before in 2025. Cloudflare's autonomous DDoS defense systems blocked 20.5 million attacks in Q1 2025 alone, a 358 percent year-over-year jump that already exceeded 96 percent of Cloudflare's full-year 2024 total of 21.3 million. The Q4 2025 report showed an average of 5,376 attacks mitigated every hour and a public-record 31.4 Tbps Aisuru-Kimwolf burst that lasted 35 seconds, eclipsing the prior 5.6 Tbps Aisuru attack disclosed in October 2024 by more than five-fold in 13 months. Microsoft Azure mitigated its own record 15.72 Tbps Aisuru-class flood targeting an Australian customer on October 24, 2025, with 3.64 billion packets per second sourced from 500,000+ IP addresses. Sector targeting remained familiar but more intense: financial services held 34 percent share at Akamai's L3/L4 telemetry, telecommunications and carriers were the top sector for hyper-volumetric attacks at Cloudflare, and APAC financial services grew from 11 percent to 38 percent of regional volumetric attacks year over year.
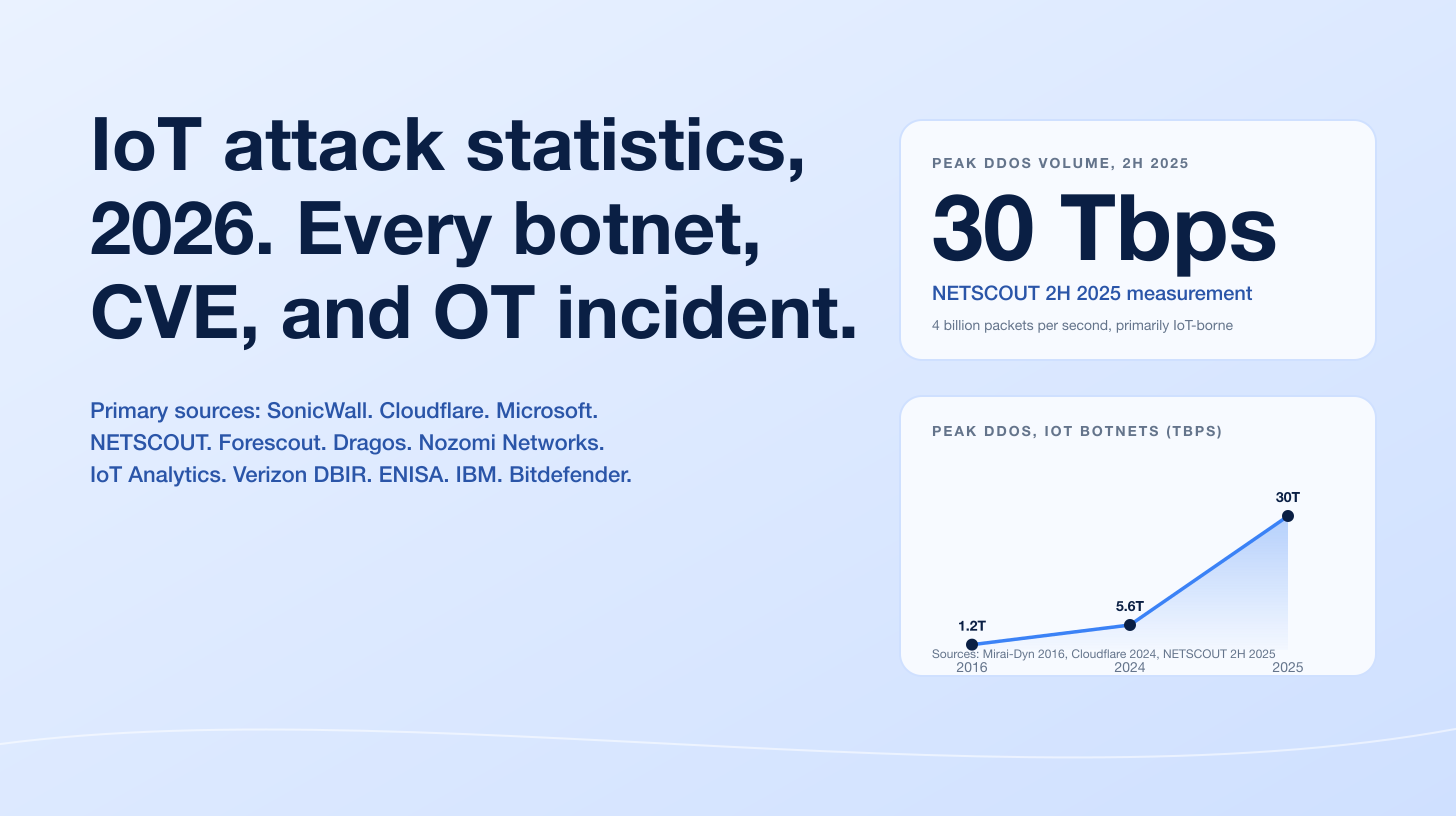
Three forces drove the 2025 surge. First, the Aisuru-Kimwolf botnet eclipsed Mirai as the apex botnet of the year: a Turbo-Mirai-class IoT family of 1 to 4 million infected Android TVs and home routers that Cloudflare credited with 1,304 hyper-volumetric attacks in Q3 2025 alone, with Lumen Black Lotus Labs reporting daily C2 traffic surging from 50,000 to 200,000 in September 2025 and null-routing 550+ Aisuru and Kimwolf C2 nodes. Second, hyper-volumetric attacks went mainstream: Cloudflare blocked over 6,500 hyper-volumetric attacks in Q2 2025, an average of 71 per day and a 65-fold year-over-year increase, with the count exceeding 1 Tbps doubling quarter over quarter. Third, hacktivist DDoS held organized: NoName057(16)'s DDoSia campaign targeted 3,700+ unique hosts between July 1, 2024 and July 14, 2025 at an average 50 hosts per day, while two Sudanese brothers operating Anonymous Sudan were charged in October 2024 for 35,000+ attacks since January 2023 that included shutting down the Cedars-Sinai Medical Center emergency department. Together these forces pushed DDoS from a noisy nuisance into a sustained operational risk for telecom, finance, gaming, and government infrastructure heading into 2026.
This post is the Stingrai research team's canonical 2026 reference for DDoS attack activity. It assembles 95 numeric claims from 22 named primary publishers, including Cloudflare DDoS Threat Reports Q1 to Q4 2025, NETSCOUT DDoS Threat Intelligence Reports H1 and H2 2025, Akamai State of the Internet (Security) and the FS-ISAC + Akamai financial-sector analysis, Microsoft Azure Infrastructure Blog disclosures, Google Cloud and AWS records, Imperva 2025 application-layer telemetry, F5 Labs 2024 DDoS Attack Trends, A10 Networks DDoS Weapons, Lumen Black Lotus Labs Aisuru disruption, CISA Alert AA23-44487, DOJ Operation PowerOFF seizures, Eurojust Operation Eastwood hacktivist takedown, Recorded Future Insikt Group NoName057(16) research, and named corporate disclosures (Cedars-Sinai, ChatGPT, Microsoft, Telegram). Lead data is full-year 2024 and quarterly 2025 telemetry, the freshest available; many primary publishers have not yet released their full-year 2026 reports as of April 2026. Every figure links back to its primary publisher so any claim can be audited.
TL;DR: 12 labeled key stats
Largest publicly disclosed DDoS attack to date: 31.4 Tbps, 35 seconds, Aisuru-Kimwolf botnet, November 2025 (Cloudflare 2025 Q4 DDoS Threat Report).
Cloudflare full-year 2024 DDoS attacks blocked: 21.3M (+53% YoY); 4,870 per hour (Cloudflare 2024 Q4 DDoS Threat Report).
Cloudflare Q1 2025 DDoS attacks blocked: 20.5M (+358% YoY); 96% of full-year 2024 in one quarter (Cloudflare 2025 Q1 DDoS Threat Report).
Cloudflare Q4 2025 DDoS attacks blocked rate: 5,376 per hour (Cloudflare 2025 Q4).
Hyper-volumetric YoY growth, Cloudflare Q2 2025: +65x; 6,500+ attacks blocked at 71 per day (Cloudflare 2025 Q2).
Largest cloud DDoS attack ever, Microsoft Azure: 15.72 Tbps; 3.64 Bpps; 500K+ source IPs; Australia target; October 24, 2025 (Microsoft Azure Infrastructure Blog).
NETSCOUT global DDoS attacks, H1 + H2 2025: 8M+ per six-month window; 16M+ across the year (NETSCOUT DDoS Threat Intelligence Reports H1 and H2 2025).
Akamai L3/L4 industry share, financial services (top): 34%; followed by gaming 18% and high tech 15% (Akamai SOTI / FS-ISAC and Akamai 2025).
Aisuru-Kimwolf botnet size: 1 to 4 million infected Android TVs and home routers (Cloudflare 2025 Q3 DDoS Threat Report).
HTTP/2 Rapid Reset (CVE-2023-44487) records: Google 398M rps, Cloudflare 201M rps, AWS 155M rps (Google Cloud Security Blog; CISA Alert).
NoName057(16) DDoSia targets, July 2024 to July 2025: 3,700+ unique hosts; 50/day average (Recorded Future Insikt Group, July 2025).
Anonymous Sudan attack count, January 2023 to March 2024: 35,000+ attacks; US$10M+ damages; two Sudanese brothers indicted October 2024 (DOJ via The Hacker News).
Key takeaways
The volumetric ceiling jumped an order of magnitude in 13 months. Cloudflare's 5.6 Tbps Aisuru disclosure in October 2024 was eclipsed by 7.3 Tbps in June 2025, then by Microsoft's 15.72 Tbps in October 2025, then by Cloudflare's 31.4 Tbps in November 2025. Defenders should plan headroom on the assumption that the public ceiling moves again before the next quarterly report cycle.
Aisuru-Kimwolf is the new apex botnet. Cloudflare's Q3 2025 deep-dive estimates the botnet at 1 to 4 million infected hosts and credits it with 1,304 hyper-volumetric attacks in Q3 alone. Lumen Black Lotus Labs reported a 4x surge in daily C2 traffic in September 2025 and null-routed 550+ C2 nodes. Most affected devices are Android TVs and unpatched home routers, putting residential ISPs squarely in the source-attribution column.
Hyper-volumetric attacks are now an every-day occurrence, not an outlier. Cloudflare's Q2 2025 report logged a 65-fold year-over-year jump (6,500+ attacks, 71 per day) and Q3 added another 1,304 from Aisuru alone. Hyper-volumetric is no longer the marketing tail; it is the operational baseline for any ISP, gaming platform, or financial-sector public surface.
The vector mix is UDP-dominant, reflector-heavy, and amplification-driven. F5 Labs measured 4x more UDP attacks than TCP and 8x more than ICMP in 2024, and A10 Networks tracks 14.6 million unique reflector amplifier weapons globally, 97 percent of all DDoS weapon inventory, with SSDP making up 22 percent of the pool. Layer 3/4 traffic accounted for 71 percent of Cloudflare's Q3 2025 attack share.
Targeting is unchanged at the sector level but shifting at the regional level. Financial services held its 34 percent top spot at Akamai for the second consecutive year, but APAC financial services jumped from 11 percent to 38 percent of regional volumetric attacks, and Hong Kong rose 12 places to second-most-DDoS'd region in Cloudflare's Q4 2025. Telecommunications now leads Cloudflare's hyper-volumetric target list.
Methodology
Date cutoff: April 29, 2026. Lead data is full-year 2024 and quarterly 2025 telemetry where a primary publisher has released it; 2026 forecasts are labeled where present and limited to figures the publisher itself projected. Statistics that could not be reached via a named primary source on at least one verification pass were dropped rather than estimated. Where multiple primary publishers report compatible figures (for example Cloudflare and NETSCOUT both reporting hyper-volumetric activity), we cite the publisher whose methodology window matches the claim. Secondary news aggregators are cited only where they constitute the public record of a corporate incident or law-enforcement action.
Sources span: Cloudflare DDoS Threat Reports Q4 2024 and Q1 to Q4 2025; Cloudflare Radar 2025 Year in Review; NETSCOUT DDoS Threat Intelligence Report H1 2025 and H2 2025; Akamai State of the Internet (Security) 2024 and 2025 financial-sector analyses jointly with FS-ISAC; Microsoft Azure Infrastructure Blog disclosures October 2025 and prior; Microsoft Azure DDoS Protection 2021 Q3 and Q4 trends; AWS Shield 2.3 Tbps disclosure (2020); Google Cloud Security Blog HTTP/2 Rapid Reset (October 2023); Imperva early-2025 application-layer DDoS commentary; F5 Labs 2024 DDoS Attack Trends; A10 Networks DDoS Weapons reports and threat map (2024 to 2025); Lumen Black Lotus Labs Aisuru and Kimwolf disruption (October 2025); CISA Alert on CVE-2023-44487; CVE-2023-44487 NVD entry; DOJ press release on Operation PowerOFF April 2026 sweep; Eurojust + Europol Operation Eastwood (July 2025); Recorded Future Insikt Group Anatomy of DDoSia (July 2025); Imperva Operation Eastwood follow-up; The Hacker News and Krebs On Security on Anonymous Sudan; Microsoft and Akamai threat-actor commentary on Russia-Ukraine and Middle East hacktivism.
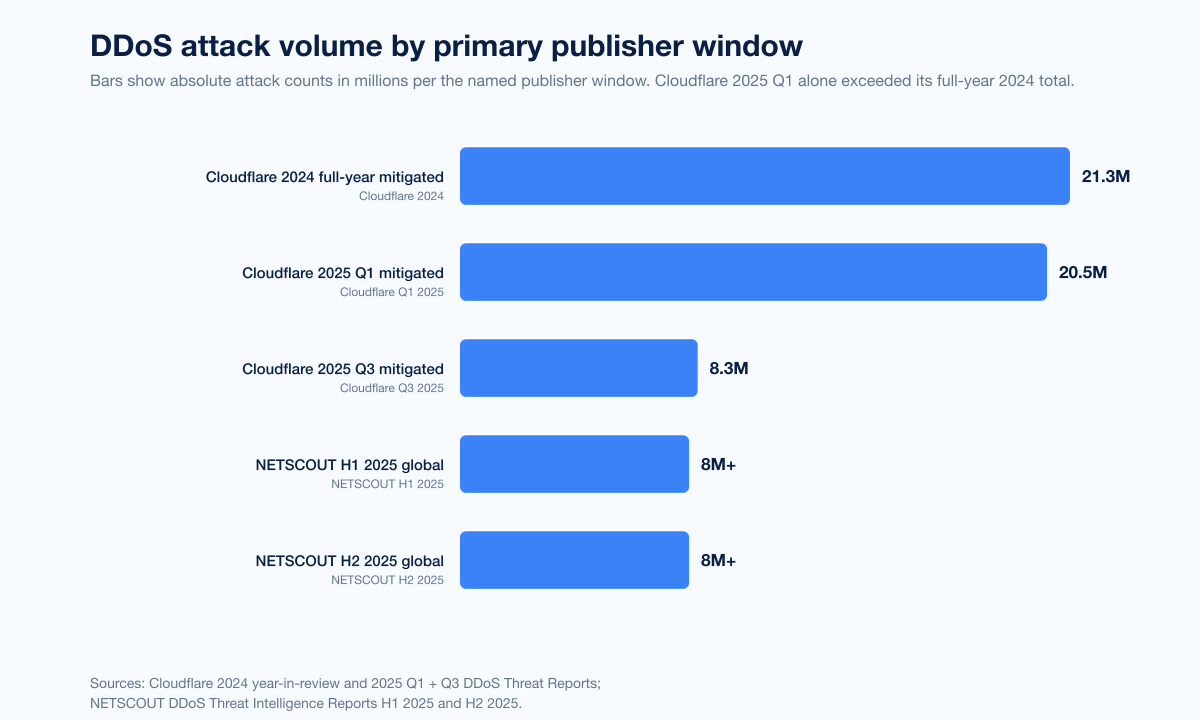
Figure 1: DDoS attack volume per the named primary publisher and reporting window. Cloudflare's Q1 2025 quarter alone exceeded 96 percent of its full-year 2024 total, and Q3 added another 8.3M. NETSCOUT logged 8M+ in each half of 2025 globally. Sources: Cloudflare 2024 Q4 DDoS Threat Report; Cloudflare 2025 Q1 DDoS Threat Report; Cloudflare 2025 Q3 DDoS Threat Report; NETSCOUT H1 + H2 2025 DDoS Threat Intelligence Reports.
How big is the DDoS problem in 2026?
Three datasets anchor the answer.
Cloudflare DDoS Threat Reports, 2024 to 2025
Cloudflare publishes a quarterly threat report that sits as close to a global ground-truth feed as the public internet has. The headline numbers across the cycle:
2024 full year: 21.3 million attacks blocked, +53 percent year over year, average 4,870 per hour. Q4 alone was 6.9 million (+83 percent YoY) and contained 420+ hyper-volumetric attacks (>1 Bpps or >1 Tbps), a 1,885 percent QoQ jump in attacks above 1 Tbps. The first publicly disclosed 5.6 Tbps Aisuru attack landed during Halloween week.
2025 Q1: 20.5 million attacks blocked, +358 percent YoY, +198 percent QoQ. Network-layer attacks alone reached 16.8 million (+509 percent YoY). Cloudflare blocked the most intense packet-rate attack on record at 4.8 Bpps (52 percent above the prior benchmark) and a separate 6.5 Tbps flood. 700+ hyper-volumetric attacks, roughly 4 in every 100,000 network-layer attacks.
2025 Q2: Hyper-volumetric attacks surged 65x year over year to 6,500+, an average 71 per day. Cloudflare blocked the largest attacks reported up to that point at 7.3 Tbps and 4.8 Bpps; the 7.3 Tbps attack lasted 45 seconds. Attacks exceeding 100 million pps surged 592 percent QoQ; attacks exceeding 1 Bpps and 1 Tbps each doubled QoQ.
2025 Q3: 8.3 million attacks blocked, 3,780 per hour, +15 percent QoQ and +40 percent YoY. Network-layer accounted for 71 percent (5.9M attacks); HTTP for 29 percent (2.4M attacks). The Q3 cover story was Aisuru itself: 1,304 hyper-volumetric attacks in the quarter, attacks surging 54 percent QoQ, including a then-record 29.7 Tbps and 14.1 Bpps.
2025 Q4: Average 5,376 attacks per hour. The 31.4 Tbps Aisuru-Kimwolf burst arrived in November, and the December "Night Before Christmas" campaign exceeded 200 million rps in HTTP DDoS attacks against Cloudflare's customers and infrastructure. DDoS attacks across the full year 2025 grew 121 percent versus 2024. Hong Kong rose 12 places to become the second most attacked region.
The 2025 cumulative trend pegs DDoS as the dominant volume threat the public internet defends against.
NETSCOUT DDoS Threat Intelligence Report, H1 and H2 2025
NETSCOUT's ATLAS visibility, derived from telemetry across hundreds of service providers, logged more than 8 million DDoS attacks worldwide in each half of 2025 across 203 countries, with some attacks reaching 30 Tbps in size. NETSCOUT's H2 2025 report highlights AI-augmented DDoS-for-hire activity (mentions of malicious AI tools surged 219 percent in underground forums) and a qualitative shift toward sophistication: large language models accelerating vulnerability exploitation and botnet expansion.
Akamai State of the Internet (Security)
Akamai's Layer 3/4 telemetry has financial services as the top targeted industry for the second consecutive year at 34 percent of attacks, followed by gaming (18 percent) and high tech (15 percent). Application-layer DDoS against the financial sector grew 23 percent between 2023 and 2024. Akamai's regional cut: APAC financial services share of all volumetric DDoS attacks jumped from 11 percent in 2023 to 38 percent in 2024 to 2025, driven by geopolitical tensions including the Russia-Ukraine war and Middle East conflict.
The 2025 record progression: from 5.6 Tbps to 31.4 Tbps in 13 months
If 2024 was the year hyper-volumetric DDoS broke through, 2025 was the year the volumetric ceiling moved every quarter.
Chronological record table
Date | Event | Disclosing provider | Headline |
|---|---|---|---|
March 2018 | GitHub Memcached amplification | Akamai (Prolexic) | 1.35 Tbps; first major amplification record |
February 2020 | AWS CLDAP reflection | AWS Shield | 2.3 Tbps; 44 percent larger than prior record |
November 2021 | Microsoft Azure UDP flood, Asia | Azure DDoS Protection | 3.47 Tbps; 340M pps; 15-min attack |
August to October 2023 | HTTP/2 Rapid Reset (CVE-2023-44487) | Google, Cloudflare, AWS | 398M, 201M, 155M rps respectively |
October 2024 | Cloudflare Aisuru volumetric | Cloudflare | 5.6 Tbps; first publicly disclosed Aisuru record |
April 2025 | Cloudflare multi-vector hyper-volumetric | Cloudflare | 6.5 Tbps; 4.8 Bpps; 30K IPs / 147 countries |
June 2025 | Cloudflare hyper-volumetric burst | Cloudflare | 7.3 Tbps; 45-second burst; Q2 record |
October 24, 2025 | Microsoft Azure UDP flood, Australia | Azure DDoS Protection | 15.72 Tbps; 3.64 Bpps; Aisuru; 500K+ source IPs |
November 2025 | Cloudflare Aisuru-Kimwolf burst | Cloudflare | 31.4 Tbps; 35-second burst; current public record |
December 2025 | Aisuru-Kimwolf "Night Before Christmas" | Cloudflare | 200M+ rps HTTP DDoS sustained campaign |
The arc is unambiguous. The largest publicly disclosed volumetric attack jumped from 2.3 Tbps in 2020 to 31.4 Tbps in November 2025, with the most aggressive scaling concentrated in 2025. Whatever defensive headroom an enterprise sized to in early 2024 was insufficient by Q3 2025.
Why the ceiling moved
Three reasons.
IoT-botnet capacity outran defender capex. Aisuru and its sibling Kimwolf push their attack capacity off 1 to 4 million Mirai-class IoT hosts, primarily Android TVs and unpatched residential routers. Compared to 2016-era Mirai (hundreds of thousands of devices), the 2025 botnet has roughly 5 to 20x more bandwidth and aggregate compute available.
Burst-mode tactics defeat thresholds. The 31.4 Tbps Cloudflare attack lasted 35 seconds; the 7.3 Tbps Q2 attack lasted 45 seconds. Burst-mode floods compress massive volume into windows shorter than typical detection thresholds, putting the burden on autonomous mitigation rather than human operators.
Multi-vector attacks layer L3/L4 with L7 to maximize damage. The April 2025 6.5 Tbps attack used SYN flood, Mirai-class TCP reset, SSDP amplification, CLDAP and ESP reflection in parallel from 30,000 IPs across 147 countries. Multi-vector blends defeat single-protocol defenses and force defenders to ride autonomous orchestration.
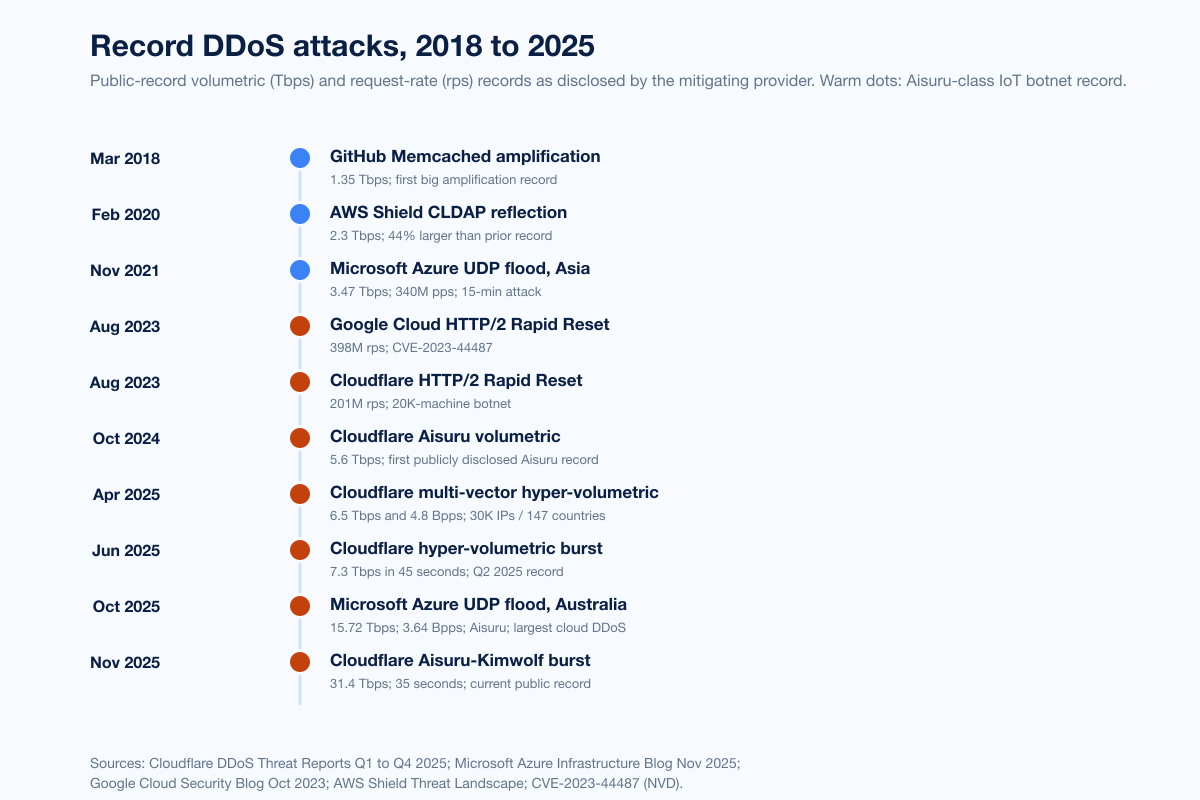
Figure 2: Public-record DDoS attack progression from March 2018 to November 2025. Warm dots: Aisuru-class IoT-botnet records. Sources: Cloudflare DDoS Threat Reports Q4 2024 and Q1 to Q4 2025; Microsoft Azure Infrastructure Blog; Google Cloud HTTP/2 Rapid Reset; AWS Shield 2.3 Tbps disclosure, June 2020; Microsoft Azure DDoS 3.47 Tbps disclosure, January 2022.
The Aisuru-Kimwolf botnet: apex of 2025
Cloudflare's Q3 2025 report titled itself "Aisuru, the apex of botnets" for good reason. The botnet drove the year's record-setting DDoS activity and reshaped the source-attribution map.
Aisuru in numbers
Hosts: 1 to 4 million infected devices, primarily Android TVs and unpatched home routers, mostly residential ISPs in the United States and other countries.
Q3 2025 attack count: 1,304 hyper-volumetric attacks attributed to Aisuru.
Cumulative 2025 mitigations: Cloudflare reported 2,867 Aisuru attacks since the start of 2025 by the time of its Q3 report.
Top targets: Telecommunications, gaming companies, hosting providers, and financial services.
Records held: 5.6 Tbps (October 2024), 7.3 Tbps (June 2025), 29.7 Tbps and 14.1 Bpps (Q3 2025), 15.72 Tbps Microsoft Azure (October 24, 2025), 31.4 Tbps Cloudflare (November 2025).
Kimwolf and the joint family
Cloudflare and Lumen Black Lotus Labs treat Aisuru and Kimwolf as a co-evolving family. Lumen disrupted the joint operation in October 2025, null-routing 550+ command-and-control nodes after observing daily C2 traffic surge from 50,000 to 200,000 in September 2025. As with prior Mirai variants, Aisuru-Kimwolf incorporates dedicated DDoS attack capabilities plus multi-use functions for credential stuffing, AI-driven web scraping, spamming, and phishing, making takedown a moving target.
What Aisuru means for residential ISPs
Aisuru's source population sits primarily inside residential networks: unpatched routers, IP cameras, and Android TVs with default credentials. The DDoS source-attribution column for 2025 is therefore dominated by ISPs that historically did not consider themselves direct DDoS targets. Industry expectation heading into 2026: greater pressure on residential ISPs to (1) push customer-premises firmware updates aggressively, (2) detect outbound DDoS traffic on residential lines, and (3) coordinate takedown lists with researchers like Lumen Black Lotus Labs and Cloudflare's Project Galileo.
DDoS vector mix and amplifier inventory
Adversaries pick vectors based on amplification factor, source population availability, and detection latency.
UDP dominance
F5 Labs measured UDP delivering 4x more attacks than TCP and 8x more than ICMP in 2024, a direct consequence of UDP-based reflection's amplification advantage. As QUIC and HTTP/3 (UDP-based) take share from HTTP/2 (TCP-based), F5 expects the UDP share to grow further.
Reflector and amplifier inventory
A10 Networks tracks 14.6 million unique reflector amplifier weapons globally, of which reflectors account for approximately 97 percent of all DDoS weapon inventory. The vector mix:
SSDP: 22 percent of global amplifier pool. Concentrated in Venezuela, China, Algeria, Croatia, South Korea, Vietnam, Taiwan, India, and Kazakhstan, with over half of all SSDP amplifiers in just ten countries.
CoAP: 4 percent of global amplifier pool, found in 155 countries. Over half of CoAP weapons are concentrated in China, Russia, and the Philippines. Amplification factor measured at 34x.
CLDAP, NTP, DNS, SNMP, Memcached: the remainder of the reflector pool, with CLDAP being the vector behind the AWS 2.3 Tbps record (2020) and DNS amplification used in many telecommunications-targeted hyper-volumetric attacks in 2025.
Layer 3/4 versus Layer 7
Cloudflare's Q3 2025 split: 71 percent network-layer (5.9M attacks), 29 percent HTTP DDoS (2.4M attacks). Network-layer is up 87 percent QoQ; HTTP DDoS is down 41 percent QoQ. The trend through 2025 is heavier shift toward L3/L4 volumetric, driven by Aisuru's UDP flood and reflector toolkit, but L7 hyper-volumetric is still climbing in absolute terms (December 2025 sustained 200M+ rps).
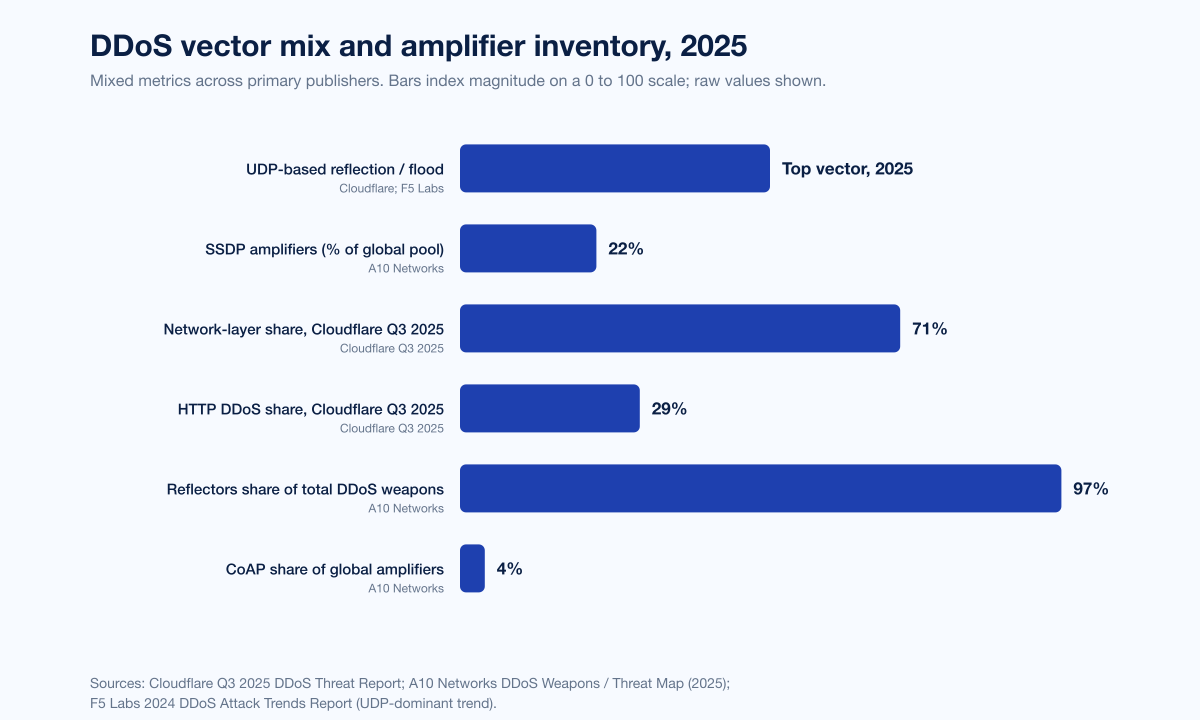
Figure 3: 2025 DDoS vector mix and amplifier inventory across primary publishers. Sources: Cloudflare 2025 Q3 DDoS Threat Report; A10 Networks DDoS Weapons / Threat Map (2025); F5 Labs 2024 DDoS Attack Trends.
HTTP/2 Rapid Reset (CVE-2023-44487): the protocol-level attack class
The single largest protocol-level DDoS innovation of the past three years remains operational in 2026.
What it is
CVE-2023-44487 is a denial-of-service vulnerability in HTTP/2 stream multiplexing. The protocol allows clients to unilaterally cancel streams (RST_STREAM frames) that have already been requested. Threat actors automate the request-then-cancel pattern at scale, generating massive request volumes per TCP connection. The collective susceptibility was rated CVSS 7.5 (High).
Records held
Google Cloud: 398 million requests per second, the largest known HTTP/2 Rapid Reset attack at disclosure. The two-minute attack generated more requests than the total Wikipedia article views for September 2023.
Cloudflare: 201 million rps, 3x larger than any prior attack Cloudflare had observed. The botnet behind the record was a modest ~20,000 machines, demonstrating that Rapid Reset multiplies a small infrastructure into hyper-volumetric capacity.
AWS: 155 million rps in the same August to October 2023 window.
Why it still matters in 2026
Every major HTTP/2 server implementation patched the vulnerability in late 2023 and 2024, but the underlying protocol weakness drove the industry to harden rate-limiting at the connection layer, push HTTP/3 adoption faster, and reset assumptions about how thin a botnet can be relative to attack capacity. Imperva's early-2025 commentary on a 6 million rps attack against a French home-supply retailer noted the attacker combined HTTP/2 Rapid Reset with traditional DDoS methods, confirming the technique remains in active use even after server-side mitigations. Imperva also reported the largest application-layer DDoS attack it has observed to date at 14.2 million rps against a Turkish luxury retailer in late 2025.
Industry breakdown: who gets hit
DDoS targeting maps cleanly to three buckets: revenue at risk during downtime, geopolitical visibility, and large public attack surface. The 2025 reports converge on the following sectoral pattern.
Sector | What the data says | Source |
|---|---|---|
Telecommunications and carriers | Top sector for hyper-volumetric attacks, Cloudflare Q3 2025; targeted by Aisuru's largest attacks | Cloudflare Q3 2025 |
Financial services | 34% of Akamai L3/L4 telemetry (top sector, second consecutive year); +23% application-layer YoY (2024); APAC fin svc grew from 11% to 38% of volumetric attacks | Akamai SOTI / FS-ISAC and Akamai 2025 |
Gaming | 18% of Akamai L3/L4 telemetry; targeted by Aisuru hyper-volumetric attacks | Akamai SOTI; Cloudflare Q3 2025 |
High technology | 15% of Akamai L3/L4 telemetry | Akamai SOTI |
Healthcare | Anonymous Sudan disrupted Cedars-Sinai Medical Center ED for 8 hours; broader hospital-targeting pattern through 2025 | DOJ October 2024; The Hacker News |
Hosting providers | Co-targeted with telecom by Aisuru in Q3 2025 | Cloudflare Q3 2025 |
Government | Doppelganger Russian influence ops co-targeting Western government domains; NoName057(16) targeting NATO and allied governments | Microsoft Digital Defense Report 2025; Recorded Future |
Retail | Turkish luxury retailer hit with 14.2M rps L7 attack; French home-supply retailer hit with 6M rps multi-vector L7 attack | Imperva 2025 |
Beverage / FMCG | US beverage company hit with 13.5M rps in 8-minute burst, January 2025 | Imperva 2025 |
Geographic targeting
Cloudflare's Q4 2025 report flagged Hong Kong as the second most attacked region of the year, jumping 12 places. Akamai's APAC financial services share of regional volumetric attacks grew from 11 percent in 2023 to 38 percent in 2024 to 2025, driven by geopolitical tensions and the regional banking system's high public visibility. Microsoft Azure's October 24, 2025 record disclosed an Australian customer as the target.
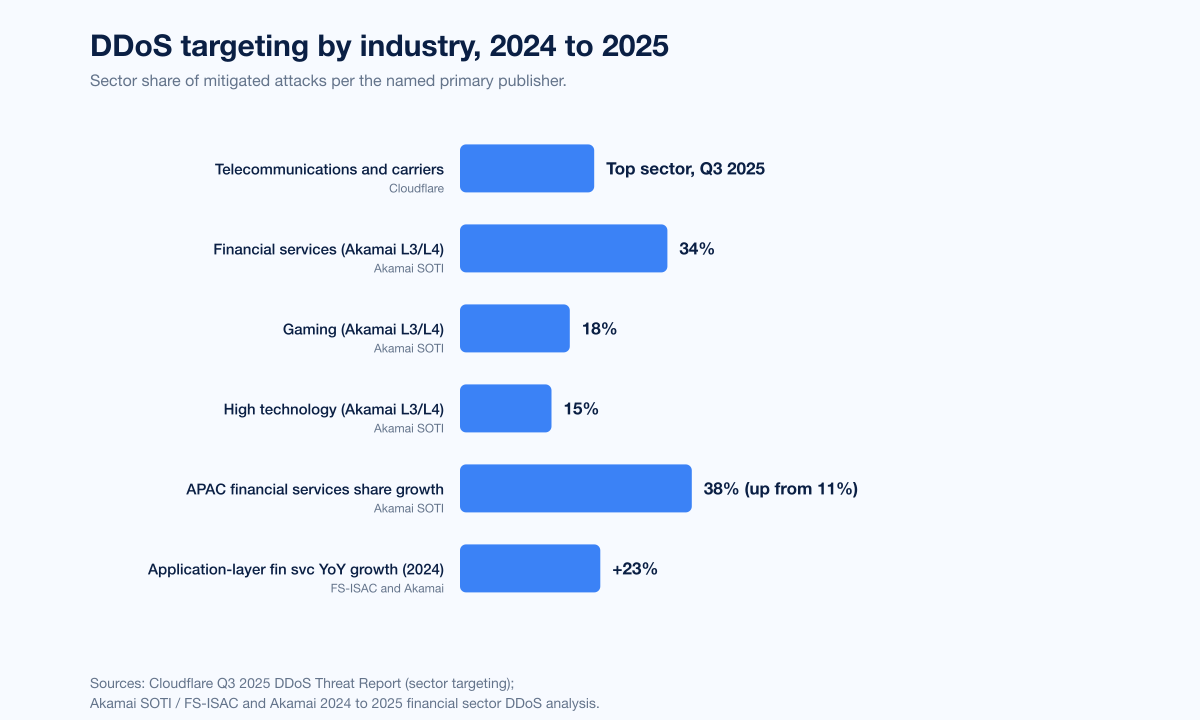
Figure 4: DDoS targeting by industry, 2024 to 2025, across primary publishers. Sources: Cloudflare 2025 Q3 DDoS Threat Report; FS-ISAC and Akamai DDoS Attacks Across the Financial Sector (2025); Akamai newsroom: APAC financial services targeting.
Hacktivist DDoS: NoName057(16), Anonymous Sudan, KillNet
Hacktivist DDoS held organized through 2025, with three named groups dominating telemetry.
NoName057(16) and the DDoSia campaign
NoName057(16) is a pro-Russian hacktivist collective best known for its DDoSia distributed-attack platform, which crowd-sources volunteer compute. Recorded Future Insikt Group's Anatomy of DDoSia, July 2025 measured: NoName057(16) launched attacks against an average of 50 unique hosts per day, peaking at 91 in a single day, targeting more than 3,700 unique hosts over the 13-month period from July 1, 2024 to July 14, 2025. After Operation Eastwood (a coordinated Eurojust + Europol takedown across 12 countries, July 14 to 17, 2025), the group's published target lists actually grew, averaging 18 sites per day in the four weeks following the operation, an 80 percent increase versus the prior month per Imperva. Operation Eastwood is therefore best understood as disruption rather than dismantling.
Anonymous Sudan and Distributed Cloud Attack Tool (DCAT)
Two Sudanese brothers, Ahmed Salah Yousif Omer and Alaa Salah Yusuuf Omer, were charged in October 2024 by a US federal grand jury for operating Anonymous Sudan. The group's Distributed Cloud Attack Tool (DCAT) was used to launch more than 35,000 DDoS attacks between January 2023 and March 2024, causing more than US$10 million in damages to US victims. Notable targets: ChatGPT, Microsoft, Telegram, X (Twitter), the Associated Press, and the Cedars-Sinai Medical Center emergency department, which was forced to redirect incoming patients to other facilities for approximately eight hours. Akamai, AWS, and CrowdStrike contributed to the March 2024 disruption operation that disabled DCAT.
KillNet and adjacent groups
KillNet cooperated with NoName057(16) and Anonymous Sudan throughout 2024 and 2025, but its operational tempo declined after Operation Eastwood. Akamai and Microsoft tracked broader pro-Russian DDoS activity layered on top of the Russia-Ukraine war and pro-Palestinian DDoS layered on top of regional Middle East tensions.
What hacktivism contributes to total volume
Hacktivism is a meaningful but not dominant slice of total DDoS. Recorded Future's 3,700+ unique hosts attacked by NoName057(16) over 13 months sits well below the millions of total attacks Cloudflare and NETSCOUT mitigated in any single quarter; hacktivist DDoS is best understood as politically targeted and persistent rather than volumetrically dominant.
DDoS-for-hire: Operation PowerOFF and the booter market
Booter and stresser sites have powered the casual DDoS market for over a decade. Two operations stand out in 2024 to 2026.
Operation PowerOFF, December 2024 wave and April 2026 sweep
Operation PowerOFF is an ongoing coordinated effort across 21 countries (including the US, UK, Germany, Netherlands, and Australia) to dismantle DDoS-for-hire platforms. The April 2026 wave seized 53 domains, arrested four suspects, and seized data on more than 3 million user accounts allegedly involved in launching DDoS attacks. The DOJ disclosed eight DDoS-for-hire domains taken down in the operation, including Vac Stresser and Mythical Stress. The cumulative total over four years: 100 booter domains seized and 11 individuals charged in the US alone.
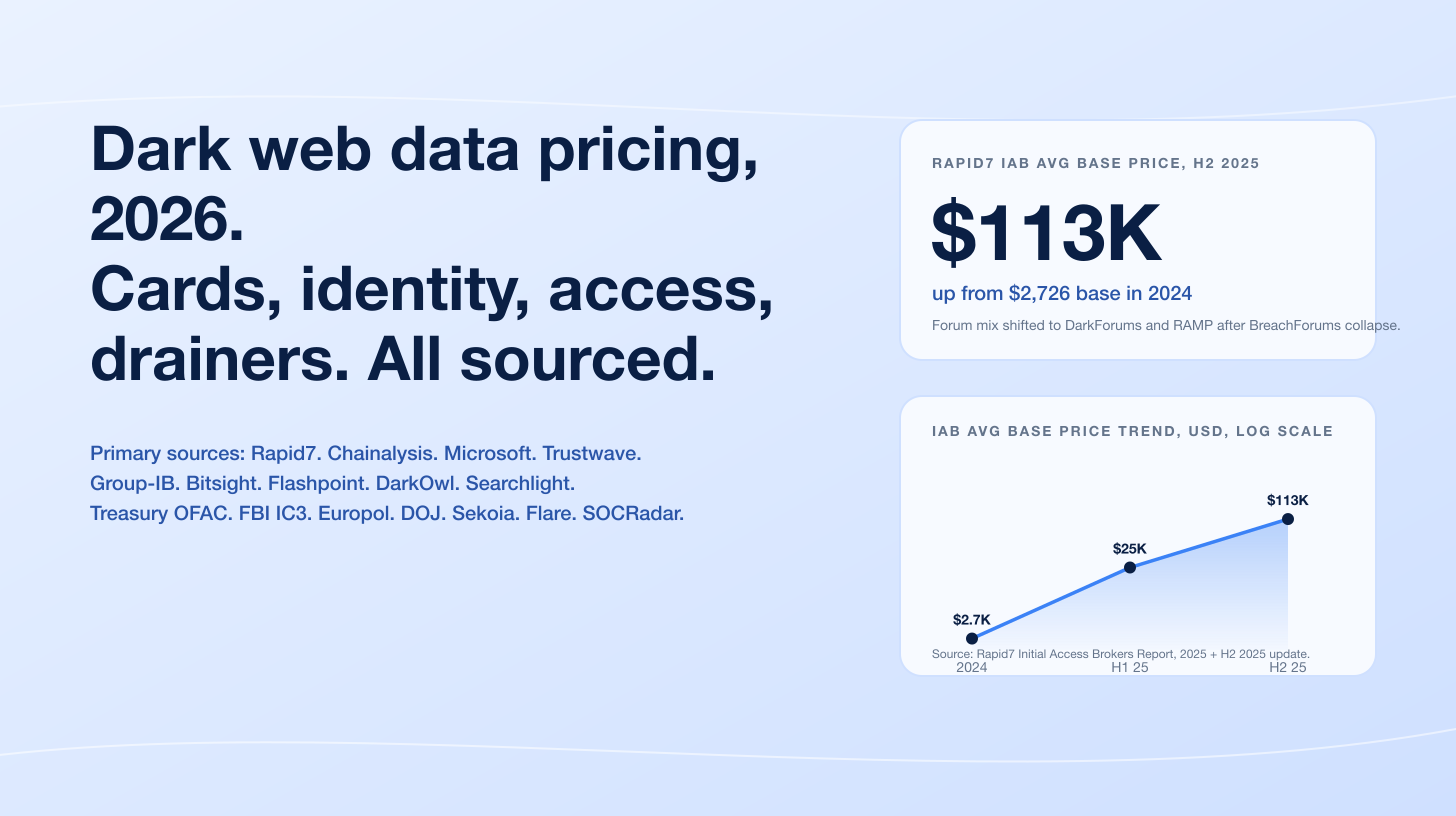
Booter pricing and market structure
Booter pricing has remained roughly stable across 2024 to 2026 in the publicly observed dark-market reporting: subscription tiers ranging from US$10 to US$200 per month for casual capacity, premium tiers escalating into the low thousands per year. Researchers note that the booter market is structurally different from nation-state DDoS infrastructure: where Aisuru-Kimwolf operates as a single unified botnet under sophisticated operator control, booters resell time-sliced access to smaller, often Mirai-derivative botnets at low cost. The two markets coexist rather than overlap.
DDoS attack durations and burst patterns
Two structural shifts in 2025 attack duration deserve explicit citation.
Short-burst attacks dominate hyper-volumetric records
The 31.4 Tbps Cloudflare attack lasted 35 seconds. The 7.3 Tbps Q2 attack lasted 45 seconds. Multi-vector hyper-volumetric attacks frequently complete in under 60 seconds, designed to compress massive volume into windows shorter than typical detection-and-mitigation latency. Burst-mode forces defenders into autonomous mitigation at the network edge.
Application-layer attacks favor sustained windows
The Imperva US beverage attack reached 13.5 million rps in 8 minutes; the French home-supply retailer attack ran 2 hours; the December 2025 "Night Before Christmas" Aisuru-Kimwolf HTTP DDoS campaign sustained 200M+ rps over multiple sessions. L7 attacks tend to be longer because the goal is to exhaust application back-ends through legitimate-looking HTTP requests rather than overwhelm a network pipe.
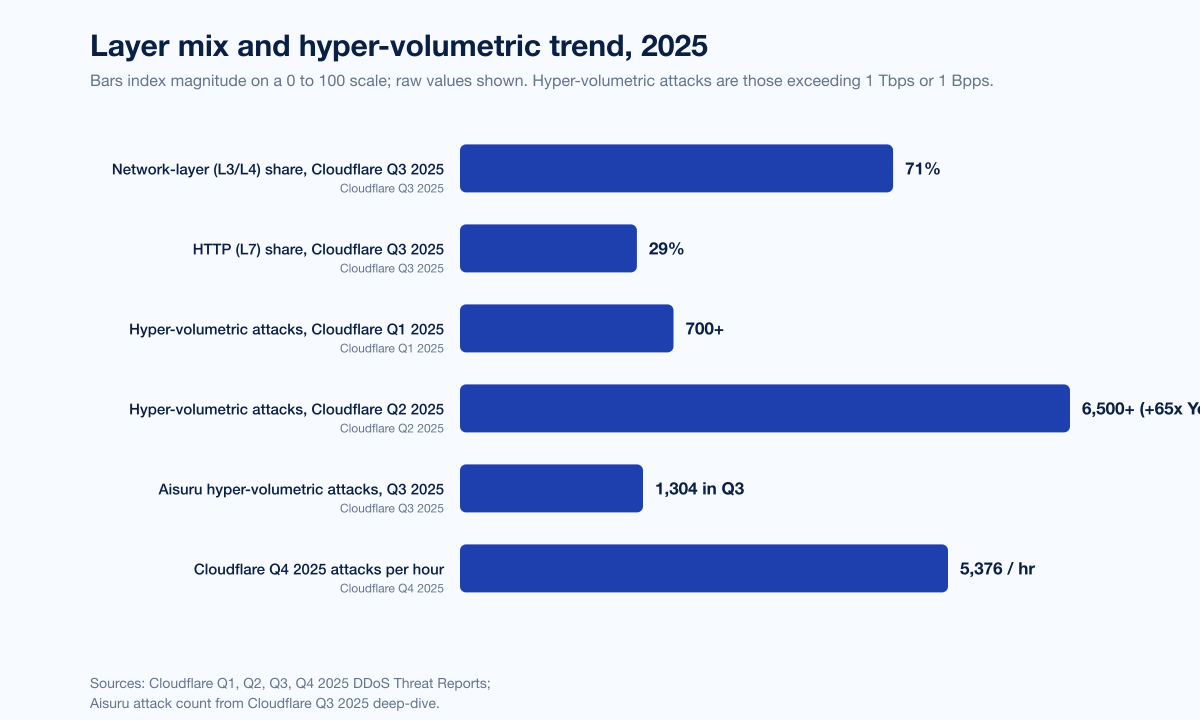
Figure 5: Layer split and hyper-volumetric trend across Cloudflare's 2025 reporting cycle. Sources: Cloudflare 2025 Q1, Q2, Q3, and Q4 2025 DDoS Threat Reports.
Forward outlook: what primary publishers project for 2026
Three forecasts from named primary sources merit explicit citation:
Cloudflare Q4 2025 outlook projects continued hyper-volumetric growth through 2026, with Aisuru-Kimwolf operating at the public ceiling and burst-mode tactics remaining the dominant volumetric pattern. Cloudflare also flags telecommunications and hosting providers as the primary 2026 target set on hyper-volumetric volume.
NETSCOUT H2 2025 forecasts qualitative shifts: AI-augmented DDoS-for-hire tooling crossing into mainstream operator use, dark-web mentions of malicious AI tools up 219 percent in their dataset, and DDoS botnet expansion accelerating in 2026.
A10 Networks 2025 reports project further growth in IoT-derived weapon inventory, CoAP and SSDP amplifier pools concentrated in countries with limited patching infrastructure, and continued reliance on residential ISPs as source attribution.
The unifying signal: 2026 will not see hyper-volumetric DDoS recede. The public ceiling will move again. Aisuru-Kimwolf is the dominant force unless or until law enforcement coordinates a comprehensive C2 takedown; partial disruption (Lumen's 550 nodes, Cloudflare's mitigation logs) has slowed but not stopped the campaign.
What this means for defenders
Five concrete buyer actions the data supports:
Treat hyper-volumetric attacks as the operational baseline, not an outlier. Cloudflare's 65x year-over-year growth in attacks above 1 Tbps or 1 Bpps removes the rationale for sizing defensive headroom to 2024 thresholds. Plan for a 2026 ceiling that may exceed 50 Tbps and confirm your DDoS provider's autonomous-mitigation capacity matches that envelope.
Default to burst-mode-tolerant detection. Threshold-based detection misses 35-second floods. Insist on autonomous, signature-free, behavioral mitigation that reacts in single-digit seconds and does not require human intervention to engage.
Patch HTTP/2, then move toward HTTP/3 / QUIC. Confirm every web server, load balancer, and reverse proxy in your stack has CVE-2023-44487 mitigations applied. Plan a migration path to HTTP/3 / QUIC where appropriate, and rate-limit at the connection layer.
Map your sector's geographic risk profile. If you are in financial services, the targeting concentration moved toward APAC in 2024 to 2025; ensure your CDN and DDoS provider has POPs in Singapore, Tokyo, Hong Kong, and Sydney. If you are in telecommunications, expect to be the top hyper-volumetric target through 2026.
Watch your origin's exposure to UDP reflection from residential ISPs. Aisuru-Kimwolf source IPs are dominantly residential. ACL hardening on UDP-based services, BCP38 source-address validation at the egress, and active coordination with upstream transit on RTBH (remote-triggered black-holing) are still the most cost-effective controls.
For organizations weighing how to test defensive readiness against the 2026 baseline, Stingrai's penetration testing services and PTaaS platform cover DDoS-resilience tabletop exercises, application-layer stress testing, and CDN configuration review as part of standard adversary-simulation engagements. For a deeper look at the IoT-botnet substrate behind Aisuru-class records, see our IoT Attack Statistics 2026 post; for the DDoS-for-hire booter pricing context, see our Dark Web Data Pricing 2026 post; and for sector targeting beyond DDoS, our Top Industries Targeted by Hackers 2026 post.
Frequently Asked Questions
What is the largest DDoS attack ever recorded?
The largest publicly disclosed DDoS attack on record is a 31.4 Tbps Aisuru-Kimwolf burst that lasted 35 seconds, mitigated by Cloudflare in November 2025 and disclosed in Cloudflare's 2025 Q4 DDoS Threat Report. The largest cloud DDoS attack ever observed is a 15.72 Tbps Aisuru-class flood that hit a single Microsoft Azure customer in Australia on October 24, 2025, with 3.64 billion packets per second from over 500,000 source IPs. The largest HTTP request-rate DDoS attack on record is Google Cloud's 398 million requests-per-second attack, mitigated in August 2023 using the HTTP/2 Rapid Reset technique (CVE-2023-44487).
How many DDoS attacks happened in 2025?
Cloudflare's autonomous defenses blocked 20.5 million attacks in Q1 2025 alone (a 358 percent year-over-year increase) and an additional 8.3 million in Q3 2025 (3,780 per hour), and the full-year 2025 total grew 121 percent versus 2024's 21.3 million. NETSCOUT's ATLAS telemetry logged more than 8 million DDoS attacks worldwide in each half of 2025 across 203 countries, totalling more than 16 million for the year on the NETSCOUT global view. Exact full-year 2025 totals from each provider depend on their visibility window and customer base, but the cumulative public-internet picture is north of 40 million mitigated attacks across the major DDoS providers.
What is the Aisuru-Kimwolf botnet?
Aisuru-Kimwolf is a Mirai-class IoT botnet of 1 to 4 million infected devices, primarily Android TVs and unpatched residential routers, mostly inside US and other residential ISP networks. Cloudflare's 2025 Q3 DDoS Threat Report describes it as "the apex of botnets" of 2025, credited with 1,304 hyper-volumetric attacks in Q3 alone and 2,867 attacks across the year through that report. Aisuru-Kimwolf is the source of the November 2025 31.4 Tbps record at Cloudflare and the October 24, 2025 15.72 Tbps record at Microsoft Azure. Lumen Black Lotus Labs disrupted 550+ command-and-control nodes in October 2025 after observing daily C2 traffic surge from 50,000 to 200,000 in September 2025.
What is HTTP/2 Rapid Reset (CVE-2023-44487)?
HTTP/2 Rapid Reset is a denial-of-service vulnerability in the HTTP/2 protocol's stream multiplexing feature, tracked as CVE-2023-44487 and rated CVSS 7.5 (High). The protocol allows clients to unilaterally cancel streams using RST_STREAM frames; threat actors automate the request-then-cancel pattern at scale to generate massive request volumes per TCP connection. Records held: Google Cloud 398 million rps, Cloudflare 201 million rps, AWS 155 million rps, all in August to October 2023. The technique remains in active use even after server-side patches, often combined with traditional DDoS methods, as Imperva documented in its early-2025 commentary on a 6 million rps multi-vector attack.
Which industries are most targeted by DDoS attacks in 2025?
Telecommunications and carriers are the top sector for hyper-volumetric attacks per Cloudflare's 2025 Q3 DDoS Threat Report. Financial services hold 34 percent share of Akamai's L3/L4 telemetry for the second consecutive year, followed by gaming (18 percent) and high tech (15 percent). Akamai also recorded a 23 percent year-over-year jump in application-layer DDoS against the financial sector and a striking shift in regional concentration: APAC financial services share of regional volumetric attacks grew from 11 percent in 2023 to 38 percent in 2024 to 2025. Aisuru-Kimwolf specifically targets telecommunications, gaming, hosting providers, and financial services per Cloudflare's Q3 2025 attribution.
What is hyper-volumetric DDoS and how prevalent is it?
Hyper-volumetric DDoS refers to attacks exceeding either 1 terabit per second (Tbps) or 1 billion packets per second (Bpps). Cloudflare blocked 700+ hyper-volumetric attacks in Q1 2025 (about 4 in every 100,000 network-layer attacks) and 6,500+ in Q2 2025, an average of 71 per day and a 65-fold year-over-year increase. The count exceeding 1 Tbps doubled quarter over quarter in Q2. By Q3 2025, Aisuru-Kimwolf alone was responsible for 1,304 hyper-volumetric attacks, including a then-record 29.7 Tbps and a 14.1 Bpps attack. The Q4 2025 31.4 Tbps record extended the trajectory.
What is Operation PowerOFF?
Operation PowerOFF is a coordinated international law-enforcement initiative across 21 countries to dismantle DDoS-for-hire (booter and stresser) platforms. The operation has run since 2018 and has accumulated 100 booter-domain seizures and 11 US indictments over four years. The April 2026 wave seized 53 domains, arrested four suspects, and seized data on more than 3 million user accounts allegedly involved in launching DDoS attacks for profit. The DOJ disclosed eight services taken down in the wave, including Vac Stresser and Mythical Stress.
What happened to NoName057(16) after Operation Eastwood?
Operation Eastwood was a coordinated Eurojust + Europol takedown of NoName057(16) infrastructure across 12 countries from July 14 to 17, 2025. Despite the takedown, NoName057(16)'s DDoSia campaign continued: in the four weeks after the operation, the group's published daily target lists averaged 18 sites per day, an 80 percent increase versus the month before per Imperva's follow-up analysis. NoName057(16) targeted 3,700+ unique hosts in the 13 months ending July 14, 2025 per Recorded Future Insikt Group. The lesson: hacktivist DDoS infrastructure is structurally hard to dismantle without sustained operator-side enforcement.
How much does a DDoS attack cost an organization?
Estimates vary by source, sector, and attack duration. Public benchmarks include: roughly US$6,130 per minute for application-layer DDoS downtime per the Security Magazine analysis of vendor data, US$5,600 per minute per a widely-cited Gartner figure on general IT downtime, and Ponemon Institute estimates ranging from US$100,000 per hour at the low end to over US$540,000 per hour for large enterprises when factoring in direct and indirect costs. The DOJ's October 2024 indictment of the Anonymous Sudan operators alleged more than US$10 million in damages to US victims across 35,000+ attacks. Cost is best estimated as: per-minute revenue at risk during peak hours, plus contractual SLA penalties, plus reputational and customer-trust impact, plus mitigation overhead.
Are DDoS attacks getting longer or shorter in 2025?
Both, depending on attack class. Hyper-volumetric volumetric (L3/L4) attacks have shifted toward burst mode: the 31.4 Tbps Cloudflare attack lasted 35 seconds, the 7.3 Tbps Q2 attack lasted 45 seconds, and most multi-vector hyper-volumetric attacks complete in under 60 seconds. Application-layer (L7) attacks favor sustained windows: the Imperva US beverage attack ran 8 minutes at 13.5 million rps, the French home-supply retailer attack ran 2 hours, and the December 2025 Aisuru-Kimwolf "Night Before Christmas" HTTP DDoS campaign sustained 200M+ rps over multiple sessions. Defenders should size detection latency to seconds for L3/L4 and minutes-to-hours-of-sustained-pressure for L7.
Where can I get the latest DDoS attack data?
The primary publishers to track for DDoS telemetry are Cloudflare DDoS Threat Reports (quarterly, blog.cloudflare.com), Cloudflare Radar (continuous, radar.cloudflare.com), NETSCOUT DDoS Threat Intelligence Report (semi-annual, netscout.com), Akamai State of the Internet (Security) (annual + ad-hoc, akamai.com), Microsoft Azure Infrastructure Blog (ad-hoc disclosures, techcommunity.microsoft.com), Google Cloud Security Blog (ad-hoc, cloud.google.com/blog), Imperva research blog (ad-hoc, imperva.com/blog), F5 Labs (annual + ad-hoc, f5.com/labs), A10 Networks DDoS Weapons reports and threat map (annual + ad-hoc, a10networks.com), Lumen Black Lotus Labs (ad-hoc, lumen.com), and CISA Alerts (ad-hoc, cisa.gov).
References
Cloudflare 2025 Q4 DDoS Threat Report: A record-setting 31.4 Tbps attack caps a year of massive DDoS assaults, February 2026.
Cloudflare 2025 Q3 DDoS threat report including Aisuru, the apex of botnets, December 2025.
Hyper-volumetric DDoS attacks skyrocket: Cloudflare's 2025 Q2 DDoS threat report, July 2025.
Targeted by 20.5 million DDoS attacks, up 358 percent year-over-year: Cloudflare's 2025 Q1 DDoS Threat Report, April 2025.
Record-breaking 5.6 Tbps DDoS attack and global DDoS trends for 2024 Q4, Cloudflare, January 2025.
HTTP/2 Zero-Day vulnerability results in record-breaking DDoS attacks, Cloudflare, October 2023.
NETSCOUT DDoS Threat Intelligence Reports H1 2025 and H2 2025.
DDoS Attacks Across the Financial Sector, FS-ISAC and Akamai (2025).
Akamai newsroom: Geopolitical tensions driving surge in DDoS attacks on financial institutions.
Defending the cloud: Azure neutralized a record-breaking 15 Tbps DDoS attack, Microsoft, November 2025.
Azure DDoS Protection 2021 Q3 and Q4 DDoS attack trends, Microsoft, January 2022.
Google Cloud mitigated largest DDoS attack, peaking above 398 million rps, October 2023.
AWS mitigated record-breaking 2.3 Tbps DDoS attack in February 2020, via SiliconANGLE on AWS Shield Threat Landscape disclosure, June 2020.
HTTP/2 Rapid Reset Vulnerability, CVE-2023-44487, CISA Alert.
Early 2025 DDoS Attacks Signal a Dangerous Trend in Cybersecurity, Imperva.
A Perfect Storm: DDoS Attack Hits Turkish Luxury Retailer During Fall Collection Launch, Imperva.
Operation Eastwood: Measuring the Real Impact on NoName057(16), Imperva.
A10 Networks DDoS Threat Map: SSDP, CLDAP, and CoAP global amplifier distribution.
Lumen disrupts AISURU and Kimwolf botnet by blocking over 550 C2 servers, Security Affairs.
U.S. Charges Two Sudanese Brothers for Record 35,000 DDoS Attacks, The Hacker News.
FBI seized domains linked to 48 DDoS-for-hire service platforms, BleepingComputer.